Endianness (Big-Endian vs Little-Endian): The Hardware Byte Array Puzzle and the Art of Communication

Introduction: The Invisible Language Barrier Dividing Silicon Architectures
Greetings, elite systems engineers and bare-metal combatants of the www.123microcontroller.com network! The dark-eyed engineer has logged back into the terminal. Today, we confront an insidious, invisible “language barrier” isolating foreign hardware architectures—an absolute theoretical headache that has fractured the computer science community for decades: the infamous domain of Endianness.
Do you comprehend the obscure historical origins dictating the bizarre nomenclature ‘Big-Endian’ and ‘Little-Endian’? The terminology historically originates violently ripped from Jonathan Swift’s 1726 political satire Gulliver’s Travels, specifically documenting an absurdly catastrophic civil war tearing two societies apart simply because they vehemently disagreed on protocol: “When cracking open a boiled egg, should one fracture the broad side (the Big end) or the pointed side (the Little end) first?!”
Operating deep within the intense trenches of Low-Level Programming, a silicon manufacturer’s unilateral architectural decision dictating exactly which targeted byte of a massive variable gets violently shoved into localized memory first translates essentially as a purely philosophical engineering stance. Statistically, neither execution logic maintains a 100% universal superiority. However, this philosophical discrepancy instantly detonates, synthesizing an absolute “Apocalyptic Execution Nightmare,” the exact millisecond two distinct hardware microchips—worshipping fundamentally opposing “religions”—are forcibly coupled and commanded to seamlessly exchange digital payloads! Today, we aggressively decrypt complex elite architectural literature, deciphering precisely how seasoned veterans manage this catastrophic phenomenon directly relating to the brutal mechanics of Hardware Interaction!
Architectural Core Theory: The Bipolar Logic Governing Hardware Byte Order
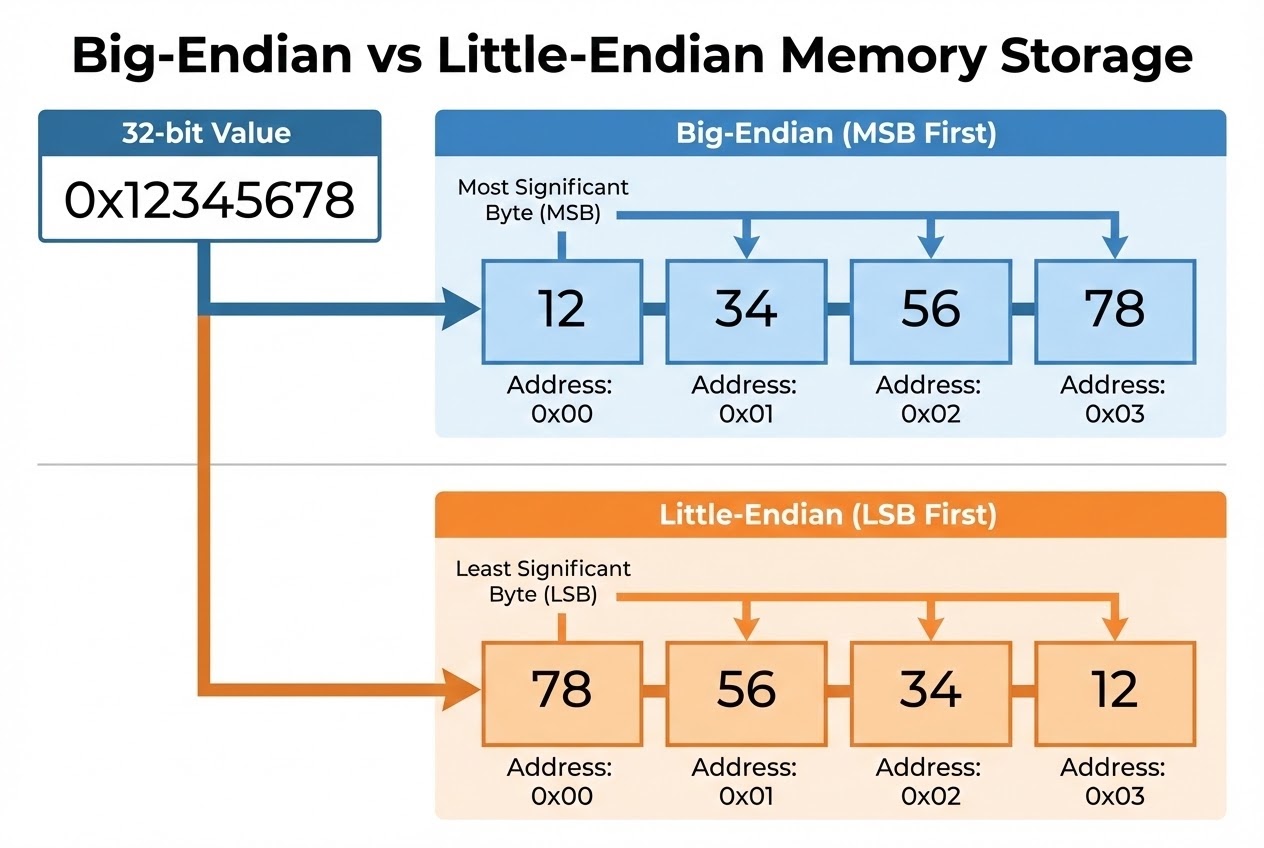
Zooming outward analyzing the massive operational framework comprising bare-metal hardware integration, Endianness fundamentally defines the absolute “Sequential arrangement protocol of Bytes.” This governs execution protocols precisely when we demand the semiconductor aggressively store or violently transmit a massive data variable exceeding the limits of a singular 1-byte boundary (For instance, forcibly packing a 32-bit int or uint32_t measuring 4 distinct bytes) either downward heavily into a physical memory grid or screaming across an ethernet network matrix. High-level architectural data-logs explicitly categorize this structural civil war dividing execution platforms primarily into two dominant combatants:
