Operator Precedence: When C's Order of Operations Defies Human Logic (Counter-intuitive Syntax)
Operator Precedence: When C’s Order of Operations Defies Human Logic
Hello fellow engineers and developers at 123microcontroller.com! Today, we are going to dive into a topic that has forced countless hardware programmers to pull their hair out and aggressively debug late into the night: Operator Precedence (or the mathematical Order of Operations).
Since elementary school, we were universally taught that multiplication and division strictly execute before addition and subtraction. However, in the vast ecosystem of the C programming language—which wields an arsenal of operators spanning 15 distinct priority levels—there exists specific syntax behavior that is violently “counter-intuitive” and actively defies human logic. Today, let’s dissect the historical reasons behind why legendary programming masters assert that C harbors “wrong” operator precedence, and how we must professionally handle these traps within Embedded Systems!
Core Concept: A Historically “Flawed” Precedence
The absolute reality is that C’s counter-intuitive syntax is not simply our minds misunderstanding complex logic; it is a globally acknowledged historical flaw! Even the founding fathers of the C language, Brian Kernighan and Dennis Ritchie, explicitly confessed in their legendary book The C Programming Language: “Some of the operators have the wrong precedence.”
These logic traps stem from a “historical accident” born during the agonizing transition from C’s predecessors, B and BCPL. Elite programming sources highlight the most notorious counter-intuitive precedence conflicts that routinely sabotage hardware logic:
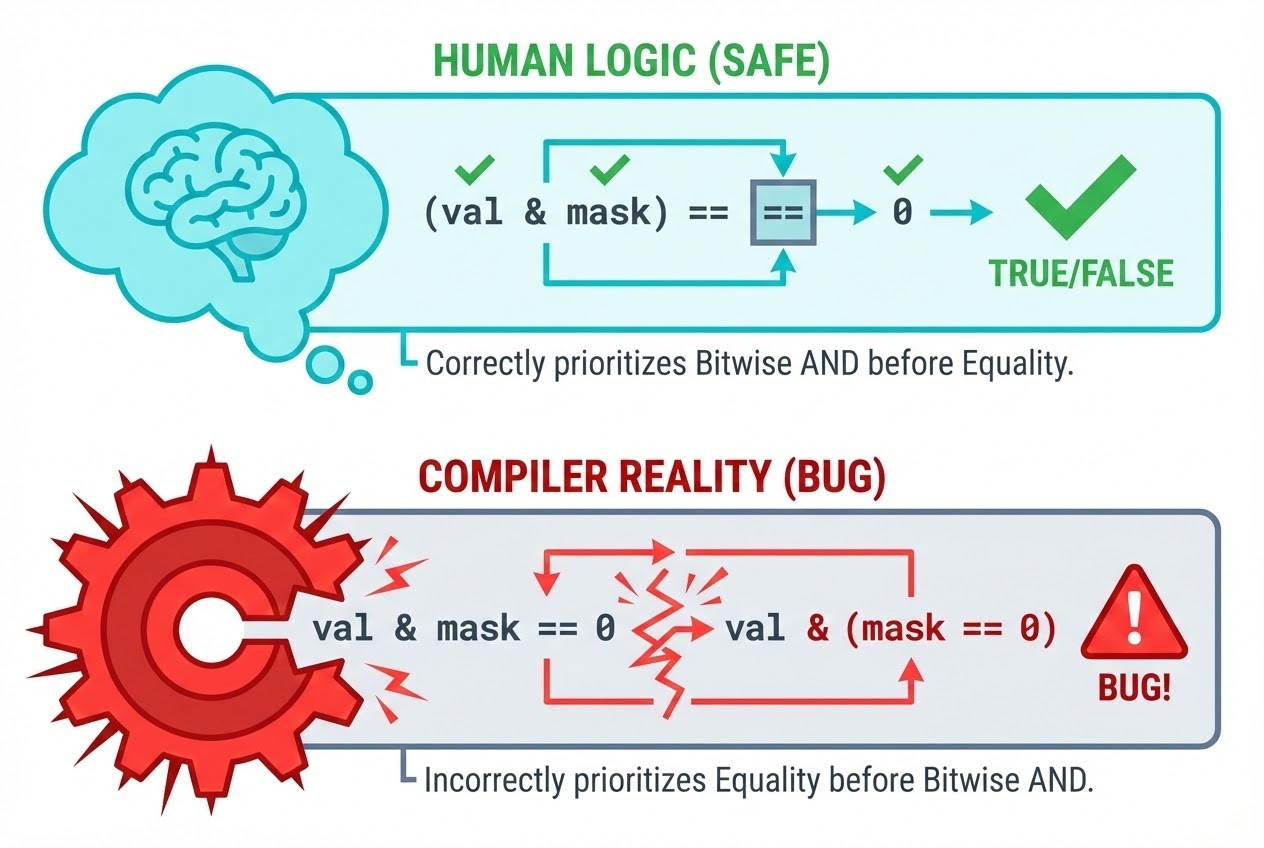
- 1. Bitwise Operators plunge below Equality (
==,!=): When we read a hardware Register and want to Verify a specific bit using a Bitwise Mask, human intuition directs us to writeval & mask == 0. We logically expect it to evaluate(val & mask)first, and then compare the result to 0. Tragically, in C, the==and!=operators command a higher priority than&. The compiler actually executesval & (mask == 0)—instantly ruining the logic! Dennis Ritchie later explained that early versions of C lacked the&&and||operators, so programmers relied entirely on&and|. When the logical operators were eventually introduced, Ritchie desperately wanted to elevate the precedence of the Bitwise operators, but backed down out of sheer terror that doing so would instantly destroy hundreds of kilobytes of existing production code. - 2. Shift Operators sink below Arithmetic (
+,-): When concatenating hardware bytes (for instance, shifting the MSB left by 4 bits and adding the LSB), developers frequently typemsb << 4 + lsb. Shockingly, Mathematical addition fundamentally outranks Bitwise shifting. The Compiler aggressively alters this tomsb << (4 + lsb), resulting in massively corrupted hardware data. - 3. The Dot Operator (
.) overpowers Pointer Dereference (*): If we deploy a Pointer targeting a Struct and attempt to access its inner members, blindly typing*p.fis aggressively interpreted by the compiler as*(p.f)rather than the intended(*p).f. This specific grammatical nightmare exclusively forced the C creators to invent the Arrow operator (->) simply as a rescue mechanism! - 4. Post-Increment (
++) bullies Dereference (*): The universally popular mechanism*p++(which functionally reads a value then advances the Pointer) executes flawlessly only because Post-increment (++) commands a higher structural precedence than Dereference (*). Therefore, the expression translates perfectly to*(p++). However, this exact idiom maliciously tricks C beginners into hallucinating that it means(*p)++(mathematically increasing the data that the pointer points to). - 5. The Comma Operator (
