Code Guardians: Elevating Safer C with MISRA C and BARR-C Industry Standards
Introduction: Why Do We Need C Safety Standards?
Hello engineers and fellow developers at www.123microcontroller.com! We are back again with another crucial topic. It might sound a bit academic today, but trust me, this is an absolute “must-have” for anyone working in industrial-grade Embedded Systems or System Programming. Today, we are deep-diving into the art of “Writing Safer C”.
We all know C is a highly flexible, powerful, and incredibly fast language. But it’s also like a “sword without a hilt”—swing it carelessly, and you might cut your own hand. In production environments where hardware has to run 24/7 without fail, simply writing code that “compiles and runs” isn’t enough. We need “traffic rules” or Coding Standards to act as a shield. Let’s explore what legendary sources say about applying standards like MISRA C and BARR-C to write truly safe C code!
The Philosophy of Standards and Bug Immunity
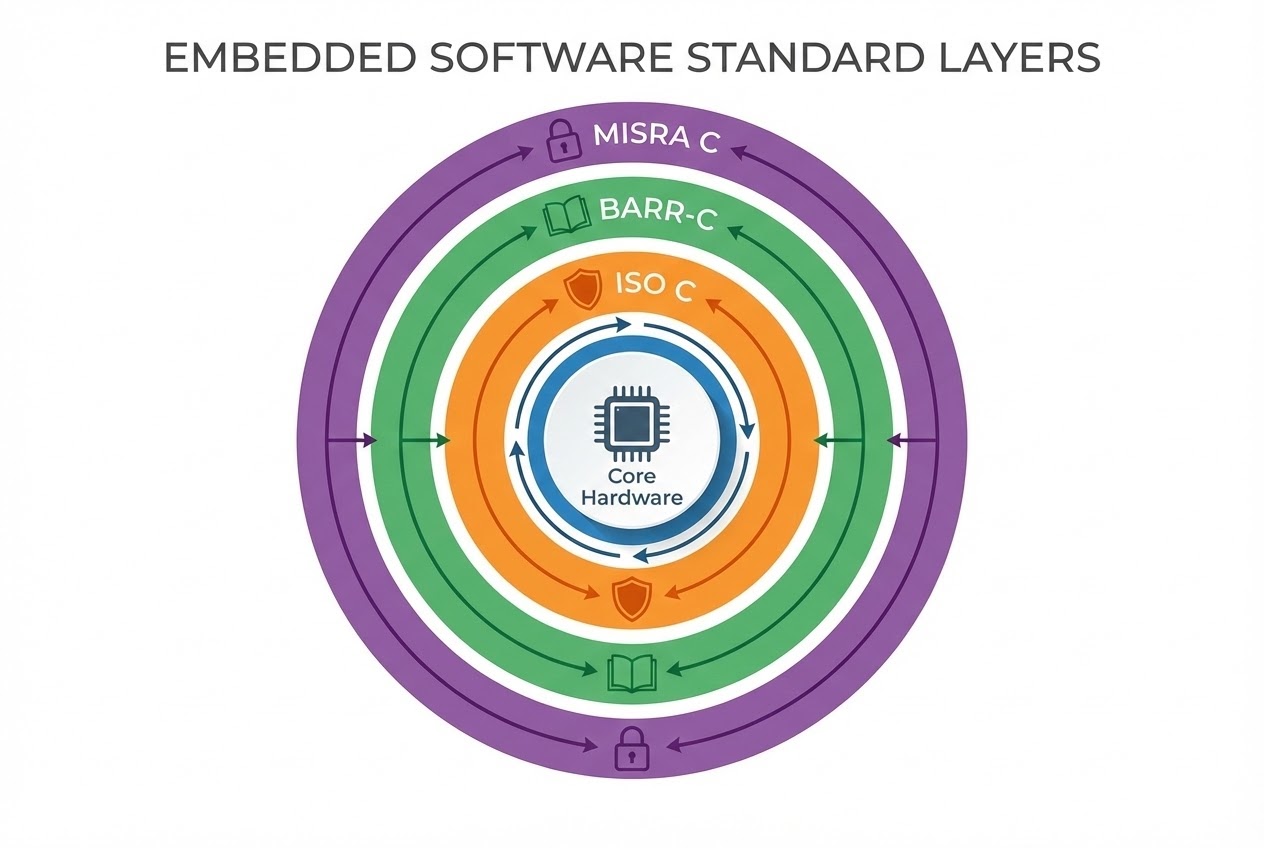
The philosophy of Safer C traces its roots back to the ambiguities within the ISO C Standard itself. The standard explicitly permits Implementation-defined behaviors, Unspecified behaviors, and the dreaded Undefined behaviors (UB). These “gray areas” mean that the exact same source code, when compiled across different chip architectures, can behave in wildly unpredictable ways.
