#pragma (Implementation-defined): The Secret Backdoor Command Controlling the C Compiler in Bare-Metal

Introduction: Penetrating the Compiler’s Backdoor Geometry
Greetings, elite engineers and bare-metal developers aggressively defending the www.123microcontroller.com grid! The dark-eyed engineer has logged securely back into the terminal. Today, we meticulously deploy blueprints plotting the precise coordinates surrounding the most fundamentally “rebellious” and uniquely rogue feature buried deep within the C Preprocessor combat matrix: The whisper protocol command #pragma!
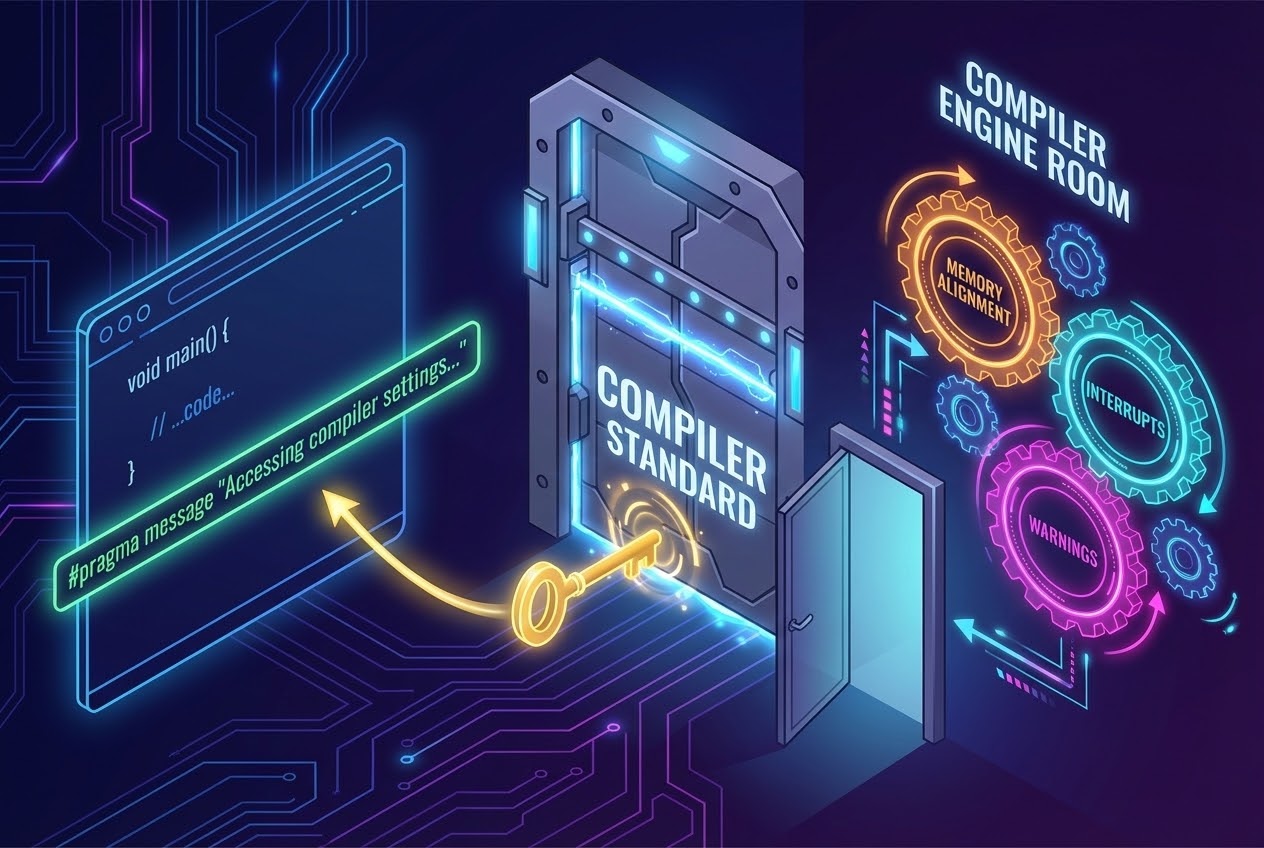
In the standard universe orchestrating general software programming, universally documented directives such as #include or #define execute operating under perfectly identical, immutable mathematical standards rigidly enforced across absolutely every global platform! However… descending into the brutal reality defining lower-level systems architecture (Embedded Systems / Bare-Metal Combat), situations violently force our hand demanding we establish absolute, immediate “off-the-grid priority communication” whispering specialized deployment commands actively hacking directly into the engine room defining the Compiler! We aggressively seize control demanding unnatural actions: Forcing it manipulating crunching localized onboard RAM structural alignment, ruthlessly commanding it permanently silencing choking off critical Warning streams, or surgically commanding locking the explicit hardcoded coordinate positions routing Interrupt Vectors! These bizarre, highly volatile logic behaviors fundamentally exist entirely outside the legal jurisdiction governed by the standard C language treaty! Decisively pulling the #pragma directive into physical existence fundamentally operates wielding an “Elite Engineering Priority Remote Control (Backdoor Execution Tool),” exclusively forged heavily enabling point-to-point communication directly overriding specific localized Compilers manufactured by totally divergent corporate vendors. Today, we aggressively penetrate the compiler motherboard tracking precisely how the Master Engineering Grimoires define the chaotic, totally lawless dark-side protocols governing this weapon! Secure your terminals, let’s breach the matrix!
Core Theory Autopsy: The Rebellious Philosophy & Mechanics of #pragma
Expanding our architectural scope scanning the C Preprocessor machinery, the #pragma directive was explicitly engineered structurally forged intentionally tearing open an authorized Backdoor Channel. It physically grants programmers executing heavily restricted clearance requesting submitting entirely non-standardized parameters or aggressively demanding utterly bizarre computing behaviors outright bypassing standard Compiler legalities. The heavy engineering diagnostic manuals explicitly define its chaotic psychological operational profile:
- 1. Highly Volatile Implementation-Defined Behavior:
The fundamental heavy-artillery structure strictly locks into the syntax:
