Serial Buses (SPI, I2C, UART): The Hardware Communication Arteries Fueling the Embedded C Ecosystem

Introduction: The Aortic Valve Pumping Data Through the Micro-Architecture
Greetings, elite hardware engineers and bare-metal coders of the www.123microcontroller.com vanguard! The dark-eyed engineer has emerged from the logic analyzer trenches once again. Today, we confront the raw, beating heart—the absolute “Major Blood Vessels”—of physical low-level programming (Hardware Interaction). We are dissecting the unrelenting highway infrastructure governing how silicon physically speaks: the architecture of Serial Buses.
Isolated perfectly inside the vacuum of Embedded Systems design, a singular naked microcontroller core operates entirely blind, deaf, and mute; utterly incapable of arrogant, solitary functioning. To achieve dominance, it must aggressively consume environmental telemetry from external sensors, forcefully dump logging parameters deep into non-volatile memory chips, or rapidly stream graphical matrix computations outward painting optical displays. The foundational capability enabling these foreign, heterogeneous silicon platforms to negotiate data exchanges seamlessly necessitates strict adherence to universal “Communication Protocols.” Scanning the landscape, legendary top-tier engineering consortiums universally recognize the dominant ‘Holy Trinity’ of hardware communication buses dictating the modern industry: UART, SPI, and I2C. Today, we mercilessly decrypt and expose the extreme tactical advantages and fatal weaknesses characterizing each bus topology, analyzing exactly how we, as aggressive C developers wielding direct authority, must intercept and manipulate them to extract maximum, undisputed terminal velocity!
Breaching the Protocols: Decoding the Big Three Serial Infrastructures
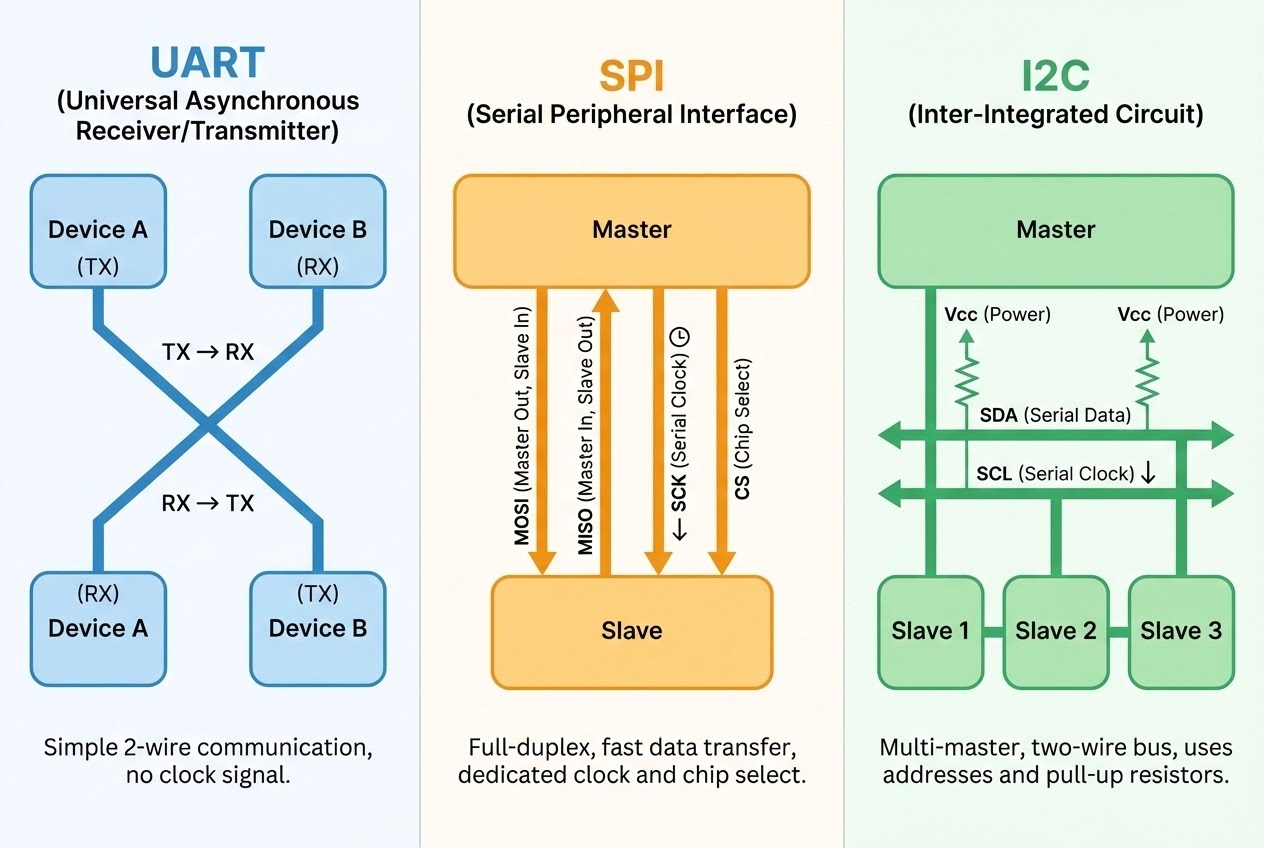
Executing tactical data routing between local hardware matrices on contemporary motherboards heavily prioritizes adopting “Serial” protocol configurations (aggressively queuing bits singularly across a single trajectory). The driving physical logic is to ruthlessly minimize massive copper trace footprints and aggressively conserve highly valuable, tightly packed logic board geography. While undeniably, rogue software-masochists possess the grim capacity to manually calculate algorithm timing delays forging synthetic clock signals and data pulses blindly manually (an archaic dark-art software hack universally classified