Arrays: The Alpha of Data Structures and the Absolute Foundation of Hardware Engineering
Introduction: The First Architectural Building Block
Hello engineers and fellow developers at www.123microcontroller.com! Today, the dark-eyed engineer is taking you backward in time to the absolute most basic, yet structurally paramount piece of programming real estate: Arrays.
Often when learning C programming, students classify the Array simply as “a variable that cleanly holds multiple values.” However, deep in the brutal trenches of System Programming, the Array is classified as the actual First Data Structure. It is the elemental silicon Lego brick from which virtually all advanced structures—like Stacks, Queues, Hash Tables, and Heaps—are constructed. Let’s delve aggressively into how master-level architecture references view the Array mathematically, and why it is the reigning king of the hardware realm.
Understanding the True Geometry of an Array
If traversing standard application RAM is like walking through scattered, disorganized storage lockers, then an Array is a hyper-efficient sector completely dedicated to sequentially interlocked storage bays. Advanced architecture outlines its distinct identity as follows:
- 1. The Pinnacle Linear Data Structure: Arrays are rigidly classified as a Linear Data Structure, dictating an unyielding Sequential Order. Bare-metal hardware CPU caches absolutely adore this structure! Because the bytes are packed in “Contiguous memory locations”, the CPU’s memory management unit can autonomously “Prefetch” huge sweeps of an Array into its L1 cache with maximum predictive efficiency.
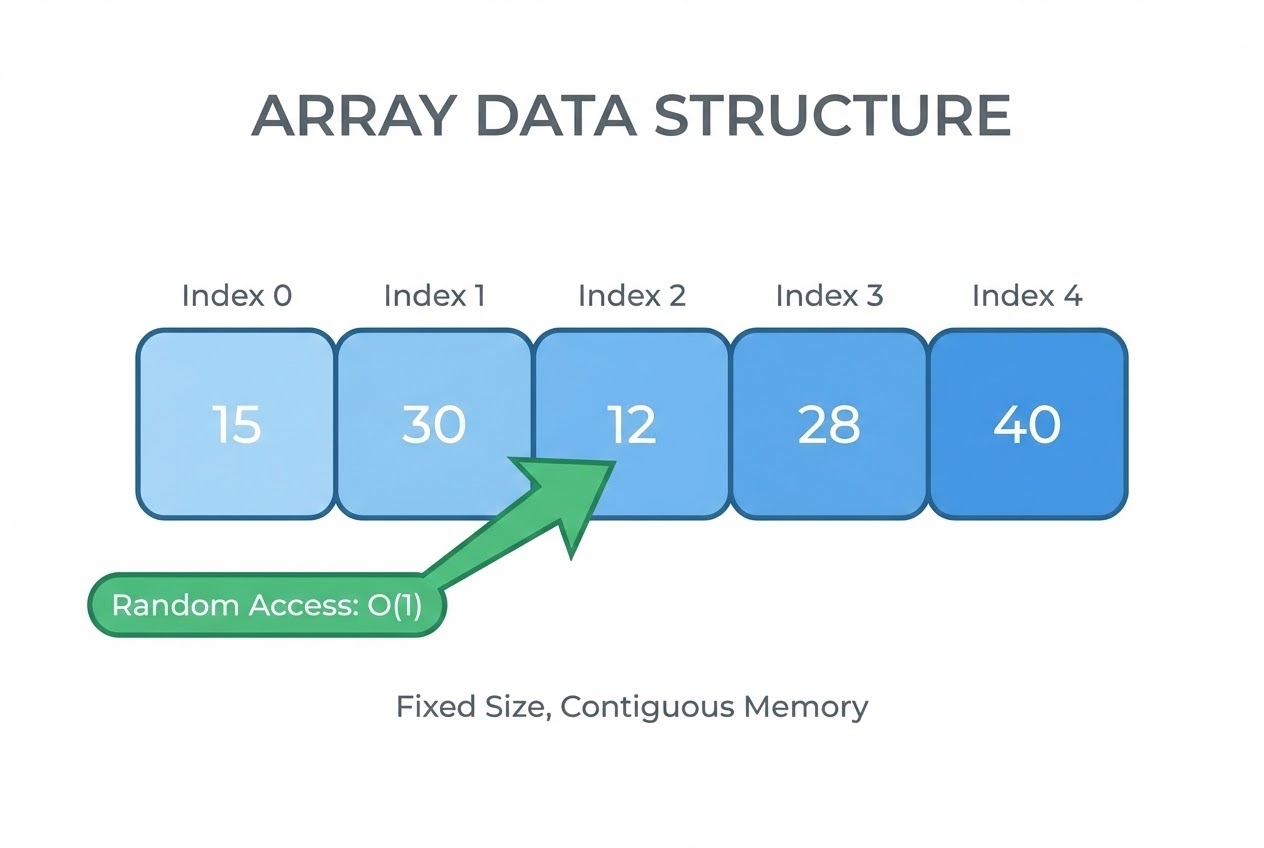
- 2. Astronomical Random Access (O(1)):
This is the apocalyptic superpower of the Array! Because elements are “Homogeneous” (all exactly the same datatype size), the compiler mathematically deduces instantaneous address lookups. Requesting
arr[x]allows the architecture to vault directly to that specific RAM address without skipping a beat, netting an absolute time complexity of O(1). Linked Lists, by terrifying contrast, force you to walk every consecutive node sequentially (O(n)). - 3. The Universal Building Block:
Arrays aren’t just for warehousing raw telemetry. They act as the physical terra firma upon which other Data Structures are built. An Array is weaponized to establish a Stack (LIFO logic), a Queue (FIFO logic), exceptionally fast Hash Tables (acting as the bucket arrays), and literally every String (which natively is just a
charArray wrapped with a null terminator). - 4. Arrays of Structures (The Nano-Database): Constrained embedded projects frequently demand complex relational logs (e.g., matching timestamps with temperatures and distinct sensor IDs). Declaring Arrays of Structures directly merges the architectural speed of the Array with the heterogeneous data mapping of a Struct. The result is a terrifyingly fast, self-contained mini-database sitting directly in pure RAM cache.
