Error Detection (Checksums & CRC): The Guardians of Data Integrity, Not the Sentinels of Security!

Introduction: The Thin Line Between Error Detection and System Collapse
Greetings, elite systems engineers and bare-metal combatants of the www.123microcontroller.com network! The dark-eyed engineer has emerged back onto the command-line interface. Today, we confront a fundamental classic—an absolute rite of passage that every hardcore hardware engineer inevitably slams into when architecting communication buses (be it UART, I2C, or SPI) or when brute-forcing read/write cycles directly into memory silicon (such as Flash or EEPROM). We are diving deep into the epic operational framework of Error Detection.
In the unforgiving, hostile environment governing raw hardware, high-speed digital electrical signals sprinting across copper traces face severe probabilities of catastrophic disruption heavily induced by Electromagnetic Interference (EMI / Noise). Simultaneously, aging memory cells inherently degrade over aggressive usage cycles. These brutal physical realities constantly trigger our microscopic armies of binary 0s and 1s to suffer violent “Bit-flips,” mutating violently away from their original, pristine payload. Fortunately, advanced mathematics bestows upon us legendary mechanical filters exactly like Checksums and CRCs serving as our frontline verification sentinels. However… a terrifying, systemic drama repeatedly erupts when amateur programmers fatally “misinterpret” the operational envelope, deploying these exact mathematical tools desperately functioning as Cryptographic Security amulets attempting to block elite hackers from reverse-engineering payloads. Let me state this with absolute clarity: that misguided logic guarantees an apocalyptic system breach! Today, we brutally rip open the truth, dissecting exactly how top-tier architectural intelligence documents categorize this massive failure, and we isolate exactly which tactical weapons you require to ensure your project’s survival!
Core Theory Autopsy: Integrity Gatekeepers vs. Security Vaults
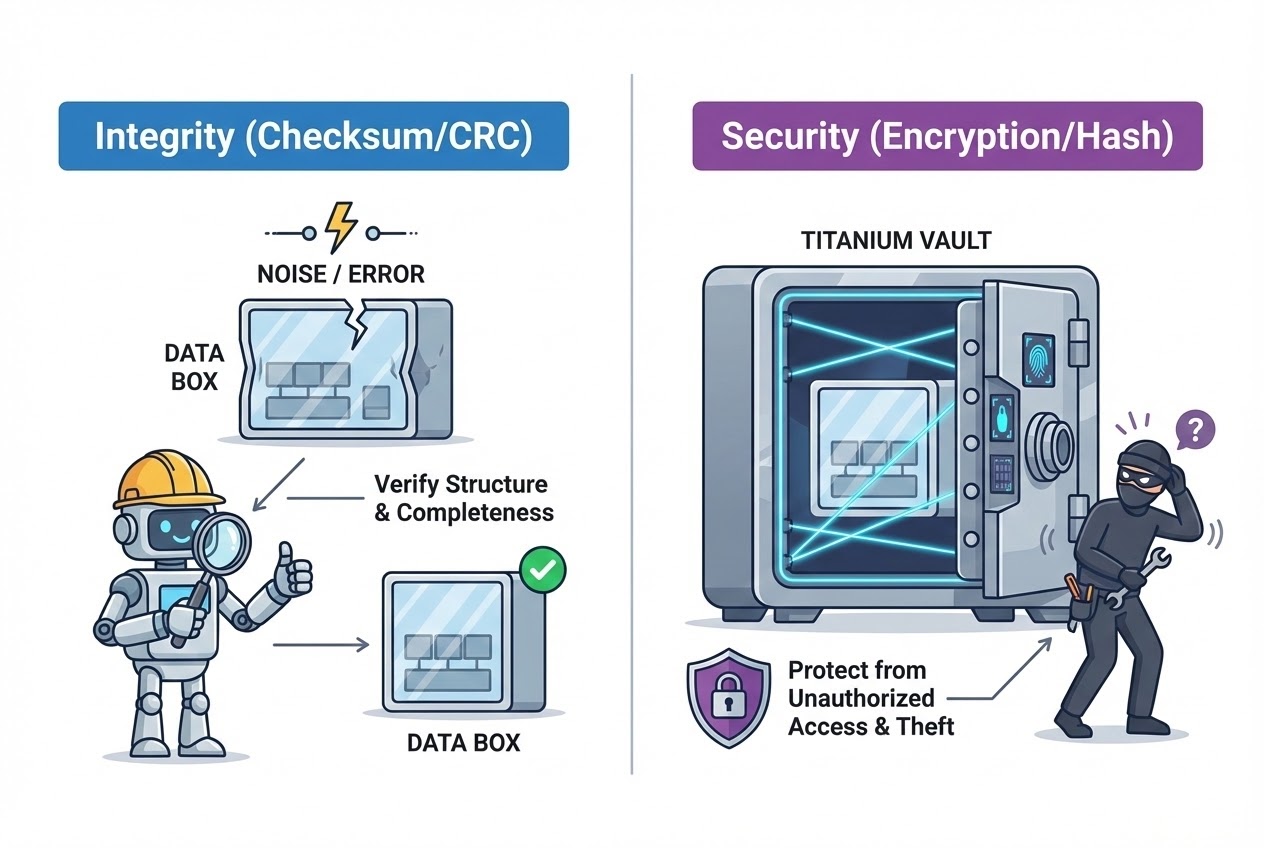
Before we ruthlessly dive downward penetrating the absolute bare-metal C code level, we must forcefully surgically divide our computational brains, entirely separating and isolating the exact “Objective” governing the operation we are executing. The elite grimoire covering advanced embedded systems explicitly categorizes and isolates two wildly dangerous terminologies that rookies constantly lazily conflate:
- Integrity (Total Data Perfection): This architectural position functions identically to a ruthless border-control gatekeeper absolutely guaranteeing that a payload injected crossing the network, or a binary block slammed onto a storage disk, lands “100% physically perfect and complete.” It mathematically verifies the payload suffered absolutely zero physical injuries, noise-corruption, or lacerations during its turbulent transit. Should the scanning matrix detect even a single corrupted, filthy bit, the overarching system immediately triggers alarms, ruthlessly demanding the transmitter execute an aggressive (Retry) payload launch, or it indiscriminately deletes the toxic data chunk. Your absolute primary frontline arsenal executing this directive consists entirely of Checksums and CRCs!
