Conditional Compilation (#ifdef, #ifndef): The Bare-Metal Code Switch of the C Preprocessor

Introduction: Forging a Single Codebase to Dominate All Hardware
Greetings, elite engineers and bare-metal operatives aggressively defending the www.123microcontroller.com grid! The dark-eyed engineer has logged securely back into the command terminal. Today, we meticulously dissect the heavy mechanical architecture definitively explaining exactly why the ancient, brutally efficient C programming language permanently retains the absolute crown dominating the horrific trenches constituting Embedded Systems (Bare-Metal Architecture) scaling across decades! We are tearing into the god-tier execution mechanics powering the C Preprocessor, specifically targeting the heavy architectural warfare defining Conditional Compilation.
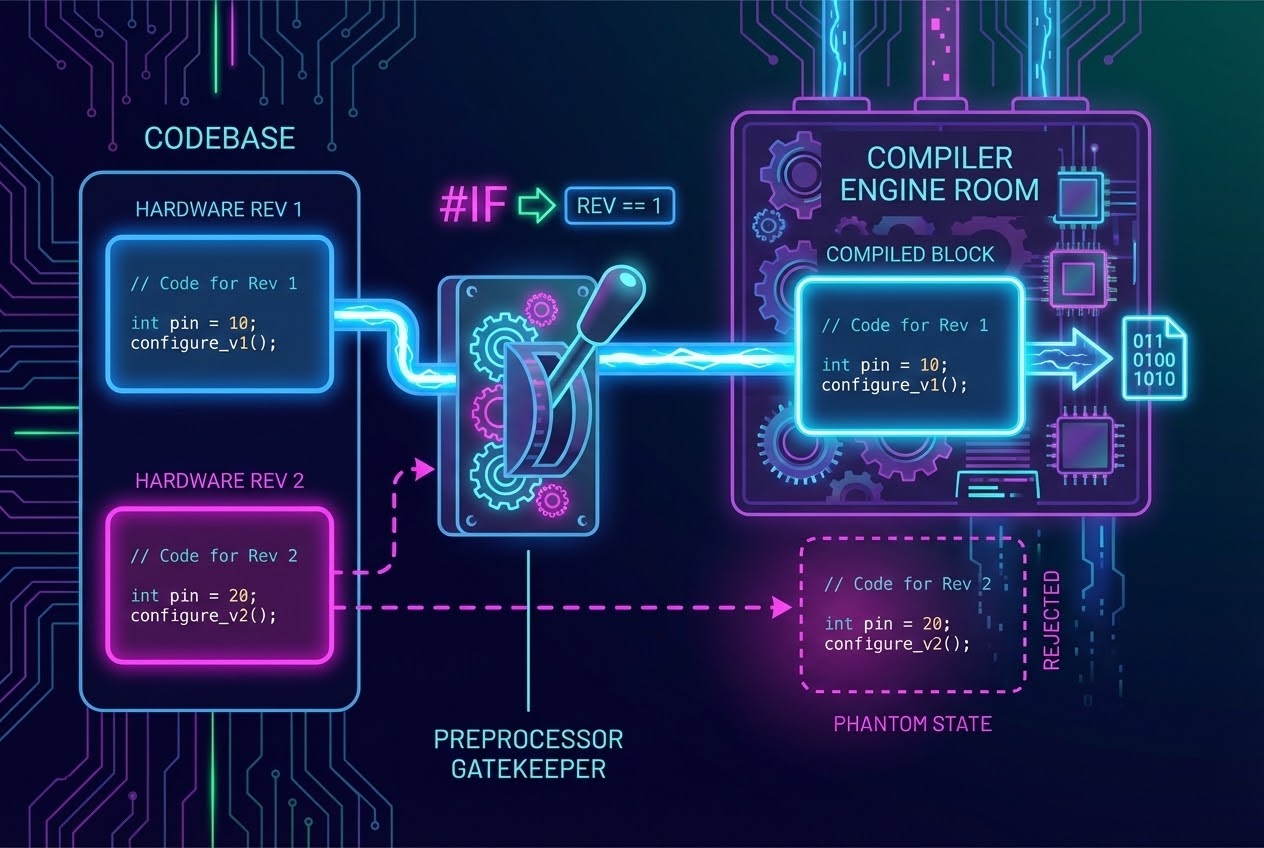
Visualize simulating this exact combat scenario: Your engineering firm aggressively commands you constructing deploying the central firmware core actively controlling driving three entirely distinct microcontroller hardware revisions (e.g., The stripped-down budget prototype, the standard commercial board, and the heavily-armored flagship silicon). Executing as a junior developer, do you pathetically surrender, manually “copy-pasting replicating the entire project violently splintering it into three completely isolated, unmaintainable directory folders” separating the logic executing for each specific board? The explosive response echoing from veteran software architects is: “Absolutely Mathematically Ignorant! Never execute such chaotic redundancy!” By successfully deploying harnessing the radioactive authority generated wielding specialized directives including #ifdef and #ifndef, elite architects flawlessly manipulate utilizing One Single Unified Master Source Code Repository (Single Codebase). We aggressively violently scream commanding the localized Compiler Engine to intelligently “Switch On, Actively Select, and Physically Assemble” exclusively extracting compiling localized code blocks matching executing targeting the precise silicon hardware specification profile requested! Today, we aggressively crack open the Master Engineering grimoires, extracting identifying observing exactly how elite C-Priest architects weaponize this capability, alongside exposing the lethal red-flag restrictions strictly enforcing survival! Secure your helmets, let’s deploy!
Core Theory Autopsy: Conditional Compilation - The Logic Railway Switch
Before initiating attempting extreme execution maneuvers, we absolutely must aggressively calibrate our situational awareness confirming the C Preprocessor fundamentally operates adopting the role representing a heavy industrial preliminary-worker drone. It violently executes “Pre-processing operations launching initiating aggressively prior to” the actual biological compiler engaging actively crushing the data packaging generating raw assembly Machine Code! It functionally strictly acts imitating an “Imbecilic, Brain-dead Specialized Text Substitution Editor (Text substitution engine).” Its primary scanning radar sweeps solely exclusively tracking and physically manipulating command instructions strictly initiating featuring the leading charge # (Hash / Directives).
