Callbacks in the Hardware Realm: Master Abstraction to Inject Supreme Flexibility into Embedded C
Introduction: Severing the Arteries of Tightly Coupled Hardware Drivers
Greetings, elite systems engineers and bare-metal hackers infiltrating the www.123microcontroller.com network! The dark-eyed engineer has logged back into the mainframe combat zone. Today, we initiate a brutal architectural upgrade—a highly advanced tactical maneuver specifically calculated to aggressively mutate your standard, rigidly fragile C code pipelines into indestructible, modular, professional-grade software architectures. Prepare to master the aggressive deployment of Callbacks squarely within the hostile, unforgiving territory of raw bare-metal hardware control.
In our prior devastating technical dispatch, we totally completely dismantled the hyper-kinetic mechanics powering Interrupt Service Routines (ISR). We established that an ISR fundamentally represents enraged peripheral hardware violently violently ripping the CPU out of its operational trance by screaming, “Maximum priority execution required immediately!” However, a catastrophic architectural fallout persistently plagues amateur engineers: If you lazily and incompetently dump massive, bloated chunks of foreground Application Logic straight into the blazing hot core of an ISR conduit, your meticulously crafted hardware driver becomes permanently mathematically shackled, suffering an agonizing, irreversible flesh-fusion precisely to that specific single-use application iteration. It becomes completely ruined, “Tightly Coupled,” and irrevocably cursed—rendering it absolutely impossible to scavenge or port to subsequent combat architectures without extensive demolition.
To utterly decimate this terrifying structural bottleneck, veteran tier-one software architects mobilize an unstoppable strategic weapon designated the “Callback.” This mechanism performs the role of an absolute surgical scalpel, violently bifurcating and separating execution domains flawlessly. Today, we forcefully decrypt massive international engineering data-logs to observe exactly how hardcore silicon veterans deploy Callbacks specifically to dominate hardware interfacing architecture!
Theoretical Core Detonation: The Essence of the Callback and Hardware Superiority
Submerged deep inside the raw, unpolished standard syntax of C memory management, the Callback mechanism is aggressively forged utilizing an incredibly sharp memory weapon universally classified as the Function Pointer. By clinical definition, it constitutes a highly specialized pointer variable—but rather than cowardly tracking a mundane integer cache in space, it physically maintains a hyper-accurate laser lock precisely targeting the unyielding “Geometric Memory Address” of an entire executable function logic block. While the raw Interrupt mechanism graciously empowers our architectures to postpone the desperate temporal decision resolving “Exactly When must we detonate this hardware sequence?” strictly towards the chaotic runtime threshold, the Callback matrix operates sequentially as the perfect complement. It empowers developers to ruthlessly isolate and postpone the critical logical decision calculating “Exactly Which specific function algorithm must actually handle the resulting payload?”
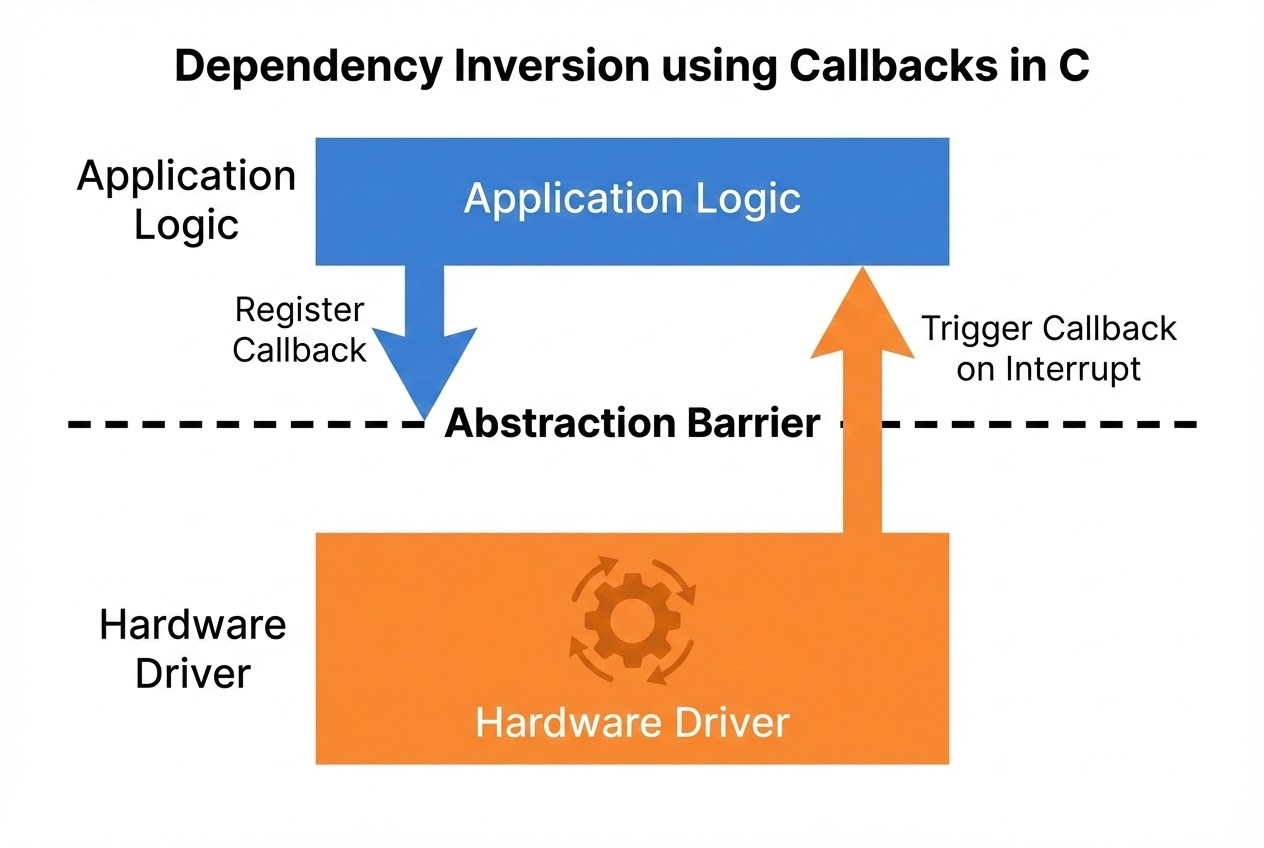
Focusing visually zooming outward grasping the overarching macro-scale context of elite Bare-Metal Hardware Interaction, high-clearance architectural intelligence blueprints firmly outline the critical role and infinite potential of the Callback parameter entirely exactly as outlined below:
