Error Correction (Hamming Codes): The Ultimate Data Recovery Wizardry at the Edge of Integrity!

Introduction: When Mere “Detection” Fails the Hardware Battlefield
Greetings, elite engineers and bare-metal developers of the www.123microcontroller.com vanguard! The dark-eyed engineer has returned to the terminal. Today, we are drastically leveling up our defensive capabilities within the brutal realm of bit-level data protection.
In our previous operation, we dissected Checksums and CRCs, deploying them as vigilant “Guardians” tasked exclusively with identifying whether structural payload data has suffered fatal corruption (Error Detection). However, a catastrophic global-scale problem immediately emerges: If the perimeter guard screams that the packet is destroyed, the central architecture must aggressively command the transmitting sensor to “resend the exact same payload (Retry).” In mission-critical Real-time systems or deep-space satellite orbital communications, violently demanding a re-transmission can instantly annihilate the entire timeline or prove physically impossible due to massive latency! Today, we absolutely must transcend primitive mathematics and deploy something vastly superior: “Error Correction.” Specifically, we are unleashing the eternal champion of this domain, the legendary Hamming Codes. Elite architectural documentation brilliantly explains this mechanism, strictly decoupling Security boundaries from pure Integrity frameworks. Let us dissect the anatomy of this wizardry!
Core Theory Autopsy: Integrity Is Not Security, and the Evolution of Autonomous Healing
Before executing a single line of logic, we must forcefully recalibrate our architectural definitions. These two terminologies frequently suffer catastrophic conflation by rookies, but the master texts explicitly separate them:
- Integrity (Pristine Bit-Level Perfection): This explicitly guarantees that the data remains physically “correct,” structurally uncorrupted throughout storage endurance or transit volatility. If the payload sustains battle damage, the system must not only detect the anomaly but possess the elite capability to “autonomously repair and correct it (Corrected),” or in the absolute worst-case scenario, discard it.
- Security (Cyber-Warfare Shielding): This explicitly prevents unauthorized hostile entities or interceptors from accessing, harvesting, or comprehending our classified data structure. This domain is strictly governed by Cryptographic Encryption methodologies.
Plunging strictly into the Integrity quadrant, we observe the brutal evolution of error management:
- From Passive Detection to Aggressive Correction: Executing primitive Error Detection (such as stapling a single Parity bit to the tail of a payload) violently minimizes bandwidth overhead. However, it operates entirely blind! It cannot mathematically calculate which exact bit suffered the lethal strike. Conversely, Error Correction matrices intentionally drastically inflate the total physical volume of the transmitted payload structure, willingly sacrificing transmission speed to forge the miraculous, magical ability to literally calculate and reconstruct shattered data! The absolute most pathetic, bandwidth-burning method involves “Three-cycle Repetition” (transmitting the identical payload three times). It works, but violently annihilates 3x the bandwidth. (A two-cycle repetition is utterly useless; if two packets differ, the CPU remains paralyzed, unable to mathematically deduce which one is truth!).