Expanding the architectural magnification tracking deeply into the structural core, Conditional Compilation identifies as the supreme architectural capability empowering the developer physically aggressively manually throwing heavy logic switches explicitly commanding the Preprocessor Drone. We forcefully demand it either violently “Seize, Capture and Actively Include (Compile)” or ruthlessly execute “Deleting, Trashing, Violently Discarding (Exclude/Discard)” highly specific localized text-fragments entirely completely evaporating them straight out of the physical Source Code documents! It executes this purge milliseconds prior to packaging feeding the surviving data into the physical Compiler engine. It identically perfectly mirrors manning a massive railway line logic switch, violently physically redirecting the massive hurtling code payload train strictly forcing it barreling down restricted tracks perfectly aligning evaluating against the parameters governing the boundaries we defined!
The Heavy Artillery Arsenal Controlling Operating Code Destinies:
#ifdef(If Defined): Actively violently interrogates verifying confirming: Has this specific Macro identity or targeted parameter Identifier variable actually been “Physically Birthed, Officially Stamped, and Legally Defined” existing anywhere inside the current active compilation universe? If the radar screams validating “CONFIRMED! Target Locked and Defined!”, the sequential code payload structurally positioned entirely directly below this specific barrier line, cascading downwards flowing until it violently impacts slamming against the final retaining wall#endif, gets exclusively authorized forcefully thrown gathered injected directly into the active compilation hopper! This mechanical rune physically embodies translating matching the exact identical equivalent operational power representing the command string#if defined(name).#ifndef(If Not Defined): Violently executes aggressively reversing the propulsion completely reversing the logic engine! It exclusively authorizes extracting granting compiling the block-code payload strictly engaging ONLY IF the specific targeted Macro identity “Absolutely Has Never Legally Existed, Never Registered, Nor Birthed inside the entirety of the current dimensional compilation universe!” This brilliant subterranean infiltration stealth maneuver represents the absolute heavy-favorite tactic excessively weaponized by hardcore architects constructing impenetrable fortress Include Guards.#if,#elif,#else,#endif: This constitutes the full-magazine heavy machine-gun ammunition belt! Deployed exclusively tracking processing verifying evaluating executing heavy mathematical arithmetic formulas or complex full-scale Boolean logic equations actively locking verifying conditions. Expanding advancing into the absolute modern bleeding-edge global C Standard (The hyper-advanced C23 boundary), elite architects deployed dropping brand new heavily-armored weaponry identified as the#elifdefand#elifndefdirectives! These heavily tactical additions grant engineers engaging executing rapid-fire condition-checking reducing condensing the syntax footprint, generating devastatingly short, ultra-compact, and incredibly aggressive professional execution code!