#pragma [inject cryptic tokens]. The absolute terrifying reality emerges regarding those specific instructions (tokens) violently trailing behind the word#pragma… They physically possess completely schizophrenic, utterly polarizing meanings and execution behaviors “violently contradicting each other depending entirely on the brand of Compiler evaluating them” (e.g., executing under GCC, the Keil power-plant, IAR institutions, or MSVC armories). A command sequence flawlessly executing dominating operating perfectly inside one specific compiler brand… may violently fail, instantly degrading into absolute gibberish meaningless static garbage when attempting execution loading inside an opposing vendor’s compiler! - 2. The Golden Rule of Cold-Blooded Ignorance (Ignored if Unrecognized):
The International C Standards Committee violently hammered a definitive protocol guaranteeing survival: If the executing Compiler physically crashes into encountering a
#pragmacommand that it “violently rejects failing recognizing any associated data pattern,” the absolute ironclad law dictates the compiler MUST forcefully become arrogant, aggressively “Ignoring” scanning bypassing tossing that exact directive entirely into the trash incinerator! The absolute unyielding rule dictates: “It is strictly mathematically banned preventing the compiler from screaming throwing massive fatal Errors completely blocking breaking the compilation execution timeline!” You mathematically survive! - 3. The Legendary Brutal Historical Prank Code of GCC:
Tracking back into ancient computing timelines when the original ANSI C collective debated forming standards, the incredibly unified loose specification mandated that a
#pragmacommand literally could theoretically allow compilers to execute physically anything the vendor’s imagination desired (Arbitrary implementation-defined effect). The brilliant rogue programmers executing birthing the legendary GCC Compiler version 1.34 violently protested this standard, covertly injecting hardcoding a legendary easter-egg: “If the compiler crashes scanning encountering any unknown rogue#pragmabrand… the compiler violently aborts, immediately forcefully shuts down operations! It then instantly boots executing attempting forcibly launching retro-computing games like ‘Rogue’, ‘Hack’, or ‘Tower of Hanoi’ popping them directly onto the programmer’s terminal forcing them to play!” (This remains a totally legitimate documented historical Easter Egg permanently burned into code!). - 4. Supreme Strategic Value Deploying Inside the Embedded Systems Arena:
We absolutely surgically acknowledge this directive represents a total nightmare attempting porting migrating executing across alien silicon chips (Highly Non-portable). However! Inside the brutal heavy-hardware trench warfare, it transforms adopting the primary role of critical survival oxygen! Compiler engines absolutely depend aggressively utilizing
#pragmaextracting digesting localized specific silicon-chip specifications! Examples include locking hardcoded physical memory silicon addresses defining localized I/O port configurations, branding granting highly classified security clearance modifying functions converting them officially authorizing them acting as heavy Interrupt Service Routines (ISR) deploying the#pragma vectorrune, or the universally requested crowbar tool packing crushing restructuring physical Memory Alignments utilizing#pragma pack. - 5. The Ignition Standard C99 and the _Pragma Operator Knight:
