Memory Management in Embedded C: Maximize Hardware Performance and Stop Critical Bugs
Introduction: Why Do We Care About RAM on Tiny Chips?
Hello engineers and fellow developers at www.123microcontroller.com! Today, the dark-eyed engineer will guide you to the deepest core of hardware programming: the critical world of “Memory Management.”
When writing C programs for standard personal computers, developers rarely agonize over memory because they have Gigabytes of RAM and massive Operating Systems (OS) performing automated garbage collection. However, in the realm of Embedded Systems, our microcontrollers are incredibly “Resource-constrained.” Some specific chips have merely a few kilobytes of RAM available. Managing memory here is like organizing files on an incredibly tiny desk—if you don’t allocate efficiently, leave clutter, or forget to release reserved space, your program will slow to a crawl, freeze, or suffer an instantaneous mid-air reboot! Let’s explore how industry elites instruct us to manage memory safely on hardware.
The Philosophy of Embedded Memory Management
When coding in C for Embedded Systems, memory management entails a far deeper understanding than merely declaring variables. The crucial fundamentals are:
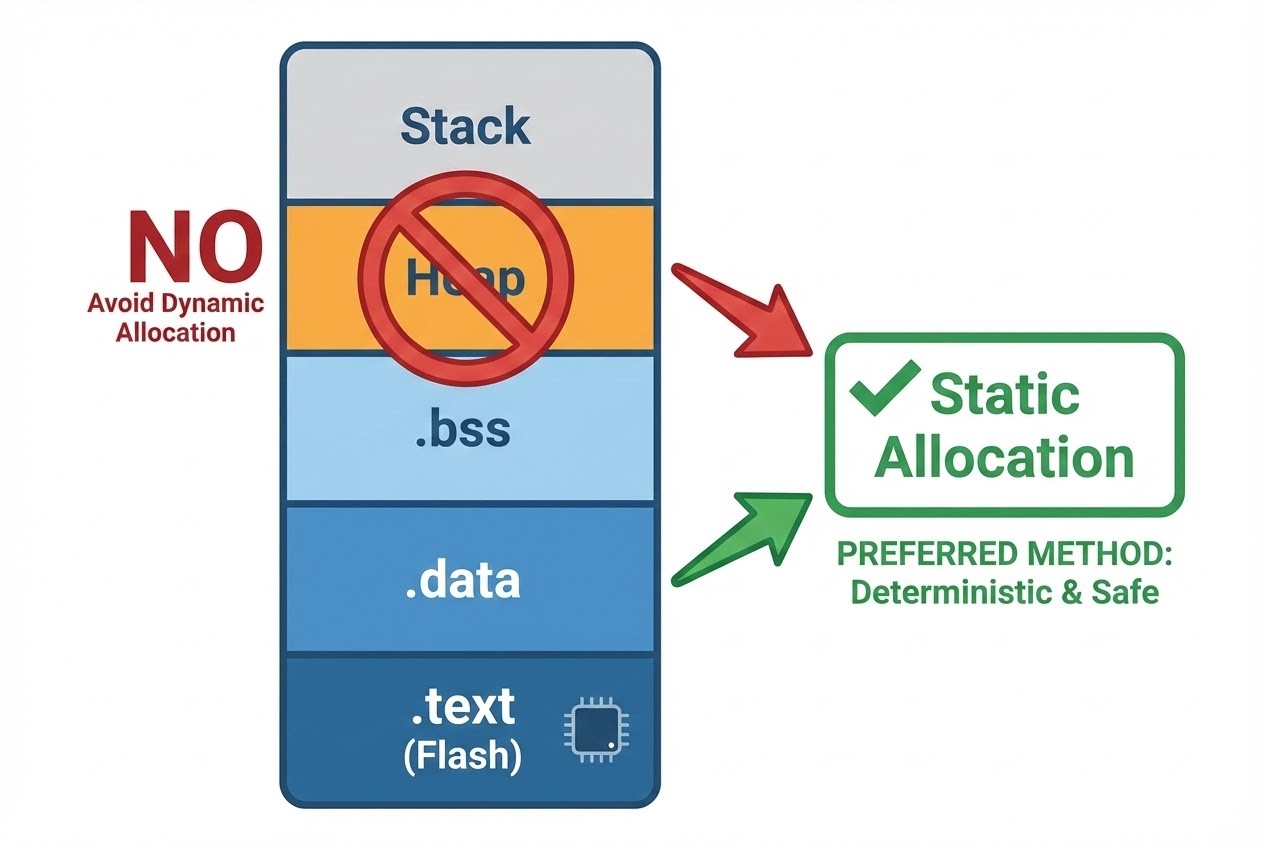
- 1. Memory Layout Insight: A C program on a microcontroller divides the memory into highly specific segments (usually governed by a Linker Script):
.text(Flash/ROM): The zone housing the executable instructions and read-only constants..data(RAM/SRAM): The segment containing Global or Static variables that arrive with pre-initialized values..bss(RAM/SRAM): The area reserved for Global or Static variables lacking initialization (typically wiped out to zero during boot).Stack(RAM/SRAM): The temporary region to store Local function variables and context parameters.Heap(RAM/SRAM): The wild, free-floating space used for dynamic memory allocation during runtime.