- Security (Impenetrable Defensive Armor): This operational profile defines the elite encrypted special forces! Its singular terrifying mandate physically mathematically guarantees that heavily classified intelligence blocks absolutely resist penetration or covert malicious mutation modifications executed secretly by unauthorized hostiles or terrifying dark-web threat actors (regardless if the mutation registers as intentional sabotage or incidental). This entire spectrum explicitly covers heavy-ordnance Cryptographic Encryption tactics (Rendering intercepted data totally illegible). The toolsets deployed commanding this sector involve advanced Cryptographic Hashes enforcing strict Authentication paradigms.
Cracking Open the Arsenal: Error Detection Mechanisms Classified:
- The Primitive Abacus: Simple Checksums:
The absolute most rudimentary, computationally cheap methodology executing this task requires forcefully grabbing an entire brutal array of data bytes occupying a buffer and blindly, aggressively “Adding” them sequentially together. It intentionally, violently ignores the physical architecture limits, gleefully allowing the maximum value to (Overflow), carelessly tossing the excess carrying bits entirely into the void. For instance: when iterating 10 data blocks, the system calculates a crude aggregate (Sum). Subsequently, we covertly append this finalized aggregated integer physically shackling it directly onto the outgoing packet. Upon impacting the receiving motherboard, the target recalculates an identical summation across the intercepted data block, matching the results. A perfect match signals an operational green light!
- The Fatal Blindspot: This primitive tractor-logic inherits a catastrophic, potentially lethal vulnerability! It operates completely blind, utterly mathematically incapable of detecting anomalies if specific data bytes suffer a “Horizontal Swap (Swapped Words—e.g., Block A illegally trading positions with Block B),” because fundamentally, swapped integers generate the exact identical primitive math sum! Furthermore, if an infiltrating scout silently injects null-bytes (Bits equating to 0), the total Checksum stubbornly refuses shifting. Most terrifyingly, if massive corruption fluctuations coincidentally mathematically cancel each other out returning to equilibrium, the pathetic algorithm registers zero Error! Extremely dangerous!
- CRC (Cyclic Redundancy Checks):
Acknowledging the pathetic weakness paralyzing primitive Checksums, elite architectural engineers forged the heavily armored CRC framework neutralizing those specific vulnerabilities. The underlying brutal mathematics demands scanning the entire data payload operating as a single, incredibly massive binary number matrix, and subsequently dragging it through a violent “Generator Polynomial Division” sequence. This highly aggressive background calculus was specifically architected hunting attempting to detect and isolate “Transmission Errors,” specifically vicious signal spikes inciting violent cascading clustered failures (Classified as Bursty Errors) with incredible, terrifying mathematical precision.
- The Iron Constraint: Exchanging performance capturing extreme precision, executing raw CRC polynomial division mathematically tortures the CPU, violently draining battery reserves drastically faster than primitive addition. However, optimizing C-architecture logic, elite engineers bypass this delay forcefully pre-computing massive (Lookup Tables) aggressively burning them into localized ROM sections, violently accelerating calculation processing velocity into the microsecond domain!
