Out-of-bounds Array Access: Escaping Memory Boundaries and Triggering Deadly Undefined Behavior
Out-of-bounds Array Access: The Gateway to Undefined Behavior
Hello fellow engineers and developers at 123microcontroller.com! After extensively exploring the terrifying realities of “Undefined Behavior (UB)”, today we will heavily dissect one of the most prolific and dangerous causes of UB in the C programming language: “Out-of-bounds array access”.
In the aggressive ecosystem of hardware and Embedded Systems—where memory (RAM) is a strictly limited and precious resource—managing Arrays and Pointers is our daily reality. But did you know that accidentally reading or writing data just exactly 1 byte beyond the defined edge of an Array could permanently crash your microcontroller board, corrupt critical operating logic, or blow open a massive security vulnerability for hackers? Let’s dive deep into exactly how this mistake connects to Undefined Behavior, and why the standard C Language fundamentally allows these devastating exploits to exist.
Core Concept: Out-of-bounds and the Context of Undefined Behavior
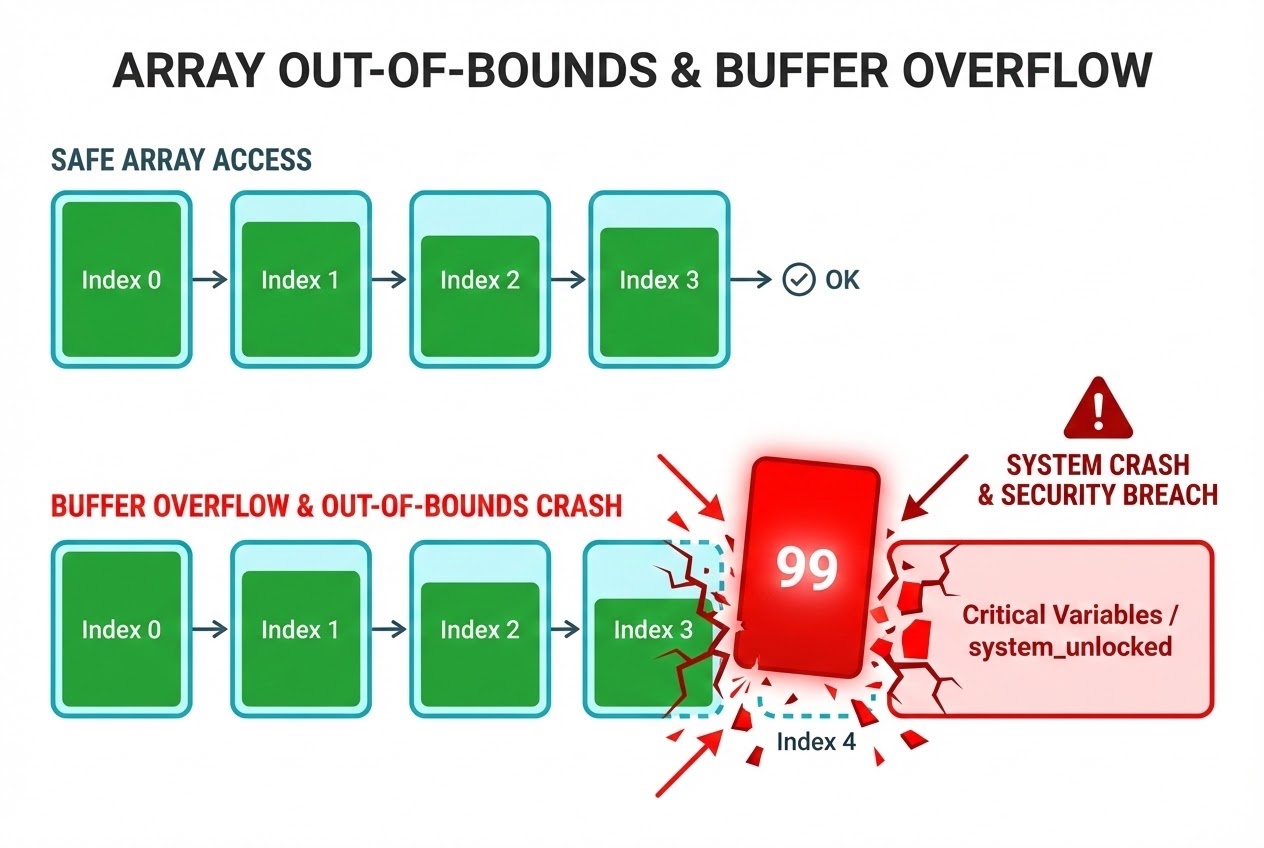
A brilliantly simple analogy is viewing an Array in C exactly like “a row of interconnected mailboxes.” If we declare and reserve 5 specific mailboxes (officially spanning Index 0 to 4) but accidentally inject data into the 6th mailbox (Index 5) or mathematically target a reverse mailbox (Index -1), we are outright invading someone else’s mailbox! In standard C terminology, this reckless operation is called Out-of-bounds access, and the C Standard explicitly categorizes this action as immediate Undefined Behavior (UB).
