Short-circuit Evaluation: The Genius of C That Secretly Morphs into Hidden Bugs (Counter-intuitive Syntax)
Short-circuit Evaluation: The Genius of C That Secretly Breeds Hidden Bugs
Hello fellow engineers and developers at 123microcontroller.com! Today, we are taking a deep dive into an architectural syntax behavior in the C language that constantly leaves programmers scratching their heads: “Short-circuit evaluation”.
In hardcore hardware-level programming, we are heavily indoctrinated with the belief that “the computer executes exactly what you tell it to do, step by step.” However, would you believe that within the specific domain of Logical Operators, the C language harbors intensely “Counter-intuitive Syntax”? Without warning, the Compiler possesses the absolute authority to aggressively “skip over” and outright refuse to run specific segments of your code! Today, let’s explore exactly how legendary computing literature describes this phenomenon, why it is mechanically brilliant, and how we can dodge its fatal traps when structuring robust Embedded Systems.
Core Concept: The Mechanics of Logical Short-Circuiting
Within the umbrella of Counter-intuitive Syntax, C possesses linguistic characteristics that superficiality appear to function one way, but aggressively operate entirely differently under the hood. For foundational Logical Operators like Logical AND (&&) and Logical OR (||), C fundamentally employs a hyper-optimized mechanism officially termed Short-circuit evaluation (frequently referred to as Minimal Evaluation or Lazy Evaluation).
The ironclad rules controlling Short-circuiting are:
- Strict Left-to-Right Processing: C architecturally guarantees that any dual-sided expression joined by
&&or||will absolutely be evaluated starting from the extreme left expression progressing towards the right. - Logical AND (
&&): The instant the left-flank expression numerically evaluates to False (0), the Compiler mathematically deduces that the entire compound statement has zero probability of ever being True. Therefore, it instantly halts all further processing, completely ignoring the right-flank expression! - Logical OR (