as ‘Bit-Banging’), integrating this horror acts as a massive carcinogenic parasite, uncontrollably consuming ultra-critical processor execution cycles while ensuring timing synchronicity drifts into near impossibility. Consequently, elite senior architectural guidelines forcefully mandate avoiding software emulation, commanding developers instead to exclusively harness hardened “Hardware Peripherals” physically etched permanently into the silicon die constituting the microcontroller. These silicon accelerators universally partition into three sovereign classifications:
- 1. UART (Universal Asynchronous Receiver/Transmitter): The Asynchronous Lone Wolf
- Operational Theory: UART architectures fundamentally operate governed by reckless Asynchronous mechanics—translating essentially to “zero synchronized clock signals directing traffic.” To prevent chaotic data-streams, both isolated peripheral endpoints (the Transmitter and Receiver targets) must rigidly agree upon a pre-calculated mathematical transmission velocity metric (Baud rate), locked into their configurations strictly prior to engagement.
- Signal Geometry: The hardware infrastructure heavily strips complexities utilizing just a skeletal two-wire matrix: The outbound muzzle TX (Transmit) and external receptor RX (Receive) pins. The absolute unbreakable physical law demands a ‘Crossover’ cabling topology: forcibly hardwiring the transmitting TX portal of silicon Unit A directly piercing into the receiving RX sensory input of silicon Unit B.
- Tactical Advantage: Innately possesses a Full-Duplex execution spirit (possessing dual independent arteries enabling simultaneous parallel transmission and reception operations). Architecturally, this represents the undisputed standard configuration predominantly weaponized for spewing raw hexadecimal and string debugging diagnostics spanning the physical chasm bridging development boards with terminal desktop computers (PCs), parsing raw textual NMEA streams off orbital GPS modules, or commanding legacy Bluetooth serial data-link payloads.
- 2. SPI (Serial Peripheral Interface): The Supreme High-Bandwidth Executioner
- Operational Theory: SPI governs as the ultimate hardened, tightly-controlled Synchronous protocol dominating a fierce Master-Slave hierarchy. The commanding Master node legally seizes total absolute authority exclusively generating and dictating every single aggressive clock pulse driving the synchronized data transaction sequence lock-step.