- 1. Big-Endian (The Most Significant Strikes First): Adhering strictly to this doctrine, the singular byte calculating possessing the absolute highest mathematical value/significance (Most Significant Byte - MSB) is violently seized and stored targeting explicitly the absolute lowest theoretical Memory Address (Positioned fully to the Left). Architecturally, this sequential alignment perfectly mirrors standard human optical neurological parsing, identical to how biological entities read numerical mathematics normally. Heavyweight silicon empires historically deploying this execution logic comprise legacy Motorola 68K processors, monolithic SPARC data-center servers, and critically—it absolutely dominates the entire global internet—mandated as the supreme universal protocol dictating physical Network Data Transmission (The Network Byte Order) governing the legendary TCP/IP and UDP frameworks.
- 2. Little-Endian (The Underdog Infiltrates First): Executing the inverted paradox, this hardware architecture intercepts the byte retaining the absolute lowest mathematical value (Least Significant Byte - LSB) and explicitly jams it packing it firmly directly into the lowest localized Memory Address array first. The critical underlying engineering tactical advantage resides in hardware logic acceleration: The processing silicon maintains the aggressive physical capacity to effortlessly slice and ruthlessly discard higher-tier surplus bytes executing incredibly rapid variable “Type Casting” reductions (E.g., forcefully crushing a 32-bit variable truncating down to a 16-bit register) flawlessly executing instantly. Mega-architectures commanding astronomical market density including the Intel/AMD (x86) legacy desktop framework running your workstation, and the omnipresent ARM cores powering global smartphone grids predominantly align heavily adopting this configuration.
Why Does This Discrepancy Paralyze Hardware Interaction Architectures? Operating isolated, completely quarantined executing firmware inside a single, solitary microcontroller environment, Endianness possesses an absolute zero-threat rating; it essentially does not exist. Engineers operate utterly oblivious caring absolutely nothing regarding how the underlying silicon physically sequences data. That blissful ignorance instantly evaporates, mutating establishing a catastrophic Critical Logic Issue specifically during these treacherous operations:
- Executing Cross-Platform Network/Bus Communication: Supposing a dominant x86 processor (A Little-Endian native) violently blasts a sprawling 32-bit numerical identifier across a serial bus penetrating a hostile SPARC target node (A Big-Endian native), the receiving board’s primitive silicon mind will blindly parse the byte array fundamentally backward (Reversed). This guarantees aggressive logic destruction, converting precision data mathematically into highly toxic garbage telemetry (Garbage Data).