- 1. Weaponized Abstraction & Strategic Information Hiding (Encapsulation): The most devastatingly supreme strategic advantage achieved by the Callback mechanism is its manifestation strictly as an impenetrable titanium firewall—an absolute “Level of Abstraction.” It guarantees elite protocol engineers possess the omnipotence to architect raw, brutal “Low-Level Hardware Drivers” (e.g., configuring raw OLED silicon displays) maintaining total blinding indifference toward whatever chaotic data-mutation the upper-echelon UI Application logic subsequently decides to inflict upon that data. This permits us to seamlessly execute total “Encapsulation,” forcefully scrubbing away horrifying cryptic hardware silicon register complexities completely out of visible range—denying amateur top-level app developers the destructive capability of accidentally reaching down and nuking the lower circuit geometries without authorization.
- 2. Forcing the Polarity Shift: The Dependency Inversion Principle (DIP): The calculated transaction mandating passing a Callback function parameter matrix downward, explicitly into the hostile hardware driver structure granting it localized execution authority, signifies the execution of an absolutely monumental architectural protocol: “Dependency Inversion.” The theoretically unintelligent, localized hardware driver (For instance, a localized SPI gyro-sensor parsing module) permanently ceases requiring any hardcoded “Dependence” tracking or acknowledging the heavy logic tree comprising the host’s upper-level Application structure! It functions entirely functionally blind, negotiating only mathematically securely by routing calls directly through the purely standardized, abstract interface exclusively provided by the localized registered Function Pointer channel.
- 3. Architectural Embedding Within the Device Struct Payload Matrix:
Operating intensely within complex multi-peripheral communications array bus sectors (dominantly I2C channels or high-speed chained SPI topologies), hardware tactical teams almost exclusively engineer unified
structblueprints mathematically representing the physical digital souls belonging individually to external hardware payloads. Tightly packed embedded directly inside thesestructentities are standard ID passports, violent data cache buffers, and—most critically to survival—the devastatingly essential Callback Function Pointers. These are specifically locked and loaded waiting aggressively to forcefully erupt and trigger only precisely when the brutal objective of absorbing a payload completes flawlessly, or paradoxically, when a critical error forces the operation into an apocalyptic fail state. - 4. Deep Symbiotic Fusion Penetrating ISR and DMA Architectures: Combat engineers retain the authorization to seamlessly fuse raw Interrupt signals violently compounding directly in tandem with Callback algorithms generating unparalleled monstrous real-time execution dominance! The prime devastating example: Explicitly commanding a localized DMA (Direct Memory Access) rogue silicon mercenary to aggressively tunnel huge uncompressed data payloads directly across the memory matrix unsupervised. Immediately when the DMA vector logs a successful termination run, the underlying bare-metal Operating System layer tracks the triggering localized hardware Interrupt, automatically violently flinging open the directory and triggering the pre-registered upper-Application Callback function instantaneously avoiding a single processing cycle of lag. Alternatively, a heavily restricted ISR execution bubble might assume the singular ultra-fast responsibility strictly evaluating targeting priorities, calculating the appropriate designated Callback target, or surgically toggling a holding Flag state, purposely ensuring the sluggish Main Loop subsequently drags itself over and manually executes the Callback pipeline. This entirely prevents catastrophic system deadlock from accumulating wasted execution milliseconds inside a radioactive priority ISR trench.