- 5. The Inevitable Trade-offs: The catastrophic weakness of the Array is its severe “Fixed Size”. Declaring an Array bolts its footprint permanently into the architecture. Declaring it too heavily results in permanent “Wasted space”. Declaring it identically small results in fatal data clipping. Furthermore, inserting or deleting an entry dead in the middle of an Array implies an atrocious computational cost of O(n), as the hardware is forced to mechanically Shift every trailing element to open a void.
Code Example: Engineering a Stack atop an Array
Let’s dissect deploying an Array of Structures to architect a LIFO Stack tailored to securely warehouse Sensor Logs in a microcontroller. This represents extreme Clean Code utilizing rigid, predictable memory logic.
#include <stdio.h>
#include <stdint.h>
#include <stdbool.h>
#define MAX_LOG_ENTRIES 100 // Hardcoded capacity to ruthlessly avoid malloc()
/* Architecting the isolated 1-Record Data Structure */
typedef struct {
uint32_t timestamp;
float temperature;
uint8_t sensor_id;
} SensorLog;
/*
* Establishing the Array of Structures (The Linear Framework)
* The index variable is weaponized to act precisely as our Stack Pointer.
*/
static SensorLog log_database[MAX_LOG_ENTRIES];
static uint16_t log_count = 0;
/* Secure function to execute a Push Operation into the Array */
bool add_sensor_log(uint32_t time, float temp, uint8_t id) {
/* 🛡️ Iron-clad Bounds Checking to ruthlessly reject Buffer Overflows */
if (log_count < MAX_LOG_ENTRIES) {
log_database[log_count].timestamp = time;
log_database[log_count].temperature = temp;
log_database[log_count].sensor_id = id;
log_count++; // Increment our logical Stack Pointer
return true; // Execution successful
}
printf("CRITICAL ALARM: Log Database is FULL!\n");
return false; // Execution denied: Capacity breached
}
int main(void) {
add_sensor_log(1005, 25.4f, 1);
add_sensor_log(1006, 26.1f, 2);
printf("Total logs recorded: %d\n", log_count);
return 0;
}
Maximum Security Protocols When Handling Arrays
Deploying Arrays demands fanatical discipline. Ensure you abide absolutely to these rigorous Secure Coding countermeasures:
- The Silent Reaper - Buffer Overflows: The C programming language implicitly assumes total developer competence—meaning it enforces Zero array bounds checking. Writing data into
array[105]on an Array sized 100 compiles identically fine, but violently overwrites adjoining RAM addresses causing sporadic board crashing (or highly destructive CWE-119 vulnerability vectors). You are architecturally obligated to hard-code explicit Bounds Checks prior to every Array mutation. - Beware the “Array Decay” Illusion: Passing an initialized Array into a sub-function (
void process_data(int arr[])) is a visual lie. The compiler inherently destroys the Array context, passing only a Pointer referencing the first element (transforming it intoint *arr). Executingsizeof(arr) / sizeof(arr[0])inside the targeted function evaluates completely wrong, resolving the sheer size of the Pointer itself! Always mechanically pass the actualsize_tscalar as an accompanying secondary parameter. - Prohibiting Variable-Length Arrays (VLA): Although modern C99 technically sanctions Arrays dynamically sized by runtime variables (VLAs), engaging them on embedded firmware is highly toxic. It practically weaponizes your Stack, provoking massive Stack Overflow crashes. Universally revert to executing rigidly declared Static / Constant-Length Arrays to acquire absolute deterministic stability.
Conclusion
Stepping back into the macro view, Arrays transcend superficial syntax. They are the supreme Linear Data Structure delivering an unparalleled O(1) execution velocity while completely harmonizing with hardware memory topologies. Though cursed with an utterly immovable Fixed Size, in the domain of Embedded Systems, that rigid boundary is secretly the god-tier weapon that grants us 100% Deterministic and secure RAM tracking!
Hopefully, this piece comprehensively illuminates the severe low-level tactical importance of Arrays. If you are captivated by hacking Array access timing or optimizing RAM pipelines, infiltrate the discussions scaling up on www.123microcontroller.com! Catch you in the next framework breakdown. Happy Coding!