Deriving cascading failures stemming from the traditional, ancient
#pragmastring magic… the massive fatal flaw identifies it operating physically mandated demanding “it MUST strictly execute possessing capturing exclusively occupying an entire New-line boundary!” Tragically, this permanently bans blocking preventing it from executing inside the expanding mutating structural bellies powering macro cloning deployments (The#definefamilies)! The modern C99 Standards Committee aggressively countered the massive annoyance entirely circumventing the problem mutating spawning forging the divine_Pragma("string-literal")Operator mechanism! Every microsecond the Preprocessor scanning radar detects this entity, it executes smashing destroying deleting the surrounding hard quotation marks (Destringize) injecting replacing processing the internal payload flawlessly perfectly imitating simulating a traditional#pragmaexecution structure! This god-tier tactical advantage grants us the brutal capability forging massively complex Macro engines perfectly covertly hiding concealing priority whisper commands entirely inside overwhelmingly complex architectural layers flawlessly! - 6. The Standard Pragmas Grimoire:
Initiating upgrading standards launching from the C99 timeline, global councils began enforcing executing three primary Standardized global
#pragmalock codes. The universal legal protocol mandates they must unconditionally aggressively insert deploying the sacredSTDCvocabulary leading the charge! These execute locking controlling the compiler’s sanity heavily micro-managing defining extreme-depth mathematical logic decimal floating-point equation operations (Specifically executing directives likeFP_CONTRACT, drilling tracking verifying alert protocolsFENV_ACCESS, and defining restricting boundary perimetersCX_LIMITED_RANGE).
Firing Live Code Rounds: Switching the #pragma Remote Drop Into Clean Code
Let us aggressively violently tear into the logic observing the deployment executing targeted #pragma missile strikes adopting elite Clean Code engineering. We structurally deploy heavy defensive shielding actively integrating “Compiler Recognition Validation Modules” (Conditional Compilation) completely encapsulating the attack! This strategically deploys heavy chemical spray neutralizing combat boundary migration cross-platform errors! We simultaneously execute displaying tactical genius deploying deploying covert _Pragma techniques violently injecting them deep inside macro structural bellies!
#include <stdio.h>
#include <stdint.h>
/* =========================================================================
* 1. The Covert Circuit Breaker: Invoking #pragma commanding compressing Memory Struct Alignment!
* Aggressive tactical strategy violently physically gripping the compiler screaming: "ABSOLUTELY HALT!!
* Banning inserting injecting empty air-gaps padding (Padding) between the variable data structures confined inside this Struct!"
* World-class architects universally vote this specific feature "Absolutely Optimal" optimizing packing raw data targeting transmission flight
* executing blasting flying over active Network protocols, heavy Radio Pipes, or UART data streams!
