Static Analysis (Lint Tools): The Automated Architect for Writing Safer C
Introduction: When Compiling Is Not Enough
Hello engineers and fellow developers at www.123microcontroller.com! Today, the dark-eyed engineer is here to discuss what is essentially the hardware programmer’s “third eye”: the incredibly powerful toolset known as Static Analysis, classically referred to by many as “Lint”.
Have you ever written C code, hit compile, and seen the beautiful “Zero errors, Zero warnings,” only to flash the firmware onto the microcontroller and watch it immediately crash upon reading a sensor? The terrifying truth is that compiling successfully offers zero guarantee that the code is logically correct, safe, or secure. In the context of Writing Safer C, manually inspecting 100,000 lines of code with the naked eye is simply infeasible. Today we will dive deeply into why top-tier engineering literature designates Static Analysis as a mandatory, non-negotiable tool for building secure systems!
Why Do We Need Static Analysis and Lint?
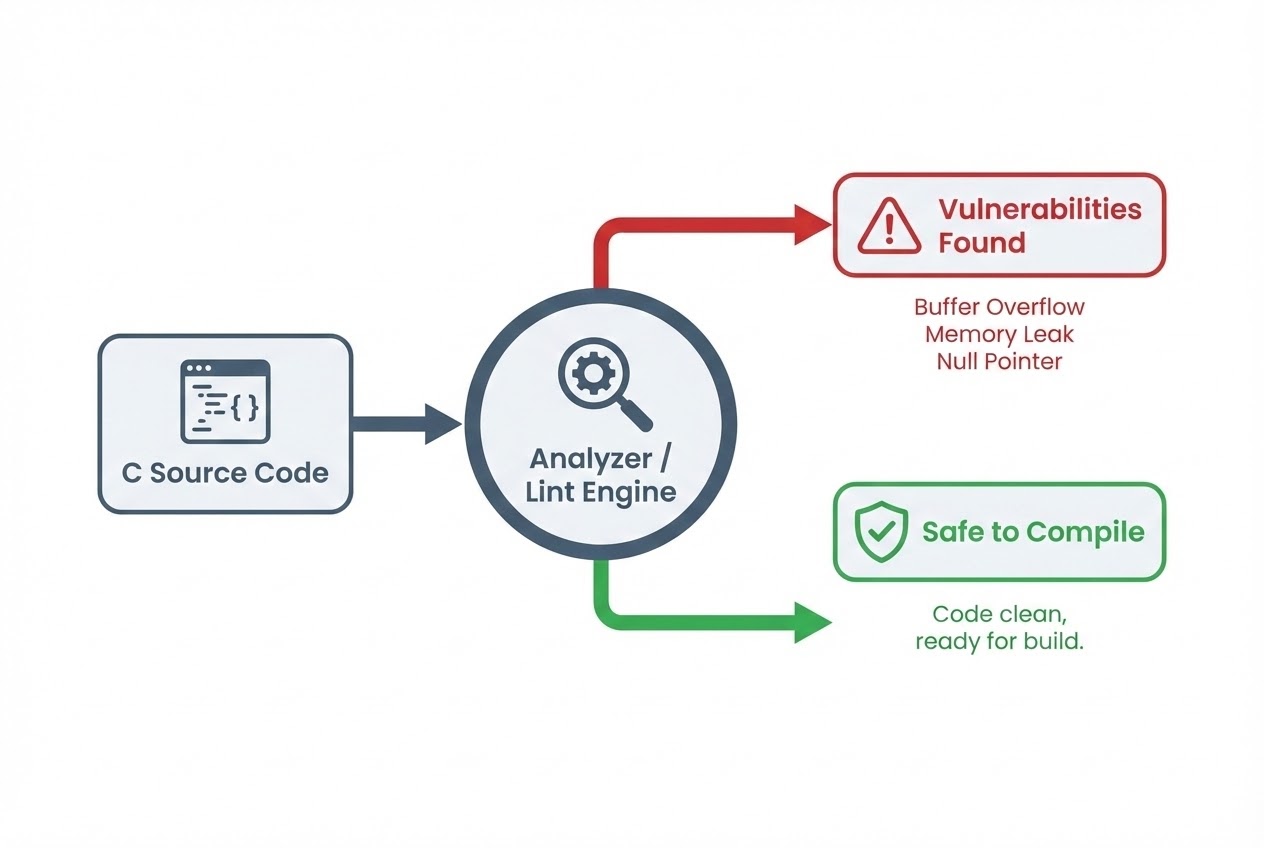
To make a simple analogy: The Compiler acts like a grammar teacher—it checks if you spelled variables correctly and closed your parentheses. The Static Analyzer (or Lint), however, acts like an experienced Editor. It investigates the “logic, semantics, and context” to determine if what you wrote contains vulnerabilities or inevitable execution crashes, doing so without actually executing the code (Assessing code without executing it).