- Binary File Save/Load Corruption Loops: If an application silently writes and dumps a compressed binary block geometry downward onto a physical SSD originating from one architecture format, and an unknowing technician subsequently violently rips that geometry loading it launching on an inverted Endian architecture, the numerical configurations and visual render data will similarly instantly catastrophically implode.
Firing Live Code Rounds: Weaponizing Pointer Casting to Expose Endianness
Initiate analysis breaking down a brutal, primitive C firmware operation engineered exclusively to “Secretly Interrogate” and expose precisely whether your underlying, executing microcontroller host’s memory matrix pledges allegiance to the Big-Endian or Little-Endian architecture. This execution relies heavily on aggressive, forced ‘Pointer Casting’ logic mechanics (An absolute legendary manipulation maneuver universally wielded by elite Embedded operatives).
#include <stdio.h>
#include <stdint.h>
/* Execute tactical interrogation function calculating the native Endianness execution state belonging to the actively hosting Hardware. */
void check_machine_endianness(void) {
/*
* Synthesize and forge a massive 32-bit (4 Byte) variable block injecting the explicit hex value 0x12345678.
* Geometrically, the MSB (Highest value segment) equals 0x12, and the LSB (Lowest value segment) equals 0x78.
*/
uint32_t num = 0x12345678;
/*
* Instrument a targeted 'char' Pointer (Physically restricting vision scanning exactly 1 Byte boundaries) snapping violently targeting the localized base Address housing variable 'num'.
* This brutal architectural hack permits us optical clearance slicing precisely into the memory block evaluating byte-by-byte (Defined in hacker-space as 'Type Punning').
*/
uint8_t *byte_ptr = (uint8_t *)#
/* Execute lethal conditional check scanning the absolute first byte buried at the lowest memory address index. */
if (byte_ptr[0] == 0x78) {
printf("Hardware telemetry confirms: Little-Endian (LSB is stored physically first).\n");
} else if (byte_ptr[0] == 0x12) {
printf("Hardware telemetry confirms: Big-Endian (MSB is stored physically first).\n");
} else {
printf("Hardware telemetry catastrophic failure: Mixed/Unknown Endian Detected (Alien Architecture!).\n");
}
/* Deploy iteration loop forcibly extracting and broadcasting the consecutive sequential memory layout verifying the physics graphically byte-by-byte. */
for (int i = 0; i < sizeof(num); i++) {
printf("Memory Matrix Address Offset %d: internally contains 0x%02X\n", i, byte_ptr[i]);
}
}
int main(void) {
/* Engage Interrogation sequence. */
check_machine_endianness();
return 0; // Terminate tracking sequence with optimal integrity.
}
Defensive Shield Configuration: Eradicating Garbage Output from Endian Collisions
To permanently obliterate the threat vectors allowing terrifying bugs cascading destroying your systems when migrating logic payloads traversing spanning independent hardware boundaries, universal Secure Coding standards and seasoned architecture combat veterans globally mandate these ironclad survival procedures:
- Worship the Byte-Swapping Macros Invading Network Corridors: Standard Internet communication protocols (TCP/IP) deploy an absolute, irrevocable iron-fisted mandate demanding transported network payload packets execute physically formatted employing strict Big-Endian alignments (Denoted as ‘Network Byte Order’). Consequently, if our high-velocity hardware operates designated Little-Endian, we carry the absolute burden forcibly, violently swapping reversing every byte alignment executing outgoing transmissions. Fortunately, standard C-libraries dispatch armored function reinforcements exactly like
htons()(Host to Network Short),htonl()(Long variant), alongside reverse-flow interceptorsntohs(), andntohl(). Always execute these functions flawlessly swapping sequencing formats averting disaster before firing payloads traversing the Serial Bus or Ethernet Sockets! - Navigate Cautiously Disabling Unstable Union Hacks Shredding Bytes: Countless inexperienced developers favor dangerous simplistic structural paths, constantly illegitimately abusing
