Linked Lists: The Origin of Dynamic Data Structures and the Memory Train

Introduction: The Ever-Adapting Tracks of the Memory Landscape
Hello engineers and fellow developers at www.123microcontroller.com! Today, the dark-eyed engineer is taking you on a rigorous journey to understand a data framework that acts as the veritable “spinal cord” of System Programming: The highly dynamic Linked Lists.
In previous deep dives, we dissected the Array—which functionally resembles rigidly welded, consecutive storage lockers. But in the unpredictable warfare of complex hardware and software architectures, you don’t always know the incoming payload size. Pre-allocating an immense monolithic Array blindly wastes microscopic microcontroller RAM. Enter the Linked List: forged in the fire of this exact dilemma. Today, let’s strictly analyze how premier engineering resources define Linked Lists within the global taxonomy of Data Structures, and why they serve as the crucial building blocks for exponentially more complex topologies!
Decoding the Anatomy of a Linked List
In the macro-perspective of general Data Structures, a Linked List transcends merely storing values; it represents the ultimate “Building Block” engineered specifically for supreme flexibility via Dynamic Memory Management. High-level architecture texts articulate its role as follows:
- 1. The Self-Referential structural architecture:
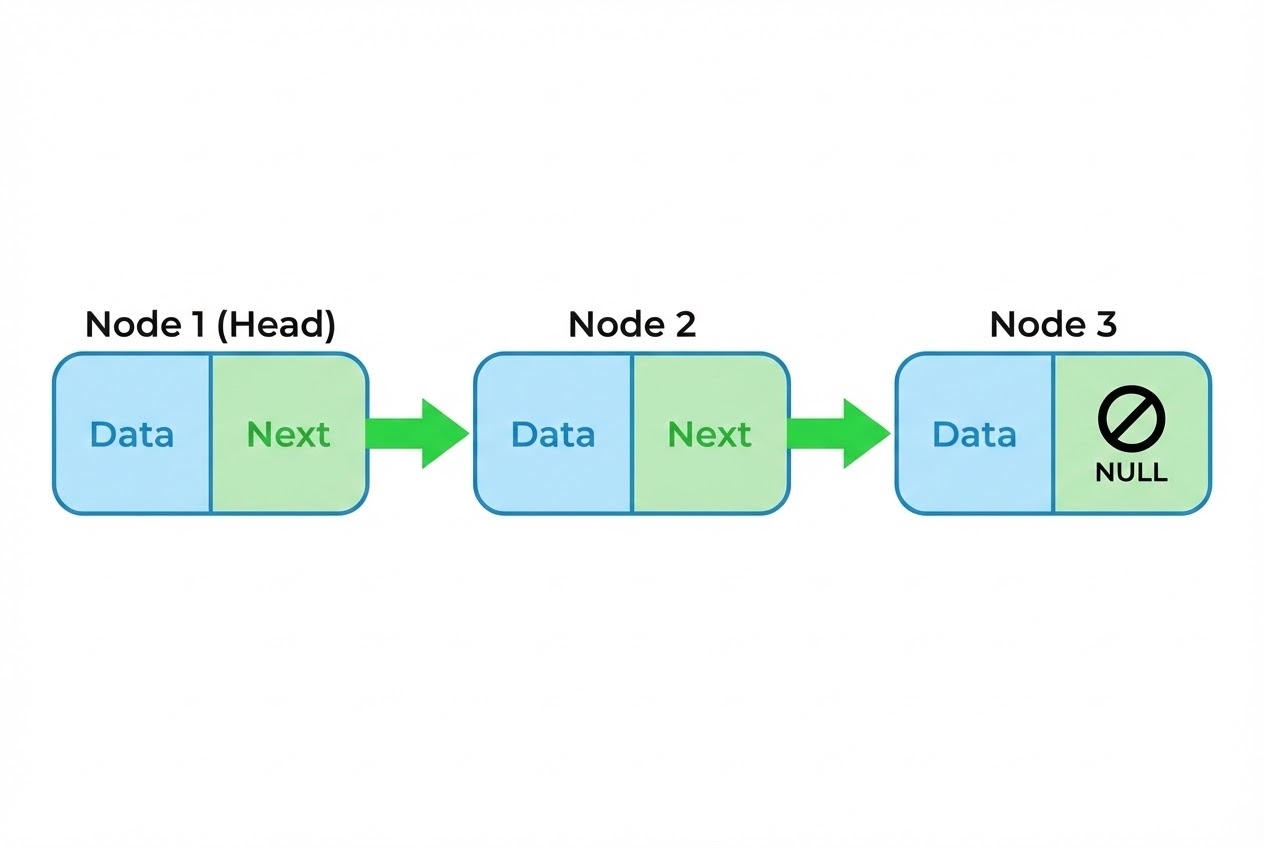
A Linked List is birthed exclusively through the C language mechanism of “Self-referential structures”. Concretely, this is a
structthat natively embeds a generic Pointer aimed directly at a struct of its exact identical datatype. Each individual chunk of payload within a Linked List is classified as a “Node”. These Nodes logically separate into two sectors: the Data sector (the payload itself), and the Link sector (the Pointer anchoring it to the chronologically next Node). - 2. The Train of Scattered Memory:
Radically opposed to the Array that strictly demands uniform, Contiguous memory real estate, a Linked List harnesses Dynamic memory allocation (such as