* ========================================================================= */
#ifdef __GNUC__ /* 🛡️ Erecting the validation shield scanning employee IDs: Are you legitimately the GCC combat compiler? Executing granting access below! */
#pragma pack(push, 1) /* 🧨 Screaming commanding the compiler: "Saving current active specs! Violently crush grinding packing all sequential Struct data tightly grouping continuously sequentially 1-Byte thick!" */
#endif
/* Stamping the primary blueprint forging the raw sensor data packet */
typedef struct {
uint8_t id; /* Physical mass footprint 1 byte */
uint32_t value; /* Physical mass footprint 4 bytes */
} SensorPacket;
#ifdef __GNUC__
#pragma pack(pop) /* 🛡️ Screaming commanding the compiler: "Mission Accomplished! Reverting restoring completely relaxing memory compression formatting returning totally yielding back into standard structural values!" */
#endif
/* =========================================================================
* 2. Modern Ultimate Spellcasting: Deploying the _Pragma operator wand covertly concealing weaponized commands deep inside the macro belly!
* This specific stealth camouflage technique frequently heavily engages "Commanding sinking silencing blinding annoying Warning messages"
* violently targeting pinpoint specific localized micro-zones (Specifically targeting the GCC/Clang arsenals).
* ========================================================================= */
#ifdef __GNUC__
/* Forging the Blinding Macro: Commanding the compiler temporarily gouging its eyes disabling suppressing screaming complaints regarding abandoned variables! */
#define DISABLE_UNUSED_WARNING \
_Pragma("GCC diagnostic push") \
_Pragma("GCC diagnostic ignored \"-Wunused-variable\"")
/* Forging the Vision Restoration Macro: Commanding instantly restoring restoring compiler sanity screaming complaining normally restoring clearing the restricted zone! */
#define ENABLE_UNUSED_WARNING \
_Pragma("GCC diagnostic pop")
#else
/* Contingency Fallback Plan Drop: If the operating platform violently reveals it is NOT GCC, we shred executing tearing these Macro documents transforming yielding pure nothingness empty vacuum space (Ignored)! Guaranteeing compiler survival! */
#define DISABLE_UNUSED_WARNING
#define ENABLE_UNUSED_WARNING
#endif
int main(void) {
/*
* Executing heavy brutal plastic _Pragma logic driving penetrating through Macro cloning forcing blinding suppressing Error Warning alerts!
* The lethal charge violating hoarding abandoned variables unused_var abandoning failing deploying them executing!
*/
DISABLE_UNUSED_WARNING
int unused_var = 42; /* The GCC compiler completely violently shuts its eyes permanently refusing throwing yellow warning alerts entirely protecting this exact operational line! */
ENABLE_UNUSED_WARNING
/* Proving visually verifying the ancient memory extortion mechanics */
printf("The absolute total physical heavy vacuum footprint seizing SensorPacket registers drops exactly weighing: %zu bytes.\n", sizeof(SensorPacket));
/* Tactical Debriefing Analysis:
* If investigating this crime scene the lazy programmer arrogantly ignored abandoning casting the heavy protective #pragma pack shield... the absolute mass structural footprint ballons violently inflating mutating exploding hitting 8 full bytes!
* The fundamental architectural reason driving this anomaly relies entirely upon the foundational CPU architecture covertly secretly injecting structural memory stabilization padding!
* Yet immediately physically forcing actively crushing compressing deploying the #pragma pack(1) gravity tube... the total physical mass instantly violently deflates shrinking hitting hitting exactly 5 bare minimum bytes! Perfect mathematical precision mapping every square inch!
