Decoding Null-Pointer Dereferencing: When a Program's End is the Beginning of Undefined Behavior Disaster
Decoding Null-Pointer Dereferencing: The Disaster of Undefined Behavior
Hello fellow engineers and developers at 123microcontroller.com! After uncovering the subtle pitfalls of Undefined Behavior (UB) in C, today we will dive deep into one of the most classic errors inexplicably linked to UB: “Null-Pointer Dereferencing”.
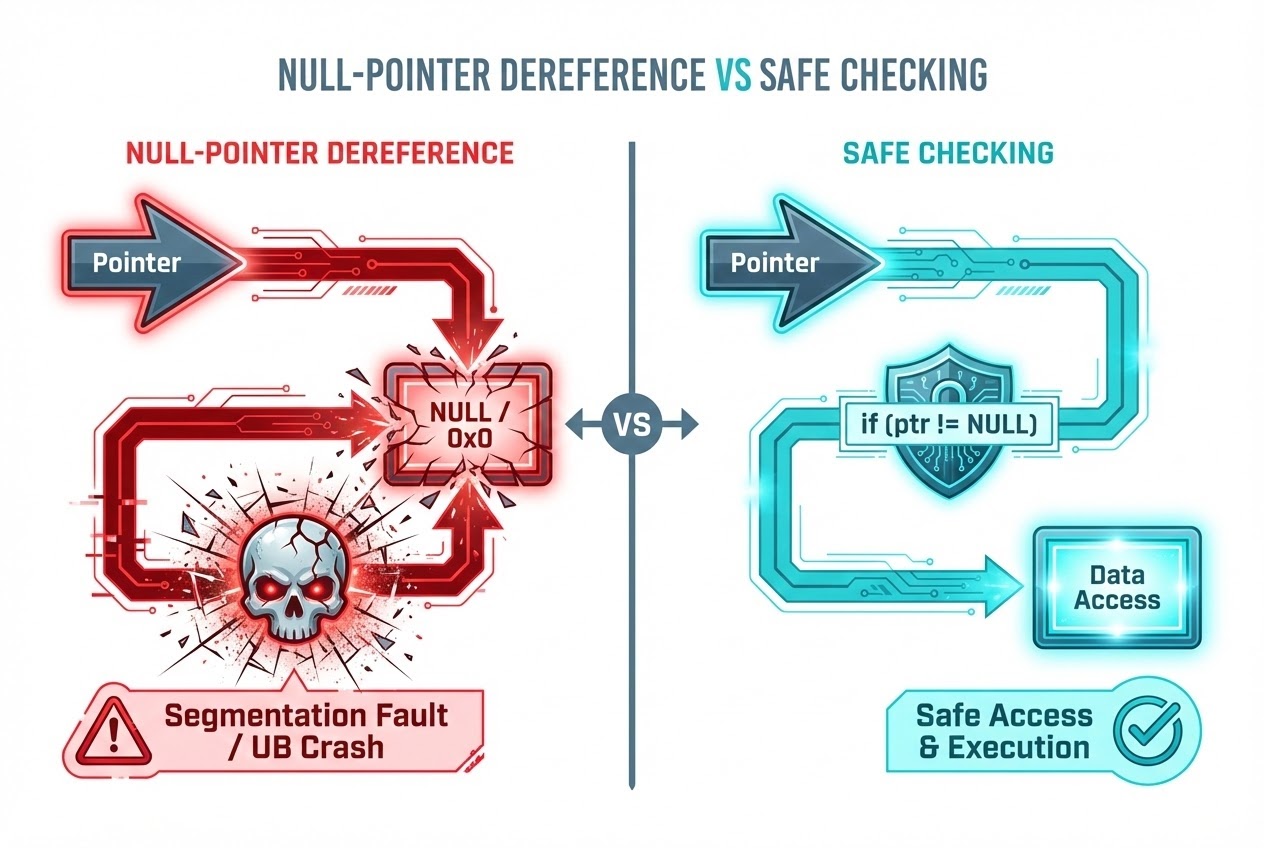
In hardware-level programming, we constantly utilize Pointers to reference specific memory addresses—much like handing the system a “home address” to retrieve data. But what happens if that address is completely “empty” or Null? Many developers assume the program simply throws a Segmentation fault and halts. However, in the realm of microcontrollers and Undefined Behavior, the consequences are far more mysterious and devastating. Today, let’s pull back the curtain on this hidden danger!
Core Concept: What is Null-Pointer Dereference and why is it UB?
Dereferencing is the act of using the * or -> operators in front of a Pointer to read or write data at the exact memory location the Pointer is targeting.
Trouble strikes when that Pointer is unequivocally a Null Pointer (frequently represented in C by the NULL macro or literal 0). Theoretically, this translates to “a Pointer that does not point to any valid object or location in memory.” The C Standard explicitly dictates that attempting to Dereference a Null Pointer results in an absolute Undefined Behavior (UB).
