Undefined Behavior (UB): The Dangerous Pitfall and Speed Philosophy of C

The Philosophy of Speed and the Perils of Undefined Behavior
Hello fellow engineers and developers at 123microcontroller.com! Today, we are exploring the notoriously difficult realm of “Undefined Behavior” (UB)—a classic issue that Embedded Systems and System Programming developers inevitably face.
The C language is incredibly powerful and sits extremely close to bare-metal hardware. It’s akin to driving a Formula 1 race car stripped of all safety mechanisms like “automatic braking” to squeeze out absolute maximum speed. This freedom comes with immense responsibility. Today, we’ll uncover the philosophy behind why UB exists, why the Compiler loves to use it against us, and the devastating impact it can have on your microcontroller code!
The Philosophy and Origins of Undefined Behavior
When discussing Issues with C, Undefined Behavior is not a “bug” in the language—it is a highly intentional design choice made by the C Standard Committee. Official documentation and core guidelines explain the concept as follows:
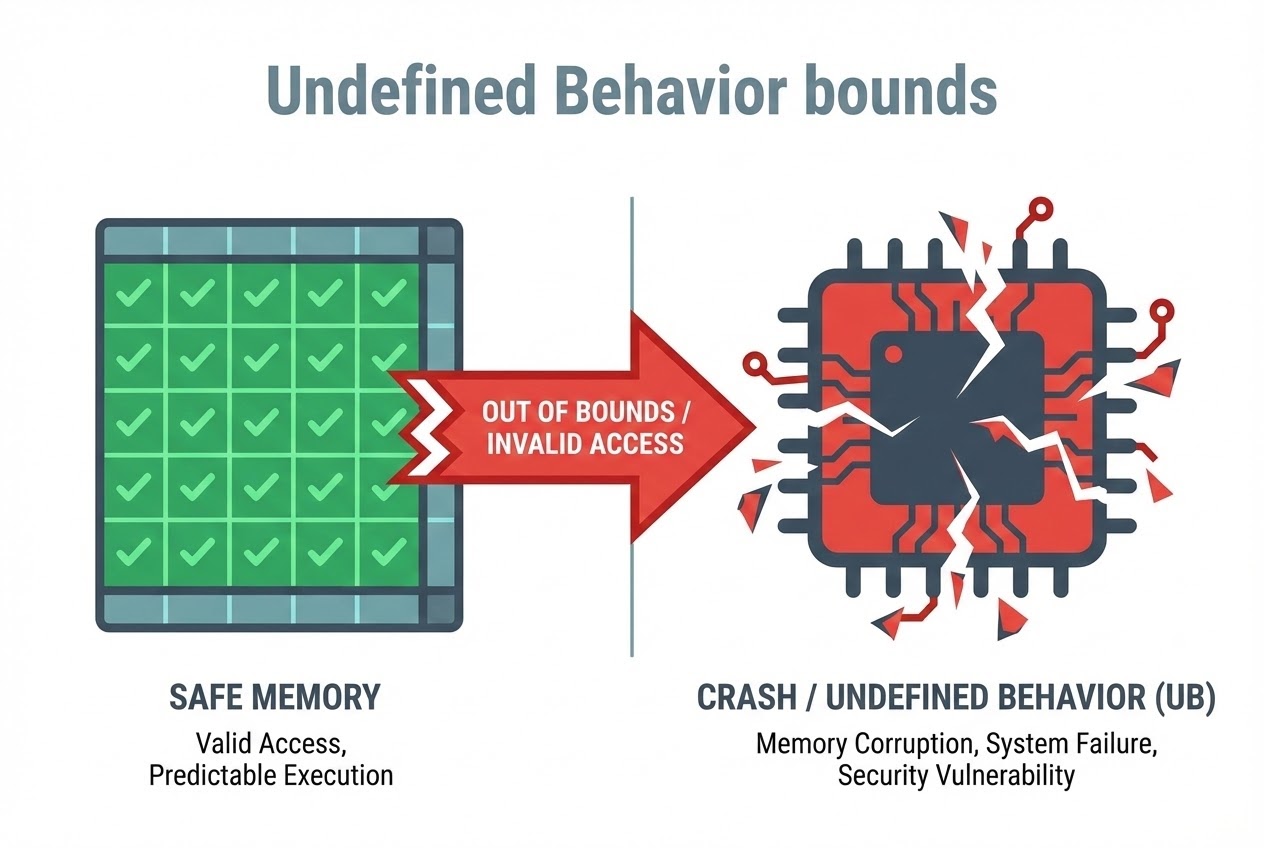
- The Definition of UB: According to the C Standard, UB occurs when a programmer writes erroneous code constructs or handles faulty data, for which the Standard “imposes absolutely no requirements” on what the Compiler must do. The result could be anything: the program might work perfectly, subtly corrupt data, crash instantly, or—in a famous programmer joke—cause “Demons to fly out of your nose.”
