Hardware Interaction: The Core Philosophy of Speaking to Bare-Metal Silicon via Bit-Level C
Introduction: The Path of the Iron Chef in the Silicon Realm
Greetings, hardware engineers and elite developers of the www.123microcontroller.com collective! Today, the dark-eyed engineer returns to ruthlessly dissect the brutal, underlying truth defending the C programming language’s immortal crown atop the Embedded Systems hierarchy. The undisputed domain of absolute superiority: “Hardware Interaction”—the visceral art of engaging directly with raw processor silicon.
When deploying high-level code onto generalized PC environments (encompassing abstracted operating systems like Linux or Windows/macOS), the horrifying complexity native to the physical hardware topography is mercifully shielded behind thousands of lines of bulletproof OS API abstractions. An application developer requires zero microscopic comprehension of the electrical current draw required to blast an ASCII character onto an LCD matrix, nor the specific routing pathways navigating the motherboard pins. Conversely, entrenched deeply within the trench warfare of Embedded Systems, firmware engineers mathematically emulate “A master chef forced entirely to manually forge the cast-iron stove, regulate the pressurized gas lines, and micromanage the atomic combustion of the flame.” We are strictly commanded to articulate logic explicitly at the electrical circuitry horizon! Fortunately, the architectural DNA underlying C was explicitly engineered specifically to dominate, aggressively penetrate, and effortlessly command the lowest hardware topography achievable. Let us forcibly rip open the industry-standard engineering doctrines today, exposing strictly how global elite programmers weaponize C to communicate directly with cold silicon logic.
The Arcane Bridge Linking C Bytecode to Physical Silicon
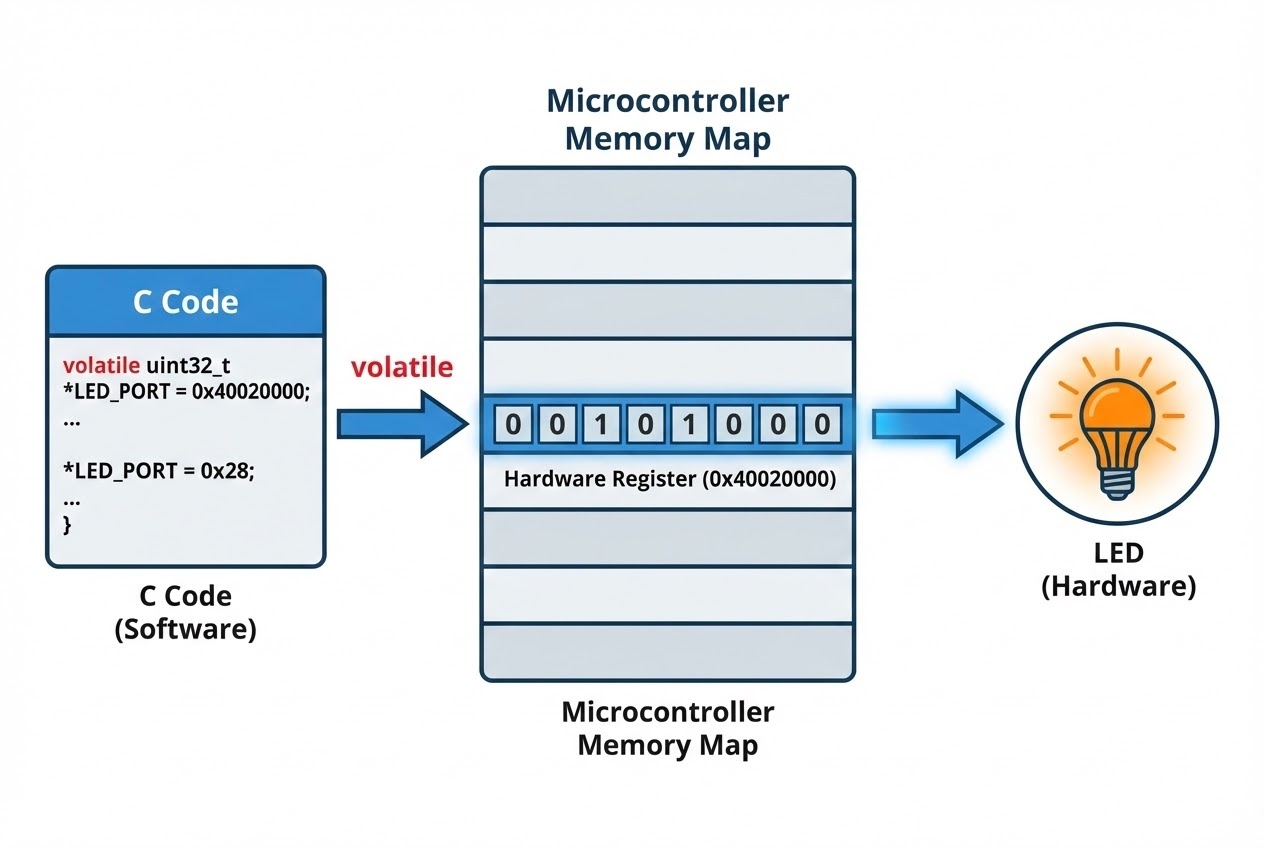
When enforcing logic upon a microcontroller (instructing an agonizingly bright LED to ignite or commanding a thermal sensor to spill its raw kinetic telemetry), the central processor does absolutely not communicate with those physical peripheral devices via high-level interpreted magic. Instead, the CPU initiates aggressive data handshakes by writing explicitly into localized physical hardware control nodes classified universally as Registers. Premier engineering architecture documents articulate this rigid ecosystem precisely:
- 1. Control and Status Registers (The F-22 Cockpit Switchboards): The processor negotiates and extracts telemetry from peripheral sub-systems strictly navigating a consolidated matrix of specialized Registers built specifically to impose commands (Control) and harvest real-time telemetric feedback (Status). Drawing a visceral operational parallel, visualize a Register array mirroring the hyper-complex overhead switchboard and diagnostic instrument clusters within a fighter jet cockpit. Actively manipulating a binary bit coordinate (0 transitioning to 1) localized within a cluster Register is technically synonymous with violently throwing a physical kill-switch, instantly energizing or terminating a live electronic circuit.