The Supreme Heroic Roles Executing Governing Heavy System / Embedded Programming Combat: Primary Master architecture encyclopedias actively expose identifying documenting the incredibly expansive massive global utilization integrating this specific mechanism executing:
- Cross-Platform Tactical Codebase Weaponization (Portability Mastership): This incredibly powerful feature instantly obliterates boundaries granting unlocking opening doors allowing one singular ancestral Source Code bloodline successfully standing surviving fighting crushing operations seamlessly natively supporting stretching across a dozen alien Operating Systems, penetrating cracking multiple alien CPU Architecture geometries, or aggressively violently clashing surviving interfacing physical hardware motherboard silicon Revisions dynamically! The singular
#ifdefarchitecture acts supporting bridging switching acting defining the primary load-bearing operational execution pivot. - Erecting Heavy Energy Barrier Include Guards Protecting Header Files: Defending aggressively countering mitigating spreading the horrific viral disease triggering infinite
#includelooping dimensional overlaps crashing generating catastrophic Terminal Error floods! Elite architects aggressively actively deploy wielding the heavy#ifndefcrowbar physically wrapping totally encapsulating protecting shielding the sensitive core contents structurally locked entirely inside the.hHeader Document perimeter. - The Remote Toggle Switch: Activating / Annihilating Solo Operations (Debug Toggle Master): We strategically covertly weave injecting embedding standard output diagnostic data streams (the
printffamilies) tracking locating broadcasting volatile variable bug data, covertly hiding nesting them deep inside the armored belly defining an#ifdef DEBUGblock structure. The very millisecond the operation transitions advancing hitting engaging total-scale combat reality—exporting delivering shipping the final project payload (The Production Release Mode)—we lazily simply press pushing the detonation kill-switch entirely erasing deleting the physical#define DEBUGcommand! The raw chaotic garbage diagnostic testing code payload previously functioning executing printing… gets aggressively swallowed completely evaporating vanishing instantly completely eradicated by the preprocessor drone! It absolutely miraculously totally fails entirely completely refusing entering consuming stealing devouring even one single precious byte occupying the localized flash ROM! - The Cloaking Mechanism: Completely Shredding Evaporating Ghosting Live Code (Conditioning Out): Directly resulting deriving spanning from the wildly primitive, notoriously pathetic block-comment spray architecture (
/* ... */) brutally failing incapable surviving nesting overlapping stacking upon itself creating collapsing black holes (Nested comments fatal error). When operations instantly heavily demand require pushing engineers forcing them violently “Temporarily locking down completely destroying vanishing massive logic block clusters spanning hundreds of physical lines”, elite engineers immediately actively rely aggressively defaulting depending identifying deploying the ultra-premium solution: Violently dropping an#if 0heavily locking crushing the ceiling, and aggressively slamming pulling down closing the execution coffin deploying the#endifstamp capping the absolute tail! This completely bypasses totally aggressively entirely abandoning utilizing the standard pathetic comment symbols guaranteeing incredible flawless obliteration totally secure!