- The “Trust the Programmer” Philosophy: Why does C purposefully allow this danger? The answer is that C was designed to be small, lean, and blisteringly fast, perfectly matching hardware behavior. For instance, C fundamentally lacks runtime Bounds Checking for Arrays because injecting that check would computationally slow down execution. C inherently “trusts” that the programmer will always write correct logic.
- The Aggressive Optimization Trap: This is the most terrifying aspect of UB today! Modern Compilers are granted permission to assume that “a competent programmer simply never writes code causing UB.” Working under this strict assumption, the Compiler uses UB as a massive loophole to aggressively optimize code. It might execute Dead Code Elimination, sometimes violently deleting the very safety checks you wrote to prevent bugs!
- Common UB Pitfalls in Hardware Programming:
- Buffer Overflow: Accessing an Array outside its boundaries is a globally catastrophic security vulnerability (e.g., W32.Blaster.Worm, Heartbleed). It writes into adjacent memory, potentially crashing the entire system or allowing remote hacking.
- Uninitialized Variables & Pointers: Utilizing a primitive variable or a Pointer that hasn’t been assigned an initial state (resulting in garbage data, Wild, or Dangling pointers).
- Signed Integer Overflow: Permitting a signed integer variable to incrementally exceed its maximum physical memory limit.
- Order of Evaluation: Ambiguities in processing sequence, such as attempting to modify the exact same variable multiple times within a single, unsequenced continuous evaluation statement.
C Code Example
Let’s examine a raw C snippet vividly illustrating the chaotic nature of Undefined Behavior and the terrifying power of Compiler Optimization.
#include <stdio.h>
#include <limits.h>
int main(void) {
// 1. Unsequenced modifications (Undefined Behavior)
int i = 0;
/* ❌ UB: The C language strictly makes zero guarantees on whether 'i'
will be incremented (++) before or after the multiplication.
The final value is entirely compiler-dependent and unpredictable. */
i = i++ * 10;
// 2. The Optimization Trap with Signed Integer Overflow
int a = INT_MAX; // Assigning 'a' to the absolute maximum value of a signed int
/* ❌ UB & Optimization: Because C designates Signed Overflow as absolute UB,
the Compiler arrogantly assumes "a + 1 mathematically MUST be greater than a".
Therefore, the condition (a + 1) < a is strictly evaluated as "False" at Compile-time.
Result: The Compiler aggressively deletes this entire 'if' block!
You completely lose your ability to catch the Overflow Error. */
if ((a + 1) < a) {
printf("Error: Integer Overflow Detected!\n");
}
// 3. Array Out of Bounds Memory Corruption
int my_array[4] = {0, 1, 2, 3}; // A strict size-4 Array (Indices 0 through 3)
/* ❌ UB: Forcing a write to the non-existent Index 4.
C will NOT throw a runtime exception to preserve lightning speed.
Instead, it blindly overwrites the adjacent physical Memory with 99,
corrupting a potentially critical system variable. */
my_array[4] = 99;
return 0;
}
Professional Best Practices
To prevent demons from flying out of your nose and to keep your microcontroller circuits humming safely, adhere to these strict Secure Coding rules:
- Avoid Overly Clever Code (Unsequenced Modifications): Strictly avoid using Increment/Decrement operators (
++,--) repeatedly on the exact same variable within a single expression (e.g.,x++ + x). Break them down into discrete, individual lines to enforce rigid execution order. - Enforce Manual Bounds Checking: Because C refuses to check array limits, you bear the sole responsibility of manually writing
if (index < MAX_SIZE)logic instantly before probing an Array or Buffer. This absolutely prevents devastating Buffer Overflows. - Beware the Overflow Optimization Trap: If you actively need to monitor for Integer Overflows, NEVER add the values first and then check (as demonstrated in the flawed example snippet). The aggressive Compiler will delete it. The correct method is validating the limit before the calculation happens:
if (a < INT_MAX). - Always Initialize Your Pointers: Never allow a Pointer to remain “Wild”. If you don’t have a target address ready, instantly lock it down by assigning it
NULL. Furthermore, immediately after deployingfree()memory, forcefully re-assign the Pointer toNULLto eradicate Dangling Pointers.
Conclusion
Undefined Behavior is not an architectural flaw in C; it is an incredibly wide “freedom zone” intentionally left blank. It unshackles hardware constraints and permits Compilers to hyper-optimize your logic to blinding speeds. However, as a System Programmer, allowing UB into your logic is effectively planting a ticking time bomb waiting to spontaneously crash your firmware.
If you are fascinated by dodging Compiler traps or eagerly want to learn how to sculpt virtually bulletproof C code for robust microcontrollers, come join us at www.123microcontroller.com. See you in the next debugging session. Happy Coding!