||): Conversely, if the left-flank expression evaluates to True (nonzero), the Compiler logically deduces that the compound requirement is already satisfied. It instantly halts processing, abandoning the right flank!
What triggers the Counter-intuitive confusion?
The core conflict arises because human programmers naturally apply mathematical algebraic assumptions where every single term is invariably calculated. Furthermore, developers frequently confuse Logical operations with pure hardware Bitwise Operators (& and |)… which strictly force the absolute evaluation of both flanks simultaneously without any short-circuiting!
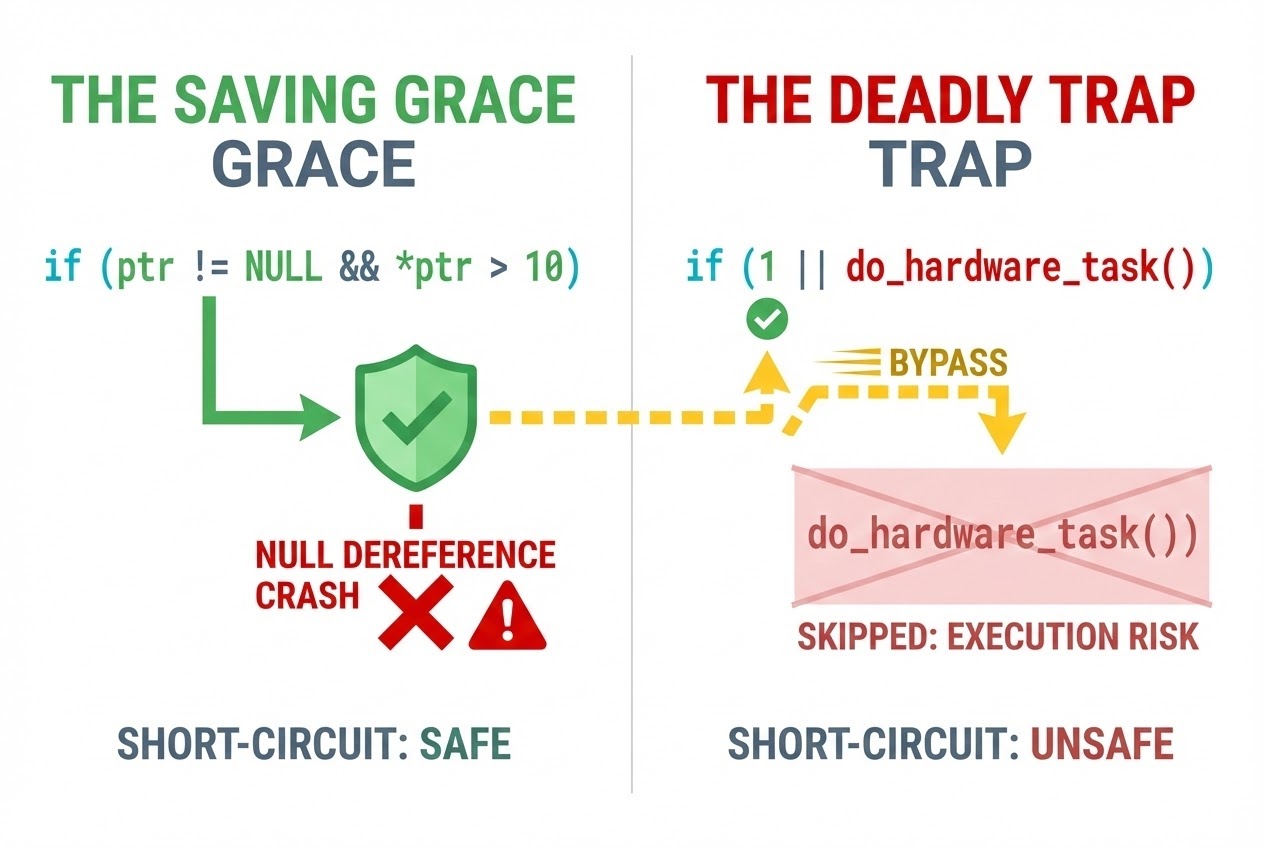
When we carelessly embed code carrying critical “Side effects” (such as performing ++, --, or calling functional logic that alters physical hardware states) exclusively into the right half of an && or || operator, that code might mathematically never be executed! The microcontroller’s internal state silently fractures away from the developer’s assumptions.
However, when weaponized correctly, Short-circuit evaluation elevates into an extraordinarily powerful engineering feature:
- Absolute Defense Against Divide-by-Zero: We can securely script
if (b != 0 && (a / b > 1)). Due to the Short-circuit mechanism, ifbis0, the hazardous division on the right is fully bypassed, saving the hardware from a fatal operating system Crash. - Null Pointer Dereference Immunity: Deep inside Pointer management, we frequently structure
if (ptr != NULL && *ptr == n). This perfectly guarantees that we will never provoke Undefined Behavior by aggressively accessing a vacant memory address. - CPU Cycle Conservation: If the right-hand function consumes massive CPU cycles (e.g., polling an intense external sensory array), we can proactively place a lightning-fast status flag on the left flank (e.g., checking if the peripheral is awake). The heavy processing is entirely bypassed if the rapid flag rejects execution.
Code Example
Let’s dissect a comprehensive C code simulation physically demonstrating both the “life-saving utility” and the “counter-intuitive traps” of Short-circuit architecture!
