Encryption (Symmetric vs Asymmetric): The Ultimate Cryptographic Weaponry Defending the Embedded Realm

Introduction: When Integrity Possesses Zero Power Over Confidentiality!
Greetings, elite systems engineers and bare-metal developers actively guarding the www.123microcontroller.com grid! The dark-eyed engineer has logged securely back into the terminal. Today, we are violently tearing into an architectural battlefield parameter critical during this Internet of Things (IoT) era where billions of hardware nodes are connecting to the hostile external internet. We are initiating a complete analytical autopsy concerning the epic saga of Encryption (Cryptographic Data Secrecy).
During our previous operational debriefings, we aggressively dismantled the theories governing Checksums and CRCs. We solidified their identity strictly as formidable tools protecting pure “Bit-Level Data Integrity.” However, elite godfather architects explicitly underline that Physical Integrity “Absolutely Does Not Equal Cybersecurity Protection (Security)!” A mathematically naive CRC algorithm cannot repel a determined hostile hacker for even a microsecond. If our tactical objective demands aggressively concealing highly classified tactical data—such as Wi-Fi WPA credentials or hardware launch keys—we are forced by protocol to abandon Checksum logic. Instead, we must aggressively armor our payloads by engaging heavy mathematical defense matrices classified as Encryption. Today, we will ruthlessly rip apart the operational manuals, analyzing exactly how this phenomenal cryptographic gear system functions. We will dissect the monumental chasm separating the brutal Symmetric arrays from the intricate Asymmetric architectures!
Core Theory Autopsy: The Advanced Architectural Cryptography of Computing
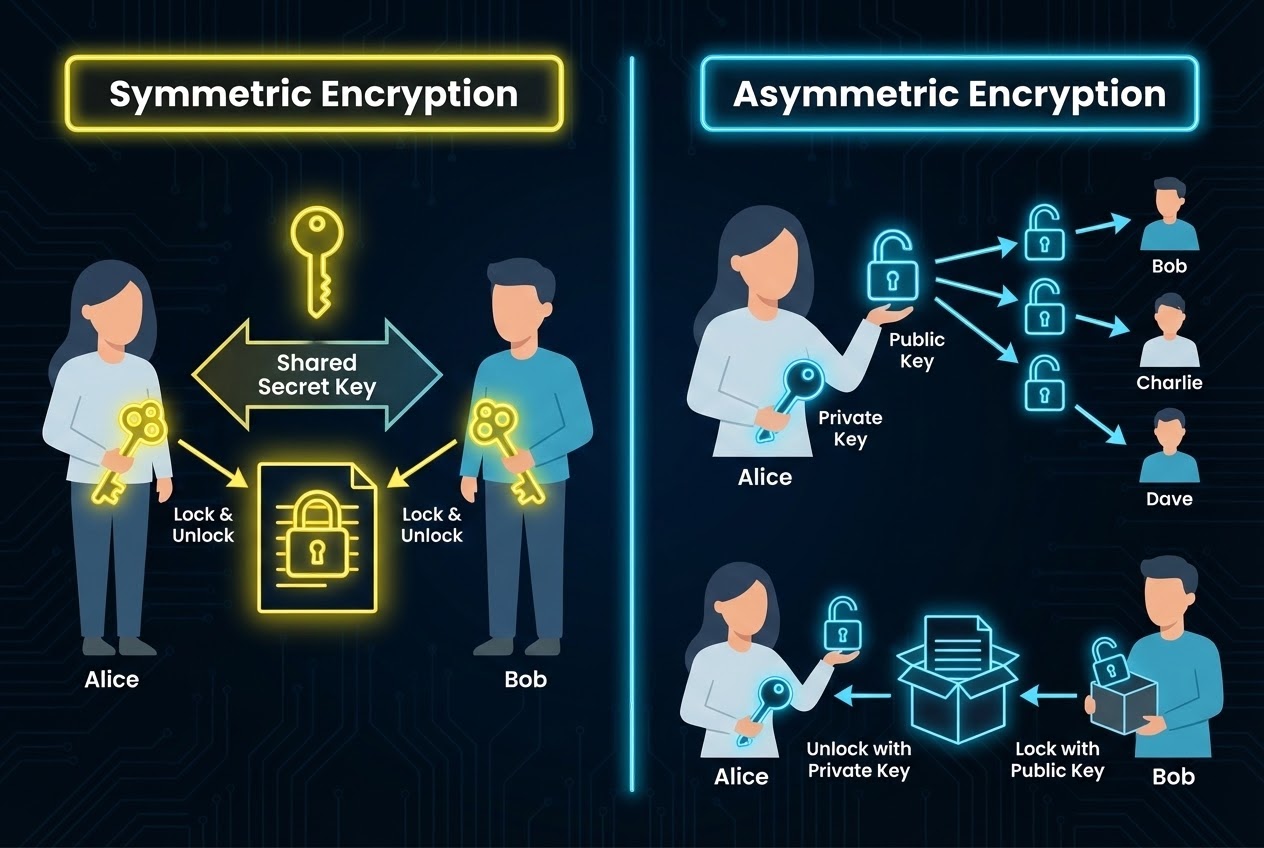
The execution verb defining Encryption involves forcibly dragging highly legible human human-readable plaintext (Plaintext), aggressively dropping them into a violently complex mathematical shredder, combined actively with a specific numerical blueprint officially designated as a “Key.” This fusion process chemically alters the data, spitting out a completely mangled, totally unrecognizable scrambled garbage payload (Ciphertext). The absolute unyielding parameter governing this dynamic asserts: The mathematical scrambling process must fundamentally remain mathematically irreversible without the opposing interceptor possessing the exact matching Key! Engineers divide this advanced mathematical weaponry strictly into two defining pillars:
- 1. Symmetric Encryption (The Single Shared Secret Military Protocol):
- The Tactical Doctrine: This highly aggressive operational structure violently demands utilizing the “Exactly Identical Master Key (Same Key)” actively engaging both the Data Lockdown sequence (Encrypting) alongside triggering the extraction sequence (Decrypting).
