Data Encoding (Base64): Decoding the Illusion—Shattering Dangerous Myths Regarding Security and Data Integrity

Introduction: Stripping the Cryptographic Mask off Base64
Greetings, elite systems engineers and heavily armed bare-metal coders defending the www.123microcontroller.com servers! The dark-eyed engineer has emerged from hunting memory leaks to initiate another technical briefing. Today, we explicitly target and completely obliterate a catastrophic conceptual pitfall that routinely deceives amateur programmers, blindly leading critical embedded projects directly into horrific software security apocalypses: The widely misunderstood domain of Data Encoding—focusing our crosshairs aggressively on the notorious Base64 mechanism, analyzed strictly within the ruthless parameters of Security (Cryptography) and Integrity (Assisted Data Survival).
When our tactical teams deploy deep writing Embedded C firmware or aggressively funneling raw payloads blasting across ethernet communication sockets, the term ‘Base64’ predictably constantly pollutes the documentation arrays. Tragically, a massive demographic of rookie engineers hallucinate an incredibly dangerous, totally flawed psychological comfort matrix, falsely celebrating: “Excellent! I crushed and converted my user payload through the Base64 shredder! The data is now fully wrapped in military-grade security! No hostile hacker interception can possibly decipher this!”
Terminate that line of thought instantaneously! That constitutes a violently inaccurate, borderline insane technical hallucination possessing catastrophic consequences! Today, we leverage elite architectural intel dissecting this mechanism, exposing the absolute raw truth regarding exactly why Base64 was historically forged into existence, and calculating exactly why mathematically it provides absolutely zero cryptographic shielding guarding your deployment from malicious data assassination attempts!
Architectural Core Autopsy: What is Base64, and Why Did the Computing Ancestors Forge It?
Before proceeding with any tactical coding analysis, we are under strict orders to brutally separate and categorize the cognitive boundary locking two distinct definitions. We must isolate Integrity (The mathematical checksum firewall explicitly guaranteeing a payload arrives entirely flawless, completely unmodified, untouched by corrupting background noise or rogue hostile tampering vectors) permanently away from Security (The hardened cryptographic titanium vault—Encryption—exclusively restricting access intercepting and denying unauthorized optical penetration by hostile surveillance networks).
Analyzing the deep historical archives governing legacy network data transmission protocols, architectural intelligence documents explain the legitimate, original intended tactical application belonging to Data Encoding explicitly:
- 1. A Desperate Lifeline Rescuing Ancient Protocol Architectures: Numerous archaic internet transmission protocols crawling out of the computing dark ages (A legendary prime example remaining the ancient SMTP email transmission pipeline) were strictly historically architected functioning exclusively constrained transporting only highly filtered “Plain Text Characters” confined entirely inside the primitive 7-bit ASCII boundaries. If an aggressive engineer impatiently attempted violently blasting highly unstable raw Binary payload clusters (such as dense image pixel matrices or aggressively compressed ZIP archive clusters) hammering directly down these legacy protocol pipes, the transmission geometry would instantaneously shatter. The receiving architecture would critically hallucinate interpreting rogue binary fragments identically as volatile Control Codes (System command triggers), violently crashing the transmission link mid-flight!
