Interrupt Service Routines (ISR): Penetrating the Real-Time Hardware Response Engine of Embedded C

Introduction: The Lightning Strike of Hardware Dominance
Greetings, elite hardware engineers and tactical developers of the www.123microcontroller.com syndicate! The dark-eyed engineer has returned. Today, we confront the absolute “Initiation Threshold” separating amateur PC-coders from the absolute pinnacle of hardcore bare-metal hardware architects: the ruthless mastery of Interrupt Service Routines (ISR).
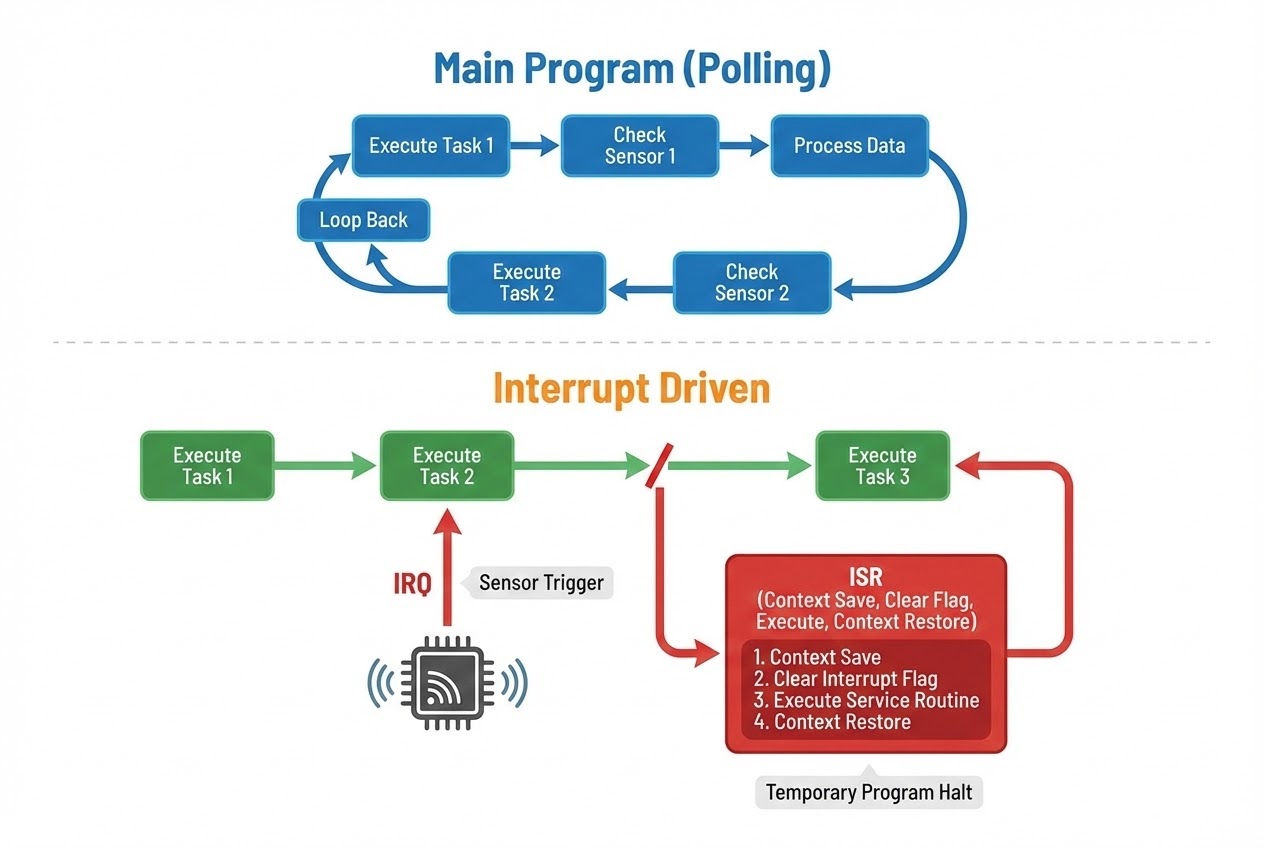
When architecting firmware designed specifically for hyper-volatile Hardware Interaction—for instance, aggressively intercepting randomized telemetry bursts from industrial sensors, or physically capturing the exact picosecond a human digit actuates a mechanical switch—relying on naive, perpetual ‘Loop Polling’ to verify hardware configuration states is functionally paralyzing. It catastrophically throttles the processing core (CPU), monopolizing an astronomical footprint of silicon bandwidth while systematically incinerating battery potential. To completely obliterate this systemic bottleneck, the godfathers of microcontroller silicon architecture engineered the ultimate execution override event known mathematically as the Interrupt system. Today, we initiate a brutal deep-dive analyzing precisely how global engineering doctrines mandate the deployment of asynchronous ISR algorithms to absolutely dominate peripheral hardware. Let us clarify this unequivocally: Assimilating this precise logic matrix guarantees your capacity to write devastatingly robust, zero-latency C code for embedded micro-architectures will permanently ascend!