- 2. Memory-Mapped I/O (The Illusion of Assimilating Hardware into RAM Architecture): Contemporary processors (heavily dominated by the brutal efficiency of ARM architectures) aggressively default to executing “Memory-Mapped” connection logistics. Systematically, this implies that the raw silicon data-locks (Registers) belonging to diverse peripheral hardware are physically intercepted and artificially forced to materialize identically adjacent to standard RAM within the unified global Memory Map perimeter. The monumental tactical advantage? This architecture grants embedded firmware developers unconditional authority to hijack standard, incredibly nimble C language syntax constraints—fabricating highly optimized Pointers, Structs, or Unions to mercilessly breach those Register Addresses and forcibly write bytecode modifications precisely as though manipulating randomized dynamic software Variables lazily floating within RAM.
- 3. The Primary Armor-Piercing Tools: Pointers and Bitwise Operations:
Having successfully acquired the absolute, unencrypted Memory Address of the targeted silicon, the embedded software explicitly aims an optimized Pointer payload locking rigidly onto those coordinates. Following target acquisition, developers ruthlessly deploy low-level Bitwise operators specifically—
|(OR),&(AND),~(NOT), and^(EXCLUSIVE-OR)—to enact vicious surgical strikes: Setting (overloading to a 1 logic state), Clearing (nuking to a 0 logic state), or Toggling (inverting the current logic) explicitly localized bit targets instantly, critically achieving this action without casting destructive ripples overriding companion bit configurations residing within the exact same Register parameter block. - 4. Polling vs. Interrupts (The Tactical Science of Harvesting Hardware Telemetry):
Immediately upon a hardware module concluding its designated processing workload, it incurs a non-negotiable architectural obligation to transmit a notification vector intercepting the controlling software logic. Two divergent warring methodologies govern this exact reception:
- Polling (The Endless Roving Sentry Guard): The firmware enforces a ruthless, perpetual executing Loop sequence actively besieging the hardware’s Status Register continually, voluntarily burning and wasting infinitely valuable CPU instruction cycles solely verifying process completion (Philosophically mirroring a human pacing and relentlessly verifying a washing machine status window every 60 seconds).
- Interrupts (The Asynchronous Lightning Strike): Alternatively, the peripheral hardware calculates independence, blasting an asynchronous electrical shockwave traveling parallel logic lines, physically electrocuting the CPU instruction pipeline. This violently paralyzes the CPU’s current thread state matrix mid-execution, freezing the system immediately—exclusively to forcibly warp execution vectors plunging into a localized, ultra-priority code block labeled an Interrupt Service Routine (ISR) designed specifically to pillage the payload data. (Mirrors the washing machine violently sounding a maximum-volume klaxon alarm the second the thermodynamic load hits absolute zero).