Why does C tolerate the existence of such a deadly trap? Architectural experts provide the following fundamental reasons:
- The “Trust the Programmer” Philosophy and Absolute Speed: The C language was explicitly engineered to extract maximum execution speed (Efficiency) while maintaining an incredibly small footprint. Forcing the Compiler to auto-inject hidden instructions to continually perform Bounds checking every single time you query a dynamic Array at runtime would inherently introduce massive Overhead—inflating both the compiled machine code size and aggressively burning CPU cycles. C thus “trusts” that a competent programmer will invariably calculate Array limits flawlessly.
- Pointer Arithmetic and Memory Layout Geometry: In C, referencing a traditional Array syntax like
arr[i]intrinsically decays into pure internal Pointer Arithmetic:*(arr + i). Standard rules assert that calculating or forcing a Pointer to point past the legally assigned Array boundaries (with the sole exception of pointing exactly “one past the last element”) strictly summons UB. - Highly Unpredictable Reactions (The Consequences of UB): When Out-of-bounds operations trigger, the compiled program might deceivingly appear to behave perfectly normal, securely pull out and calculate Garbage/Junk values, or trigger an aggressive operating system Crash.
- The Devastating Escalation to Buffer Overflow: This is astronomically the most severe consequence within System Programming. Executing an Out-of-bounds write instantly triggers a Buffer Overflow. The overflowing rogue data naturally overwrites adjacent, structurally distinct variables. More frighteningly, if the targeted Array resides dynamically on the Memory Stack, the overflow could cleanly overwrite a function’s critical Return Address! This provides hackers the exact mechanical vector needed to hijack the program’s execution flow and execute malicious Arbitrary code.
C Code Example
Let’s meticulously inspect a classic bug that routinely strikes microcontroller code when a sleepy developer forgets that Array indexing strictly begins at 0 (Zero-indexed).
#include <stdio.h>
int main(void) {
/* Imagine this critical variable stores the core security status of the system
(e.g., whether a physical safe is locked or unlocked). */
int system_unlocked = 0;
/* Declare an Array securely limited to exactly 4 distinct slots (Indices: 0, 1, 2, 3) */
int sensor_data[4] = {10, 20, 30, 40};
/* ❌ FATAL FLAW: Out-of-bounds access / Undefined Behavior.
The programmer carelessly utilized '<=' instead of strictly '<',
forcing the iteration to target Index 4, which structurally DOES NOT EXIST
within the confines of sensor_data. */
for (int i = 0; i <= 4; i++) {
sensor_data[i] = 99; // When i=4, the value '99' overflows massively out of bounds!
}
/* On a vast majority of Compilers, the critical 'system_unlocked' variable
will be memory-allocated physically adjacent to 'sensor_data'.
The rogue memory overflow in the loop structurally overwrites the value
of 'system_unlocked', forcibly unlocking the system entirely by accident! */
if (system_unlocked) {
printf("DANGER: System is UNLOCKED due to Buffer Overflow!\n");
} else {
printf("System is SECURE.\n");
}
return 0;
}
Secure Coding & Best Practices
To actively plug these disastrous vulnerabilities and isolate our hardware systems from UB Out-of-bounds attacks, Secure Coding directives universally mandate the following rigid defenses:
- Programmers Must Calculate Bounds Manually (Manual Bounds Checking):
Because C refuses to check inherently, the burden correctly falls on us. Before injecting any dynamic variable (especially unfiltered data parsed from a human User or physical Sensor parameters) into an Array Index query, you MUST enforce structural
iflimits ensuring the requested value strictly exists between0andARRAY_SIZE - 1. Always utilize#defineor specificconstvariables to establish immutable Array dimensions for vastly elevated safety. - Pass Absolute Dimensions With Arrays (Pass Size with Array):
Mechanically, when an Array is dispatched into a function parameter, it dangerously loses its dimensional identity and ‘Decays’ into nothing but a raw Pointer aiming at the initial index. The receiving function natively has zero idea how long the actual original Array is! It is absolutely critical you always ship a secondary parameter capturing the dimension (e.g.,
size_t size) so the target function can legally execute Bounds checking. - Terminate Unsafe Functions (Avoid Unsafe Functions):
Permanently cease usage of historically lethal functions like
gets(). It is arguably the most notorious originator of Buffer Overflow exploits. Architecturally swap it forfgets(), or integrate advanced functions native to C11 Annex K Bounds-Checking Interfaces (characterized prominently by the_ssuffix, such asgets_s,memcpy_s,strcpy_s). These optimized utilities forcefully require Buffer dimensions as parameter inputs, massively heightening embedded security.
Conclusion
Mechanically executing an Out-of-bounds access is not a benign, isolated glitch—it is ripping open an expansive gateway directly into Undefined Behavior. This glitch functions akin to a microscopic digital timebomb quietly waiting to violently destabilize both the logic and the physical security of your rigid Embedded systems. Unlocking a deeper comprehension of C’s architecture—which actively prioritizes raw blistering speed by intentionally offloading security checks entirely onto the developer’s shoulders—will mechanically fortify your coding habits and push you solidly into the realm of professional System Developers.
If you are electrified by discovering these hardcore Secure Coding practices, or desperately want to dissect more complex memory management mechanics deep inside microcontrollers, ensure you routinely visit our expanding knowledge base and discussions at www.123microcontroller.com. See you all in the next exhaustive tutorial. Happy Coding!