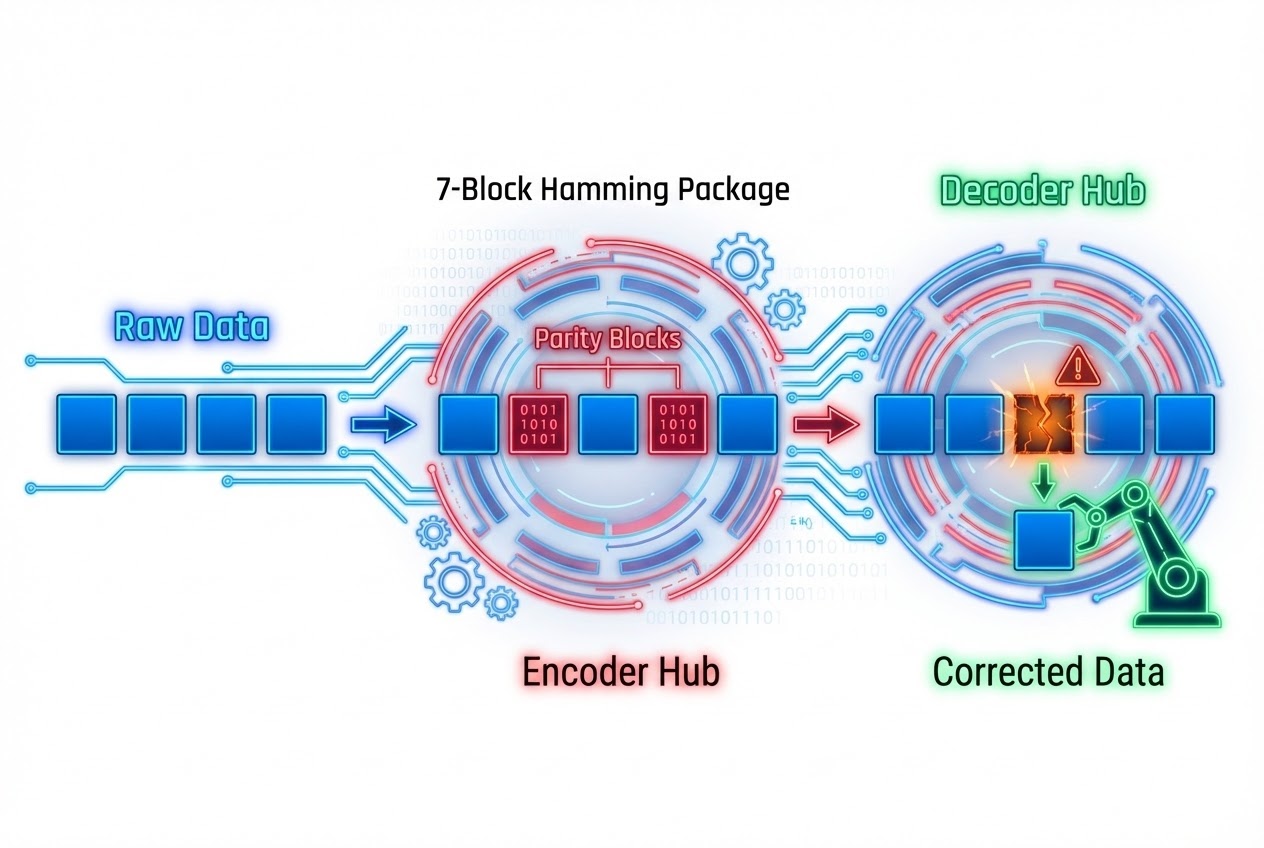
- The Wizardry of Hamming Codes (7,4): To obliterate the horrendous inefficiency haunting brute-force repetition, visionary engineers mathematically forged the legendary Hamming (7,4) code. It functions by violently interweaving 4 raw Data bits together with 3 highly calculated Parity/Check bits, fusing them into a heavy, 7-bit armored package. The absolute god-tier advantage of this architecture? It possesses the infallible mathematical power to detect and completely seamlessly reconstruct any “Single-Bit Error” autonomously!
-
The Calculus of Precision Targeting (Syndrome Calculation): Visualize a 7-bit payload lined up in absolute formation (occupying Positions 1 through 7). The elite grimoire dictates that we surgically embed our pure Data bits holding positions 3, 5, 6, and 7, while stationing our calculated Parity guards strictly at positions 1, 2, and 4. The absolute integer value of each Parity guard is derived by aggregating highly specific overlapping combinations of Data bits, performing a brute-force modulo 2 division—which translates precisely inside C architecture as a primitive Bitwise XOR execution! When the intercepting motherboard ingests this structured 7-bit package, it aggressively calculates three distinct verification equations yielding secret keys $c_1, c_2, c_4$ (Officially classified as the Syndrome).
The absolute universe-bending brilliance of this design dictates that if you concatenate $c_4, c_2, c_1$ together forging a pure Binary sequence, the resulting decimal integer geometrically pinpoints the exact physical “Index (Coordinate)” of the compromised bit with terrifying sniper precision! For instance, if the mathematical assembly yields 110 (Decimal 6), the architecture explicitly confirms that physical bit 6 suffered a catastrophic noise strike. The CPU simply executes a surgical Flip on that exact bit, instantly fully restoring the entire payload to pristine structural perfection without ever begging the transmitter for a retry! Constructing structured parity bits physically chained alongside data bits defines a “Systematic Code,” a design guaranteeing logic chips execute decoding cycles at blazing-fast microsecond speeds!
Firing Live Code Rounds: Microsecond Data Reconstruction Architecture
Initiate extreme breakdown analyzing standard C logic designed extracting and autonomously repairing corrupted intercepts utilizing the Hamming Code (7,4) format, written adhering strictly to Bare-Metal Clean Code principles. This protocol violently ingests a 7-bit package (stowed efficiently inside a standard 1-byte container), processes the combat damage identifying the shattered bit, and executes an instant flawless repair!
#include <stdint.h>
#include <stdio.h>
/* Monstrous Macro engineered forcibly ripping target bit values occupying specifically requested coordinates (Mathematically anchored initiating Position 1 exclusively) */
#define GET_BIT(word, pos) (((word) >> ((pos) - 1)) & 1U)
/*
* Rescue Protocol: Verify and execute autonomous Single-Bit Error reconstruction algorithms.
* Ingests a pre-encoded Hamming (7,4) payload block structured holding physical bits occupying coordinates 1-7.
*/
uint8_t correct_hamming74(uint8_t received_word) {
uint8_t c1, c2, c4;
uint8_t error_index;
/*
* Initiate Syndrome calculative extraction forcing logic gates executing XOR operations (Executing pure modulo 2 addition).
* Parity Gate c1 actively monitors physical stability securing bit coordinates 1, 3, 5, 7.