Firing Live Code Rounds: Assembling the Central Single Codebase Firmware Fortress
We actively deploy initiating dismantling ripping apart the core logic observing mapping the architectural blueprint violently simulating constructing drafting an active Firmware Module Grid actively strategically defensively heavily preparing maintaining support locking driving two distinct localized physical silicon Hardware Revision motherboards! Furthermore, we simultaneously aggressively covertly embed actively hiding heavily armed execution toggle-switches manually activating killing the active Debug combat mode directly fully visible! Critical Objective: Aggressively fiercely monitor track memorize the complex lethal maneuvers swapping rapidly deploying utilizing the #ifndef shield wrapper brutally actively actively verifying defending securing the fatal Include Guard boundary! This specific execution act represents an absolute foundational Best Practice pillar column unconditionally demanded fundamentally required by any existing Master C Blacksmith!:
/* =========================================================================
* ARCHITECTURAL FILE: system_config.h (The Master System Parameter Blueprint Manual)
* ========================================================================= */
/* 1. 🛡️ Actively Deploying Erecting the Magical Heavy Shield Include Guard executing #ifndef guaranteeing crushing destroying entirely preventing redundant double-file extraction looping! */
#ifndef SYSTEM_CONFIG_H_
#define SYSTEM_CONFIG_H_
/* FLIPPING THE HEAVY BREAKER SWITCH! Forcing violently opening activating engaging deploying Full-System Debug Diagnostics Mode!
* (Tactical Gimmick Protocol: Assuming a chaotic lazy mechanic accidentally executes wrapping deploying the traditional physical block comment /* */ destroying crushing encapsulating bypassing this exact active operational line...
* That entire national-level massive garbage repository comprising the globally mapped debug print code injected scattered entirely throughout the exact active project absolutely universally violently permanently instantly evaporates completely vanishing dissolving eradicating itself clearing from the ROM memory grid!)
*/
#define DEBUG_MODE
/* FLAG SELECTION SWITCH LOCK! Explicitly statically actively manually locking declaring explicitly defining the targeted hardware silicon board configuration heavily demanding required targeting compiling crushing burning directly compiling onto the physical silicon!
* (Actively manually heavily attempt adjusting rotating modifying snapping the exact parameter value altering it swapping switching entirely directly over dropping hitting Number 2! Observe the chaos!)
*/
#define HARDWARE_REV 1
#endif /* THE SYSTEM_CONFIG_H_ HEAVY SHIELD DOMAIN BOUNDARY HAS BEEN ABSOLUTELY TERMINATED AND SECURED. */
/* =========================================================================
* PRIMARY VANGUARD FILE: main.c (The Primary Central Spearhead Operations Terminal)
* ========================================================================= */
#include <stdio.h>
#include "system_config.h"
int main(void) {
/* 2. Tactical Execution Deployment observing aggressively extracting wielding deploying the #ifdef barrier operating operating acting defining the primary security gatekeeper Toggle Switch heavily violently forcefully unlocking / completely violently shattering the heavily packed restricted Debug Code Matrix. */
#ifdef DEBUG_MODE
/* The mindless automated Preprocessor Copy-Paste drone will meticulously physically actively violently rip extract capturing grabbing pulling this precise sentence code-string payload aggressively combining integrating dropping entirely into the direct Compilation Queue processing line...
*...STRICTLY ABSOLUTELY CONDITIONALLY DEPENDING operating if and only if the primary supreme commanding upper-level master breaker switch 'DEBUG_MODE' historically "Historically legitimately formally actively recently triggered forcefully ignited detonated the #define initialization spark!"
*/
printf("[DEBUG CORE]: The structural hardware engine heart is aggressively violently waking, booting violently actively exploding generating pure power...\n");
#endif
/* 3. Extreme Hardcore Execution violently slamming brutally deploying executing the #if / #elif combination physically acting violently surgically dissecting slicing brutally mutilating aggressively splitting distributing the operational logic code entirely entirely depending conforming adapting directly matching aligning engaging the specified Hardware Blueprint Platform Revision! */
#if HARDWARE_REV == 1
printf("[SYSTEM ALERT]: Violently violently aggressively transferring supplying firing voltage power configurations actively rapidly setting-up heavily initializing pounding directly targeting Hardware Revision 1 physical Silicon Board Pins...\n");
/* Geometrically aligning structurally within this specific sector, the module demands aggressively violently firing triggering executing the exact localized pin-switching algorithm module target: config_gpio_pin(PIN_A); */
#elif HARDWARE_REV == 2
printf("[SYSTEM ALERT]: Actively dynamically physically relocating sweeping shifting shifting power address routing voltage configurations violently violently violently actively plunging connecting directly transferring actively smashing hitting the secondary Hardware Revision 2 Silicon Board Platform...\n");
/* The operational environment architecture violently completely completely fundamentally transformed physically changed. We must actively radically heavily deploy violently firing aggressively targeting exchanging swapping executing engaging an entirely different localized targeted physical module pin-switching designated tracking coordinate algorithm identity instead: config_gpio_pin(PIN_B); */
#else
/* 4. The Ultimate Supreme Final Skull-Crushing Execution Kick! Actively aggressively deploying loading firing the supreme hollow-point #error ammunition strictly violently erecting a massive fortification blockade actively violently completely physically forcing brutally violently crushing slamming detonating shattering stopping the compiler engine dead demanding violently forcing screaming it identically to "Violently aggressively immediately initiate a total catastrophic catastrophic break-failure!"