,) is Absolute Bottom Tier: Executingi = 1, 2;will absolutely not yieldi = (1, 2);. Because the Assignment operator=claims higher authority, the Compiler strictly views it as(i = 1), 2;. The variableicaptures only the1, while the2is processed and silently discarded into the void.
Code Example
Let’s meticulously analyze a simulated Sensor Register readout that tragically fails compiling due to fatal Precedence traps.
#include <stdio.h>
#include <stdint.h>
#define SENSOR_READY_MASK 0x04 // The 2nd Bit Target (0b00000100)
int main(void) {
uint8_t status_register = 0x00; // Assume the sensor is currently NOT ready
uint8_t msb = 0x0F;
uint8_t lsb = 0x02;
/* ❌ Example 1: The Devastating Bitwise vs Equality Bug */
// The programmer intends to evaluate if the SENSOR_READY_MASK bit is completely cleared.
// However, `==` outranks `&`. The compiler silently manipulates this into: status_register & (SENSOR_READY_MASK == 0)
// SENSOR_READY_MASK (4) == 0 is False (0). Therefore, status_register & 0 invariably equals 0 (False)!
if (status_register & SENSOR_READY_MASK == 0) {
printf("BUG 1: Sensor is NOT ready (or so it thinks!).\n");
}
/* ✅ Fix 1: Establish Absolute Control via Parentheses */
if ((status_register & SENSOR_READY_MASK) == 0) {
printf("FIX 1: Correctly checked! Sensor is NOT ready.\n");
}
/* ❌ Example 2: The Byte-Stitching Disaster (Shift vs Addition) */
// Human Expectation: (0x0F << 4) + 0x02 = 0xF0 + 0x02 = 0xF2
// Compiler Reality: msb << (4 + lsb) = 0x0F << 6 = 0x3C0 (Utterly Corrupted!)
uint16_t data = msb << 4 + lsb;
printf("BUG 2: Shifted data = 0x%X\n", data);
return 0;
}
Secure Coding Best Practices
To actively shield our critical hardware architecture from these silent historical logic traps, elite industry standards and masterclass books universally mandate these defenses:
- Never Attempt to Memorize the 15 Levels: The only dual rules you must burn into your mind are: 1. Multiplication and division strictly outrank addition and subtraction. 2. “Put parentheses around everything else.”
- Parentheses are Ultimate Security Shields: Simply wrapping expressions in parentheses does not incur even a microsecond of runtime performance overhead. It costs physically zero processing power, yet unequivocally dictates your explicit “intent” to both the Compiler and your engineering teammates. Legendary texts command: “When in doubt, insert ().”
- Aggressively Guard Macro Parameters: When forging Function-like Macros, the dynamically injected expressions can be violently shredded by surrounding Precedence mechanics. Therefore, every single internal parameter parameter interacting within a Macro must be heavily shielded by its own isolated parentheses.
- Abolish Micro-Optimized One-Liners: Never attempt to flex your C mastery by violently cramming
++,--,=,<<and&into a singular terrifying Statement. It generates zero hardware acceleration and violently exposes your application to catastrophic Undefined Behavior regarding the strict Order of evaluation. Breaking logic into sequential, readable micro-steps generates impenetrable code.
Conclusion
The C language functions as the undisputed engine driving optimal Embedded Systems, but it carries profound historical baggage causing specific syntactical hierarchies to aggressively defy fundamental human intuition (Counter-intuitive). Mastering the deep-rooted vulnerabilities hiding within Operator Precedence—especially surrounding the Bitwise, Shift, and Pointer paradigms—will absolutely save you from endless agonizing debugging sessions. Remember this definitive law: “Parentheses are the absolute strongest armor available in the C language.”
We truly hope this technical breakdown arms you with the foresight to write structurally impenetrable code! For those craving more highly-specialized C Language quirks or deep-dive Register manipulation mechanics, ensure you heavily engage with our community over at www.123microcontroller.com. See you all in our next hardcore debugging article. Happy Coding!