- Signal Geometry: Requires a moderately bloated four-lane superhighway comprising four independent copper lines: strictly MOSI (Master Out, violently pushing payload Slave In), strictly MISO (Master In, aggressively extracting data Slave Out), strictly SCK (Serial Clock pacing the blast), and the crucial target-painter designated CS/SS (Chip Select / Slave Select defining the exact target).
- Tactical Advantage: Identical to UART, SPI deploys a Full-Duplex payload handling configuration. Crucially, exact paired data geometries are brutally shifted simultaneously in and out during every singular synchronized clock revolution (Executing pure hardware Shift-Register parity). This brutal electrical alignment physically guarantees SPI holds the absolute reigning title concerning “Extreme Top-End Bandwidth Capacity” (Trivially capable of colliding into and sustaining transmission metrics burning across several tens of Megahertz limits). It dictates selection for data-starved components calculating colossal flow requirements including orchestrating dynamic active LCD display matrices, rapid high-volume bulk SD Card block journaling, or sampling blistering high-frequency kinetic gyroscope modules. However, the catastrophic architectural flaw emerges: scaling up connecting multiple target devices maliciously drains and aggressively zeroes out all your available GPIO pins exclusively burning them fulfilling individual CS destination select routes.
- 3. I2C (Inter-Integrated Circuit): The Low-Copper Smart Matrix Network
- Operational Theory: I2C represents an exceptionally intelligent, hyper-optimized Synchronous configuration supporting an advanced anarchic Multi-Master negotiation architecture.
- Signal Geometry: The absolute king of resource starvation, it monopolizes only a razor-thin two-wire footprint: SDA (The shared serial data artery) and SCL (The shared serial clock synchronization metric). Crucial requirement: Both active transmission lines carry an absolute engineering mandate dictating installation of passive Pull-Up resistor components ensuring nominal default high voltage states across the active signal line.
- Tactical Advantage: Operates fundamentally constrained utilizing Half-Duplex mechanics (Politely alternating, bi-directional single lane communication traffic), but compensates brilliantly by deploying a sophisticated embedded software “Addressing Topology” (Architected parsing either 7-bit or expanded 10-bit hardware identifications). This mathematical wizardry authorizes developers the capability to physically daisy-chain parallel-connect dozens of independent localized sensor modules tapping aggressively onto precisely the identical two microscopic wire traces. It completely bypasses the horrific pin-wasting Chip-Select requirements plaguing the SPI caste! Furthermore, it incorporates an intensely rigid, auto-verifying hardware verification feedback matrix actively tracking bit success metrics relying on embedded hardware acknowledgement (ACK) and negative-acknowledgement (NACK) pulses natively. Perfect hardware match explicitly catering to slow, hyper-dense localized PCB clusters grouping localized sensors, or flashing localized configuration metrics to internal EEPROM matrices.
Source Code Integration: Smashing Bare-Metal Registers Dictating SPI Transmission
Force your attention onto this explicit analytical breakdown dissecting standard C firmware language formatting (Utilizing robust Clean Code safety formatting frameworks) engineered to aggressively command a dormant SPI silicon peripheral to violently eject (Transmit) exactly one byte of data functioning strictly at the pure logic Register configuration axis (Operating definitively Bare-Metal). This algorithm intentionally actively demonstrates a brutal structural ‘Polling’ loop mechanism verifying physical semiconductor transmission states prior to launching the data packet.
