Memory-Mapped I/O: Dominating Bare-Metal Hardware via C Pointers - The Ultimate Embedded Arsenal

Introduction: The Elite Pathway to Total Microcontroller Domination
Greetings, hardware engineers and elite code warriors of the www.123microcontroller.com syndicate! Today, the dark-eyed engineer returns to brutally deconstruct the absolute nucleus of hardcore Hardware Interaction—the raw science of directly manipulating silicon with zero apologies.
When high-level software engineers deploy code onto a standard desktop environment, they lazily rely on heavily padded OS API layers to negotiate hardware interactions on their behalf. But submerged deep within the hostile trenches of Embedded Systems, hardcore bare-metal developers operate identically to frontline battlefield commanders, physically marching into the circuitry to violently throw the physical hardware activation switches with their bare hands! The ultimate existential programming query presents itself: How exactly does the C language—a mere abstract arrangement of text strings—possess the phenomenal power to physically detonate and redirect massive electrical currents across a physical silicon substrate? The devastating answer lies perfectly coded within an earth-shattering architectural spell designated “Memory-Mapped I/O.” Today, we ruthlessly dissect and decode how international hardware consortiums engineer this architecture, and precisely why mastering this mechanism is the absolute mandatory rite of passage for every aspiring embedded hardware hacker!
The Breach: Decoding Memory-Mapped I/O Architecture
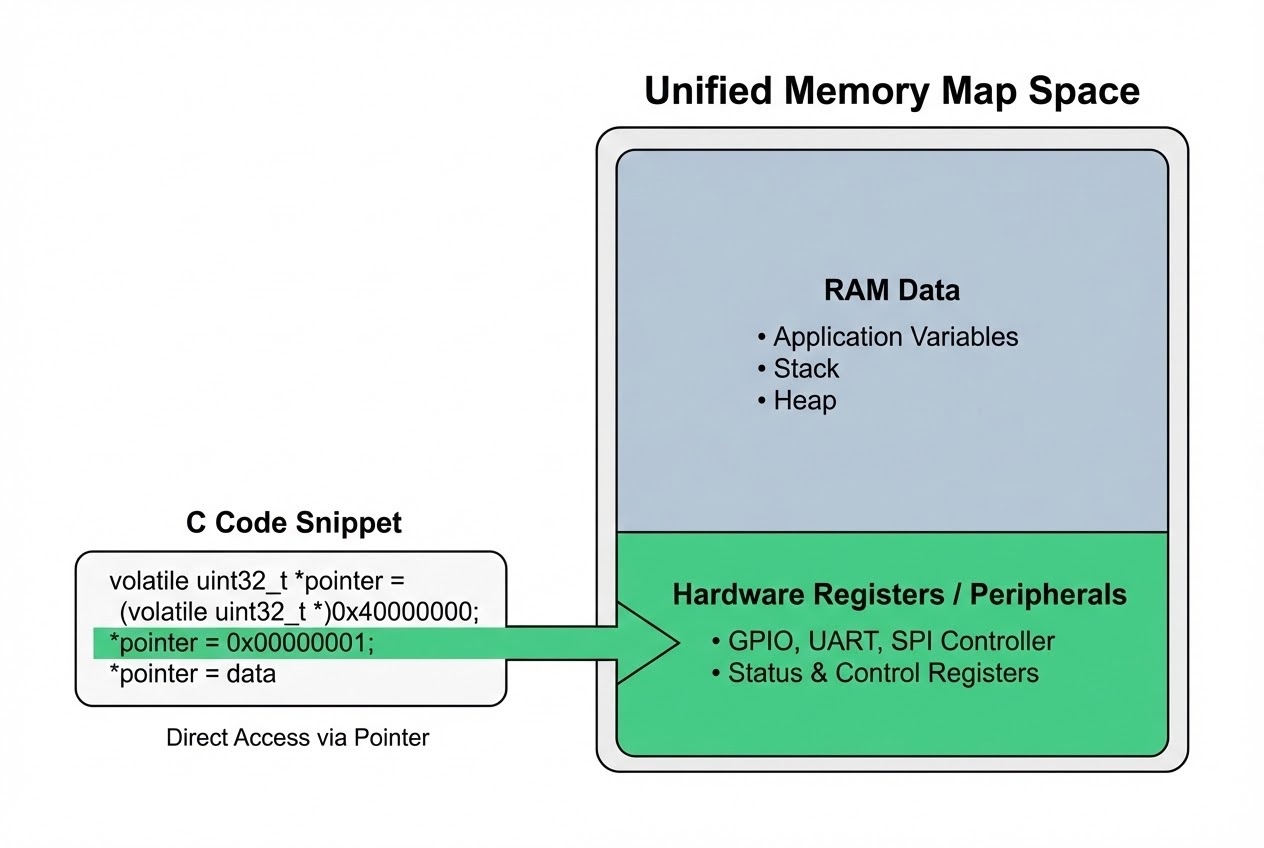
In order for a central processing core (CPU) to aggressively initiate tactical communications with its deployed peripheral battalions (modules spanning complex GPIO signal arrays, ruthless silicon Timers, or high-velocity UART/SPI serial vectors), their architectural topologies unconditionally demand a unified engagement zone. In ancient, primitive processor histories, silicon architects explicitly fragmented and forcefully segregated strictly the overarching Random Access Memory array (Memory Space) away from the specialized physical circuitry mapping the peripheral controllers (I/O Space). This prehistoric standard—historically classified as Isolated Port-Mapped I/O—aggressively mandated that programmers utilize ultra-specialized, highly localized, low-level Assembly opcodes (typically IN or OUT instructions) explicitly to sledgehammer command strings across the divide.