- The Hard Truth: Unveiling the Painful Reality—Neither CRC nor Checksum Blocks Hackers! ❌ Global security intelligence repositories urgently warn, triply-underlining the absolute explicit fact: Deploying Checksums or CRCs “Do Not Provide Zero Hack Prevention (Absolutely Not Preventions Against Hacking)!” These algorithms exclusively possess the IQ required filtering power-surges and static decay. They mathematically lack all capability recognizing or deflecting “Intentional Malicious Data Modification” or sophisticated Man-in-the-Middle hijacking vectors! Because these archaic algorithms execute globally recognized public standard mathematical protocols extensively documented on Wikipedia, a bored script-kiddie can effortlessly intercept, alter a financial value directly inside your packet, and simply command their own board effortlessly calculating stamping a brand new valid CRC matching their forged data perfectly (Trivial to spoof). Your gullible system will ingest the hostile payload entirely unchallenged! If your tactical objective demands defending blocking aggressive hacker interceptions, you are absolutely mandated legally required executing Cryptographic Hashes (Explicitly SHA-256) or deploying heavy Digital Signature frameworks functioning utilizing private asymmetrical key infrastructure entirely preventing mathematical prediction reversing!
Firing Live Code Rounds: Pulverizing Mathematics Calculating Integrity in Bare-Metal
Initiate extreme logic breakdown analyzing the aggressive C coding tactical approach engaging a crude Simple Checksum alongside spinning the heavy mechanical gears executing a pure-software CRC-8 calculating verification array (Integrity Check). This code is absolutely structurally engineered explicitly matching Clean Code principles, instantly ready hot-dropping deploying onto localized Embedded silicon.
#include <stdint.h>
#include <stddef.h>
#include <stdbool.h>
/*
* Mission Objective 1: Simple Checksum (Blindingly Fast, Pathetically Insecure)
* Violently summate every data byte crushing them together (Intentionally executing allowing natural 8-Bit integer Overflow capacities deleting excess).
*/
uint8_t calculate_simple_checksum(const uint8_t *data, size_t length) {
uint8_t sum = 0;
/* Shield against illegal null pointer execution strikes */
if (data == NULL) return 0;
for (size_t i = 0; i < length; i++) {
sum += data[i]; // Although absolute value violently exceeds 255, the compiler aggressively truncates keeping only the residual 8-bit garbage. This represents optimal conditions.
}
return sum;
}
/*
* Mission Objective 2: CRC-8 (Burn CPU Cycles Slower, Guarantee Maximum Trust, Immune to Byte-Swaps)
* This brutal logic loops executing standard Polynomial Division (Utilizing targeting standard Polynomial 0x07).
* (Intentionally refusing Lookup Table acceleration logic prioritizing conserving extreme low-memory RAM boundaries).
*/
uint8_t calculate_crc8(const uint8_t *data, size_t length) {
uint8_t crc = 0x00; /* Drop anchor initiating absolute Zero baseline */
const uint8_t polynomial = 0x07; /* Secret divisor mathematical equation (Hot-swappable strictly matching industrial standards) */
if (data == NULL) return 0;
for (size_t i = 0; i < length; i++) {
crc ^= data[i]; /* Seize current byte forcefully slamming a XOR logical strike injecting charge driving into the primitive CRC register */
/* Drop transmission into low-gear looping 8 cycles calculating pulverizing mathematical load executing 8-bit Polynomial division */
for (uint8_t bit = 0; bit < 8; bit++) {
if (crc & 0x80) { /* Execute mask actively checking highest extreme-left bit (MSB) searching 1 */
/* If highest bit flags 1, execute aggressive Left-Shift brutally slamming XOR polynomial overwrite */
crc = (crc << 1) ^ polynomial;
} else {
/* Exclusively otherwise, blindly push Left-Shift dropping the bit aggressively into the void */
crc = (crc << 1);
}
}
}
return crc;
}
/* Security Checkpoint: Example deployment function executing inbound Integrity verification (CRITICAL REMINDER! Not Security Authentication) */
bool verify_packet_integrity(const uint8_t *packet, size_t length, uint8_t received_crc) {
/* Engage Pointer interception shield crushing garbage logic drops */
if (packet == NULL || length == 0) return false;
/* Command processor calculating raw CRC directly ripping generated inbound packet block, forcefully colliding results comparing targeting the trailing CRC ticket */
uint8_t calculated = calculate_crc8(packet, length);
return (calculated == received_crc); /* Return True surviving integrity metrics, False confirming toxic data corruption */
}
Proximity Defcons: Cease Arrogant Fire-Play! Survival Checklist
Aggressively upgrading your hardware logic architecture achieving impenetrable industrial safety ratings necessitates strictly honoring these elite constructor Best Practices governing Error Detection management:
- Strict Prohibition Grabbing Incorrect Weaponry: Permanently burn into your neural architecture understanding the primary prime directive deploying Checksums guarantees exclusively: “Scanning triggering klaxons detecting structural physical signal decay (Detect Error)” entirely ignoring Identity verification (Zero Authentication). If your system architecture currently ferries corporate classified GPS configurations or transmits firing-commands operating autonomous hunter-drones, immediately abandon employing pathetic CRC logic instantly! You must immediately surrender deploying utilizing the absolute standardized MAC (Message Authentication Code) protocols demanding paired secretive Cryptographic Keys actively blocking hostile enemy decryption!
