Type Punning: The Ninja Technique to Bypass Type Safety in Hardware Programming

Type Punning: The Ninja Technique to Bypass Type Safety in Hardware Programming
Greetings to all engineers and fellow developers of www.123microcontroller.com! Today, the dark-eyed engineer will guide everyone through an advanced technique in C that’s often compared to a “ninja skill” known as “Type Punning”.
In modern programming paradigms, we often hear the term Type Safety. This mechanism acts as a guardian, ensuring we don’t accidentally mix incompatible data types together. Its core purpose is to guarantee that data maintains its type structure (Preservation) and code executes without malfunctioning (Progress). However, the C language traces its roots back to completely typeless origins (Typeless languages). Because of this, C lacks extreme strictness regarding Type Safety.
Sometimes in Embedded Systems development, we have an absolute “necessity” to intentionally bypass this Type Safety rule to transform how we view a block of memory from one perspective to another. Today we will dive deep to decode how legendary documentation defines Type Punning in the context of breaching the Type Safety wall, and how to reliably accomplish it without crashing our code during the compiler’s optimization pass!
Core Concept: Type Punning and Evading Type Safety
To illustrate clearly, imagine we have a solid block of memory representing a photograph. Performing Type Punning is simply us swapping “colored lenses” to view the exact same data chunk (Memory) through a completely different data type viewpoint (Type), all while the fundamental underlying bit representation in memory remains completely untouched.
Why Do Hardware Engineers Need to Break Type Safety?
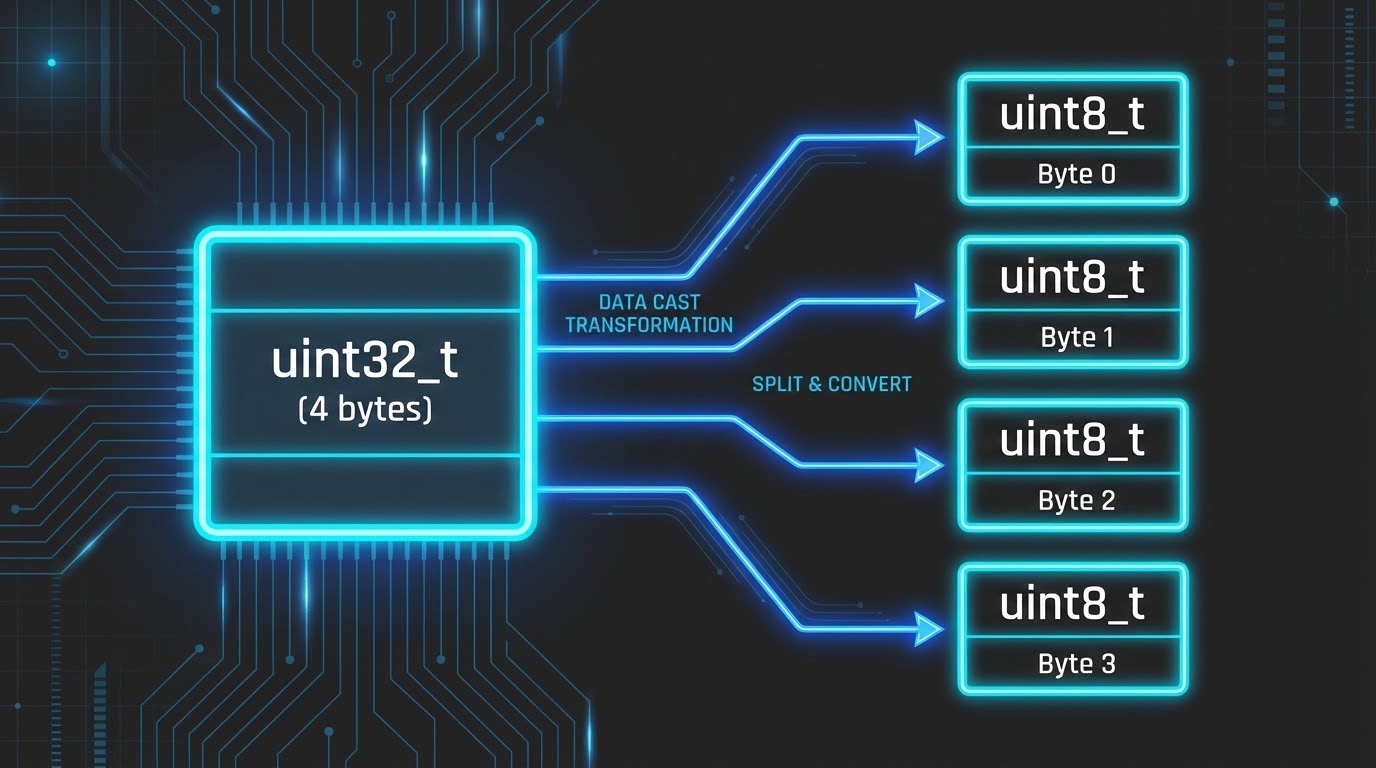
The primary motivation revolves entirely around “hardware-level communications”. Imagine reading a sensor output as a 32-bit floating-point value (float), but we must immediately transmit this data through a communication protocol strictly utilizing 1 byte at a time (like UART, I2C, or SPI). We cannot merely convert float to int using standard Type Casts because the core value will heavily distort. What we truly desire is to “slice” the raw byte data of the float into fractions, entirely neglecting that it mathematically represents a decimal number.
Pitfalls and Countermeasures in Type Punning: Type Punning is the direct evasion of the Type System logic. When applied incorrectly, it instantly induces Undefined Behavior. Standard sources define core techniques and dire warnings as follows:
- 1. Pointer Casting (The Classic Hazard): This is the traditional approach we’re accustomed to, forcefully taking an existing variable’s Pointer and casting it into a new Pointer type entirely. However, this is exceptionally dangerous! It flagrantly violates a rule known as the Strict Aliasing Rule.