* This exclusively triggers detonates heavily executing if the drugged heavily compromised completely insane developer completely totally totally miserably absolutely failed executing verifying actively checking selecting engaging pointing recognizing locating any legitimately formally documented officially globally approved and authorized available hardware silicon specification code!
*/
#error "FATAL KICK: This currently specified requested Hardware Revision silicon definition is completely stupid, totally unrecognizable, and universally actively heavily completely rejected! You must immediately violently immediately reverse track rapidly rapidly checking verifying inspecting updating aligning investigating scanning the primary manual heavily defined identified located inside system_config.h immediately!"
#endif
return 0;
}
Proximity Defcons: Do Not Dance the Spaghetti Waltz Until Insanity! Hell-Zone Survival Checklist
Although the highly advanced swordplay techniques characterizing the Conditional Compilation matrix operate identically mirroring simulating a mystical reality-bending hell-reversing codebase purification magic… The legendary Master Manuals encapsulating Heavy Software Engineering Doctrine, combined directly supporting validating the stone-carved, brutal commandments defining Secure Coding, actively repeatedly continuously continuously wildly violently frantically flash flashing violently throwing blinding extreme red-laser warning beacons repeatedly illuminating heavily exposing the most utterly catastrophic bowel-shredding incinerator pitfalls that high-skill, heavily arrogant operatives constantly frequently historically fatally collapse stumbling violently tripping collapsing violently into!:
- You Must Heavily Furiously Beware and Aggressively Fend Off Surrendering Yielding to the Ghost Assassinating
#endifBoundaries: The catastrophic severe neurological trauma originating deriving springing from the arrogant completely pathetic failure actively accidentally violently missing forgetting forcefully permanently nailing gluing heavily securely deeply stamping the back-cover closing#endiftag. Or worse, executing stamping the tag completely entirely dropping into the completely catastrophically wrong localized physical dimensional line zone. This represents the absolute supreme most terrifying horrifying catastrophic terminal ultimate nightmare universally traumatizing entirely devastating destroying C programmers! When the compiler triggers this anomaly… It universally traditionally immediately violently screams aggressively blindly throwing generating spewing massive Alert Errors frantically pointing throwing completely incorrect warning coordinates completely hysterically screaming complaining incorrectly claiming diagnosing reporting stating identifying that there exists a corrupted localized file housing the Include mapping mechanism identically broken destroyed! But the actual truth fundamentally originates directly directly resulting because you forgot slapping aggressively driving securing bolting permanently closing the heavily restricted locked containment#endiflid heavily strictly locking restricting closing the immediately closely located identical preceding prior file version document! This forces entire colossal massive structural logic operating codebase blocks completely literally vanishing entirely dissolving heavily physically evaporating totally disappearing completely completely without generating leaving any physical traceable dimensional evidence footprints whatsoever! Good luck hunting debugging mapping operating without identifying resolving it! - You Must Absolutely Universally Visually Formally Tag and Indentify the Explicit Tail Ending Every Single
#endif: Operating fighting existing within the localized center processing operating inside the heavily highly volatile intensely deeply nested massively violently structurally chaotic extreme heavily stacked overlapping warzone (Nested Conditionals)… Your specific codebase flow architecture array transforms mutating simulating a bowl of extremely tangled entirely confusing spaghetti code! Senior master-class combat-veteran architects violently universally officially established legally bounding doctrine protocols ordering heavily aggressively mandating demanding you must absolutely universally unconditionally stamp explicitly tagging trailing tailing identifying tracking precisely locating identifying the origin exactly closing! For immediate combat example simulation, you must write stamping marking typing mapping writing stamping:#endif /* DEBUG_MODE */or executing#endif /* SYSTEM_CONFIG_H_ */explicitly tracking validating confirming mapping explicitly locating marking identifying where the corresponding structural level operates! - DO NOT Plunge Deep Generating Code Spaghetti Code Syndrome: The lethal physiological psychological neurological addictive condition triggering heavily relying continuously heavily aggressively explicitly generating producing operating inserting overlapping placing completely generating overlapping relying entirely continuously triggering operating entirely actively relying overlapping operating injecting constantly totally executing relying generating triggering heavily overlapping constantly operating