*/
c1 = GET_BIT(received_word, 1) ^ GET_BIT(received_word, 3) ^
GET_BIT(received_word, 5) ^ GET_BIT(received_word, 7);
/* Parity Gate c2 commands perimeter securing bit coordinates 2, 3, 6, 7. */
c2 = GET_BIT(received_word, 2) ^ GET_BIT(received_word, 3) ^
GET_BIT(received_word, 6) ^ GET_BIT(received_word, 7);
/* Parity Gate c4 locks down securing bit coordinates 4, 5, 6, 7. */
c4 = GET_BIT(received_word, 4) ^ GET_BIT(received_word, 5) ^
GET_BIT(received_word, 6) ^ GET_BIT(received_word, 7);
/* Violently smash Syndrome boolean results compiling a targeted binary sequence hunting the Error Index coordinate (Matrix formula: c4_c2_c1) */
error_index = (c4 << 2) | (c2 << 1) | c1;
/* If the targeted Index registers anything above absolute Zero, trigger alarms! A hostile physical Error hides at that exact coordinate! */
if (error_index != 0) {
printf("⚠️ Intrusion Warning: Single-bit physical corruption detected striking coordinate %u!\n", error_index);
/* Command Auto-Correct protocol aggressively Flipping the shattered bit executing targeted Bitwise XOR */
received_word ^= (1U << (error_index - 1));
printf("✅ System Healed: Structural integrity completely restored.\n");
}
/* Return perfectly cleansed uncorrupted data payload (or the pristine original) resuming primary operations */
return received_word;
}
(Operational Note: This specific data-sheet intentionally emulates the absolute rigid theoretical mathematics governing Syndrome Error Index calculation explicitly designed for heavy educational comprehension. Live production firmware typically utilizes heavily optimized instruction cycles tailored towards the specific internal silicon.)
Proximity Defcons: Cease Arrogant Fire-Play! Enterprise Survival Checklist
Although the legendary Hamming Code unleashes god-like reconstruction capabilities, incorrectly deploying this architecture in the wrong theater of war practically guarantees catastrophic system annihilation or horrific cyber-breaches! Elite source repositories aggressively deploy the following absolute warnings:
- Force Hardware Acceleration When Available: Elite documentation explicitly commands that if you deploy heavy communication arrays or specific microcontrollers, they inherently possess native, hardwired “Specialised ECC (Error Correcting Code) Hardware” fused directly into the silicon substrate! Engaging hardware-accelerated processing operates infinitely faster, exponentially safer, and significantly more reliably than frantically scribbling manual C instruction code desperately attempting software verification!
- The Kryptonite Limits of the Hamming Code: The entire Hamming Code lineage architecture, regardless of how massively long you stretch the array footprint (for instance, the heavy 255-bit Hamming structure transporting 247 payload bits), is structurally permanently locked, only possessing the power to “Fix exactly one single catastrophic error! (Single-bit problem).” Consequently, when the system slams repeatedly into “Burst Errors” (Massive electromagnetic waves shattering multiple sequential data blocks simultaneously), the entire Hamming framework dissolves, becoming just as uselessly paralyzed as a primitive Checksum! If your operational project launches deep into high-interference zones, you must immediately abandon Hamming and deploy heavy industrial algorithms targeting Reed-Solomon architecture, strictly accepting the horrific mathematical CPU penalty it commands!
- Kerckhoff’s Principle & The Security Apocalypse: Never suffer the absolute fatal delusion assuming that aggressively chopping up a payload and heavily scattering disorganized Parity bits inside the transport block (Unusual Encodings) mathematically equates to deploying a secure encrypted defense (Encryption)! These brilliant architectural tools operate exclusively preserving pure physical Bit Integrity! If a highly trained tactical hacker intercepts your radio transmission mid-flight, they effortlessly deploy standard open-source mathematical algorithms reversing your encoding sequence, immediately reading your classified payload with zero effort! Absolute impenetrable Security (Cryptography) mandates mechanisms structured guaranteeing “Reverse-calculation utilizing algorithm mathematics alone remains totally impossible! (You must definitively deploy and physically hide a private Cryptographic Key!).”
Conclusion
Engineering Error Correction matrices synchronized with heavy algorithmic logic mirroring Hamming Codes defines an incredibly brilliant classical architectural technique! It showcases the beautiful art of fusing raw data bits together with aggressive advanced mathematics constructing heavily fortified protocols possessing massive Fault Tolerance. This architecture unlocks the absolute terrifying potential allowing Bare-Metal hardware to execute deep communications and instantly cast resurrection magic, healing totally shattered data blocks autonomously without ever enduring the latency penalty begging the source to re-transmit the payload!
If the heavy-lead smoke operators deeply appreciate aggressive high-velocity articles absolutely shredding dissecting advanced Hamming Code applications or heavily analyzing tossing heavy Reed-Solomon logic into deep-space RF communication frameworks, immediately drop your coordinates and launch aggressive project threads inside our specialized community logic grid stationed explicitly at www.123microcontroller.com! As long as the digital clock signal oscillates, our hardcore code must march forward endlessly! Grip your heavy mice tightly; I will intercept you operating deploying the next aggressive coding arena! Stay heavily optimized! Happy Bare-Metal Coding, everyone!