- The Visual Metaphor: Imagine taking highly classified intelligence, sealing it inside an indestructible titanium lockbox, and aggressively slamming a physical padlock completely shut. The defending ally can only mechanically spring that titanium lockbox open exclusively IF they already possess a geographically separated but physically identical stamped duplicate “Key” matching your master original perfectly in their pocket!
- The God-Tier Advantage: The underlying raw mathematical algorithm crushes numbers with terrifying, blindingly fast execution speeds (Extremely Fast). Consequently, this architecture dictates the absolute standard protecting massively huge clustered data payloads (Bulk Encryption). Operationally, engineers slice this specific architecture downward targeting Block Ciphers (Specifically utilizing the indestructible AES protocols) or rapid Stream Ciphers.
- The Catastrophic Lethal Vulnerability: The eternal nightmare paradox driving security architects insane is fundamentally answering: “Exactly how do we safely, covertly smuggle this original master key across an insecure, chaotic global network avoiding enemy surveillance?” Because if an elite sniper hacker violently intercepts that symmetric master key during transit, the entire global network architecture instantly and fatally collapses (The Dreaded Key Sharing Problem)!
- 2. Asymmetric Encryption (The Public-Key Cryptographic Alliance):
- The Tactical Doctrine: This architecture was specifically forged entirely to violently obliterate the horrific key smuggling vulnerabilities plaguing primitive symmetric systems! This advanced matrix forces the algorithmic creation forging an inseparable cryptographic “Twin Key Pair.” The twins operate locked in an unbreakable mathematical relationship, strictly comprising a globally published Public Key coupled silently with a highly dangerous, intensely guarded Private Key! Any target payload locked and sealed executing the power of the published Public Key can exclusively be cracked solely utilizing the immense mathematical power of the corresponding twin Private Key guarding the castle alone!
- The Visual Metaphor: Imagine your allied contact mails you a heavy “Snap-Lock Padlock (Public Key)” shipped actively in the open unlocked position. You ingest the classified target payload inside the titanium box, actively slam their padlock executing a loud physical “click,” and send the box back. It is irrelevant if hostile syndicate hackers hijack the cargo truck during transit; they stare at the box entirely confused, incapable of opening it! Why? Because your ally securely physically buried the singular unique matching “Unlocking Key (Private Key)” securely inside their secure bunker!
- The God-Tier Advantage: It magnificently and flawlessly obliterates the Key Exchange distribution paradox! Furthermore, advanced architects rapidly mutate this logic converting it to power Digital Signatures (Authentication identity verification) mathematically guaranteeing with 100% certainty that specific payloads originated precisely from an authorized commander.
- The Catastrophic Lethal Vulnerability: Because the heavy gears grinding deep inside this system absolutely demand executing terrifyingly complex infernal mathematical algorithms (Specifically demanding immense prime number factorizations driving the RSA backbone), its processing speed actively crawling extracting the data operates “Incredibly Slowly.” It evaluates orders of magnitude slower than Symmetric matrices and constantly furiously drains energy severely lagging the physical CPUs powering smaller low-tier Embedded silicon microcontrollers causing system hangs!