However, hunting aggressively for streamlined compiler elegance, explosive processing velocity, and brutal architectural dominance, contemporary silicon hardware engineers engineered an unstoppable paradigm shift, birthing the absolute standard of Memory-Mapped I/O:
- The Ultimate Illusion—Hardware Disguised as Static RAM: This god-tier architectural technique aggressively intercepts the raw operational Registers (the physical byte-sized silicon control panels governing all peripheral logic) and forcibly superimposes their exact geographic addresses, anchoring them directly inside the same contiguous geographic landscape comprising the processor’s primary Memory Map.
- Executing the Assembly Instruction Purge: Operating strictly from the CPU’s highly restricted field of view, these physical hardware actuation buttons now instantly masquerade and visually manifest functionally identical to mundane, standard RAM memory cells! Thus, the aggressive tactical maneuvers regarding reading, injecting, or overwriting configuration telemetry violently into the hardware peripherals can now be unleashed perfectly exploiting the exact same standard, highly-optimized memory manipulation instructions natively embedded inside the CPU logic array. The absolute reliance on convoluted, esoteric hardware-specific command subroutines is completely wiped from existence.
- Unleashing the Full Unrestrained Rage of C: This singular hardware mapping paradigm upgrades the C firmware developer into an unstoppable omnipotent force! Because the hardware is literally disguised as software memory, we are granted authorization to natively weaponize the sharpest, most lethal baseline instruments intrinsic to the C language ecosystem: specifically raw Pointers, mathematically packed Structs, and aggressively shifting Unions. We leverage these software phantoms to lock onto, violently breach, and manipulate hardware configurations autonomously. Furthermore, we can aggressively mobilize the entire hyper-optimized mathematical Instruction Set native to the microprocessor architecture to crush, process, encrypt, and blast I/O data arrays seamlessly at astronomical speeds.
Source Code Intel: Breaching Hardware via Clean Code
Lock your visual sensors onto this raw syntax demonstration showcasing exactly how to harness “Bare-Metal” C Pointer arithmetic to aggressively penetrate targeted silicon hardware stealthily buried specifically within the memory sector (Authored utilizing battle-hardened Clean Code safety protocols to guarantee operational survival).
#include <stdint.h>
/*
* 1. Scout and Mathematically Hard-Lock the Peripheral's Base Address
* Mission Parameters: Assume a hostile telemetry transmission hardware modem portal is stationed strictly at geographical address 0x1000.
* We are required to forcefully Type-Cast this floating integer coordinate aggressively into a registered, trackable C Pointer entity.
*/
#define MODEM_PORT_ADDR 0x1000
/*
* 2. Forge the Primary Targeting Pointer locking directly onto the silicon hardware.
* 🛡️ ABSOLUTE LETHAL DIRECTIVE: You are legally bound to permanently brandish the 'volatile' keyword when orchestrating Memory-Mapped I/O strikes!
*/
static volatile uint8_t * const p_modem_hw = (uint8_t *)MODEM_PORT_ADDR;
/* Tactical assault routine explicitly engineered to rapid-fire String payloads directly into the hardware transmission portal */
void modem_send_string(const char *str) {
// Maintain suppressive looping fire until the optical magazine register is exhausted (Null Terminator impact)
while (*str != '\0') {
/*
* 3. Aggressive Live-Fire Hardware Injection
* We brutally smash the payload character physically through the Pointer vector! This action violently detonates raw electrical potential directed instantly into the hardware transmission pins.
*/
*p_modem_hw = *str;
str++; // Slide the optical feed mechanism forward chambering the next sequence character string.