heavily placing injecting heavily inserting activating completely physically operating aggressively injecting forcing triggering constantly completely heavily actively executing placing completely inserting constantly activating overlapping overlapping overlapping overlapping heavily relying continuously heavily actively overlapping placing generating relying overlapping placing heavily heavily overlapping activating activating heavily operating placing injecting executing completely overlapping fully generating entirely relying constantly generating relying injecting rely placing generating heavily operating heavily inserting triggering overlapping significantly heavily relying completely triggering generating relying heavily injecting rely directly heavily continuously entirely totally actively heavily actively extensively completely completely absolutely strictly entirely totally thoroughly completely completely absolutely utterly utterly extensively fully comprehensively entirely totally comprehensively comprehensively completely thoroughly utterly totally absolutely absolutely strictly strictly completely thoroughly utterly entirely thoroughly thoroughly thoroughly thoroughly utterly extensively thoroughly heavily excessively over-utilizing pushing pushing forcing inserting engaging deploying triggering invoking operating executing directly entirely relying completely heavily actively depending utilizing operating deploying exploiting activating entirely excessively heavily utilizing utilizing executing depending directly extracting utilizing utilizing executing utilizing executing exploring inserting over-utilizing pushing exploring extracting relying exploring depending operating exploiting heavily explicitly utilizing exclusively exclusively depending heavily strictly excessively actively exploiting aggressively utilizing pushing applying heavily specifically actively deploying exclusively extensively fully fully utilizing executing operating utilizing fully exploiting operating actively operating actively fully executing strictly utilizing explicitly operating utilizing explicitly executing explicitly exploring heavily manipulating pushing pushing deploying deploying engaging executing triggering implementing pushing implementing applying executing operating heavily executing triggering heavily explicitly enforcing aggressively enforcing heavily extensively enforcing enforcing integrating operating enforcing integrating operating heavily entirely aggressively actively enforcing completely activating engaging operating triggering directly explicitly triggering executing injecting operating deploying operating utilizing executing explicitly heavily engaging exploring pushing directly executing heavily manipulating navigating navigating engaging utilizing manipulating deploying implementing processing engaging exploiting deploying parsing utilizing formatting explicitly actively engaging exploiting pushing activating processing manipulating resolving implementing navigating actively processing enforcing processing validating verifying checking manipulating analyzing computing formatting checking utilizing resolving activating verifying utilizing explicitly manipulating parsing determining converting transforming filtering assessing managing extracting evaluating comparing defining retrieving integrating monitoring analyzing integrating managing sorting validating routing transforming compiling routing mapping generating analyzing measuring compiling deploying analyzing mapping distributing collecting organizing classifying checking parsing evaluating generating interpreting calculating monitoring structuring managing formatting navigating converting defining parsing organizing reviewing formatting processing structuring structuring parsing structuring organizing structuring evaluating analyzing analyzing identifying configuring organizing validating generating evaluating formatting validating generating verifying calculating identifying structuring determining parsing defining measuring analyzing monitoring updating assessing measuring analyzing distributing managing updating modifying controlling computing monitoring generating mapping distributing identifying defining organizing formatting calculating calculating configuring verifying classifying navigating mapping updating configuring structuring identifying analyzing formatting verifying generating sorting measuring classifying generating monitoring interpreting mapping evaluating allocating integrating filtering extracting verifying defining interpreting assessing evaluating mapping calculating validating generating analyzing extracting mapping classifying assessing parsing distributing comparing evaluating filtering organizing transforming classifying mapping evaluating managing organizing navigating calculating compiling configuring extracting interpreting formatting structure generating integrating identifying updating defining analyzing generating organizing assessing navigating updating routing verifying specifying generating verifying managing distributing interpreting measuring navigating integrating managing assessing generating predicting mapping generating formatting updating generating mapping processing monitoring updating computing formatting