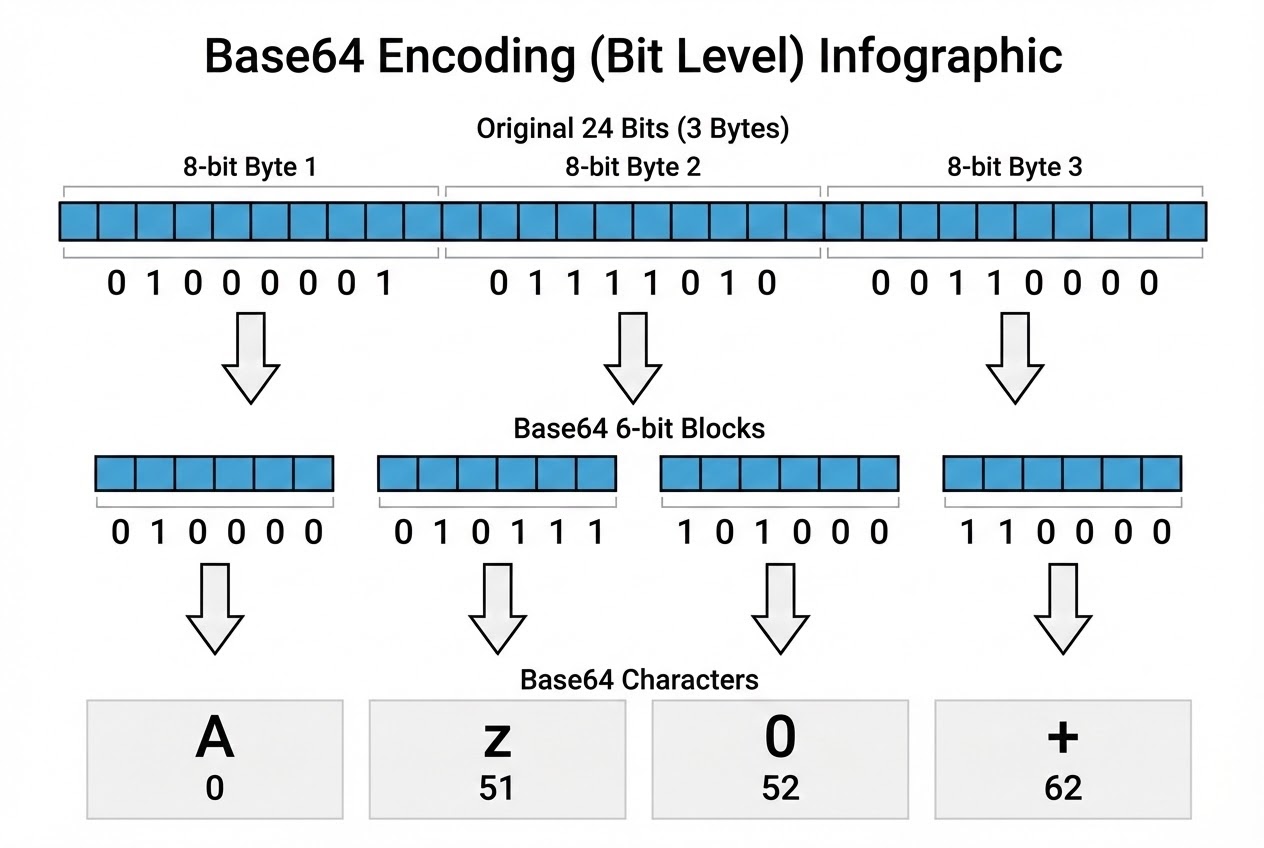
- 2. The Byte-Mutilation Mechanics Governing Base64 operation: The ultimate engineering survival tactic conceived circumventing executing catastrophic binary delivery traversing hyper-restricted text pipelines deployed utilizing the Base64 conversion algorithm. Inherently, this exists fundamentally merely as a mechanical “Binary-to-Text Encoding” translation cipher. Its execution logic operates ruthlessly mimicking an industrial meat grinder shredding and reassembling fragmented data zombies. It aggressively targets the incoming payload marching file, ripping sequences binding raw 8-bit bytes aligning a continuous string, only to violently decapitate and forcefully chop them into smaller, entirely synthetic 6-bit fragment blocks (Mathematically calculating, a 6-bit grid limits explicit possible variations containing strictly absolutely a maximum boundary encompassing just 64 possible combinations).