Core Demolition: Decrypting ISR Execution and Bare-Metal Interfacing
If forced to contrive a layman’s analogy accurately describing the operational mechanics: traditional “Polling” firmware exactly mirrors a prisoner forced to neurotically stare unblinkingly at an inactive teakettle until the water violently boils—a horrific expenditure of operational reality. Conversely, a weaponized Interrupt architecture structurally represents upgrading to a teakettle explicitly rigged with a deafening siren hookup. The firmware is liberated; you are officially authorized to relax, process entirely distinct foreground logic (racking up execution mileage inside the Main program loop). Automatically upon the hardware successfully boiling the payload, it electrically detonates an overriding, asynchronous alarm (the physical Interrupt signal) immediately halting your reality matrix. Only then are you forcefully compelled to stand up and pour the coffee (executing the exact encapsulated subroutine—the ISR).
Zooming outward framing the overarching architecture controlling Hardware Interaction, elite telemetry documentation outlines the ferocious internal mechanics governing the ISR pipeline identically as follows:
- 1. IRQ (Interrupt Request): Instigated immediately when external perimeter hardware (e.g., A designated GPIO portal pin aggressively transitioning voltage metrics) or heavily entrenched internal hardware subsystems (e.g., Dedicated Timer circuitry experiencing a mathematical integer overflow threshold) urgently demands absolute unmitigated processor focus. The peripheral immediately launches an asynchronous electrical shockwave designated an IRQ (Interrupt Request), a localized lightning strike firing straight into the CPU core geometry.
- 2. Context Saving (The Suspension of Reality): The CPU instantly paralyzes the execution currently flowing within the instruction pipeline, forcefully hitting the digital brakes. It assumes a frantic bookkeeping operation designated “Context Saving.” It violently captures the volatile snapshot of the current operating reality—scraping all mathematical states currently residing across its delicate general-purpose Registers and the crucial Program Counter vector—hurling this crucial data cache deep into the restricted RAM sector known as the Stack, erecting an absolute safeguard preventing the foreground program memory from experiencing complete annihilation.
- 3. Vector Table Lookup (The Assassination Roster): The loyal CPU rapidly parses the exact digital signature code identifying the incoming Interrupt barrage and mechanically pivots to interrogate a rigidly localized silicon directory explicitly labeled the Interrupt Vector Table (IVT). Functionally mimicking an encrypted assassin’s ledger, this exact table is populated with distinct Function Pointers mapping geometric coordinates aiming explicitly at the exact localized memory address harboring the response firmware block (the ISR algorithm) that the developer previously explicitly programmed into the firmware to combat that specific threat.
- 4. Execution & Acknowledge (The Strike and The Counter-Sign): The targeted response algorithm explicitly housed inside the ISR (Interrupt Service Routine) immediately hijacks processing parameters and runs! The absolute most universally critical directive your C code must execute within this specific hostile territory is projecting an unmistakable “Acknowledge” signal. You must force-trigger code destroying the original alerting Flag currently lodged inside the targeted Hardware Register, screaming backward at the peripheral hardware: “Message universally received. Status nominal. Cease detonating my logic circuit with that alarm immediately!”
- 5. Context Restore (The Resurrection Event): Immediately transitioning upon fulfilling the ISR tactical strike parameters (an operation typically terminating involving an implicitly compiled hardware-level Assembly opcode such as
rti[Return from Interrupt]), the CPU core flawlessly salvages the archived context parameters heavily buried resting inside the Stack, reinflating its registers beautifully. It then smoothly violently snaps back into exactly the localized sequence of the Main Loop program logic, flawlessly resuming the mathematical grind entirely blind that an asynchronous anomaly ever materialized.
Recognize this critical truth: pristine, original standard ANSI C language specifications utterly lack a canonical keyword inherently designed to spawn a raw ISR. Consequently, giant dominant compiler architects globally (entities such as GCC, Keil, or IAR) aggressively invented proprietary non-standard compiler Keywords (manifesting commonly as __interrupt, #pragma interrupt, or strictly forcing the programmer to architect the exact string function-name rigidly mirroring the designated compiler’s specific Vector Table array structure). This specific hack informs the compiler engine itself to forcefully bolt explicit Context Save/Restore assembly wrappers flanking both limits containing the targeted function body prior to binary compilation!