malloc()). Therefore, individual Nodes can be entirely scattered (fragmented) anywhere across the massive plain of Heap memory. The Pointers operate essentially as automated train couplings, forging these wildly detached bytes into an unbreakable logical chain. - 3. The Tactical Supremacy (and Flaws) vs. Arrays:
The catastrophic weapon of the Linked List is its astronomical speed during absolute Node Insertion or Deletion. Should you desire to inject highly critical telemetry dead in the center of the list, you merely “intercept and rewire the Pointers” — avoiding the massive processing penalty of physically Shifting every subsequent element (as is mandatory in Arrays). The agonizing trade-off? Depleted Random Access. You cannot arbitrarily demand the 10th Node (like
arr[10]). The CPU must painstakingly march from the Alpha Node (Head), riding Pointers chronologically, Node by Node (Sequential Access). - 4. The Core Substrate for Abstract Data Types (ADTs): Due to their sheer elasticity, Linked Lists are routinely cannibalized to act as the raw foundational lattice for fabricating vastly different Data Structures. They physically execute Stacks (LIFO architectures), Queues (FIFO architectures), Hash Tables (utilizing ‘Chaining’ to bypass key collision crises), and ultimately construct Non-linear dimensional map structures like Trees and Adjacency List Graphs.
- 5. Formidable Variations in Topology: While the Singly Linked List propels logic exclusively forward, engineers rapidly mutated the architecture. We deploy Doubly Linked Lists (dual pointers granting instantaneous bi-directional traversal) and Circular Linked Lists (the Omega node’s pointer hooks directly backward into the Alpha node), enabling complex looping processing algorithms.
Code Example: Bootstrapping a Singly Linked List
Let’s dissect an elegant, natively static framework executing a Singly Linked List, integrating a rigorous Clean Code technique for inserting a new Head Node. (Note: While this example harnesses malloc(), legitimate embedded production code replaces this with allocating chunks from a pre-defined Memory Pool as we’ve discussed previously!)