To combat this, the hardware industry adopted “Coding Standards”—clearly documented and enforceable rule sets. These standards encourage programmers to write code according to project requirements, rather than personal preference or habit. In the embedded systems realm, two major standards dominate the conversation:
- MISRA C (Safety-Critical Systems):
- Origin: Initiated in the UK automotive industry around 1993-1996, born out of the frustration of seeing developers repeat the same software bugs over and over.
- Goal: Specifically designed for “Safety-critical” systems where a software failure could lead to human injury or death (e.g., ABS braking modules, pacemakers).
- Characteristics: MISRA C defines a safer “Subset” of the C language. It is incredibly strict and limiting, but interestingly, it does not dictate stylistic preferences (like indentation or bracket placement). While access to the official standard document isn’t free, it’s an invaluable investment for highly reliable systems.
- BARR-C (Bug-Killing Standard):
- Origin: Created by Michael Barr from his experience as a consultant, where he observed development teams making the same recurring errors.
- Goal: BARR-C rules aren’t just for making code look pretty (stylistic preferences). Every rule was selected with the singular goal to “minimize defects”. It focuses heavily on reliability and security, and best of all, the standard is available to download for free.
- Compatibility:
- The best part is that BARR-C was designed to be entirely “non-conflicting” with MISRA C. In fact, MISRA C rules can be considered a subset of BARR-C rules. Therefore, development teams can seamlessly use BARR-C to govern code style while simultaneously enforcing the stringent safety rules of MISRA C.
Code Example: Adhering to the Standards
Let’s examine a clean code example that follows basic standard guidelines (such as using Standard Data Types and Complete Data Types to eliminate variable size ambiguity), which is a core part of writing Safer C.
/*
* Following standards like CMSIS, MISRA, or BARR-C
* encourages the use of <stdint.h> to ensure constant variable sizes across all hardware platforms.
*/
#include <stdint.h>
#include <stdbool.h>
#include <stddef.h>
/* Avoid Magic Numbers by defining them as Macros */
#define MAX_SENSOR_READINGS (10U)
/* Ensure complete and well-defined data types in structures */
typedef struct {
uint16_t readings[MAX_SENSOR_READINGS];
size_t count;
} SensorData;
/*
* Function to append sensor readings.
* Always includes Bounds Checking for safety.
*/
bool add_sensor_reading(SensorData *sensor, uint16_t new_value) {
/* Prevent Null Pointer Dereference */
if (sensor == NULL) {
return false;
}
/*
* Prevent Array Out-of-bounds (Undefined Behavior).
* Routine bounds checking is a primary way to minimize defects.
*/
if (sensor->count < MAX_SENSOR_READINGS) {
sensor->readings[sensor->count] = new_value;
sensor->count++;
return true;
}
return false; /* Buffer is full */
}
Best Practices to Keep in Mind
To truly transform ordinary code into “Safer C,” industry experts emphasize the following Best Practices:
- Use Automated Analysis Tools: A good coding standard rule must be automatable. You should leverage automated Static Analysis tools to scan and enforce these rules before compilation. Simply relying on code reviews by eye to catch bugs in a 100,000-line project is practically impossible.
- Apply Standards Based on Risk Levels: If you are designing a product that could injure or kill someone, you “must” study and integrate MISRA C. However, if your project isn’t a matter of life and death, starting with BARR-C is a fantastic first step toward reducing overall defects.
- Don’t Code Out of Habit: While some rules in BARR-C or MISRA C may feel pedantic or annoying to seasoned programmers accustomed to their own style, their purpose is to eliminate C’s gray areas and restrict dangerous behaviors. Strict adherence prevents bugs and drastically improves long-term stability.
Conclusion
Mastering Writing Safer C isn’t merely about memorizing syntax; it’s about building “discipline” and utilizing Coding Standards like MISRA C and BARR-C as your risk-filtration system. These standards aren’t there to stifle creativity. They are blueprints formed from the painful experiences of global development teams, ensuring our microcontrollers execute code stably, safely, and without causing harm.
If you are interested in diving deeper into configuring Static Analysis Tools or looking at more case studies of industry-certified code, don’t forget to follow us and join the conversation at www.123microcontroller.com. See you in the next article. Happy Coding!