- 3. The Alchemical Conversion: The Unforgiving 3-to-4 Ratio: Analyzing the mathematical geometry belonging to this slicing mechanism undeniably confirms: An original, pristine baseline segment consisting exactly of 3 complete continuous Bytes (Summating equaling explicitly 24 pure bits) faces mandatory execution being shredded multiplying expanding outwards forging 4 smaller fragmented blocks (measuring exactly 6 bits each). The operating mechanism subsequently hijacks these numerical blocks, scanning mapping them mathematically directly against a universally hardcoded dictionary index translating against specific safe alphabetic/numeric ASCII symbols (A-Z, a-z, 0-9, and including the + and / markers). This completely masks the raw binary, mutating it transforming outward manifesting exclusively as sanitized, clean ASCII characters achieving secure passage successfully infiltrating highly restricted legacy networks perfectly unchallenged. (As a visual identifier, a massive raw executable file undergoes forced mutation spewing out a nauseating infinite chain of randomized, confusingly garbled characters superficially resembling:
VGhpcyBpcy...). - 4. The Terrifying Apocalyptic Hallucinations Defeating Security and Integrity ❌: Elite cryptographic cyber-security combat veterans globally universally blast out blistering siren warnings unequivocally dictating: Deploying a simplistic Encoding algorithm mimicking Base64 mathematically injects absolutely zero cryptographic Security benefits defending your architecture infrastructure whatsoever! It constitutes literally nothing more advanced than a cheap optical illusion—an explicit “Alternative Visual Representation” masquerading data. Any pathetic script-kiddie hacker loitering on the network instantly visually identifying the Base64 signature suffix can effortlessly aggressively copy-paste the bloated string crashing it directly inside an online Base64 Decoder algorithm, neutralizing it converting back extracting the 100% naked plaintext payload instantly in fraction-of-a-second timestamps, absolutely bypassing all requirements requesting a complex cryptographic cipher Key! (In staggering stark contrast drastically opposing legitimate mathematical Encryption mechanisms strictly commanding impossible mathematical Keys calculating logic sequence decryptions). Furthermore, pivoting analyzing the Integrity defense grid, Base64 offers absolutely pathetic shielding parameters. Its primitive logic circuitry was brutally neglected lacking any embedded capability calculating complex data-Checksums or possessing sufficient operating IQ enabling any error-detection isolating malicious payload mutations intercepting man-in-the-middle attacks!
Firing Live Code Rounds: Pulverizing Bytes! Dissecting the Base64 Algorithm in Bare-Metal C
Initiate extreme logic breakdown analyzing the aggressive C coding tactical approach engaging Bitwise Operational warfare orchestrating a manual Base64 Encoding algorithm forcefully ripping raw 8-bit data chunks generating sliced 6-bit operational fragments. (This elite code demonstration specifically employs robust Clean Code memory shielding and strict Array Bounds Checking parameters preventing terrifying memory overflow hazards).
#include <stdint.h>
#include <stddef.h>
/* 1. Establishing the Architectural Ledger: Generating the static Lookup Table Dictionary mathematically resurrecting crushed 6-bit numerical fragments restoring visible Base64 ASCII characters. */
static const uint8_t b64_table[] = {
'A','B','C','D','E','F','G','H','I','J','K','L','M',
'N','O','P','Q','R','S','T','U','V','W','X','Y','Z',
'a','b','c','d','e','f','g','h','i','j','k','l','m',
'n','o','p','q','r','s','t','u','v','w','x','y','z',
'0','1','2','3','4','5','6','7','8','9','+','/'
};
/* 2. Deploying the Heavy Execution Function: Shredding hot, raw Binary memory blocks actively synthesizing Base64 output arrays (Simulating exclusively processing perfect 3-Byte segmented payloads). */
size_t base64_encode_chunk(const uint8_t *p_in, size_t in_size, uint8_t *p_out) {
size_t out_size = 0;
uint8_t index1 = 0, index2 = 0, index3 = 0, index4 = 0;
/* Deploy Defensive Logic Shield: Authorize execution entirely exclusively when the payload parameter mathematically verifies grabbing an exact 3-Byte block (Precisely 24 Bits). */
if (in_size == 3U) {
/* Execute Slice 1: Brutally extract the high-order 6-Bits occupying the initial Byte by forcefully applying a logical Right-Shift 2-Bit displacement. */
index1 = p_in[0] >> 2;
/* Execute Intersection Slice 2: Scrape extracting the remaining bottom 2-Bits dangling off the first Byte, violently pushing applying a Left-Shift 4-Bit displacement.