- The Origin of Lint: Believe it or not, developers misusing C is an ancestral problem! The original code analysis tool, literally named “Lint”, was developed in 1976 by the K&R team (the creators of C). They realized early on that programmers frequently “misused legal but dubious constructs” allowed by C’s syntax. While modern linting capabilities are often heavily integrated into contemporary compilers, the engineering community still fondly refers to this entire class of tools as “Linters.”
- Automated Enforcement: Writing Safer C means adhering to rigorous standards like MISRA C or SEI CERT C. Since humans cannot feasibly memorize hundreds of dense rules and spot infractions by eye, we rely on Static Analysis to continuously scan our repositories and throw automated alerts whenever we accidentally violate a safety constraint.
- Deep Vulnerability Coverage: Advanced static analyzers perform extensive “Data flow analysis”. They can track highly obscure bugs ranging from Uninitialized variables, division by zero, and Buffer overflows (out-of-bounds array access), to menacing Race conditions hidden within Multithreading environments.
The Challenge: False Positives and False Negatives
The mechanism is not 100% flawless. According to the Halting problem in theoretical computer science, perfectly predicting program behavior without running it is computationally impossible. Thus, static analysis tools typically face two primary challenges:
- False Positives (The Boy Who Cried Wolf): The tool flags a bug, but logically the code is entirely safe. This generates annoying “noise” for developers.
- False Negatives (The Silent Killer): A severe vulnerability exists, but the tool entirely misses it. An exceptional static analysis tool aims to be both “Sound and Complete” (catching everything without throwing random noise), though this is incredibly difficult to achieve perfectly.
Code Example: Catching the Silent Killer
Let’s examine a terrifying example that an ordinary C compiler will often silently pass (unless explicit warning flags are enabled), but an impassioned Static Analyzer will immediately yell at you for.
#include <stdio.h>
#include <stdint.h>
/* Mock function reading a sensor (May return negative value on hardware error) */
int get_sensor_value(void) {
return -1; // Simulating a disconnected sensor
}
void process_sensor_data(void) {
/* Allocate a buffer of 10 slots (Indices 0-9) */
uint32_t sensor_buffer[10] = {0};
int index = get_sensor_value();
/*
* ❌ VULNERABILITY ALERT!
* A standard C compiler compiles this perfectly.
* But a Static Analyzer immediately points out that 'index'
* could vividly be negative (-1), leading straight to a fatal
* Out-of-bounds write memory corruption!
*/
sensor_buffer[index] = 1000;
printf("Data logged at index: %d\n", index);
}
int main(void) {
process_sensor_data();
return 0;
}
The Safer C Fix: We must forcefully inject explicit bounds checking: if (index >= 0 && index < 10). Once this safeguard is implemented, the Static Analyzer recalculates the data flow and happily silences its alarm.
Best Practices for Utilizing Automated Analyzers
Global standard literature recommends employing these tools via the following Best Practices:
- Don’t Just Quiet Warnings: Good compilers and linters provide extremely high-value warnings. When you encounter a warning, understand the root engine of the issue and fix the underlying code. Never blindly slap on a Type Cast just to make the red squiggly line disappear!
- Max Out Compiler Features First: Before purchasing sophisticated external tools, maximally crank up your compiler’s internal warning flags. Use
-Walland-Wextrain GCC/Clang. Furthermore, leverage the built-in static analysis engines like-fanalyzerin GCC (version 10+) or/analyzein Microsoft Visual C++. - Supplement with Third-party Tools: There is an ocean of free and commercial tools built entirely for security scanning. Examples include Splint for legacy security checks, clang-tidy for enforcing modern clean code guidelines, ROSE for validating CERT C rules, or Enterprise-grade juggernauts like Coverity and LDRA.
- Use Multiple Tools: Because different tools deploy distinct traversal algorithms (e.g., detecting buffer overflows), running multiple distinct linters simultaneously significantly reduces blind spots, providing incredibly robust vulnerability coverage.
Conclusion
Writing Safer C absolutely cannot rely on human discipline and eyesight alone. Static Analysis and Lint tools are a hardware programmer’s truest companions and automated architects. They tirelessly scan for semantic weaknesses, memory vulnerabilities, and twisted logic, allowing us to rest significantly easier before flashing code onto our production microcontrollers. Investing time in these tools equates to saving an immeasurable magnitude of brutal debugging hours later.
If you are eager to learn step-by-step how to install clang-tidy or deeply configure -fanalyzer, be sure to keep reading and sharing incredible projects over at www.123microcontroller.com. See you in our next deep-dive. Happy Coding, everyone!