- Establish Immediate Nonvolatile Memory Physical Health Inspections: Functioning deep inside Embedded architectures, legacy computing memory silicon mirroring ROM or EEPROM inherently suffers debilitating physical diseases, damaged memory cell degradation, decaying solder joints, or drifting ground matrices accelerating throughout absolute time. The absolute supreme engineering survival tactic (Ultimate Best Practice) dictates heavily executing pre-computation calculating sweeping ROM memory Checksum analysis immediately initialized inside the factory burn-facility (Build Stage). Maintain secretly hoarding that pristine calculated Checksum record physically implanted (Secretly embedded utilizing the absolute maximum furthest extreme physical Memory Address bounded inside the ROM block). At absolute any millisecond the physical system applies power triggering an operational Boot sequence, the absolute first priority dictates the runtime software fiercely sprint launching executing calculating an aggressive full-block massive Checksum recalculation, mathematically colliding comparing directly verifying hitting the saved factory original value. This actively mathematically proves your massive primary Firmware programming maintains absolute physical structural integrity shielding avoiding horrific rogue malfunctions triggering robotic decapitations. (Establishes Runtime Firmware Validity).
- Global Annihilation Triggered Orchestrating Integer Overflow Inside Titan Scale Projects: If your operational manifest mandates executing massive repetitive Checksum data block additions aggregating vast monstrous geometries (For example: Scanning total total memory Firmware Image file clusters) and you pathetically carelessly explicitly deploy heavily restricted micro-sized datatypes like 16-Bit Word containers holding total mathematical aggregates, you absolutely must maintain hyper-aware vigilance actively preventing your mathematical total violently accelerating shattering boundaries triggering a horrific Integer Wraparound anomaly flipping cycling backward initializing identically starting zero accidentally inside complex calculus (Which completely instantly annihilates total calculation lookup tables entirely). The absolute mandatory defense parameter strictly commands: Maintain hyper-aggressive surveillance validating C-Language logic Type-Casting formats aggressively calculating declaring massively thick heavily armored variable containers (Execute declaring
uint32_tor ultra-heavyuint64_tdata arrays) structurally stabilizing anticipating extreme massive mathematical impacts maintaining absolute structural integrity perpetually!
Conclusion
Carving out the ultimate absolute final logic line unconditionally: The deployed technical algorithms executing Checksums alongside advanced CRC polynomials are incredibly phenomenally mathematically structured superheroes developed brilliantly executing strictly successfully guarding protecting the perimeter locking “Bit-Level Data Perfection/Integrity” deflecting disastrous localized environmental physical threats, erratic native electrical copper cable line-noise, or completely physically destroyed severed serial bus cables! They absolutely do not function operating identically replicating heavily armored Hacker defense logic-grids (Zero Security functionality). Aggressively deploying correctly identifying accurately selecting matching intelligent algorithms successfully resolving combating neutralizing explicitly your exactly designated “Threat Vectors” visually determines definitively extracting acknowledging distinguishing identifying recognizing the absolute pinnacle brilliance recognizing an absolute Grandmaster Embedded System Architect!
If the heavy-lead smoke operators deeply appreciate aggressive high-velocity articles absolutely shredding dissecting ripping the core logic combining brutal Hardware Integration crossing dangerous Security principles mirroring this specific analysis, or any operational team members hold agonizing scars recalling combat-trauma compiling a singular failed CRC library preventing generating a hundred-thousand client motherboards refusing completely booting up—transmit exact coordinates distributing those horrific stories immediately! Dump aggressive hardcore code snippets targeting our specialized community logic grid stationed explicitly at www.123microcontroller.com! As long as the digital clock signal oscillates, our hardcore code must march forward endlessly! Grip your heavy mice tightly; I will intercept you operating deploying the next aggressive coding arena! Stay heavily optimized! Happy Firmware Hacker Logic Coding, everyone!