Data Structures & Memory Management: The Art of Organizing RAM for Flexible and Bug-Free Code
Introduction: Data Warehouses and Hardware Layout
Hello engineers and fellow developers at www.123microcontroller.com! We meet again, and today the dark-eyed engineer is bringing you face to face with a subject that forms the absolute beating heart of robust System Programming: The inseparable, symbiotic relationship between Data Structures and Memory Management.
In bare-metal terms, the RAM inside your microcontroller is exactly like an immense, entirely empty warehouse. If we casually throw raw data into it arbitrarily, finding and sorting what we need later becomes an architectural nightmare. A Data Structure acts precisely as the “industrial shelving” or “inventory management system,” optimizing how rapidly we store and index that data.
However, in standard C—where there is absolutely no automated Garbage Collection saving us—we act as the sole warehouse managers. The sheer structure of our data is relentlessly bound to how we manage the raw memory underlying it. Today, let’s dissect exactly how elite engineering literature describes constructing robust Data Structures in the unforgiving realm of Embedded Memory!
The Collision of Data Logic and Memory Arenas
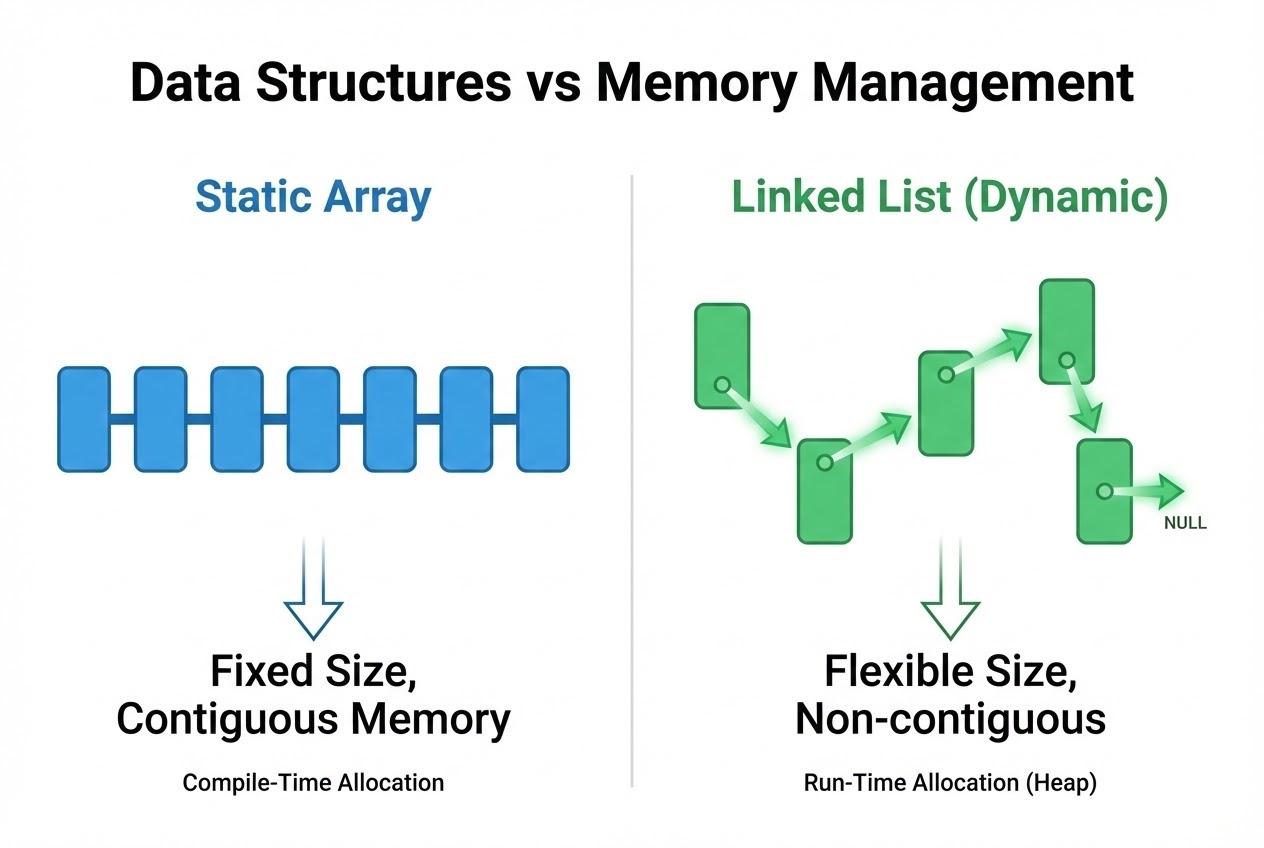
Within the C ecosystem, Data Structures predominantly bifurcate into two core worlds, dictated entirely by their memory footprint signatures:
- 1. Static Data Structures:
This category includes classical Arrays and flat Structs. These architectures demand firmly “Contiguous memory” (bytes occupying adjacent silicon addresses) and mandate explicitly knowing their maximum size at Compile-time.
- The Advantage: Brutally fast execution. They allow instantaneous Random access via simple index offset math and inherently offer zero risk of Memory Leaks.
- The Drawback: Zero flexibility. If you hyper-allocate an oversized array, you permanently waste precious bare-metal RAM. If you under-allocate, an incoming data spike triggers a catastrophic Buffer Overflow.