#include <stdint.h>
/* Execute initialization binding forging a permanent Pointer directly locking onto the physical Hardware Register cluster designated for the local SPI peripheral (Reference Target: STM32 Silicon Architecture) */
typedef struct {
volatile uint32_t CR1; /* Control Register 1 - The Primary Command Deck */
volatile uint32_t CR2; /* Control Register 2 - Auxiliary Command Parameters */
volatile uint32_t SR; /* Status Register - The Physical Hardware State Mirror */
volatile uint32_t DR; /* Data Register - The Live Ammunition Feed Chamber */
} SPI_TypeDef;
#define SPI1 ((SPI_TypeDef *) 0x40013000)
/* Authoring static Bitmask matrices engineered for aggressively interrogating isolated binary logic states (The Status Register matrix) */
#define SPI_SR_TXE (1U << 1) /* Target logic bit dictating Transmit buffer completely empty (Chamber clear) */
#define SPI_SR_BSY (1U << 7) /* Target logic bit dictating Busy flag (System heavily engaged, unauthorized access denied) */
/**
* @brief Tactical function execution dedicated to forcefully transmitting exactly 1 byte traversing the physical SPI communication pipe.
* @param data The localized 8-bit payload designated for immediate atmospheric transmission.
*/
void spi_transmit_byte(uint8_t data) {
/* 1. Demand absolute holding pattern remaining deadlocked spinning until the localized silicone explicitly raises the telemetry flag defining "The outgoing Transmission Data Buffer rests entirely empty" (TXE = 1).
* Implement this suicide-prevention blockade directly interrupting software actively overwriting deleting executing data currently cycling locked mid-transmission.
*/
while (!(SPI1->SR & SPI_SR_TXE)) {
// Execute aggressive holding loop (Polling architecture burning CPU clock cycles)
}
/* 2. Instantaneously confirming the holding buffer reads clear, aggressively inject the payload byte directly penetrating the Data Register (DR) container.
* With minimal latency, the physical circuitry engages, violently intercepting the byte, serializing it, and converting it directing high-velocity electrical bursts rocketing outbound across the MOSI terminal.
*/
SPI1->DR = data;
/* 3. Execute secondary waiting blockade terminating absolutely solely upon the physical hardware thoroughly verifying the complete electrical signal purging across the physical trace has finalized permanently terminating.
* (The secondary validation demands confirming the hardware Busy flag status violently demotes crashing back establishing a zero boolean state).
*/
while (SPI1->SR & SPI_SR_BSY) {
// Maintain architectural lock avoiding code progression until silicon perfectly exits the chaotic Busy execution interval.
}
}
Defensive Shielding: Averting Hardware Implosion Under Hostile Communication
Exacting heavy stability and absolute dominion over fluctuating communication frameworks rigidly conforming strictly with aggressive Secure Coding principles mathematically requires veteran systems-engineers to aggressively flag warnings guarding against these horrifying logic pitfalls:
- Surviving Basic Gravity Regarding Inverted TX/RX Geometry: The absolute reigning, legendary champion defining ultimate pathetic catastrophic logic bugs universally plaguing UART connections involves executing absolutely blind, backward physical wiring! Permanently burn this rule deep into your retinas: The transmitting TX muzzle terminal exiting the local processing Microcontroller Must absolutely be strictly cross-wired surgically inserting directly into the localized external receiving RX ear of the foreign target payload device (Execute a full signal swap). Catastrophically attempting blindly jamming two screaming TX signals directly colliding head-on actively creates an impossible paradox and permanently zeroes all communication probabilities guaranteeing total system blackout!