- 3. The God-Tier Amalgamation (The Hybrid Approach - TLS/HTTPS): Deep inside active corporate networking combat zones, elite top-tier network architects force both separate cryptography camps violently integrating together executing a dual-tag-team assault! The protocol executes Phase One: The software temporarily launches deploying an Asymmetric Cipher acting covertly whispering across the hazardous channel establishing a secure “Shared Symmetric Key” absolutely neutralizing intercepting hackers. Following the successful stealth key creation, both endpoints actively discard the heavy dual-key framework and instantly aggressively shift gears deploying the brutally blazing fast Symmetric Cipher executing the heavy lifting blasting massive intelligence directly across the active link maintaining maximum velocity!
Firing Live Code Rounds: Pulverizing Primitive XOR Encryption in Bare-Metal
To accurately visualize the primitive raw mathematical XOR bit-logic natively, the lead engineer is forcefully presenting a stripped-down demonstration calculating the absolute Most Primitive Symmetric Encryption Vector: Deploying the Bitwise XOR (Exclusive-OR) logic operator. This specific code example is explicitly formatted strictly demanding Clean Code parameters, executing encrypting a standard localized string array deploying a single-character secretive Master Key.
#include <stdio.h>
#include <string.h>
/*
* Simulation Protocol: Executing violently rapid Symmetric Encryption deploying primitive Bitwise XOR logic.
* The core mathematical theorem dictates: any target data structure heavily distorted and crushed encrypting executing XOR logic...
* Should we aggressively execute slamming extracting XOR collision utilizing the exact identical numerical key again, it miraculously resurrects the core pristine payload perfectly!
*/
void xor_encrypt_decrypt(char *str, char key) {
/* 🛡️ Strict Iron Security Directive: Absolutely prevent savage Null Pointer Dereference logic errors detonating the motherboard! */
if (str == NULL) {
return;
}
int len = strlen(str);
for (int i = 0; i < len; ++i) {
/* Forcefully smash grinding the target ASCII character bit-matrix crashing directly into the secretive Key variable */
str[i] ^= key;
}
}
int main(void) {
/* Top-Secret National Defense Plaintext Intelligence Payload */
char secret_message[] = "Hello, Microcontroller!";
char symmetric_key = 'K';
printf("Original Data: %s\n", secret_message);
/* Tactical Objective 1: Drop the raw payload directly into the shredding algorithm (Encrypting) */
xor_encrypt_decrypt(secret_message, symmetric_key);
printf("Encrypted Data: %s\n", secret_message);
/* Tactical Objective 2: Recover the mangled Ciphertext garbage structure, dropping it returning feeding the decoding matrix utilizing the precise identical Key (Decrypting) */
xor_encrypt_decrypt(secret_message, symmetric_key);
printf("Decrypted Data: %s\n", secret_message);
return 0;
}
⚠️ ABSOLUTE CRITICAL WARNING: The crude XOR software coding logic actively displayed above exists entirely exclusively fueling fundamental bit-level theoretical educational research! Thrusting this specific XOR logic inside a real-world active hostile factory production theater is catastrophically pathetic and mathematically weak, completely incapable of blocking even primitive rogue hacker interference vectors. International engineering laws forcibly mandate you strictly interface deploying invoking legendary universal libraries executing heavily armored AES-256 executing from OpenSSL or invoking mbedTLS strictly!
Proximity Defcons: Cease Arrogant Fire-Play! Survival Logic inside the Crypto Minefield
Arrogantly aggressively slamming a screaming keyboard coding attempting manual authorization managing software C-language Security architecture definitively represents the absolute most terrifyingly fatally chaotic heavily mined combat zone (An Absolute Software Minefield)! Elite global mastermind architects have flagged exposing massive horrific sinkholes erecting tactical warnings commanding you:
- Absolutely Never Arrogantly Execute Forging Your Own Personal Cryptographic Algorithms! (Don’t Roll Your Own Crypto!): The paramount absolute physical law commanding Kerckhoffs’s Principle aggressively points out: “A highly robust secure cryptographic framework must maintain indestructible safety even assuming the enemy hostile hacker completely breaches your firewall, stealing your core source code and comprehending the algorithmic execution parameters down crossing every single integer line! (The enemy understands completely everything regarding the combat structure, explicitly lacking solely the single hidden master Key).” If your ego attempts manually programming raw C integrating bits mixing random addition shifting mathematics manually generating Custom Algorithms, it absolutely mathematically DOES NOT classify rendering a strong Encryption matrix! Highly skilled dark-web hackers can effortlessly crack decimate those garbage algorithm logics freely consuming under 5 minutes. Kill your coding ego immediately, heavily bow executing invoking universal mathematical standards surviving the vicious torture mathematically proven by thousands of elite cryptographers deploying AES or RSA continuously!