- What is Strict Aliasing?: Compilers strongly assume that Pointers featuring incompatible types will never point identically to the exact same memory block. If we forcefully map an
int *onto afloat *to perform Punning, the compiler actively running Optimization mode (such as-O2in GCC) might discard our code completely or compile it erratically malfunctioned!
- What is Strict Aliasing?: Compilers strongly assume that Pointers featuring incompatible types will never point identically to the exact same memory block. If we forcefully map an
- 2. The Character Pointers Exception: The standard C language specification officially permits using
char *orunsigned char *pointers to view ANY underlying data type devoid of violating Strict Aliasing rules. Consequently, casting any Pointer directly to anunsigned char *to strictly extract data byte-by-byte is universally recognized as safe. - 3. Using Unions (The Preferred Way): Data structures formulated as
unionare distinctly architected so every enclosed member openly shares the identical memory footprint. Actively writing data into a specific member (likefloat) and subsequently reading the outcome from an alternate member (likeintor abyte array) is recognized as the safest, most transparent manifestation of Type Punning. The compiler implicitly understands from structural mapping that these variables share memory properties upfront.
Code Example
Let’s witness an example of extracting the raw hidden bytes of a float value to transmit the data externally. This code contrasts the methodology that violates Strict Aliasing (Bad) versus utilizing a union structure which is robustly safe (Good).
#include <stdio.h>
#include <stdint.h>
/* ✅ Good Practice: Utilizing Union for safe Type Punning */
typedef union {
float f_val; // Lens 1: View as a 32-bit floating-point number
uint32_t i_val; // Lens 2: View as an Integer 32-bit data block
uint8_t bytes[4]; // Lens 3: View as an Array of Bytes (ideal for UART transmission)
} FloatConverter;
int main(void) {
float sensor_val = 3.14f;
/*
* ❌ Bad Practice: Pointer Casting violently piercing Type Safety (Crash Hazard)
* Doing this breaches the Strict Aliasing Rule. The compiler might heavily misoptimize the code.
* The SEI CERT C standard rule EXP39-C severely forbids this.
*/
uint32_t *bad_ptr = (uint32_t *)&sensor_val;
printf("Bad Punning (Hex): 0x%08X\n", *bad_ptr);
/*
* ✅ Good Practice: Implementing Union or unsigned char *
* Code remains fundamentally readable, and the compiler explicitly comprehends the shared Memory.
*/
FloatConverter converter;
converter.f_val = sensor_val; /* Write data purely as float */
/* Safely extract data output as uint32_t devoid of breaking Aliasing rules */
printf("Good Punning (Hex): 0x%08X\n", converter.i_val);
/* Safely dissect and extract data iteratively byte-by-byte ready for UART/I2C staging */
printf("Byte 0: 0x%02X\n", converter.bytes[0]);
printf("Byte 1: 0x%02X\n", converter.bytes[1]);
return 0;
}
Best Practices / Precautions
To guarantee our hardware avoids malfunctioning crashes when executing this ninja skill, the gold standard SEI CERT C Coding Standard coupled with expert consensus recommends complying with these directives:
- Do Not Access Data Via Impermissible Pointers (Rule EXP39-C): Modifying or accessing data utilizing pointers possessing incompatible types is strictly forbidden (Exception:
unsigned char) as this invariably ushers unpredictable outcomes stemming from compiler optimization layers. If Type Punning is absolutely mandatory, employing standard-compliantunionarchitectures is vastly advocated. - Beware of Memory Alignment Pitfalls (Rule EXP36-C): Disillusioning a Pointer explicitly to target a data type encompassing significantly stricter Memory Alignment prerequisites (e.g., transitioning from a
char *capable of occupying any address seamlessly, to anint *mandated exclusively traversing addresses divisible by 4) invokes an instantaneous Hardware Trap or aggressive system crash instantly upon memory read operations. - The Endianness Conundrum: When actively dissecting data structures utilizing Type Punning to dispatch it externally, the chronological sequence layout of the mapped bytes (which byte commands the foremost sequence) profoundly depends on the innate CPU architecture (Little-endian vs Big-endian). Should the communication cross bridging distinct contrasting platforms, developers must proactively swap the byte positioning sequence strictly prior to practical execution.
- Emergency Countermeasures for Legacy Code: If condemned heavily to maintain massive Legacy Code utterly flooded with volatile Pointer Casting Type Punning with extreme difficulty to patch swiftly, developers can aggressively instruct the compiler to temporarily disable Strict Aliasing analysis. Appending the flag
-fno-strict-aliasingexplicitly within GCC ensures the foundational program doesn’t exhibit radical chaotic behavior induced directly by malicious optimization stripping away logic.
Conclusion & CTA
Type Punning represents an agile ninja technique enabling Embedded programmers supreme manipulative freedom to convert perspectives and manipulate root byte-level bits entirely directly. However, recognizing it overtly punches straight through the defensive armor of C’s Type Safety, imposing perilous disasters including catastrophic Strict Aliasing miscalculations and Memory Alignment tragedies is crucial. Avoiding purely brutal unrestricted Pointer Casting logic while embracing standard struct Union integration or Character Pointers persists universally recognized as the fundamentally secure benchmark protocol!
We wholeheartedly hope this deep dive clarifies the sheer intricacies underlining Type Safety and arms you with immense confidence tackling deep hardware data manipulations flawlessly devoid of bugs! Have you survived encountering a brutal bug spawned from reckless Type Punning Compiler Optimization stripping logic? Bandwidth over to share incredible war-stories in our heavily populated tech discussion board at www.123microcontroller.com immediately! Catch you again next intensive coding article, Happy Coding!