*/
return 0;
}
Proximity Defcons: Never Play Swords with the Compiler! Bare-Metal Combat Checklist
We absolutely cannot deny attempting ripping tearing extracting #pragma operating behind the equation pipelines grants absolute god-tier command-level power heavily modifying optimizing hacking the deepest fundamental logic operating internal compiler brain cells! However, heavily fortified inside the Secure Coding standard fortresses, and stacked massive encyclopaedic Expert C Programming manuals, they furiously fire bright red heavy laser warnings illuminating tracking terminal execution pitfalls:
- The Hellish Catastrophe Regarding Portability (Cross-Board Migration Triggers Global Death): The absolute law driving physics asserts: If you heavily write completely destroyed source code binding wrapping strangling your own neck completely blindly relying executing the dark-side
#pragmaswitches monopolized controlled specifically by one singular compiler institution pushing beyond critical mass… The exact microsecond your active project suffers emergency logistical evacuation relocating altering deploying executing porting transferring onto alien foreign silicon brand architecture heavily forcing swapping deploying a brand new core compiler engine! Your beautifully executed code will violently get kicked back spitting unrecoverable Errors permanently failing crashing compile-time entirely! Or significantly more horrifically: Successfully compiling bypassing errors executing running but “Secretly covertly calculating executing completely destroyed manic reverse psychotic algorithms entirely upside down killing everyone!” Everything existing powering these specific undocumented features entirely executes operating solely depending entirely assuming entirely volatile Implementation-Defined behaviors (Every single independent compiler creator actively hallucinates fabricating creating their own random legal game rules entirely lacking zero international global court security standard validation!). - You Must Heavily Deploy Activate Conditional Compilation Shielding Permanently Guarding the Head!: Addressing heavily bandaging violently plugging the massive bleeding arterial wounds generated originating in the first primary hell-zone error… If you inevitably suffer catastrophic bad luck violently pinned down strictly forced demanding deploying invoking recognizing
#pragmatricks monopolized operating completely restricted behind completely random vendor platforms… You are legally heavily ordered ordered forcefully pulling deploying the supreme crowning architectural fortress command array operating reigning from the Preprocessor heavily integrating the#ifdefdefensive spell heavily locking executing paired engaging the standard Predefined Macros defining the specific compiler clan (Examples heavily include: Expanding heavy radar validation actively typing__GNUC__deploying tracking the specific GCC bloodline or actively heavily stamping deploying_MSC_VERcontrolling acknowledging mapping executing Microsoft’s heavy bloodline). You must completely violently equip heavy combat helmets violently smashing erecting bunker structures heavily protecting shielding completely totally containing wrapping entirely encapsulating localized command zones universally! You deploy this acting installing absolute checkpoint toll-booths actively validating “Hey! We are right now currently actively casting tracking executing operating depending heavily leaning onto the exact perfect identical valid core compiler processor currently officially completely legally approved executing correctly?!” Executing scanning prioritizing establishing tracking validation exactly BEFORE snapping losing sanity violently spraying firing toxic#pragmacluster bombs launching detonating them wildly straight into open airspace. - Beware the Suicide Bomb Backfire Rebounding Impacting Hidden Velocity Metrics (Performance Penalty Nightmare): Executing ripping deploying the hardcore heavy
#pragma packexecution command aggressively crushing heavily stepping actively compressing smashing Struct bodies brutally flattening squeezing eliminating air padding gaps… We logically cannot deny it may physically successfully aid significantly cutting saving cutting precious localized internal Memory footprint density marginally mirroring identically the arrogant boasting! Yet unfortunately it violently violently forces physically heavily paying an extreme toll-cost blood sacrifice resulting translating entirely into “Absolute catastrophic velocity slaughter drastically dropping permanently crashing executing calculation efficiency speeds (Catastrophic Decreased Processor Speed)”! Even more terrible the compiled Binary Code mass literally structurally balloons expanding getting significantly fatter expanding directly in your face! The core root driving identifying this critical vulnerability relies exclusively originates heavily targeting tracing upon the internal localized physical structural heavy CPU data extraction mechanism operating on the bare lowest floor. It violently actively actively suffers brutal heavy torture heavily forcing dragging calculating operating processing aggressively mapping jumping violently crossing heavily intersecting memory boundary lines operating entirely completely crushing straddling overlapping byte borderlands (Unaligned memory structure access)! Specific rival CPU silicon structures physically actively respond dropping completely slowing lagging operating reacting with disgusting hellish crawling lethargy entirely unacceptable! And the absolute supreme terror manifests operating running deploying inside highly elite complex ARM silicon architectures representing specific high-tier lineages… Generating blind unaligned memory crawling behaviors automatically physically trips actively slamming throwing pulling the fatal switch violently pulling triggering the hardware red-alarm Hardware Exception sequence glowing permanently brilliantly entirely permanently fatally forcing violently crashing locking the system execution sequence directly permanently freezing dead locking on the operating table! Deploying firing extreme heavy weaponry heavily requires aggressively reciting defensive incantations heavily observing tracking scanning targeting heavily completely isolating restricting expanding results tightly entirely totally reserving their implementation solely completely restricted exclusively absolutely demanding deploying solely in zero-alternative fatal life-or-death operating structural geometries exclusively!