Firing Live Code Rounds: Surgically Excising the Driver from the Malignant Application
Proceed to analyze and dissect the tactical approach, deploying brutal Clean Code structural algorithms to design an impenetrable external Hardware Driver entity. We architect it maintaining an open, vulnerable docking portal intentionally authorizing an independent upper-tier Application script to forcefully register and dock its own customized secondary Callback Function coordinate (Witness the immaculate glory of raw Dependency Inversion execution). Observe exactly how we absolutely guarantee the hardware protocol stack achieves total operational escape velocity, flawlessly disconnecting any tightly coded dependencies locking it to the tangled, sluggish spaghetti framework belonging to the primary executing program matrix below.
#include <stdint.h>
#include <stdbool.h>
#include <stdio.h>
/* 1. Carve The Tombstone Blueprint. Architect the core structural definition regulating the targeted Callback Function Pointer strictly awaiting incoming UART byte extraction signatures. */
typedef void (*uart_rx_callback_t)(uint8_t data);
/* 2. Assemble the hardened internal Device Struct capsule geographically wrapping the physical hardware ghost—and brutally nest the lethal Callback Pointer deep within its payload walls. */
typedef struct {
uint32_t base_address;
uint32_t baud_rate;
uart_rx_callback_t on_receive_cb; /* The Upper Application logic algorithm payload physically jacks directly straight into this precise variable dock. */
} UartDevice;
/* The static localized shadow variable exclusively tracking our hardware soul parameter (Functionally sealed and quarantined operating strictly masked inside the opaque Driver .c sector file). */
static UartDevice my_uart = { .base_address = 0x40011000, .baud_rate = 9600, .on_receive_cb = NULL };
/* 3. Drop the drawbridge enabling the public interface portal! Granting clearance allowing arbitrary App-level algorithms to surgically register their targeted execution vectors internally down into the low-level hardware structures. */
void uart_register_rx_callback(uart_rx_callback_t callback) {
my_uart.on_receive_cb = callback;
}
/* 4. Simulating the chaotic engagement parameter activating the ISR (Interrupt Service Routine) specifically assigned tracking UART buffer overflows. */
void UART_IRQHandler(void) {
/* (Tactical Simulation) Pretend the localized CPU just aggressively violently scraped the explicit Hardware Register and secured a live hex target 0x41 (ASCII 'A'). */
uint8_t received_byte = 0x41;
/* (Absolute Priority) Violently erase and neutralize the bleeding hardware Interrupt Flag immediately securing sequence integrity... */
/* 🛡️ THE LETHAL PRIME DIRECTIVE (BEST PRACTICE): It is an absolute mathematically enforced suicide-prevention mandate establishing a 'NULL' check validation confirming the payload vector isn't empty prior to arrogant Callback execution! */
if (my_uart.on_receive_cb != NULL) {
my_uart.on_receive_cb(received_byte); /* Unleash hell. Detonate the target Callback sequence forcefully entrusted internally by the oblivious application architects. */
}
}
/* =========================================
* CROSSING THE BORDER: Operating securely within chaotic Application Code (The Slow Main Program Reality Axis)
* ========================================= */
/* The massive bloated calculation algorithm explicitly required and demanded structurally from the application side to crush numbers the split second raw silicon confirms a new byte acquisition. */
void process_sensor_data(uint8_t data) {
printf("Application received sensor data: %c\n", data);
/* At this explicit execution matrix coordinate, the upper algorithm savagely attacks the fresh byte payload calculating massive float geometries! The underlying hardware driver operating below is brutally oblivious maintaining 100% logic ignorance regarding these operations. */
}
int main(void) {
/* File protocol paperwork. Aggressively transfer and digitally merge the function pointer 'process_sensor_data' downward establishing permanent registration into the hardened Hardware Driver cache parameters. */
uart_register_rx_callback(process_sensor_data);
/* Close optical sensors. Visualize executing a synthetic hardware-driven Interrupt blast trajectory mimicking a live sensor read. */
UART_IRQHandler();
return 0; // Terminate tracking sequence beautifully.