- 2. Why Hardware Engineers Despise Dynamic Memory Allocation:
In standard C, we’re equipped with standard functions like
malloc(),calloc(),realloc(), andfree()to manipulate the Heap dynamically. However, strict Embedded System standards violently forbid or discourage their usage. Here is why:- The Nightmare of Memory Fragmentation: This is the primary culprit! When we repeatedly allocate and free blocks of non-uniform sizes, the available Heap fractures into tiny, shattered fragments. Eventually, when requesting a larger chunk, the system panics: we have enough “total” space left, but zero “continuous blocks” large enough to fulfill the request. Boom, crash.
- Non-deterministic Timing: In strict Real-time control structures, invoking these dynamic functions takes an unpredictable number of clock cycles to complete. This irregularity is incredibly dangerous if your system demands millisecond architectural precision.
- 3. The Ultimate Solution: Static Allocation and Memory Pools: Safety resources advocate utilizing pure Static Memory Allocation instead. This means pre-allocating your Arrays and variables globally at compile time. This guarantees that your maximum memory load is 100% predictable. In cases where dynamic behavior is utterly unavoidable, experts recommend custom Memory Pools—a technique where large, equally-sized blocks of memory are pre-allocated safely at boot and explicitly disbursed via custom robust pointer routines to permanently exterminate Fragmentation risks.
Code Example: Safe Static Allocation vs The Dynamic Menace
Let’s do a side-by-side code review contrasting “brittle, fragile” dynamic memory usage against a highly “safe (Best Practice)” static methodology suitable for constrained microcontrollers.
#include <stdint.h>
#include <stdbool.h>
#include <stdlib.h>
#define MAX_SENSOR_LOGS 10
// Standard structure for housing sensor metrics
typedef struct {
uint8_t sensor_id;
uint16_t temperature;
} SensorLog;
/*
* ❌ DANGEROUS BAD PRACTICE (Never use in bare-metal Embedded)
* Utilizing Dynamic Allocation (malloc)
* High risk of Memory Leaks and devastating Heap Fragmentation long-term.
*/
void bad_log_sensor(uint8_t id, uint16_t temp) {
// Arbitrary runtime Heap allocation
SensorLog *log = (SensorLog *)malloc(sizeof(SensorLog));
if (log != NULL) {
log->sensor_id = id;
log->temperature = temp;
// FATAL FLAW: If we export the data later and forget to call free(log),
// we unleash an immediate, unrecoverable Memory Leak!
}
}
/*
* ✅ BEST PRACTICE (Static Memory Allocation)
* Pre-allocating maximum buffer potential statically generates absolute
* footprint predictability, entirely bypassing malloc() vulnerabilities.
*/
static SensorLog log_buffer[MAX_SENSOR_LOGS]; // Resides predictably in .bss (RAM)
static uint8_t log_index = 0;
bool good_log_sensor(uint8_t id, uint16_t temp) {
// Preventing deadly Buffer Overflows via rigid Bounds Checking
if (log_index < MAX_SENSOR_LOGS) {
log_buffer[log_index].sensor_id = id;
log_buffer[log_index].temperature = temp;
log_index++;
return true; // Successfully logged
}
return false; // Buffer maxed out, preventing catastrophic out-of-bounds corruption
}
Best Practices to Attain Secure Coding Standards
To elevate our firmware logic to professional robustness adhering to international standards (such as the SEI CERT C rules), engineering authorities hammer home these memory commandments:
- Slay the Memory Leak Demon: If you are somehow forced into utilizing
malloc(), the unbreakable golden rule is that every allocation must have a corresponding, guaranteedfree(). Memory leak negations will slowly eat away at your precious tiny RAM until you hit full “Memory Exhaustion” and halt abruptly. - Buffer Overflows Are Lethal: C grants us supreme unadulterated power over memory—but zero automated array bounds checks. Blasting data past the final index of an Array (Out-of-bounds write) will ruthlessly corrupt adjacent variables. Even worse, it opens massive architectural vulnerabilities exploited by hackers (Stack Smashing). You must manually code rigorous Bounds Checking using
iflogic universally! - Banish Dangling Pointers: CERT MEM30-C aggressively mandates never touching memory after it is
free(). The veteran trick is instantly nullifying pointers immediately post-free:free(ptr); ptr = NULL;. This definitively cuts off any chance of a fatal “use-after-free” crash occurring down the execution line. - Hardware & Memory-Mapped I/O Safeguards: Whenever utilizing a strictly typed Pointer to command the raw hardware registers (e.g., aggressively toggling GPIO port silicon), you must weaponize the
volatilekeyword. This forces the Compiler Optimization engine to back off entirely, making it aware that external silicon can mysteriously alter the memory address values at any time.
Conclusion
Effective Memory Management in C for Embedded Systems goes immensely beyond just understanding the syntax of memory reservation. It is the tactical design philosophy of architecting a software skeleton that is relentlessly “Predictable” and built purely on “Risk Avoidance”. Transitioning entirely off dynamic malloc() and completely mastering Static Allocation and internal Memory Pools will massively eliminate the most anxiety-inducing debug cycles veteran engineers face.
If you enjoy these deep, hardcore technical dives connecting software behavior to raw silicon reality, or if you’ve been burned by evil pointers and want to share your debug nightmare, leap into the discussions at www.123microcontroller.com. Masterful programming emerges from having an unbreakable core understanding. See you in the next tutorial. Happy Coding!