#include <stdio.h>
// Simulated function that triggers actual physical hardware action
int read_sensor_data(void) {
printf("--> Physical Hardware Sensor is being aggressively polled...\n");
return 25; // Transmits payload back
}
int main(void) {
// ---------------------------------------------------------
// 🟢 Scenario 1: Weaponizing Short-circuit for Hardware Safety (Best Practice)
// ---------------------------------------------------------
int *sensor_ptr = NULL; // Uninitialized isolated pointer
/* 100% Secure! Because the left constraint (sensor_ptr != NULL) mathematically resolves to False,
the Compiler aggressively short-circuits. The fatal right constraint (*sensor_ptr > 10)
is categorically suppressed, completely dodging a catastrophic memory Crash! */
if (sensor_ptr != NULL && *sensor_ptr > 10) {
printf("Sensor payload is extremely high.\n");
} else {
printf("Safety Engaged: Pointer evaluated to NULL, dereferencing forcefully bypassed.\n");
}
// ---------------------------------------------------------
// 🔴 Scenario 2: The Counter-intuitive Trap (Sensor is completely ignored!)
// ---------------------------------------------------------
int override_mode = 1; // 1 = Hardware override switch engaged
/* ❌ DANGER: Because the 'override_mode' on the left validates as True (1),
the logical OR (||) instantly short-circuits the entire statement!
The right-hand functional call 'read_sensor_data()' is NEVER executed!
The critical hardware read operation was completely abandoned! */
if (override_mode || read_sensor_data() > 20) {
printf("System Integrity Check Authenticated!\n");
}
// ---------------------------------------------------------
// 🔴 Scenario 3: The Silent Evaporation of 'Side Effects'
// ---------------------------------------------------------
int apple = 1;
int pear = 3;
/* ❌ Counter-intuitive: The programmer structurally assumes the pear variable will decrement (--).
Harsh reality: Because 'apple' is inherently True (1), the OR (||) actively skips the right flank!
The decrement operator is functionally disabled, leaving 'pear' at its original state of 3. */
if (apple || (--pear)) {
printf("Command issued: take a piece of fruit.\n");
}
printf("Pears remaining: %d (Human expectation was 2, but actual reality is %d!)\n", pear, pear);
return 0;
}
Secure Coding Best Practices
Sourced directly from ironclad global frameworks like the SEI CERT C Coding Standard and insights from Expert C Programming, here are the mandates to systematically inoculate your code against Short-circuit vulnerabilities:
- Absolutely No Side Effects on the Right Flank: Structurally forbid the usage of increment/decrement operators (
++,--), assignments (=), or function calls that actively alter the program’s global state (State-changing functions) on the right side of&&and||. Because you can never mathematically guarantee they will be processed, violently extract them and execute those operations chronologically before the encompassingifstatement. - Rigorously Distinguish Logical (
&&,||) from Bitwise (&,|) (Rule EXP46-C): Bitwise operators uniquely do not perform Short-circuit evaluation. They rigidly force dual-flank processing. Accidentally utilizing a single&when a dual&&was required within control conditions spawns microscopic logic bugs that spiral rapidly into catastrophic Undefined Behavior or deep security vulnerabilities. - Optimize Order for Terminal Velocity: Inside
&&operations, intentionally place the condition statistically harboring the highest “False” probability aggressively on the far left. Conversely, inside||statements, structure the condition carrying the highest “True” probability strictly on the left. This weaponizes the compiler to trigger the Short-circuit mechanism blazingly fast, heavily compounding your CPU execution speeds!
Conclusion
Within the structural hierarchy of C, Short-circuit evaluation operates as a razor-sharp double-edged sword. Functioning dynamically as an automated Safeguard, it enables us to write hyper-compact condition validations cleanly and sequentially. Simultaneously, it acts as an extremely deceptive, Counter-intuitive grammatical trap because its mechanics literally vaporize executable commands directly off your screen without triggering a singular compiler warning. As hardcore Embedded Systems engineers, we must maintain ultimate vigilance regarding how we place destructive ‘Side effects’ inside our structural control flows!
We emphatically hope this granular technical breakdown enables you to harden your codebase and engineer profoundly safe execution loops! If you possess a relentless drive to deconstruct hyper-advanced logical behaviors in C or analyze industrial-grade Secure Coding standards, join our relentless technical community over at www.123microcontroller.com. See you all in the incoming tutorial slice. Happy Coding and maintain absolute vigilance over your syntax!