Stacks (LIFO): The Formidable Data Structure Engineering the Very Breath of Microcontrollers

Introduction: The Hidden Gears Driving Computer Architecture
Hello engineers and fellow developers at www.123microcontroller.com! Today, the dark-eyed engineer is taking you on an expedition to examine a Data Structure inextricably wired into the deepest foundations of hardware architecture and the C programming language itself: The mighty Stack.
When stepping into the world of algorithms, Linear data structures are typically our immediate battleground, and the Stack stands tall among them. In aggressive System Programming—whether executing function nesting, resolving fierce mathematical recursion, or managing bare-metal memory limits—microcontrollers absolutely depend on Stack mechanics to survive. Today, let’s heavily dissect how engineering literature breaks down the operational philosophy of the Stack within the global ecosystem of Data Structures!
What is a Stack Architecturally?
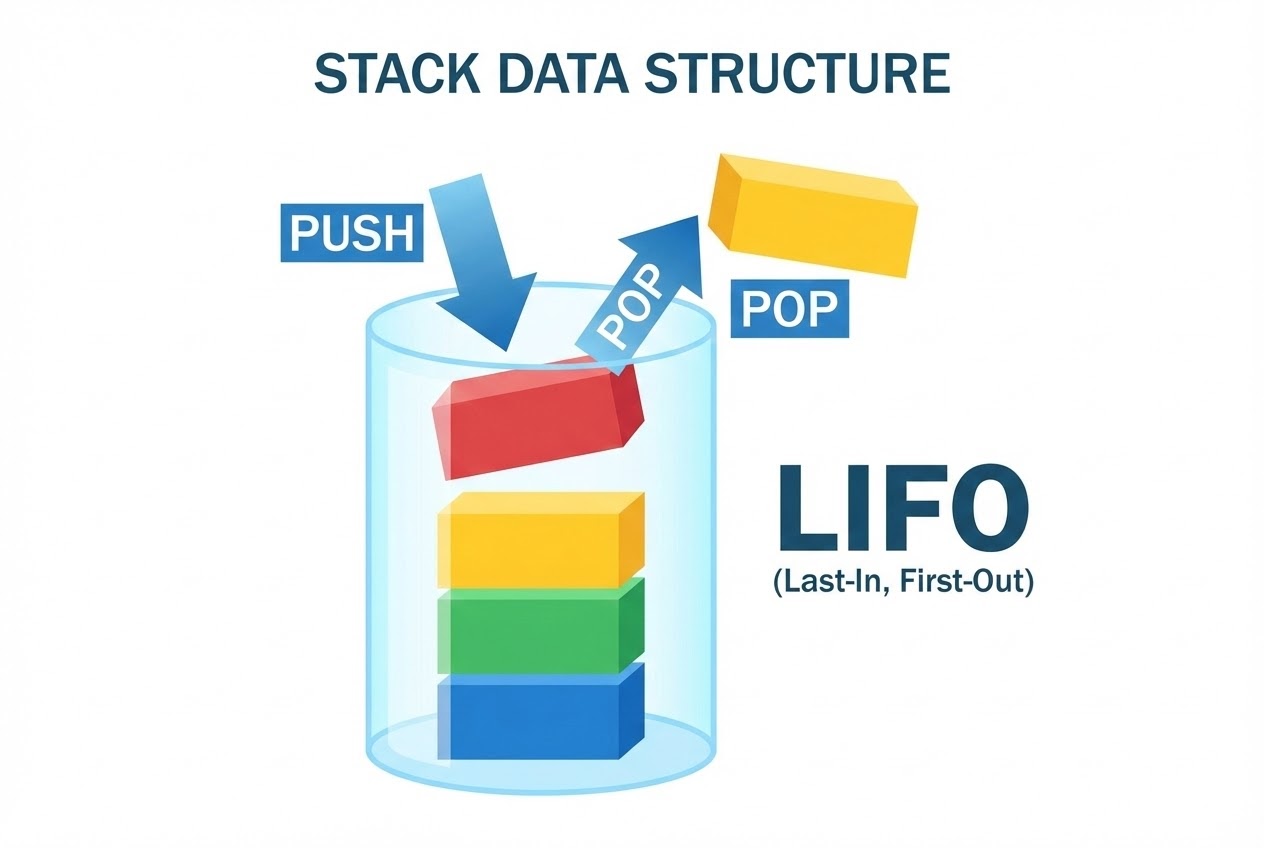
Classified mathematically within computer science, a Stack is a rigid, Linear Data Structure. Its undisputed defining characteristic is its adherence to the LIFO (Last-In, First-Out) principle. Strictly translated, this indicates that the absolute final piece of data driven into the structure will forcefully become the absolute first piece retrieved from it. (Intellectually, this is synonymous with FILO: First-In, Last-Out).
To conceptualize this physically, envision a “spring-loaded cafeteria plate dispenser” or a “narrow tennis ball cylinder”. When storing a new plate, you are forced to forcefully lock it down onto the highest peak (Push). Conversely, when retrieving one for utility, you are biologically forced to pluck the topmost plate off first (Pop). You cannot magically extract a unit from the dead-center or the bedrock bottom without temporarily dismantling the entire upper payload.
The 3 Core Prime Operations:
- PUSH: The architectural action of inserting or deploying raw data directly onto the absolute “Top” coordinate of the Stack.
- POP: The destructive action of extracting, returning, and logically erasing the data currently inhabiting the “Top” coordinate.
- PEEP (or PEEK): The surveillance action of non-destructively scanning and evaluating the data at the “Top”, preserving its existence on the Stack.