#include <stdio.h>
#include <stdlib.h>
/* 1. Architecting the Self-Referential Structure forming the Node */
typedef struct Node {
int data; // Encapsulated payload
struct Node* next; // Relational Pointer chaining down the line
} Node;
/* Protocol for injecting a newly minted Node at the very vanguard (Push Front) */
Node* insert_at_head(Node* head, int new_data) {
/* 2. Dynamically requisitioning RAM across the Heap for the incoming Node */
Node* new_node = (Node*)malloc(sizeof(Node));
/* 🛡️ SECURITY PROTOCOL: Unconditionally detect Heap exhaustion */
if (new_node == NULL) {
printf("CRITICAL: Memory allocation structurally failed!\n");
return head; // Abort architecture modification, return unchanged framework
}
/* 3. Assigning the payload and forging the Pointer Chain */
new_node->data = new_data;
new_node->next = head; // Redirect new Node to point towards the legacy Head
/* Export the new Node address, anointing it as the new Head of the List */
return new_node;
}
/* Protocol for total architectural demolition and Heap restoration */
void free_list(Node* head) {
Node* current = head;
Node* next_node;
/* Traverse the linked chain and dismantle the structure systematically */
while (current != NULL) {
next_node = current->next; // Pre-cache the escape vector address
free(current); // Incinerate current Node
current = next_node; // Propagate to the next cached Node
}
}
int main(void) {
Node* head = NULL; // Initiate architecture with absolute void (NULL pointer)
// Populate the Linked List architecture
head = insert_at_head(head, 30);
head = insert_at_head(head, 20);
head = insert_at_head(head, 10);
// Mandated complete cleanup post-utilization
free_list(head);
return 0;
}
Iron-Clad Security Protocols for Pointer Mitigation
Wielding Linked Lists requires directly manipulating raw Pointers and dancing explicitly on Dynamic Heap Memory. This is a notoriously hostile environment breeding severe bugs. Maximum security and coding standards dictate the following survival protocols:
- Guarding the Weakest Link: Engineering a Linked List epitomizes the phrase “A chain is only as strong as its weakest link.” If your code accidentally overwrites a single logical Pointer without backing it up first (e.g., losing the next Node’s address during deletion), every single chronological Node downstream is permanently and irrevocably severed from your program.
- Combating The Memory Leak Demon: Due to the list’s reliance on
malloc()(or direct Pool acquisition), you are entirely responsible for its destruction. Your firmware must universally deploy an explicitly designed destruction loop (e.g.,free_list) triggering afree()call physically on every single Node. Neglecting this before ending a Task slowly drains your microcontroller’s RAM pool until the hardware collapses. - Neutralizing Dangling Pointers (Zombies): The moment you invoke
free()upon a Node, absolutely never utilize its lingering Pointer variable to pull data (Dereference) ever again. Doing so unleashes catastrophic Undefined Behavior causing random crashes and data wipeouts. Golden Rule: Instantly obliterate a killed Pointer’s value by explicitly assigning it toNULL. - Absolute Null Verification: The primary law of Linked List Traversal: Precipitously verify if your targeted Node, or its incoming
nextNode, resolves exactly toNULLbefore initiating a structural read. Bypassing this will trigger a Null Pointer Dereference, violently forcing almost any microcontroller architecture to execute an immediate Hard Fault Reset into safety mode.
Conclusion
In the overarching universe of Data Structures, the Linked List is undeniably the “Initiation Ritual Puzzle” every C programmer must flawlessly conquer. It aggressively educates developers regarding the unfathomable raw power of manipulating Dynamic memory and wielding raw Pointers to synthesize relational databases out of thin air. Although it utterly sacrifices the blistering rapid access of the Array, the Linked List is the hyper-flexible backbone fundamentally necessary to bootstrap massively scalable architectures like advanced Stacks, intelligent Queues, and dynamic Decision Trees into reality.
Hopefully, this deep exposition enables you to intuitively trace the “hard-wired” data logic streaming through your physical RAM! If you possess pressing questions concerning adapting Linked Lists into raw asynchronous sensor systems, or wish to dissect fully loaded Doubly Linked List C-code, rendezvous with us deep in the forums at www.123microcontroller.com! Stand by for the next brutal architectural breakdown. Happy Coding everyone!