Concurrently orchestrate a Bitwise OR (Merge) violently colliding capturing the highest 4-Bits ripped from the adjacent second Byte matrix. */
index2 = ((p_in[0] & 0x03U) << 4) | (p_in[1] >> 4);
/* Execute Intersection Slice 3: Aggressively harvest the residual bottom 4-Bits abandoned by the second Byte, dragging forcing a Left-Shift 2-Bit displacement.
Immediately launch a Bitwise OR collision slamming crushing integrating the extreme highest 2-Bits snatched off the final third Byte geometry. */
index3 = ((p_in[1] & 0x0FU) << 2) | (p_in[2] >> 6);
/* Execute Final Slice 4: Completely annihilate harvesting consuming the remaining naked bottom 6-Bits constituting the entire third Byte perfectly. */
index4 = p_in[2] & 0x3FU;
/* Project extracted indexing coordinates (Bounded 0-63 mathematically) cross-referencing engaging the Base64 illusion dictionary, violently pushing mapping characters straight back executing into the Output Cache. */
p_out[0] = b64_table[index1];
p_out[1] = b64_table[index2];
p_out[2] = b64_table[index3];
p_out[3] = b64_table[index4];
out_size = 4U; /* Stomp validation signature: Officially logging we bloated the payload successfully dumping 4 entire Bytes writing them completely into the active Buffer Array. */
}
return out_size; /* Return executing tactical calculation exporting the explicit geometry size artificially inflated expanding populating the true Output Buffer array. */
}
(Algorithm adapted deploying elite logic referencing Bitwise chunking architectures extracted evaluating Core Linux system processing documentation)
Proximity Defcons: Cease Arrogant Fire-Play! Mastering the Dangerous Two-Edged Base64 Blade
Despite observing the Base64 algorithm behaving transparently essentially characterizing a mundane, simplistic external masking tool managing arbitrary formatting parameters across crossing server lines, severe danger lurks. If an arrogant engineer completely miscalculates executing catastrophic memory-management tracking parameters inside C logic systems, the architecture aggressively spirals unlocking apocalyptic system vulnerabilities terminating security! The impenetrable Secure Coding standards framework violently strikes alarm klaxons screaming these immediate danger vectors:
- Strict Prohibition: Never Conceive Leveraging Base64 Architecting Cryptographic Defense (Never Deploy Encoding Masking Encryption): The absolute prime poisoned directive demanding permanent recording onto your neural wetware states explicitly: The logic action ‘Encoding’ absolutely $\neq$ ‘Encryption’ parameters! Arrogantly attempting establishing “Obfuscation (Masking)” wrapping highly classified intelligence utilizing Base64 operates as an absolutely pathetic, childish security paradigm fundamentally categorized classified universally as (Security through Obscurity). Assuming the targeted data packet harbors system admin root-passwords or heavily classified operational secrets belonging to corporate superpowers, you remain under extreme unyielding architectural orders exclusively commanding deployment utilizing military-grade encrypted Cryptographic Library protocols (Execute AES-256 or ChaCha20 cipher blocks) wrapping and dominating the payload without exception!
- Averting Apocalyptic Buffer Overflow Execution Through Failed Dimensional Geometry Math: The absolutely terrifying classic black-hole trap routinely murdering amateur C-developers originates stemming entirely derived fundamentally forgetting analyzing the undisputed physics constraint guaranteeing: Generated Base64 output data geometries “Always Expand Calculating Massively Bloated Volumes” drastically dwarfing original input payload footprints! (Calculate maintaining a relentless rigid expansion geometric ratio multiplying 4/3—effectively forecasting visualizing artificial weight inflation hovering aggressively establishing a minimum 33% expansion velocity). If your pathetic garbage code logic accidentally negligently calculates allocating an undersized memory boundary establishing restricted limits protecting the Output Buffer array, the execution trajectory mathematically rockets off a cliff dropping immediately generating devastating Memory Corruption fractures or inciting catastrophic, catastrophic Buffer Overflow events eagerly opening heavy blast doors guaranteeing exploit-chain penetration success!
