Integer Promotion: When C's 'Good Intentions' Break Type Safety and Spawn Bugs

Integer Promotion: When C’s “Good Intentions” Break Type Safety
Hello fellow engineers and developers at 123microcontroller.com! Today, we are deep diving into the underlying architecture of the C language that every Embedded Systems developer will eventually encounter (and probably be bitten by): Integer Promotion.
When we discuss Type Safety in modern programming languages, systems typically impose extremely strict boundaries ensuring specific data types are never misused. However, the C language was forged to intimately control hardware. Therefore, C deliberately chose extreme flexibility, executing hidden “Implicit Conversions” automatically in the background. In this specific domain, “Integer Promotion” acts as one of the most confusing mechanisms and a primary pitfall that violently shatters Type Safety within System Programming! Let’s crack open the hood and expose exactly how this engine operates!
Core Concept: Type Safety vs The Integer Promotion Mechanism
To clearly visualize Type Safety, imagine “electrical sockets and plugs.” Strong typed systems aggressively reject plugging a 110V plug into a 220V socket to avoid explosions. Modern languages scream violently if you combine strictly different types. Conversely, C is a “Weakly Typed” language that generously hands you a universal adapter, silently coercing and mutating data types behind your back.
One of the most recurring implicit conversions is Integer Promotion:
- The Linguistic Definition: Any narrower data type (Narrow Data Types) such as
char,short,_Bool, or Bit-fields (whether explicitly signed or unsigned) will be systematically “Promoted” upward to become anint(or anunsigned int) “before” ever being actively processed in mathematical operations (Arithmetic) or Boolean comparisons. - The “Good Intentions” of C: Why does C blindly force this?
- It actively shields against mathematical Overflow. Imagine calculating two 8-bit
charvariables multiplying them and then dividing by a third. Promoting them to a 32-bitintbefore calculating guarantees the intermediate values never blast past the 8-bit boundary! - It serves as a historical legacy (a Kludge) from the early architectural era to assist Compilers in weaving Machine Code. Feeding uniform data structures (matching strict Register widths like 16-bit or 32-bit) into the ALU guarantees incredibly rapid and fundamentally natural calculations directly targeting the silicon level.
- It actively shields against mathematical Overflow. Imagine calculating two 8-bit
The Fracture of Type Safety: Despite possessing solid engineering benefits, Integer Promotion inherently betrays Type Safety because “the programmer is often utterly oblivious that the data type has been mechanically swapped!” The most catastrophic collisions trigger when mixing Signed (negative capable) and Unsigned (positive only) architectures in the exact same expression.
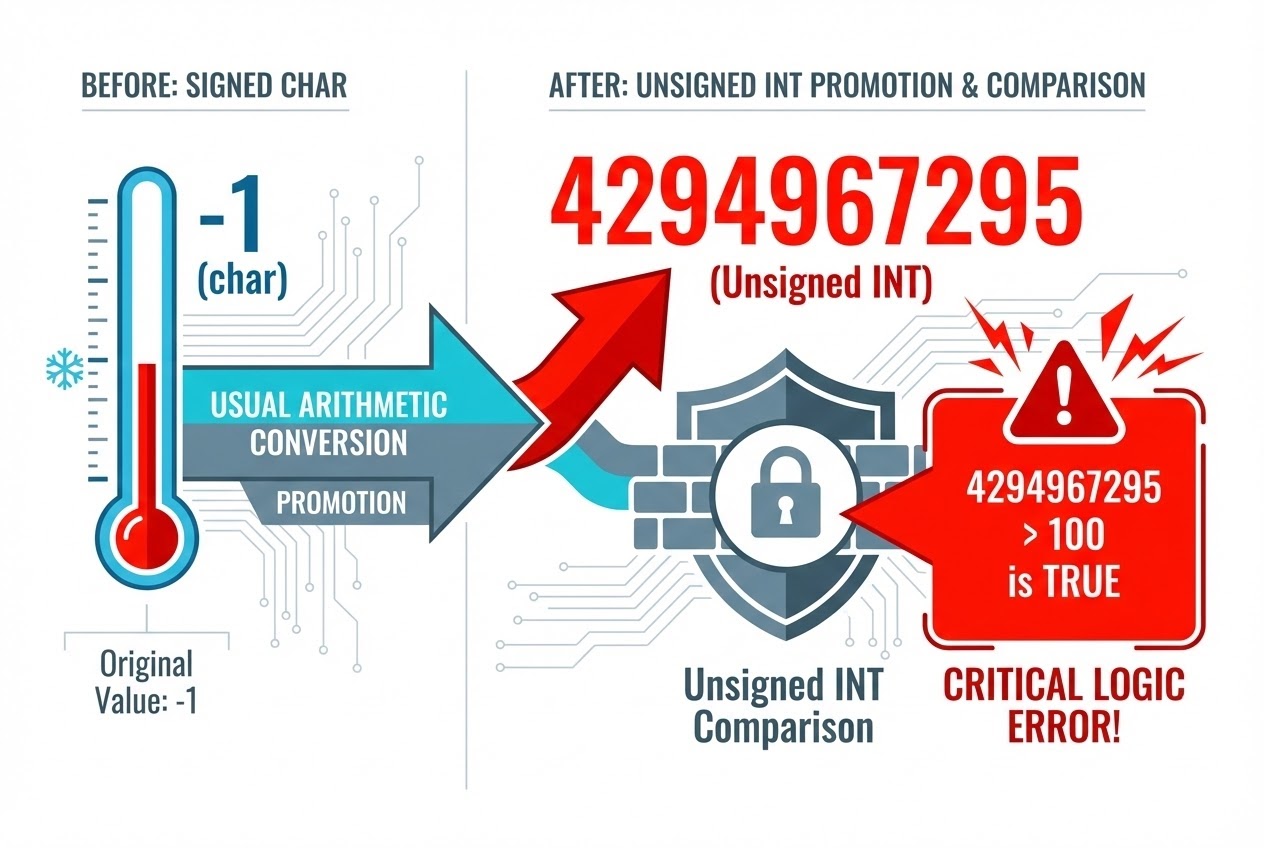
The ironclad rule: If a signed variable actively holding a “Negative” value is evaluated against an unsigned variable of exactly equal or superior size, the compiler will mutate that Negative variable specifically into an unsigned data type too! Because processors utilize the “Two’s Complement” structure, this transformation forcibly rips a simple -1 and interprets its raw binaries as a “Massive Positive Integer” (Specifically 4,294,967,295 in standard 32-bit architecture). Mathematical logic is immediately obliterated, infinite loops trigger, and security vulnerabilities rip wide open!