- Absolute Prohibition Evading CPU Suicide Utilizing Polling Under Massive Data Loads: Contained inside the stripped down minimal code illustration featured above, we purposely deployed the dreaded
whileexecution loop physically chaining the execution thread monitoring silicon data transmission states (Categorizing as the Polling Architecture), successfully intentionally vaporizing absolutely massive margins capturing critical CPU execution bandwidth preventing processing alternate external matrices. If your operational objective dictates recklessly flooding and blasting vast payload megabytes ripping aggressively spanning SPI or UART pipelines, it is unconditionally mathematically mandated that you rip out polling and pivot demanding usage deploying asynchronous Interrupt logic interceptors, or calling utilizing the unyielding heavy armor characterizing DMA (Direct Memory Access) matrix accelerators. These extreme architectures successfully outsource aggressively orchestrating all physical low-level background data traffic pushing it onto localized secondary peripheral silicon, surgically electing simply dropping a single wake-up ping onto the sleeping main CPU strictly precisely at the exact nanosecond payload transfer achieves absolute conclusion. - Surviving Stealth Hostile Collisions Enacting Race Conditions Across Shifting I2C Architecture: Predicated upon the mathematical foundation dictating the I2C geometry fiercely fighting sharing operating precisely over exactly the identical localized data artery (SDA) serving simultaneously parsing dual transmission/reception data-states (Simulating Half-Duplex configuration boundaries), the core executing logic responsible sequencing writing parameters and extraction phases must be phenomenally rigidly structured utilizing advanced State Machine logic matrix queues! Engineers require remaining completely hyper-vigilant dodging destructive hostile overlapping executions originating spawning from random background Interrupt storms (Sustaining Critical Section firewalls). Failure here mathematically guarantees the precision synchronized logic conversation chain (ex: Inject Address Sequence -> Fire Target Data -> Blast Execution Stop trigger) gets violently violently smashed out of order creating localized data destruction corrupting the entire transmission matrix layout.
- Reject Arrogant Attempted Software Bit-Banging Re-Invention Outside Massive Desperation: The explicit moment project parameters compel your logic to establish protocols locking data exchanges involving remote I2C sensors or demanding extracting high bandwidth SPI geometry, unconditionally default utilizing the silicon Peripheral Hardware accelerator specifically burnt directly inside the microcontroller template architecture. Arrogantly attempting manual logic software translation writing C-code mimicking toggling GPIO voltage rails manually (The Bit-Banging procedure) acts catastrophically dragging terminal code operating execution speeds directly spiraling towards zero, collapsing performance dramatically! Furthermore, this hack exponentially elevates risk vectors ensuring you critically and easily catastrophically violate the terrifyingly rigid, infinitesimal universal protocol timing parameters (Shattering established logic Clock Stretching tolerances), shattering connection reliability entirely.
Conclusion
Aggressively analyzing the overarching structural overview defining how we execute localized Hardware Interaction, these rigid Serial Bus communication pipelines effectively translate representing identical localized “Universal Diplomatic Languages.” The microscopic silicon chips utilize precisely these pipelines transmitting telemetry desperately trying manipulating the physical external reality extending far past local board perimeters! Cultivating the elite execution engineering wisdom to quickly mobilize UART geometry pursuing simplified, incredibly rapid, transparent firmware debugging terminals; rapidly altering trajectory unsheathing the SPI protocol operating parameters immediately reacting addressing aggressive project parameters demanding absolutely blistering, maximum velocity logic thresholds; or strategically calculating retreating deploying intelligent I2C geometry when forced combating logic matrices necessitating networking clusters managing twenty rogue localized sensors whilst fighting aggressively to eliminate redundant wire traces—constitutes the absolute zenith defining architectural mastery distinguishing elite embedded-systems engineering specialists ensuring components optimally align structurally supporting the explicit tactical program.
Our command matrix holds supreme expectation this exact forensic autopsy penetrating macro Serial Bus architectures definitively illuminated the structural complexities clarifying visibility analyzing complex local data-port integrations effectively, developers! Has any developer within this operating network suffered the horrifying existential dread resulting executing a flawless I2C loop geometry only encountering agonizing failure directly triggered entirely by forgetting physically soldering the required passive Pull-Up logic resistors dragging voltage lines down sending the board screaming randomly into an apocalyptic locked death-state void? (The Dark-Eyed Engineer personally survived that specific nightmare shedding real tears! 😅) Do not permit hesitation stopping your squad dropping into our operating rally point! Share those horrifying phantom debugger anomalies and detonate explosive technical C debates stationed directly at the localized command structure www.123microcontroller.com! Stand by for rapid deployment executing our subsequent intensive hardware logic article parameters. Stay heavily locked, and execute your Embedded Bus streams flawlessly, cyber-warriors!