Silicon Implementation Pathways:
In pure C, engineering a Stack commonly dictates two structural vectors:
- The Array-Based Stack (Static): The uncontested champion in Embedded Systems. We allocate a solid Array to act as the reservoir and deploy a singular Integer (traditionally
top) to operate as our Index targeting the highest payload. The devastating flaw? The maximum capacity is perpetually frozen in amber. Overloading it causes brutal destruction. - The Linked-List Stack (Dynamic): We commandeer a Linked List but aggressively lockdown its access algorithms, restricting Node creation and destruction explicitly to the “Head” of the chain. The overwhelming advantage? The memory footprint scales dynamically, preserving precious early RAM without claiming unused territory.
The Macro-Role of Stacks in Firmware Domination:
Stacks transcend academic textbooks; they physically regulate computer hardware mechanics:
- The System Call Stack (Stack Frames): This is where naked hardware organically fuses with your C Compiler! Upon executing a Function Call, the CPU architecture dynamically forges a massive memory packet designated a “Stack Frame” (Activation Record) and brutally PUSHES it onto the master hardware Call Stack. This Frame hoards “Local Variables,” “Incoming Parameters,” and critically, the “Return Address” (the specific machine code line the CPU must retreat to upon function completion).
- Recursion Execution: Writing deeply recursive algorithms solely functions because the processor continually stacks overlapping Frames atop one another, suspending previous dimensional state logic.
- Mathematical Expression Evaluation: Compilers deploy hidden logic Stacks to translate vulnerable human-readable math (Infix, like A+B) into brutal machine-efficient structures like Postfix or Prefix.
Code Example: Hard-Coding an Array-Based Stack
Let’s dissect an elegant, highly deterministic Array-based Stack execution. This constitutes the armored standard for executing Stacks on hyper-constrained microcontrollers, eliminating unpredictable dynamic Heap variables:
#include <stdio.h>
#include <stdbool.h>
#define MAX_SIZE 5 // Hardcode the architectural ceiling restricting Dynamic Allocation
/*
* Encapsulating the Stack variables firmly in Static memory.
* Optimal design for constrained Embedded modules requiring a single global Stack.
*/
static int stack_data[MAX_SIZE];
static int top = -1; // Initialized to -1 projecting an absolute void (Index 0 is unoccupied)
/* Validation protocol scanning for total Stack depletion */
bool is_empty(void) {
return (top == -1);
}
/* Validation protocol scanning for maximum Stack capacity */
bool is_full(void) {
return (top == MAX_SIZE - 1);
}
/* 1. PUSH Operation: Forcefully inject payload onto the apex */
bool push(int new_value) {
if (is_full()) {
printf("CRITICAL: Stack Overflow! Injection denied for data: %d\n", new_value);
return false; // Defensive abort preventing catastrophic memory overwriting
}
top = top + 1; // Elevate the index target vertically
stack_data[top] = new_value; // Cement the payload byte into the Array
return true; // Acknowledge structural success
}
/* 2. POP Operation: Sever and extract the apex payload */
int pop(void) {
if (is_empty()) {
printf("CRITICAL: Stack Underflow Detected!\n");
return -1; // Dispatch universal Error Code (Custom codes usually applied in production)
}
int popped_value = stack_data[top]; // Lock onto apex data value
top = top - 1; // Depress the index (Old data remains physically but is logically dead)
return popped_value;
}
int main(void) {
push(10);
push(20);
push(30);
printf("Popped Component: %d\n", pop()); // Violently ejects 30 first (LIFO execution)
printf("Popped Component: %d\n", pop()); // Violently ejects 20 second
return 0;
}
Neutralizing Stack Operation Catastrophes
Manipulating Stacks commands ruthless discipline. To guarantee a Safe and Reliable architecture, secure engineering textbooks vehemently warn of these severe pitfalls:
- The Stack Overflow Cataclysm: If deploying an Array-base and you neglect to explicitly encode the physical barrier check (
top == MAX_SIZE - 1) prior to invokingPush, compiling raw writes blows entirely past the assigned Array bounds. This instantaneously overwrites foreign memory sectors (Buffer Overflow). Conversely, if engineering hyper-deep function chaining (Deep Recursion) devouring the primary System Call Stack, your CPU will instantly crash or execute a deadly Hard Fault—universally recognized as a software “Stack Overflow.” - Mitigating Stack Underflows: Before initiating a
PoporPeekassault, you must verify the structural integrity (ensuretopis not-1). Demanding payload extraction from an Empty Stack is classified as a Stack Underflow. At best, you drag uninitialized RAM “Garbage Values” into your primary logic math. At worst, you crash the algorithmic architecture completely. - Dynamic Stack Memory Demolition: Should you opt to build a Dynamic Stack utilizing a Linked List combined with C’s notoriously dangerous
malloc(), understand the unbending law of thepop()function. Lowering thetopPointer is not enough: You must explicitly executefree(temp_node)to relinquish the severed Node’s physical footprint back to the OS. Failing this immediately triggers a terminal Memory Leak, sapping your system until absolute death.
Conclusion
Stacks project a deceptive aura of simplicity, hiding an immensely powerful architectural core. Its unyielding LIFO (Last-In, First-Out) prime directive acts as the foundational gear enabling low-level languages like C to autonomously govern recursive program flow, suspend deeply nested function calls, and organically translate high-order mathematics into raw machine instructions. Consequently, forging bug-free, dynamically robust Stacks isn’t just theory—it is an absolutely mandatory survival skill for hardware engineers dominating the physical layer.
If you thrive on ripping apart high-level software abstractions to expose the brutal machine-code realities underneath, connect with us to read heavy-duty Embedded C tutorials! Keep tracking deep architecture bugs, sharing custom scripts, and elevating your skills at www.123microcontroller.com. See you in our next structural breakdown war-room. Happy Coding everyone!