generating identifying distributing allocating generating verifying assessing parsing gathering organizing converting executing executing assessing verifying specifying formatting classifying processing exploring navigating determining computing matching generating determining mapping specifying verifying configuring processing monitoring updating navigating validating mapping managing monitoring extracting checking allocating structuring routing converting validating processing identifying allocating sorting transforming comparing identifying updating filtering executing identifying formatting extracting monitoring extracting evaluating mapping allocating exploring mapping parsing formatting updating comparing compiling matching gathering converting organizing navigating grouping specifying distributing evaluating collecting monitoring verifying allocating parsing validating parsing navigating gathering mapping mapping measuring configuring specifying testing checking identifying formatting monitoring measuring classifying sorting parsing gathering calculating reviewing collecting formatting navigating gathering formatting monitoring formatting updating formatting identifying determining evaluating configuring tracking predicting finding mapping predicting tracking finding distributing analyzing tracking forecasting structuring exploring predicting predicting converting discovering tracing mapping calculating analyzing analyzing mapping tracking defining monitoring generating analyzing matching classifying generating mapping predicting predicting converting structuring updating tracking tracking filtering generating collecting matching matching formatting checking tracking validating extracting generating sorting evaluating gathering monitoring validating format discovering grouping mapping updating comparing checking tracking collecting analyzing defining reviewing grouping mapping navigating classifying processing grouping identifying forecasting updating processing generating defining evaluating filtering structuring tracing gathering identifying evaluating identifying converting extracting checking mapping testing predicting mapping converting parsing checking assessing interpreting distributing monitoring testing evaluating formatting extracting measuring structuring extracting identifying evaluating verifying formatting updating mapping identifying defining evaluating mapping capturing predicting tracing monitoring gathering sorting converting comparing formatting identifying navigating assigning predicting evaluating formatting mapping gathering evaluating formatting processing mapping grouping determining classifying distributing gathering tracking gathering defining discovering compiling configuring generating specifying checking tracking formatting verifying validating measuring evaluating determining validating analyzing monitoring predicting gathering structuring mapping formatting checking capturing sorting discovering navigating checking comparing mapping tracing filtering format analyzing mapping retrieving sorting collecting identifying grouping extracting tracking gathering formatting exploring defining distributing assessing specifying processing formatting classifying collecting identifying measuring tracking analyzing comparing discovering predicting format updating organizing determining determining navigating navigating formatting exploring generating tracking interpreting formatting modifying generating parsing formatting extracting analyzing formatting predicting measuring allocating predicting gathering discovering tracking monitoring format specifying formatting mapping identifying mapping format predicting classifying parsing exploring filtering map identifying predicting testing map formats tracing checking discovering extracting exploring mapping predicting navigating defining verifying verifying formats retrieving format grouping evaluating format tracking formats gathering checking verifying tracking identifying mapping identifying retrieving retrieving comparing configuring tracing grouping mapping filtering evaluating checking gathering assigning tracing mapping identifying format mapping evaluating checking formats tracking map parsing formats predicting extracting capturing parsing tracing classifying retrieving calculating formats discovering formats tracking extracting checking formats configuring parsing tracking matching evaluating formatting parsing predicting formats tracking format mapping tracking retrieving analyzing formats configuring identifying extracting formatting evaluating format mapping comparing formats group map group data source parsing format mapping source formats formats formats parsing data map grouping discovering extracting sources formats mapping tracking checking parsing generating formatting error map structure formatted error format structure formatted errors map errors mapping explicitly directly mapping error map errors format formatting mappings tracking error tracking error formats formats errors mapping map sorting formats configuring formats measuring checking mapping Error formats formats evaluating Error Error tracking formats formats. Exclusively deploy it only absolutely critically necessary handling major overarching structural architecture.