Raw C Execution: Engineering a Hardened Peripheral Trap
Let us rapidly deconstruct an authorized blueprint demonstrating a professional (Clean Code Architecture) methodology. The code constructs an aggressive firmware trap configured to intercept electrical voltage spikes from a raw mechanical button utilizing a dedicated External Interrupt vector. Strictly observe the incredibly calculated tactical application invoking the volatile modifier required specifically to architect a safe data-bridge transmitting logic states bridging between the radioactive ISR zone and the nominal Main Loop parameters.
#include <stdint.h>
#include <stdbool.h>
/*
* Establishing the abstract Header File masking raw silicon Hardware Registers (Weaponizing Memory-Mapped I/O mechanics).
* The EXTI_PR structure operates as the designated Pending Register strictly utilized to scope interrupting entities and aggressively erase active Flags.
*/
#define EXTI_PR (*(volatile uint32_t *)(0x40010414))
#define LINE_BUTTON (1 << 13) // Tactical abstraction: Operating under the assumption the designated switch trigger is physically soldered confronting matrix Line 13.
/*
* 🛡️ THE IRON VAULT RULE: Any vital tracking logic variable explicitly deployed functioning as a communication nexus shared symmetrically bridging across the ISR chamber into the Main Loop structure...
* MUST UNCONDITIONALLY BE CLASSIFIED SECURED VIA THE 'volatile' KEYWORD MODIFIER!
* This explicit parameter denies the optimizing compiler engine the capacity to erroneously delete the variable under the suicidal assumption it operates redundantly.
*/
volatile bool g_button_pressed = false;
/*
* The Core Vanguard, deploying the highly volatile Interrupt Service Routine (ISR)
* (Critical Note: the specific nomenclature defining this function heavily depends upon strictly mirroring the static identifiers encoded into your chosen compiler's exclusive hardware Vector Table).
*/
void EXTI15_10_IRQHandler(void) {
/* 1. Establish perimeter check: Interrogate the register guaranteeing the volatile environmental Interrupt blast specifically originated stemming from the targeted hardware pushbutton trigger parameter (rejecting rogue parallel port chatter). */
if ((EXTI_PR & LINE_BUTTON) != 0) {
/* 2. 🛡️ OMEGA-LEVEL CRITICAL: Aggressively obliterate the targeted Interrupt Flag trapped inside the physical Hardware Register instantaneously!
* (Standard industry-practice across dominants silicon brands deploys a paradoxical write protocol: explicitly smashing a '1' logic value physically back upon the targeted silicon to violently trigger a flag "clear/erase" sequence.) */
EXTI_PR |= LINE_BUTTON;
/* 3. Arm the semantic software trap; permanently Setting a localized Flag alerting the primary software ground forces (Main Loop) to inherit calculation liabilities.
* A cardinal architectural sin involves attempting to physically execute massive, heavy-lifting logic algorithms explicitly localized inside the perimeter of an active ISR trench. */
g_button_pressed = true;
}
}
int main(void) {
/* (Conceptual abstraction zone: Acknowledge this region executes the intricate Setup logic governing the hardware peripherals and successfully throws the macro switch Enabling global system Interrupt cascades) */
while (1) {
/* The indestructible Main Loop operates universally cruising smoothly traversing logic cycles endlessly... aggressively transitioning into hyper-computation logic strictly when a legitimate Event matrix materializes. */
if (g_button_pressed) {
// Outsource massive, incredibly CPU-hostile, prolonged payload calculation subroutines pushing them exclusively out into this buffer zone (e.g., executing heavy graphical LCD pixel redraw matrices or purging massive data block transmissions across UART conduits).
update_display();
g_button_pressed = false; // System purge sequence initiated. Terminating the Flag parameters to zero-state status. Awaiting subsequent hostile engagement.
}
}
return 0; // In the unyielding domain of bare-metal embedded silicon, the processor mathematically failing into returning this integer value represents a systemic impossibility.