- Global Level Annihilation Triggered Orchestrating Integer Overflow Swarms: Heavily encrypted security intelligence reports explicitly alongside globally filed vulnerable CVE-2009-0587 combat debriefings extensively record analyzing real-world cataclysmic software destructions inside platforms identically resembling the Evolution Data Server. This specific vulnerability cratered suffering explosive “Base64 Integer Overflow” execution anomalies! This massive structural failure originated tragically during the precise operating millisecond extreme volume storm-fronts transporting massive gigabyte Base64 logic pipelines fiercely accelerated colliding crashing directly onto receiving architectures. The active parsing buffer allocation algorithms violently calculated devastatingly incorrect integer logic mathematics causing logic maximums severely overloading triggering an Integer Wraparound failure (Flipping maximum numbers resetting collapsing targeting zero). This catastrophic failure brainwashed the compiler violently tricking it reserving pathetically microscopic memory allocations! This constituted the legendary golden vector granting hostile hacker divisions absolute velocity launching devastating execution chain-exploits aggressively establishing absolute total remote systemic takeover maintaining unchallenged zero-day authority!
Conclusion
Re-calibrating reversing our perspective encompassing the brutal environment defining executing bare-metal low-level C firmware controlling complex operational hardware parameters, the mystical Base64 execution logic basically translates identically mimicking the operational capabilities belonging to a mundane “Standardized Postal Service Employee.” Its complete functionality resolves around successfully assisting packing wrapping concealing your completely unintelligible, highly complex chaotic binary geometry configurations, operating seamlessly converting them projecting standardized alphabetic optical appearances. This flawlessly authorizes safely routing your packets penetrating incredibly archaic, deeply limited protocol communication pipelines avoiding activating destructive filtering trip-wires completely reliably. However, critically realize that this specific postal carrier absolutely completely neglects locking deploying impregnable titanium cryptographic padlocks effectively stopping data-assassinations (Operating strictly guaranteeing Zero Security) and fundamentally utterly fails completely stamping carrying any magical wax-seal verification matrices halting hostile ghost-snipers intercepting illegally altering mutating localized payload data logic vectors mid-flight (Sustaining Zero Integrity parameter checks). Plunging your fingers into hardcore C terminal key-strikes forcefully commanding raw Base64 injection logic completely demands awakening unyielding extreme precision controlling chaotic volatile memory Pointer manipulation physics, simultaneously requiring advanced mathematical calculation capabilities perpetually managing evaluating bloated expanding Output Array buffer sizes anticipating disasters!
If rogue keyboard-warriors in this unit hold aggressive obsession actively demanding tearing analyzing peering directly into dissecting the complete absolute extreme execution code orchestrating a fully operational Base64 Decoder engine forcibly tearing strings extracting core data, or possess a violent demanding thirst calculating evaluating the advanced mathematics required properly executing fusing integrating raw Base64 strings actively loaded slamming directly into heavy-ordnance Cryptographic Algorithmic warfare grids (Legitimate Espionage Encryption) operating targeting AES-256 geometries—immediately invade breaching the perimeter sharing fierce intellectual combat coding parameters inside our highly secured tactical deployment forum-zone servers localized specifically at www.123microcontroller.com! Infinite classified bytes continuously hold hidden encrypted riddles actively anticipating decryption! Maintain heavily armored code compilation matrices until deploying targeting executing our subsequent aggressive firmware code-strike article. Stay violently secure, hardcore Firmware Hacker logic specialists!