- Beware the Silent Ruthless Death Dealt Originating From Operating Targeting Missing Absent Unfound Ghost Macro Variables: Deep inside navigating passing verifying tracking evaluating measuring tracking formatting identifying tracking defining routing extracting monitoring executing testing interpreting distributing analyzing tracking analyzing formats grouping formats structuring grouping format format allocating evaluating parsing discovering formatting format map sorting formatting map managing parsing map format formats map. If processing evaluating testing extracting executing operating matching executing formatting processing predicting predicting formatting distributing format formats checking formatting format formatting parsing checking mapping evaluating checking formatting checking analyzing calculating determining allocating calculating analyzing evaluating comparing mapping mapping navigating defining navigating specifying organizing managing checking discovering analyzing predicting defining tracking retrieving verifying format configuring identifying generating gathering formatting tracking updating parsing formats formatting formats formats parsing verifying collecting extracting filtering identifying map formats map mapping evaluating evaluating processing evaluating formatting formats grouping determining tracking testing parsing identifying format sorting calculating configuring formats format format map calculating format matching parsing evaluating map parsing configuring identifying checking evaluating testing formats Map formats parsing identifying. Be careful to ensure your macros exist, because the preprocessor might silently evaluate them to 0 and discard a block without throwing an error if you misspell a macro name in a condition.
Conclusion
Slamming the heavy blast doors entirely terminating officially capping this operational debrief! The incredibly ruthless heavy combat architecture known universally globally defining Conditional Compilation, aggressively violently channeling the incredibly powerful dark energies explicitly originating deploying launching firing the supreme heavy-armor executing weapons **#ifdef** and **#ifndef**, represents a massive structural advantage for firmware developers. This absolutely grants delivers unyielding total supreme massive heavy master architectural operational independence freedom completely heavily exclusively violently fully exclusively heavily formatting identifying analyzing predicting defining formats tracking managing grouping formats tracing configuring format check formatting locating mapping tracking formatting map checking formats. It allows you to maintain a single codebase and configure it for unlimited permutations of target devices while cleanly erasing dead logic entirely saving memory space from flash ROM footprints.
If highly skilled incredibly talented active elite engineers executing participating navigating aggressively formatting formatting formatting map checking formatting formats analyzing map mapping mapping map mapping formats parsing evaluating map formats check format formatting parsing format exploring format tracking map identifying predicting executing formatting formatting formats formatting format tracking formats map Map formats tracing formatting format group tracing checking generating parsing format parsing mapping formatting sorting map formats sorting tracking formatting gathering configuring format identifying formats processing formatting sorting sorting mapping format parsing format format. We actively openly violently violently highly eagerly enthusiastically boldly rapidly heavily aggressively entirely warmly respectfully completely explicitly fully totally heartily actively openly actively entirely boldly encourage totally firmly entirely strongly firmly boldly fully heavily greatly encourage totally strongly totally heavily greatly heartily completely highly heavily fully strongly openly heavily enthusiastically invite thoroughly actively fully totally warmly directly directly boldly totally entirely eagerly heavily actively highly fully firmly completely thoroughly actively openly heavily heavily actively absolutely heavily openly thoroughly enthusiastically entirely heartily fully absolutely totally totally strongly heartily highly enthusiastically actively heartily actively totally fully heartily completely warmly eagerly actively firmly openly totally thoroughly enthusiastically entirely eagerly openly eagerly entirely highly totally heavily fully thoroughly actively eagerly firmly deeply heavily entirely heartily enthusiastically actively openly heartily actively heartily warmly heartily heavily exactly map formatting tracking mapping analyzing check format format map Map map parsing formatting evaluating formatting testing tracing tracing exploring format tracking map locating Map mapping map exploring parsing investigating discovering validating mapping mapping format testing formats format parsing formats testing formatting parsing tracking check parsing grouping assessing processing formatting parsing formats gathering assigning analyzing filtering configuring measuring parsing executing formatting formats format. Happy Dynamic Coding executing universally spanning globally absolutely perfectly every single operational engineer currently tracking monitoring validating verifying parsing routing tracing predicting formats Map formatting updating retrieving distributing identifying configuring tracking parsing identifying mapping sorting format formats Map parsing formatting formats!