}
The Suicide Protocols: Fatal Catastrophes To Avoid During Lightning Operations
Wielding ISR capabilities mathematically translates to effectively juggling lit thermite! Attempting to architect sloppy, bloated subroutines deeply embedded within an interrupt vector introduces the terrifying potential to absolutely cement the logic system in an unrecoverable hung state or hallucinate logic parameters generating impossible errors (Identified universally among elite engineers as mythological “Heisenbugs”). Hardened Safer C coding guidelines strongly document strict survivor protocols classified beneath these Best Practices parameters:
- Execute Rapidly, Evacuate Immediately (Keep ISRs Short): This represents the supreme, irrevocable law! An operationally functional ISR must behave mimicking a trained assassin: breaching the perimeter, scanning the Hardware Register parameters, brutally clearing the localized trace Flag, adjusting a singular global Boolean tracking variable, and violently detonating a tactical retreat instantaneously. (Mathematically categorized as Deferred Processing). Categorically forbid deploying massive block-functions such as
delay(), nor execute unyielding sequentialwhileloops trapping the CPU awaiting shifting hardware thresholds. Intentionally stalling executing code inside an ISR structurally generates apocalyptic “System Latency,” effectively throttling and permanently severing incoming, critical micro-level priority Interrupts, functionally resulting in triggering fatal firmware logic lockups universally. - The Insanity of Reentrancy and the Absolute Ban on Blocking Operations: It remains an unforgivable offense attempting any rogue operation to inject massive block operations heavily characterized by library suites including
printf,sprintf, or deploying erratic RAM memory-gobbling sequences spanningmallocphysically inside the internal scope governing an ISR! But why? Beneath the visible hood, these bloated operations are internally heavily leveraging localized Global variables establishing complex state tracking metrics. Given the freak scenario wherein your foreground primary software is happily crunching aprintfblock matrix, and is suddenly violently struck overriding the CPU thread executing an asynchronous ISR blast that maliciously issues a secondary recursive parallelprintfcommand vector! The core data pointer mapping geometry will instantly shatter attempting cross-collision resolution across two identical, unyielding variables concurrently, instantly nuking your hardware into an unrecoverable hard-fault status. - Ruthless Clearance of Hardware Flags is Non-Negotiable (Acknowledge): Attempting an audience interacting intimately with hardware controllers mathematically obligates your engineering focus to aggressively study specific brand Datasheets strictly diagnosing identical methodologies dictating the exact protocol necessary validating and clearing the Hardware Interrupt Flag parameters assigned. Failure completely forgetting to author this manual clearance operation dictates a fatal infinite feedback matrix: the split nanosecond your architecture successfully evacuates exiting the ISR logic window, the enraged, uncleared hardware (identifying an active, bleeding flag) instantaneously screeches activating the identical secondary Interrupt sequence! Consequently, executing logic is brutally locked trapped endlessly ricocheting transitioning exclusively routing back inside the ISR over and over again. The essential foreground CPU sequence running critical application matrices permanently starves to death failing any initialization chance (Diagnosed technically resolving into an unrecoverable Infinite ISR Loop death spiral).
- Erecting Heavy Shielding Destroying Race Conditions (Critical Sections): Universally anytime the prominent, lumbering foreground sequence (Main loop) attempts calculating, extracting read intelligence, or injecting write algorithms across a data parameter matrix simultaneously mapped sharing overlap with any executing ISR function (Categorically dangerous assuming the variable spans a massive memory footprint vastly exceeding a rudimentary 1 Byte vector—e.g., attempting a 32-bit integer array alteration operating across archaic architectures explicitly requiring the CPU cycle four shifting cycles to parse), you assume the obligation to forcefully execute “momentary tactical system blackout: Execute global Disable Interrupts” actively immediately transitioning executing prior to initiating data stream interactions! Providing this hardened structure functionally erects an impenetrable tactical dome shielding data currently transferring transport preventing localized volatile rogue ISR lightning drops dropping aggressively tearing down modifying internal segments corrupting variables halfway through operation before re-establishing nominal communication reads!
Conclusion
The architecture classifying Interrupt Service Routines (ISR) manifests as the single most hyper-critical, hardened suspension bridge fusing the impenetrable border segregating asynchronous, unpredictable independent physical Hardware reality and our heavily regulated, rigid synchronous software calculation dimensions. Architecting a phenomenal ISR system rejects simple naive claims successfully facilitating baseline operational hardware responses; it aggressively pivots analyzing executing metrics demanding “hyper-kinetic volatility coupled meticulously minimizing destructive shockwave disruptions across the overarching processing matrix landscape (Mathematically limiting System Latency metrics to absolute zeroes).” Vigorously amputating punishing, cyclically dense logic computation payloads away transferring them buffering comfortably inside the Main Loop operations while brutally restricting the scope of ISR architectures specifically establishing pure rapid “Event capture-and-flag” sentry mechanics embodies the pinnacle of mastery characterizing elite Embedded mercenary programmers globally.
If interacting heavily engaging aggressive firmware deconstructions radically excavating tearing directly across the absolute bleeding edge silicon processor components resonates heavily alongside you, or perhaps you privately nurse severe psychological trauma experiencing devastating hardware crashes resulting from arrogantly ignoring clearing the Flag within an ISR matrix operating under grueling client delivery pressure (Rest assured, the Dark-Eyed Engineer has repeatedly survived such trench warfare bombardments! 😅)—never hesitate establishing tactical comms! Drop your shields, share your heaviest localized war-casualties, and ignite deep philosophical systems debate interacting alongside the active veteran community currently populating the www.123microcontroller.com engineering staging ground immediately! Stay locked and secure. We intercept further algorithmic vulnerabilities operating entirely within upcoming technical intelligence dispatches. Happy Coding operating while submerged directly inside the fiery Interrupt parameters, cyber engineers!