- 2. Dynamic Data Structures:
Whenever we process inherently fluctuating data (e.g., asynchronous command queues, variable-length sensor telemetry lists), we unleash Linked Lists, Trees, Stacks, or Queues. These entities dynamically “inflate and deflate” strictly during Execution time (Runtime).
- The Core Mechanism: These structures manipulate reality through Self-Referential Structures married to the almighty Pointer. Pointers act as the physical “chains” linking fragmented nodes scattered wildly across the Heap memory zone.
- The Role of Dynamic Allocation: Appending a Node in a Linked List demands invoking
malloc()to requisition Heap silicon space. Once dismantled, we are honor-bound to return the territory viafree().
- 3. The Embedded Developer’s Nightmare:
In desktop PC programming, hammering
malloc()is relatively benign. But in resource-constrained microcontrollers, rapidly spinning up and tearing down Dynamic Data Structures introduces deadly Memory Fragmentation. This phenomenon splinters your RAM into tiny pockets. Eventually, the hardware possesses enough total bytes, but no contiguous block large enough to satisfy an allocation request, crashing your firmware unpredictably. - 4. The Hardware Engineering Solution - Memory Pools:
Advanced system architecture books dictate a phenomenal pivot: When Embedded Systems require dynamic structures like Queues, we completely bypass standard
malloc(). We employ Memory Pool Allocation (Arena Allocation). This involves reserving one massive Static array of Structs at compile-time. We then manually juggle Pointers back and forth inside this isolated Pool to emulate dynamic behavior, utterly obliterating Fragmentation andmallocoverhead risks!
Code Example: Clean Struct Allocation and Memory Auditing
Let’s examine the anatomy of spawning a single Node for a Dynamic Linked List, rigorously securing our memory interactions (Clean Code).
#include <stdio.h>
#include <stdlib.h>
/* 1. Crafting the Self-Referential Structure */
typedef struct Node {
int data; // The payload
struct Node *next; // The hardware Pointer chaining to the next chronological Node
} Node;
/* Function injecting a new node with armored memory validation */
Node* insert_node(Node *head, int new_data) {
/* 2. Dynamic Memory Allocation: Requesting Heap territory */
Node *new_node = (Node*)malloc(sizeof(Node));
/* 3. ARMOR: Always verify against Heap exhaustion (Null Pointer Dereference defense) */
if (new_node == NULL) {
printf("CRITICAL: Memory allocation failed!\n");
return head; // Abort operation, return intact legacy list
}
// Assign payload and weave the chain (Link)
new_node->data = new_data;
new_node->next = head;
return new_node; // Return the newly established head
}
/* Function annihilating the List and returning memory safely to the OS */
void free_list(Node *head) {
Node *temp;
while (head != NULL) {
temp = head;
head = head->next;
/* 4. Sequentially dismantle and free each specific Node.
Failure here triggers an immediate Memory Leak. */
free(temp);
}
}
Best Practices to Defend Against Memory Demons
Weaving Data Structures via raw Pointers is the equivalent of juggling chainsaws. Slip up, and your processor halts. Security standards (like SEI CERT C) aggressively caution the following:
- Exorcise the Memory Leak Demon: Elaborate structures like recursive Trees or vast Linked Lists demand highly surgical destruction sequences. When discarded, you must construct a loop explicitly running
free()on absolutely every spawned node. Orphaning a single Node constitutes a Memory Leak, which silently vampirizes your RAM until your board suffers full Memory Exhaustion. - Eliminate Dangling Pointers (Zombie Links): After detonating a Node via
free(), the Pointer referencing it technically still retains that physical hex Address. Utilizing this zombie interface is a fatal “Use-after-free” vulnerability. Institutional rule: Always overwrite killed pointers explicitly withNULLinstantaneously. - Beware the Shadows of Struct Padding: When packing raw silicon data into Structs, watch your Memory Alignment. Processors often architecturally enforce that Integers sit strictly on an easily divisible address offset (e.g., divisible by 4). Resultantly, compilers aggressively inject invisible dead space (Padding/Holes) between your Struct members, permanently bloatifying your memory map. (Fix this by organizing Struct members from largest to smallest, or deploying
#pragma packfor hyper-compact Network packet transmission). - Avoid Deep Recursion on Trees: Deploying elegant Recursion functions to traverse immense Binary Trees is academically beautiful but practically suicidal on microcontrollers. Recursion ruthlessly consumes Stack Memory (generating stacked Activation Records corresponding to Tree depth). Small, embedded Stack limitations will instantly result in a devastating Stack Overflow. Always favor iterative while-loops coupled with a manually tracked Heap Stack.
Conclusion
Data Structures are not merely abstract academia you endure in college. They represent the actual silicon “blueprint” dictating exactly how aggressively your firmware consumes and organizes raw hardware Memory. C language blesses us with god-like tools—Pointers and Dynamic Allocation—facilitating the creation of infinitely intricate topologies. But that terrifying power demands the unyielding responsibility of micromanaging allocation and destruction. For the hardcore Embedded specialist, pivoting exclusively to Memory Pools interacting with Linked Lists yields the ultimate hybrid: Supreme Flexibility merged seamlessly with Secure Stability.
Hopefully, this piece vividly illustrates the low-level, metallic connection bridging logic and raw memory execution. If you have engineered utterly bizarre data structures, or have nightmare stories tracking down ghost memory leaks, come join our community forum and share your tales at www.123microcontroller.com. See you in the next architectural breakdown. Happy Coding!