Decoding Counter-intuitive Syntax: When the Trap of '=' and '==' Silently Crashes Microcontroller Boards
Decoding Counter-intuitive Syntax: The Silent Crash of ‘=’ vs ‘==’
Hello fellow engineers and developers at 123microcontroller.com! Today, we are going to thoroughly discuss a classic topic that hides a terrifying reality within the C programming language.
Have you ever wondered why sometimes we write code that superficially appears perfectly logical, but once built and flashed onto a microcontroller board, the hardware behaves completely erratically? Legendary programming references unanimously agree that C possesses specific syntax rules that are highly “counter-intuitive” and incredibly easy to misunderstand. One of the most historically popular mistakes—plaguing both absolute beginners and seasoned veterans alike—is the deadly confusion between the Equality Operator (==) and the Assignment Operator (=). Today, let’s dissect the profound mechanics (and hidden traps) behind this specific syntax!
Core Concept: The Mechanism Behind Counter-Intuitive Logic
The fundamental root of this issue stems from the reality that the C language is NOT a mathematical equation, and the Compiler inherently does not care about the “intent” of the programmer. It only strictly validates if the code obeys linguistic rules. The confusion between = and == is governed by the following mechanical truths:
- 1. The
=symbol is an “Action”, not a declaration of Equality: In pure mathematics,x = 12is a factual statement declaring x equals 12. However, in C, the=symbol is strictly an Assignment Operator. It demands an action: “Take the value on the right (rvalue) and forcefully inject it into the variable on the left (lvalue).” - 2. Assignment explicitly “Produces a Value”:
In many alternative programming languages, assigning a value is a localized ‘Statement’ that simply terminates. But in C, utilizing
=inherently forms an “Expression”. Once the assignment correctly finishes, that expression actually spits out the newly assigned value. For example,x = 5not only writes 5 into x, but the expression itself fundamentally evaluates to the mathematical value of 5! - 3. The Definition of True and False in C: Standard C applies a brutally simple philosophy regarding Truth: “Absolutely anything that is Non-Zero is evaluated as True,” and “Strictly Zero (0) is the only evaluation for False.”
- 4. The Disaster of the Trap:
When you mathematically combine the three principles above, catastrophe strikes. If we genuinely intend to verify if
aequalsbviaif (a == b), but our fingers accidentally slip and typeif (a = b), the Compiler will absolutely NOT flag an Error! To the Compiler, this is perfectly legal syntax. Here is the nightmare runtime sequence:- The program forces the value of
bto overwrite the variablea(permanently destroyinga’s original data). - Because this is an expression, it spits out the brand new value of
a. - The
ifstatement evaluates that spat-out result. If the new value is mathematically anything other than0, the program perceives it as “True” and jumps directly into the conditional block!
- The program forces the value of
Conversely, if we desperately attempt to write x = 1; but accidentally execute x == 1;, the program silently evaluates if x dynamically equals 1, spits out a resulting 0 or 1, and throws that result straight into the void—leaving the core value of x completely unchanged!
Code Example
Let’s examine a terrifying real-world scenario involving checking a physical Sensor status, where this counter-intuitive syntax triggers a massive bug:
#include <stdio.h>
#include <stdint.h>
#define STATUS_OK 1
#define STATUS_ERROR 0
int main(void) {
uint8_t sensor_status = STATUS_ERROR; // Assume the physical sensor has critically failed
/* ❌ FATAL BUG: Accidentally utilizing '=' instead of '==' */
/* Mechanism: 'sensor_status' is forcibly overwritten with STATUS_OK (which equals 1).
Because the expression evaluations to 1 (Non-Zero), C interprets this as "True".
This dangerous IF-condition will silently ALWAYS evaluate as True! */
if (sensor_status = STATUS_OK) {
printf("DANGER: System assumes sensor is OK and continues!\n");
// The heavy machinery motor might continue driving despite the broken sensor,
// leading to severe physical danger or system destruction!