- Violently Shunt the Processing Nightmare Directly onto Silicon Hardware Architecture! (Hardware Cryptographic Acceleration): Surviving inside tiny embedded board layouts, allowing a pathetic 8-bit sluggish CPU forcefully crawling attempting calculating the infernal mathematical RSA prime-factorization arrays or churning AES-256 utilizing Pure Software architectures aggressively detonates ripping your battery supplies entirely obliterating the device! It immediately throws system monitoring routines into chaotic freezing stalling causing brutal hard resets! The ultimate primary rule executes: BEFORE attempting lowering your finger writing generating a single software logical statement, equip your glasses violently flipping open ripping through the exact technical Datasheet matching your specific microcontroller silicon. Aggressively search confirming identifying whether it possesses heavy hard-mounted Cryptographic Hardware Acceleration logic modules permanently etched physically! Assuming it detects positive, immediately shift your entire trajectory commanding the architecture heavily executing software requests plunging directly interacting with those specific Hardware APIs! Invoking hardware module architectures runs blindingly orders of magnitude faster totally remaining hidden shielding the operations avoiding catastrophic side-channel attacks running significantly faster safer infinitely surpassing writing compiling your own vulnerable C source code!
- Detect and Defend Against the Lethal Random Generation Death Trap (The PRNG Trap): Premium-tier globally deployed encryption security keys operating across this entire planet are mandated born explicitly transmitted relying strictly upon randomizing numerical logic structures completely alien totally unpredictable entirely hiding blocking any hostile hackers! (Operating demanding Cryptographically Secure PRNG - CSPRNG matrices)! Absolute maximum prime regulatory law dictates: Absolutely completely prohibit violently utilizing the basic C-language foundational baseline function
rand()desperately attempting generating your defensive numerical Keys! The fundamental structural physics governing that primitive randomization function remains pathetically mathematically deterministic (Stupidly static and mathematically weak), immediately allowing advanced enemy hackers deploying algorithmic mathematical reverse-analysis predicting trapping ripping intercepting every password sequence completely extracting your payload! You are absolutely forced extracting hardware resistance structures invoking a genuine True Random Number Generator (TRNG) hardware module, or actively scraping noise static variables aggregating heavy entropy (Noise Entropy) from analog ADC pins! - Defend the Key Parameters Embracing Mortal Combat! (Key Management Apocalypse): Your NASA-tier mathematical algorithm aggressively operating enforcing indestructible levels exceeding universe parameters remains totally worthless, instantly collapsing disintegrating into putrid digital garbage instantly… IF you arrogantly lazily attempt Hard-coding permanently burning the master encrypted secret key physically locked inside the active Plaintext Source Code strictly openly exposing naked character strings! Because absolutely any hostile criminal extracting capturing pulling downloading the
.binfirmware dump or tracking pulling extracting the.hexfile directly unplugged straight from silicon chip easily loads the file executing standard software tools peeling violently extracting isolating decoding the string revealing your master cryptographic key effortlessly cracking your entire network! (Study Secure Enclaves and TrustZone immediately!)
Conclusion
Carving out the ultimate absolute final logic line unconditionally observing the massive operational macro-view encompassing hardcore defensive Security and Integrity structures, modern Encryption technology—whether analyzing the architectural strategy deploying the Symmetric front (Brutally slamming a single shared key blasting rapid execution) or the Asymmetric side (Erecting a highly flexible heavily delayed crawling completely separated twin-key protocol)—represents an arsenal of heavy artillery weaponry. Modern bare-metal embedded developers must intelligently deploy precisely matching the operational tempo and threat vectors actively surrounding intercepting protecting heavily shielding classified secretive user-generated payloads actively avoiding shadow-level snipers desperately attempting hijacking tearing the transmission stream intercepting lines! Nevertheless, forcefully deploying impenetrable defensive walls absolutely requires mathematically combining heavily aggressively utilizing deploying universally recognized internationally tested standardized algorithms entirely executing absolute freezing protection hiding the absolute Master Cryptographic Key configurations.
If the heavy hardcore soldering smoke operatives participating deeply appreciate tearing studying viewing the heavy C-language code logic aggressively piercing deploying deep communications commanding the isolated raw Hardware Crypto modules executing directly commanding dense Microcontroller hardware layouts, or you aggressively crave aggressively learning executing tracking pulling porting deploying high-architecture universal libraries invoking standard mbedTLS downloading—absolutely immediately breach our community dropping heavy thread topics igniting brutal combat debates discussing advanced sharing violent logic programming ideas continuously directly across the specialized combat community message board operating positioned specifically at www.123microcontroller.com! Maintaining active defense capabilities guarantees our protocols aggressively continuing advancing eternally adapting responding surviving preventing any hacker infiltration! Happy Secure Coding, everyone!