unionconstructs attempting violently shredding dissecting a robust 32-bit integer arraying it into 4 fragmented 8-bit slices. Although lenient, cowardly compilers routinely tolerate validating this compilation, referencing explicit ironclad C Standard regulations, this aggressive trickery officially ranks designated completely as “Unspecified Behavior.” Furthermore, the resulting fragmented slices mathematically mutate changing positions randomly directly slaving to the underlying microchip’s localized Endianness. If your mission dictates isolating extracting exact specific bytes without failure, abandon Unions! Default pivoting worshiping Bitwise Operators (Specifically leveraging Right Shift>>coupled deploying Mask AND&). Bitwise extraction guarantees an absolute indestructible mathematical return maintaining 100% Endian indifference (Hardware Independent Operations)! - The Omega Directive: Absolutely Forbid Throwing Raw Structs System-to-System: The reckless, pathetic maneuver launching solid raw
structmemory blocks blindly flying jumping systems relying on primitive pointers statistically causes massive software homicides. Beyond directly colliding battling alternating, reversed Endianness logic arrays scrambling your data, you concurrently trigger devastating secondary explosions battling ‘Memory Alignment’ conflicts and hidden ‘Padding’ booby-traps (Invisible empty memory gaps the deceptive compiler covertly injected inflating your struct layout without authorization). Should operational missions require dropping data penetrating foreign SPI tracks, I2C matrices, or writing binary save configurations, unconditionally execute rigorous Serialization protocols! (Mathematically unraveling, defining, parsing, and packing payload bytes sequentially executing adhering specifically strictly referencing a pre-agreed network communication geometric pattern). This guarantees peak defensive integrity and bulletproof software Portability universally ensuring survival! - Extract Dominance Deploying Emerging C23 Standard Features (If Compiler Verified): Surveying the absolutely newest cutting-edge framework draft defining Modern C (The C23 Release candidate), architectural overhauls forcefully inject inserting an updated header module
<stdbit.h>, actively heavily loaded dispensing holy architectural logic Macros including__STDC_ENDIAN_LITTLE__alongside__STDC_ENDIAN_NATIVE__. This arsenal miraculously empowers our architecture deploying#ifconditional checks scanning calculating targeted Compiler-level Endian configurations entirely resolving pre-computation dynamically during Compile-Time (Logically executing prior dropping silicon flash burns), making life defending hardware vectors immensely easier for our engineering divisions!
Conclusion
Aggregating the final logic conclusions, the structural anomaly categorizing Endianness accurately mimics behavioral differences observing human global linguistics: Specific diverse international demographics prefer visually consuming reading characters moving left to right, whereas opposing civilizations adamantly enforce vertical or right-to-left optical consumption physics. Operating purely in vacuum isolation, running your code hermetically sealed inside an air-gapped single-chip silicon vault, this anomaly presents zero tactical threat profiles. However, immediately breaching the boundary, deciding transmitting executing critical foreign-policy sharing this parameter data aggressively to neighboring systems (Executing complex Hardware Interaction protocols), engineers become irrevocably responsible legally locking entering an airtight logical agreement guaranteeing identical pre-agreed “Grammar, Formatting, and Transmission Syntax.” Neglecting executing establishing this communication baseline guarantees conflicting circuit topologies parsing completely misaligned chaotic telemetry matrices, spawning terrifying, un-debuggable ghost-bugs which embedded engineering divisions routinely hate chasing deep into the night!
If your engineering unit cultivates an aggressive addictive pursuit chasing tearing analyzing bare-metal macro-processing structures executing dominating raw memory payloads, or if your operating squad survived the terrifying trenches diagnosing hunting a phantom communication error terminating discovering hours later a pathetic byte-flipped MSB/LSB Endianness corruption bug—transmit coordinates immediately sharing those combat stories! Dock your vessel connecting engaging fiery code debates localized exactly at target www.123microcontroller.com! Forcefully extracting peak logic manipulating hardware via relentless C-language manipulation establishes an incredibly brutal, adrenaline-pumping engineering philosophy! Ensure code purity; we prepare waiting locking sights targeting the subsequent technical engagement framework. Stay heavily optimized, infantry commanders, and execute your firmware safely!