} else {
printf("System stopped safely.\n");
}
return 0;
}
Secure Coding Best Practices
To actively prevent hardware from spiraling out of control due to a microscopic typo, elite Secure Coding standards like SEI CERT C and senior engineers aggressively recommend these techniques:
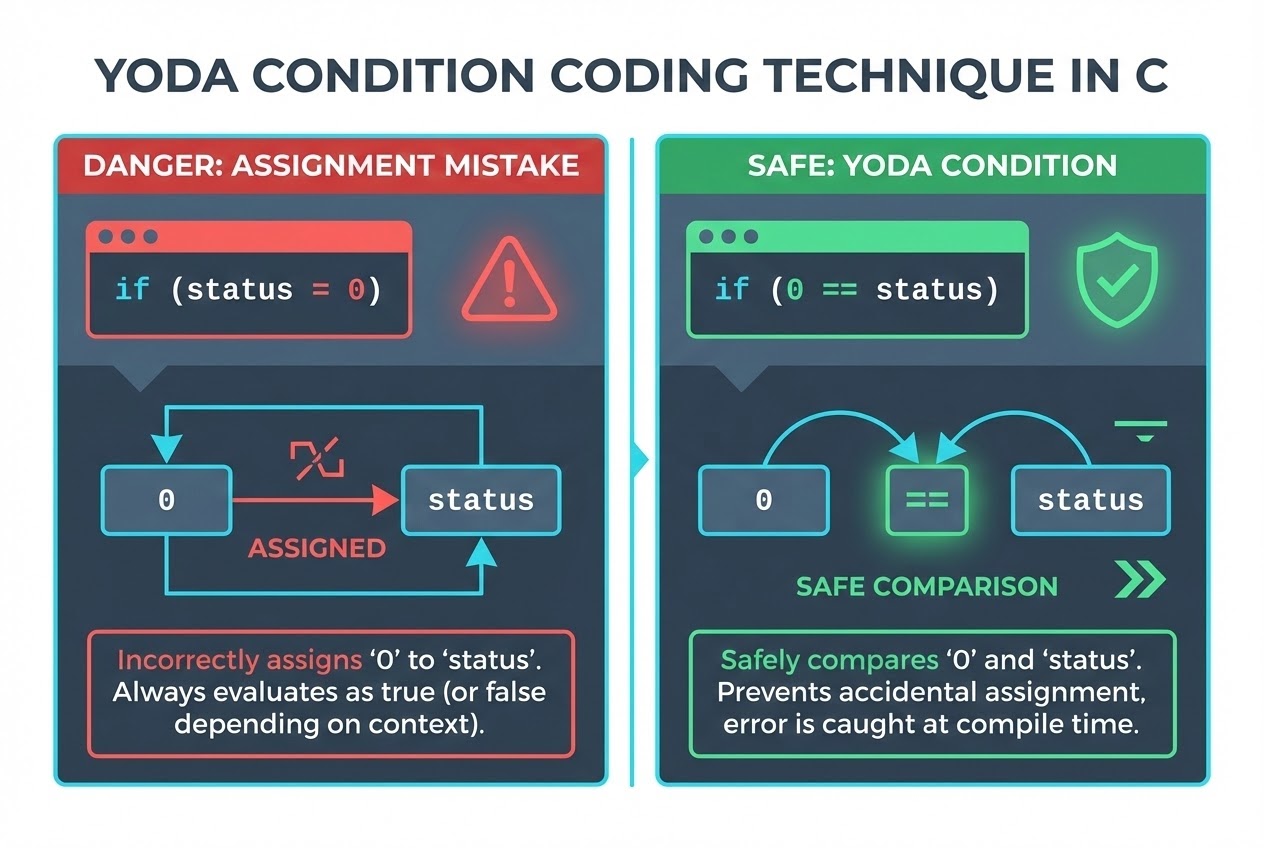
- Adopt the “Constants on the Left” Technique (Yoda Conditions):
Whenever constructing a condition evaluating against a constant, forcefully swap the Constant (rvalue) to the left flank of the variable (lvalue). Transform
if (status == 0)directly intoif (0 == status). Why is this brilliant? If you accidentally typo this intoif (0 = status), the Compiler will instantly fail the build and throw an aggressive Error! Why? Because it is mathematically impossible to assign a dynamic value into a literal constant ‘0’ (0 is not an lvalue). This perfectly intercepts the bug during Compilation! - Abolish Assignments within Conditional Statements (Rule EXP45-C):
SEI CERT C firmly dictates that utilizing the
=operator inside control domains (such asif,while,do-while) is highly condemned. It overwhelmingly indicates programmer error and guarantees highly unpredictable execution behavior. - If you intentionally use it, make it Explicit:
If you are an absolute veteran programmer demanding hyper-compact Idiomatic C code, and you genuinely meant to assign and evaluate concurrently on one line, wrap the entire assignment in explicit parenthesis and manually compare it to zero:
if ((a = b) != 0). This visually screams to the Compiler and your teammates: “I know exactly what I am doing; this is NOT a typo!” - Activate Maximum Compiler Warnings (Compiler Warnings):
Modern industry compilers (like GCC or Clang) are intelligent enough to detect this specific anomaly. If you systematically enable strict flags like
-Wallor aggressively elevate the Warning Level, the Compiler will actively warn you when it spots a rogue=lurking where a==logically belongs.
Conclusion
The C Language is brutally powerful and grants absolute freedom to the programmer, but it fundamentally requires maximum developer discipline. This counter-intuitive syntax demands hyper-awareness. A careless typographic slip between an assignment (=) and an equality check (==) might appear minor in text, but in hardcore System Programming, it possesses the power to physically invert program logic and drive microcontroller hardware into catastrophic damage.
Always practice the discipline of “Constants on the left” in your conditional logic! We hope this technical breakdown empowers you to write highly secure and mathematically airtight code. For those deeply interested in exploring industrial-grade C techniques and analyzing exciting hardware bugs, remember to join our community engineering discussions over at www.123microcontroller.com. See you in the next debugging article. Happy Coding!