Raw Code Exhibition: Bare-Metal Register Domination Tactics
Prepare to deconstruct a master-class exhibition explicitly defining “Bare-Metal” C syntax (executed strictly devoid of training wheels or the buffer of a high-level RTOS). This payload physically assaults Memory-Mapped structural confines identically aligning to standard GPIO (General-Purpose Input/Output) processor architectures embedded deep relative to an STM32-series microcontroller platform. This script represents the pure distillation of the authentic firmware hacker’s hardware soul!
#include <stdint.h>
/*
* 1. Mathematically anchoring the absolute silicon Base Address parameters rigidly copied from the encrypted Datasheet Grimoire.
* Observe the extremely hostile deployment of advanced Typecasting protocols forcibly subjugating C into interpreting raw integer strings as active memory Pointers.
* We inextricably fuse the impenetrable 'volatile' Keyword invoking maximum protective protocols buffering erratic hardware communications.
*/
#define GPIOA_BASE 0x40020000
#define RCC_BASE 0x40023800
/* 2. Etching definitive Pointer Macro abstractions acting as targeting systems dialed explicitly to designated sub-Registers (injecting localized coordinate Offsets). */
#define GPIOA_MODER (*(volatile uint32_t *)(GPIOA_BASE + 0x00))
#define RCC_AHB1ENR (*(volatile uint32_t *)(RCC_BASE + 0x30))
void setup_hardware(void) {
/*
* 3. Injecting raw electrical lifeblood (System Clock frequency) feeding aggressively into Port A hardware block.
* We wield the Bitwise OR assignment overload operator (|=) to brutally hammer hardware-bit 0 upwards locking at logic level 1, flawlessly circumventing logic pollution within neighboring configurations.
*/
RCC_AHB1ENR |= (1 << 0);
/*
* 4. Morphing the physical structure of Pin 5 (Port A matrix) transforming behavior into a driving Output conduit capable of discharging voltage.
* The PA5 architecture strictly sequesters control bits index 10 alongside 11 serving as steering mechanisms (denoted: MODER5[1:0]).
* We successfully slam bit 10 high to state 1 (Technically manifesting forced Output Mode processing routing).
*/
GPIOA_MODER |= (1 << 10);
}
int main(void) {
// Ignite the embedded Silicon Matrix
setup_hardware();
// The Infinite Firmware Singularity Event loop
while(1) {
/* Heartbeat cycle perpetuating embedded system autonomous functionality endlessly */
}
return 0; // Operation mathematically restricted from achieving execution naturally.
}
Defensive Countermeasures Against Lethal Silicon Communication Catastrophes
Before charging the frontline attempting unregulated, volatile bidirectional communication with hostile localized hardware interfaces, international firmware standards heavily advocate absorbing these absolute bedrock directives and fatal coding hazards specifically documented by elite systems architects:
- The Indestructible Ward Keyword
volatile: Recognize this as the single most hyper-critical defensive spell shielding your firmware’s mortality! Spawning a Pointer assigned explicitly seeking peripheral hardware silicon Address blocks (intentionally parsing oscillating sensor telemetry or sequentially executing destructive write cycles) guarantees absolute environmental volatility—the numeric state enclosed within that geographical byte array is absolutely expected to oscillate or violently mutate outside the rigid operational oversight bound natively to the executing firmware process. Neglecting the iron-clad application ofvolatileviolently provokes the dangerously overly-intelligent C-Compiler logic engines into performing malicious Code Optimization sweeps. Assuming complete operational ignorance regarding physical hardware autonomy, the compiler brazenly deletes or consolidates identical read/write instruction clusters assuming pure redundancy. Enforcingvolatiledictates a literal threat against the Compiler engine: absolutely commanding it to surrender caching procedures and mechanically rip fresh silicon status updates forcefully straight from the hardware pins directly spanning across every single execution cycle demanding that memory. Assumed values are strictly prohibited logic. - The Dawn of Halo-Systems (HAL), The Twilight of Raw Syntax: Admitted openly: aggressively hard-coding the command string
*((int*)0x0070C1) |= (1 << 2);technically fulfills electrical actuation correctly. However, deploying code obfuscated to this savage degree instigates unparalleled horrors against subsequent code-maintainability protocols! Global protocol regulations universally advise migrating heavily onto standardized architectural Header files, intertwining effortlessly within layered Hardware Abstraction Layer (HAL API) toolkits traditionally generated and packaged explicitly directly from the overarching Silicon Vendor. These comprehensive interface frameworks systematically package highly hostile naked silicon Registers structurally organizing them employing incredibly logicalstructencapsulation packages. Consequently, our barbaric, hostile memory syntax elegantly morphs becoming:GPIOA->CRL |= 1 << 2;. This structural layout acts substantially more humane to visually parse, vastly more sequentially uniform, and incredibly heavily guarded against lethal compilation typos. - The Midair Logic Collision Event (Race Conditions in Hardware): Fusing sophisticated asynchronous Interrupt processing frameworks simultaneously overlapping legacy Read-Modify-Write logical manipulation algorithms natively hammering static Registers (ex: deploying