Code Example
Let’s inspect a terrifying classic example where Integer Promotion stealthily bypasses Type Safety, tricking us into analyzing completely wrong values!
#include <stdio.h>
#include <stdint.h>
int main(void) {
/* Imagine parsing a crucial temperature sensor capable of returning sub-zero values */
signed char temp_c = -1;
/* Establish a strict unsigned threshold limit */
unsigned int limit_ui = 100;
/*
* ❌ HIDDEN BUG spawned via Integer Promotion breaking Type Safety.
* Human logic: -1 is obviously less than 100. This should fail.
*/
if (temp_c > limit_ui) {
printf("DANGER: Temperature has exceeded safety limits!\n");
printf("Truth: 'temp_c' was aggressively evaluated as: %u\n", temp_c);
} else {
printf("Temperature status normal.\n");
}
return 0;
}
What exactly happened in this Code?
- The
temp_cvariable (declared assigned char) is trapped by Integer Promotion. C violently upgrades it into asigned int, managing to retain the exact-1value. - The Compiler notices it must now compare this evaluated entity against
limit_ui(which is definitively anunsigned int). The rigid “Usual Arithmetic Conversions” rulebook demands it mutually convert thesigned int(-1) directly into anunsigned int! - Forcing
-1into an Unsigned 32-bit boundary physically interprets the raw hex as4294967295. - The final executed comparison demands:
4294967295 > 100. This is mathematically TRUE. The error messages violently print despite the temperature actually being freezing!
Secure Coding Best Practices
To patch these terrifying Type Safety fractures generated by C’s good intentions, Expert C Programming guides alongside strict Secure Coding standards (SEI CERT) demand adopting these ‘Clean Code’ principles:
- Absolutely Never Mix Signed and Unsigned Variables: This is the paramount rule! Always block mixing Signed variables with Unsigned arrays directly within the identical evaluating Expression! Eliminating this eliminates the mutation.
- Actively Standardize Explicit Type Casting: Reject relying entirely on Implicit conversions operating automatically in the dark. If passing variables across differing system types is absolutely unavoidable (e.g. library values), aggressively forge an Explicit Cast (Coercion) physically visible in your code. Using
if ((int)temp_c > (int)limit_ui)mathematically directs the Compiler exactly what to execute while documenting your “explicit intent” for your engineering peers. - Exercise Maximum Caution Leveraging
<stdint.h>: Employing rigorously defined width integers (e.g.uint8_t,int16_t) is fundamentally excellent practice for embedded hardware. However, actively engrave into your memory that these specific variables are still unconditionally governed by Integer Promotion. The absolute second they are shoved into multiplication, division, or comparison expressions, C will ruthlessly strip their masks and inflate them into anint. - Activate Elite Compiler Warnings: Modern compilers wield advanced analytical architectures capable of pinpointing “Type mismatch” violations in real-time. Boost your warning flags intensely (e.g. utilizing
-Wall -Wextraor explicitly-Wsign-comparevia GCC). An aggressive compiler acts as your strongest frontline defense mechanism!
Conclusion
The architecture of C was meticulously forged optimizing for raw speed and minimizing hardware constraints. In this scope, “Integer Promotion” stands brilliantly as a safeguard intercepting intermediate Arithmetic Overflow while concurrently squeezing every drop of efficiency out of CPU Registers. However, it violently swings backwards acting as an insidious double-edged sword that aggressively perforates the boundaries of Type Safety through stealthy Implicit data substitutions. For hardware or System Programming engineers, this singular mechanic forms the bedrock responsible for the most brutally elusive bugs in history!
To elevate into highly professional Embedded Engineers, we must intimately recognize and comprehend C’s deeply eccentric underlying behaviors. We sincerely hope this architecture breakdown heavily arms your programming perspective! For any fellow developers fascinated with unraveling secretive memory management or hardcore C syntax for microcontrollers, make sure you eagerly subscribe to our upcoming in-depth architectural breakdowns. Jump into the community and share your projects directly over at www.123microcontroller.com. See you all in the next article. Happy Coding!