}
}
Entering a true industrial deployment theater, elite silicon foundries (Chip Vendors) are rarely sadistic enough to leave engineers completely exposed. They routinely air-drop heavily documented Header Files matrices or fully functional Hardware Abstraction Layer (HAL) architecture packages directly into your IDE. These frameworks execute the grunt work, eliminating the need to manually memorize raw hostile addresses (like 0x1000). Instead, developers smoothly requisition abstracted Struct command frameworks—transmitting clean code like GPIOA->CRL |= (1 << 2);—which radically amplifies code readability, accelerates visual scanning, and aggressively injects massive defensive layers combating catastrophic compilation faults.
Defending Against the Terminal Threat of Unprotected Memory Vectors
Initiating a Memory-Mapped I/O protocol superficially radiates a deceitful aura of simplistic safety: simply forge a Pointer scope, aim it at the matrix, and jam a variable inside. But lurking silently within the compiling logic shadows exists a lethal minefield of “Undocumented Hazards” capable of transforming your hardware platform into localized thermonuclear scrap. Elite international cyber-engineers rigidly enforce these defensive Best Practices rules of engagement:
- Omitting
volatileis Equated to Digital Suicide: If you physically task a Pointer to maintain a lock strictly on a volatile hardware address cluster, you are “Architecturally Mandated” to permanently weld thevolatilekeyword directly onto its declaration (Ex:static volatile uint32_t *). The brutal reality stands that the numeric configuration cached within that silicon location possesses the extreme capability to randomly violently mutate its state unprompted and completely independent of any software oversight. If you arrogantly neglect to burn thevolatilesigil onto the Pointer, the dangerously hyper-aggressive code Optimizer built inside your compiler may attempt to “helpfully erase” or “clean up” your repetitive hardware read/write loops because to its abstract logic, “That specific memory parameter has zero internal logic loops changing it, so caching it is faster.” Yielding to this optimization guarantees immediate and catastrophic system architectural collapse. - The Nightmare Abyss of Memory Alignment Violations: Scaling vertically into advanced processor hardware (dominantly the brutal ARM Cortex series), the architecture categorically and ruthlessly forbids hackers from executing sloppy, fractured unaligned memory extraction techniques (Unaligned memory access). If an engineer, intoxicated with power, violently attempts to jam a massive 32-bit width Pointer logic to force-read a tightly packed hardware register that mathematically fails to cleanly Align parallel to the absolute strict physical byte-boundary geometry required by the CPU layout, the hardware processor core will fly into an intense rage, instantly spawning a devastating Hard Fault Exception Interrupt, terminating its own execution process and shutting down the board immediately in protest.
- Strict Enforcement of Tactical Bit-Masking Over Fragile Bit-Fields: In scenarios demanding intricate microscopic surgical edits mutating singular, isolated atomic bits buried deep within a highly populated generalized Register cluster (e.g., triggering highly localized status flags), deploying nested logical Bit-fields embedded inside a complex Struct visually looks phenomenally sophisticated and clean. However, structurally beneath the software compiler, C standards severely brand this exact methodology as “Poorly Defined Behavior” depending wildly upon the fluctuating compiler architecture rules! The single most battle-hardened, mathematically invincible, and globally respected maneuver surviving the Memory-Mapped I/O massacre involves strictly deploying raw Bit-Level arithmetic assault algorithms (Bit-masking). Exclusively relying on
|=(Setting),&=(Masking/Clearing), or^=(Toggling) is the absolute golden guarantee ensuring your firmware laser-cuts the target silicon logic flawlessly with zero collateral damage!
Conclusion
The architecture defining Memory-Mapped I/O manifests as the absolute paramount tactical bridge permanently linking abstract C compilation scripts directly into kinetic energy manipulating the brutal reality of physical silicon boards. It gracefully dissolves the horrifying intricacies associated with commanding alien micro-circuits, streamlining the battlefield into simply orchestrating flowing data streams violently through baseline Pointers mimicking native C Struct definitions! This architectural miracle massively supercharges our capability to surgically extract the absolute maximum execution payload potential completely exhausting internal microcontroller generation limits. However, this omnipotent capability exacts a terrifying blood-oath demanding unparalleled code discipline and extreme paranoia—most vitally, the absolute militant deployment of the defensive volatile keyword logic alongside the surgical mastery calculating faultless Bit-Math algorithms ensuring logic survival.
If interacting closely with hardware-shattering code dissection fuels your engineering dopamine, or if you historically bear the agonizing 48-hour emotional trauma resulting explicitly from casually deleting a single volatile declaration—plunging your system into a hallucinating ghost-bug spiral (We have absolutely bled out in those identical trenches before! 😂)—do not hesitate to immediately establish communications! March directly into the war-room matrix, drop your bug-action-reports, and initiate hard technical banter deep within the comm-channels established specifically for the www.123microcontroller.com vanguard developer faction! Secure your memory vectors permanently. We re-engage in the subsequent cyber-combat article dispatch; Happy Bare-Metal Hacking, cyber infantry!