|=masks or aggressive&=clearing algorithms) acts as a highly volatile catalyst. Given a freak scenario causing a massive Interrupt burst to detonate intersecting parallel logic absolutely precisely centered amid the exact nanosecond your software architecture physically opened the register port preparing to manipulate state data, this collision catastrophically shatters and irreversibly mutates the silicon logic parameters suspended mid-read (Firmware terminology categorizes this disaster specifically as a critical Race Condition payload). Professional-grade firmware engineering permanently shields this threat structurally encasing hazardous Register mutation operations within hardened “Critical Sections,” purposefully executing tactical logic strikes (exemplified typically by issuing brutal logic overrides momentarily Disabling All Interrupt Processing matrices globally) explicitly when forcing interaction atop highly contested shared system Registers. - Datasheet Dominance: The Sacred Vow of the Silicon Tamer: Orbiting casually among the abstract safety native to PC developer ecosystems affords programmers the luxury to arbitrarily salvage code snippets infinitely scrolling across Stack Overflow instances. Parachuting rapidly into the unforgiving hellscape denoting bare-metal Embedded Systems logic radically shifts the atmospheric pressure. “The Core Silicon Datasheet operates exactly resembling an infallible, absolute religious text commanding life and death operational authority.” You assume uncompromising personal responsibility absolutely requiring deeply infiltrating and decoding the manufacturer’s encoded Memory Map layout arrays, establishing intimate tactical awareness of overlapping Bit-Fields buried inside targeted Register clusters, and embracing a paranoid diagnostic lifestyle interrogating highly classified Errata documentation (Specialized engineering apologia manuscripts published formally by the original manufacturer publicly detailing irredeemable localized silicon bugs mathematically baked irrevocably into early-batch manufacturing runs). This exhaustive due-diligence acts non-negotiably mandatory perpetually prior to initiating even the basic keystrokes aiming machine code directed confronting newly encountered mystery-hardware elements resting on your engineering bench.
Conclusion
The overwhelming supremacy driving Hardware Interaction manifests serving as the explosive flashpoint directly unifying invisible, ethereal code algorithms silently floating behind your PC monitor screen directly morphing transitioning violently converting physics generating physical kinetic momentum operating raw hardware reality shaping the material world dominating your surroundings. The baseline C-language ecosystem benevolently endows firmware architects unlocking god-tier manipulation systems enabling unparalleled access to violently drill and micromanage atomic byte strings deeply buried embedded inside microscopic processor matrix layouts operating entirely free from external API restraints. Leveraging incredibly overpowered engineering instruments (predominantly executing tactical Pointers payloads, aggressive Bitwise algebraic surgical strikes, backed unconditionally utilizing defensive volatile command encryptions) fully internalizing these core logic axioms remains inherently the absolute bedrock initiating first step aggressively accelerating your overarching goal dominating and officially ranking globally classified definitively reigning as a hardened Embedded Systems Firmware Engineering mastermind.
If you specifically thrive on deep-dive surgical code deconstruction tearing aggressively entirely through the superficial abstraction layers, ripping outward exploring the volatile reality buried operating deep within atomic processor logic execution—or perhaps bearing the emotional trauma fighting unexplained phantom hardware bugs stemming universally resulting overlooking deploying the absolute volatile defensive shielding, deploy rapidly toward the war-room matrix communication hub! Interface heavily displaying raw battle-hardened firmware scars heavily engaging fellow tactical coders universally discussing optimization techniques exclusively on the bleeding-edge architecture forums located directly within the www.123microcontroller.com engineering syndicate! Secure your parameters tightly, the subsequent devastating algorithmic architecture demolition operations swiftly approach intercept vectors in the following publication dispatch! Stay sharp; Happy Bare-Metal Coding to the cyber-vanguards!