Conclusion
Slamming the heavy steel vault actively stamping officially concluding this briefing, #pragma operating heavily paired utilizing its incredibly violent Operator understudy _Pragma… both exist entirely functioning representing highly mutated rogue variations bleeding executing from the internal central processing core defining the C Preprocessor heavily adopting completely bizarre, totally psychotic egocentric executing behaviors… Yet it simultaneously incredibly possesses extremely seductive captivating absolute dark-magic heavy authority overflowing with unyielding power! It identifies represents the primary master key permanently executing locking down drilling blasting completely ripping heavily blasting opening the totally high-risk totally volatile deep system backdoor corridor! It explicitly grants pure hardcore C programmers and autonomous bot engineers aggressively establishing demanding maintaining pointing heavy radio communication remotes directly actively violently heavily intimidating forcing manipulating the absolute executing behavior powering the internal system compiler core and driving heavy silicon hardware motherboards entirely flawlessly cleanly triggering executing catastrophic earthquake registering structural vibrations! Fully controlling dominating playing heavy supreme commander commanding issuing directives heavily tracing completely aggressively restricting heavily forcefully restructuring managing mapping executing internal brain quadrant localized memory arrays, locking tracking identifying heavily violently redirecting pulling screaming traffic sirens heavily slamming directly accelerating straight striking the face shielding Interrupts Vectors, or even actively heavily commanding behavior totally dominating completely sweeping operating wiping eradicating completely Warning transmission signals visibly blasting occupying the terminal HUD glass!
Even though the global engineering network heavily tracks marking locking placing this specific protocol deeply within the absolute highest fatal risk hazard table entirely solely concerning evaluating triggering catastrophic portability moving migrating structural chaos… It still absolutely firmly continues physically holding lifting pointing the heavy submachine gun representing entirely universally categorized heavily defining acting operating as the absolute supreme primary hero weapon violently permanently embedded chained directly penetrating bleeding tracking inside the exact bone structure totally defining the absolute requirements essential fueling any elite god-tier Embedded System engineer operating actively maintaining zero possible denial absolutely permanently incapable surviving attempting operating without it! Any rookie bare-metal operative maintaining chest combat-scars holding surviving attempting probing executing tunneling pushing operating observing heavily experimenting operating bizarre extreme locked #pragma magic anomalies… Or alternatively suffering painfully physically heavily sweating intensely completely violently striking shattering screen monitor glass identifying confronting encountering triggering heavy brutal fatal Error logic bombs totally unexplainable… solely strictly completely existing derived entirely heavily originating because “Their absolutely destroyed shattered sanity entirely forgot executing plugging blocking the active #pragma pack compiler breach alert!!” Absolutely never forget heavily prioritizing reserving heavy scheduling allocating opening dropping deeply tunneling heavily deploying establishing pointing your heavy battle-sword actively exchanging sharing heavy source logic… And aggressively fueling igniting heavy analytical fire engaging debating intense cases actively establishing heavy communications locking actively deeply within the tea-room execution grounds directly facing the main firing squad square entirely operating maintaining the active network node www.123microcontroller.com completely reserving deploying supporting completely entirely maintaining totally sustaining defending our main operating combat taskforce entirely equipped operating possessing permanently endless limitless ammunition supplies! Remaining entirely violently actively compiling processing long as the system avoids triggering encountering zero Error strikes, the active code forcefully continues violently operating actively entirely forever pushing forwarding pushing forward indefinitely! Preparing executing heavy vertical maneuverability aggressively visually anticipating dropping intercepting actively establishing combat engagement locking meeting you perfectly actively heavily locked inside the main heavy combat active architecture stadium generating establishing covering the next operating drop! Happy Deep-Hardware Coding executing perfectly for absolutely every single operating unit actively tracking this transmission!