}
Proximity Defcons: Navigating the Double-Edged Blade of the Callback Architecture
Deploying Callback geometry violently injects unparalleled architectural freedom allowing unbounded abstract firmware structures, undeniably! However, this terrifying power unconditionally demands maintaining absolutely crushing engineering accountability constantly crushing down against your architectural foundations! Universal code-safeguard survival protocols frantically emphasized globally across the highest elite C engineering command structures strictly require absolutely zero deviation encompassing these devastating parameters:
- The Phantom Bullet Tragedy (Lethal Threat of Invalid Function Pointers): The single most brutally catastrophic, apocalyptic penalty incurred assuming blind deployment integrating the Callback architecture remains the arrogant developer entirely forgetting the terrifying mathematical baseline logic constraint: “It structurally just manifests fundamentally as a volatile Ghost Pointer.” If an incompetent engineer pathetically fails completely strictly establishing aggressive mathematical initialization routines zeroing out the matrix (Leaving an uninitialized variable floating wildly in logic), or idiotically permits the trajectory tracker failing shifting establishing a phantom ‘Invalid Address’, attempting to recklessly force-execute the Callback (Dereferencing the pointer) instantly weaponizes random garbage memory cache patterns forcing your silicon CPU to suicidally interpret random chaotic electrical noise natively incorrectly as legitimate execution OPCODES (Executable instructions). This triggers an instant, unrecoverable, violent terminal hardware system self-destruction Event chain (Unanimously labeled by mortified programmers as ‘Undefined Behavior’). THE OMEGA-CLASS SURVIVAL LAW: You are fundamentally obligated establishing an unbreakable shielding evaluation
if (callback != NULL)fortifying the immediate entry proximity surrounding every single Callback engagement parameter! - Psychotic Context Transitions: Mutating the Execution Domain Matrix: If an obscure, massive Callback target suddenly accidentally wins the horrific lottery experiencing immediate force-activation specifically originating directly sourced from deep inside the radioactive confines of an asynchronous ISR, that mundane, bloated Callback function immediately undergoes a terrifying involuntary logic-identity transformation universally re-classifying its operating parameters classifying it instantly fundamentally as a “Subsequent Extension Component of the Critical Emergency Interrupt.” This inherently translates enforcing absolute zero-tolerance forbidding executing Callback logic incorporating sluggish, agonizing internal loops (Blocking APIs) or universally banning standard slow algorithms including
printfoperations—or significantly worse—attempting memory hijacking operations universally spanning themallocprotocol! Violating this rule guarantees completely crashing the CPU pipeline intentionally inducing critical latency bottlenecks inducing guaranteed software deadlock logic cascades causing hardware-system asphyxiation. - The Endless Void of Reentrancy and Global Variable Collisions: Functions temporarily masquerading behaving identically as Callback targets retain the incredibly dangerous structural authorization manifesting violently firing activating themselves absolutely whenever (Chaotic Asynchronous execution algorithms). Supposing some clinically insane programmer structures that target function executing dangerous extraction logic slicing into mutating publicly accessible Global variables completely isolated existing separately outside the scope covering its protective Stack containment architecture (A highly fragile Shared Variable payload), you immediately become locked battling the nightmare generating terrifying ‘Race Conditions’! The engineer carries the absolute burden definitively guaranteeing completely executing the memory alteration strike must utilize mathematically flawless brutal ‘Atomic Operations’ (One-shot cycle lock strikes), or implementing iron-clad Mutex/Interrupt-Disable firewall locking architectures flawlessly guaranteeing absolutely zero rogue parallel ISR drop-in logic corruptions halfway across the transaction process.
Conclusion
The elite tactical strategy encompassing seamlessly fusing Callback methodologies violently interfacing with massive brute-force Hardware Interaction physics solidifies definitively as the supreme, ultimate grand-master maneuvering technique dominating our sector! It possesses the surgical capability to utterly decapitate separating the “Hardened silicon execution mechanics” flawlessly away, purging them from the bloated, fragile dependency structures crippling the “Complex application business logic”. It represents the heavily guarded shadow architecture empowering veteran heavy-infantry programmers, allowing them to mold violently shifting firmware deployments displaying total fluid adaptability. This algorithm authorizes establishing impenetrable reusable library stockpiles generating infinite hardware integrations, while standing phenomenally resilient flawlessly managing terrifying unpredicted Asynchronous Events (Random Hardware Triggers) with absolute breathtaking, elite clinical efficiency.
If this engineering unit aggressively hungers for more brutal code architectures and feels a violent demand to dissect active source-code teardowns defining hardcore bare-metal Driver structures wrapping brutal I2C or rapid-fire SPI silicon—fully locked embracing massive Callback infrastructure—do not permit hesitation to derail your momentum! Rip the steering wheel, crash directly into the forum logic, and detonate engaging brutal structural coding debates immediately on the frontline deployment base stationed strictly at www.123microcontroller.com! We actively anticipate re-engaging your unit within the next brutal firmware technical teardown. Stay lethal, and Happy Hardware Code hacking, infantry commanders!