Once your logic enters UB territory, the Compiler washes its hands of all responsibility. The ensuing results are terrifying across multiple dimensions:
- Program Crash / Segmentation Fault: On operating systems equipped with Virtual Memory management (like Windows or Linux), attempting to access a Null Pointer is usually intercepted by the OS, which forcefully terminates the program (Segmentation Fault). Ironically, this is considered “good luck” because you instantly know a severe bug exists!
- Embedded System Catastrophe (Hardware Fault & Data Corruption):
On microcontrollers that typically operate without a Memory Management Unit (MMU), the memory address
0x00000000might not be restricted space! It could point directly to critical Flash Memory, the system Reset Vector, or vital Hardware Registers! Accidentally overwriting Address 0 could scramble the hardware’s behavior or corrupt the Exception Vector Table, permanently crashing the system until a hard manual reset is performed. - Security Vulnerabilities:
Malicious hackers aggressively exploit this flaw for Arbitrary Code Execution or injecting dangerous payloads. For instance, a historic bug in the
libpnglibrary allowed attackers on ARM architectures to overwrite the Exception Vector located at Address 0! - The Demon of Compiler Optimization:
This is the most frightening byproduct of UB! The Compiler is globally entitled to assume: “A competent programmer simply never writes UB code.” Therefore, if you accidentally Dereference a Null Pointer, and then on the very next line write
if (ptr == NULL)to catch the error, the Compiler deduces: “Wait! If it was NULL, it would have crashed on the previous line. Since it reached here, it mathematically CANNOT be NULL!” Consequently, the Compiler ruthlessly deletes your NULL-check code (Dead Code Elimination), instantly stripping your system of its only defense mechanism!
Code Example
Let’s examine a deceptively simple code example demonstrating the lethal trap of dereferencing a Null pointer before verifying it—a mistake routinely optimized away by the Compiler.
#include <stdio.h>
#include <stdlib.h>
/* Hypothetical System Configuration Struct */
struct DeviceConfig {
int device_id;
int status;
};
/* Function to verify the hardware's status */
int check_device_status(struct DeviceConfig *config) {
/* ❌ FATAL FLAW: Prematurely Dereferencing the 'config' pointer
to extract config->status.
If 'config' is NULL here, we have instantly triggered Undefined Behavior! */
int current_status = config->status;
/* ❌ The Compiler Optimization Trap:
Because UB has already theoretically occurred above, the Compiler takes the liberty
of deleting this entire 'if' block during compilation. It strictly assumes
'config' is NOT NULL (otherwise, UB would have already terminated execution). */
if (config == NULL) {
printf("Error: Null pointer detected!\n");
return -1;
}
return current_status;
}
int main(void) {
struct DeviceConfig *my_config = NULL; // Initialized strictly as a Null pointer
// Accidentally passing the Null pointer into the function
int status = check_device_status(my_config);
printf("Device status: %d\n", status);
return 0;
}
The Clean Code Fix: You must definitively relocate the if (config == NULL) guard to be ABOVE the config->status dereference line. Verification must always precede access!
Best Practices & Secure Coding
To shield our hardware from unpredictable erratic behavior or Null Pointer hacking vulnerabilities, we must strictly adhere to globally recognized Secure Coding standards like SEI CERT C:
- Always Validate Before Use (Rule EXP34-C): Never Dereference a Pointer without actively guarding it with
if (ptr != NULL)orif (ptr). This is absolutely critical for Pointers returned from dynamic allocations likemalloc()or data received from external libraries. - Initialize and Reset Aggressively (Rules MEM01-C / MEM30-C): Upon declaring a Pointer variable, if you do not immediately have a valid address to assign, set it to
NULLinstantly to prevent extremely hazardous Wild Pointers. Furthermore, after executingfree()to release memory, you must forcefully reset that Pointer back toNULLto eradicate Dangling Pointers. - The Arrival of
nullptrin C23: For engineers utilizing the modern C23 standard, decisively upgrade from the legacyNULLmacro (or0) to the newnullptrkeyword. The Compiler inherently understands that its concrete Type is an authentic Pointer, which massively reduces obscure bugs caused by confusing integers with memory addresses.
Conclusion
Null-Pointer Dereferencing does not merely halt a program gracefully; it acts as an active summoner of Undefined Behavior into the heart of your system. In an Embedded Systems environment lacking the protective armor of a high-level OS, this bug spirals directly into hardware corruption, gutted optimization checks, and lethal security exploits. Therefore, hardware developers must operate with ironclad discipline: constantly verify your Pointers and ruthlessly enforce NULL or nullptr defaults!
If you thoroughly enjoy these deep technical dives exploring the absolute core mechanics and memory management intricacies of compiling, don’t forget to join our community to share exciting technical insights and projects at www.123microcontroller.com. See you in the next debugging article. Happy Coding everyone!