Synchronization (Mutexes & Semaphores): Forging Multitasking Discipline & Halting Data Train Wrecks in the Embedded Realm
Introduction: The Multitasking Combat Grid
Greetings, elite engineers and hardcore developers aggressively defending the www.123microcontroller.com grid! The dark-eyed engineer has securely logged back into the terminal.
When our operational payloads scale out of simplistic single-loops and violently breach the absolute hardcore domain of Multitasking and RTOS (Real-Time Operating Systems), code that previously functioned flawlessly can instantaneously detonate! This catastrophic failure executes the exact millisecond multiple independent Threads violently collide, aggressively fighting to hijack identical Shared Resources! Elite global architects explicitly warn: Authorizing unregulated, chaotic multi-thread assaults upon identical memory vectors or hardware registers guarantees an absolute atomic disaster classified as a “Race Condition”!
Deploying heavy countermeasures mitigating this exact threat requires mastering the brutal art of Synchronization! Today, we are violently summoning the two legendary absolute heroes dominating this battlefield: The Mutex and the Semaphore! We will dissect their mechanical differences and weaponize them to permanently shield our active architecture! Initiate the launch sequence!
Core Concept: The Queue Wardens & The Critical Section
Inside the massive architecture of Multitasking, whenever we identify a specific block of code or a physical resource actively besieged by multiple threads (e.g., Global variables, Memory buffers, or raw Hardware Registers), we classify this highly volatile combat zone as a “Critical Section”! If the OS authorizes two independent Threads to violently breach the Critical Section attempting simultaneous data overwrites, a catastrophic Race Condition instantly corrupts the payload! The system deploys specific heavy mechanical tools enforcing absolute discipline:
- 1. Mutex (Mutual Exclusion) - The Absolute Security Key
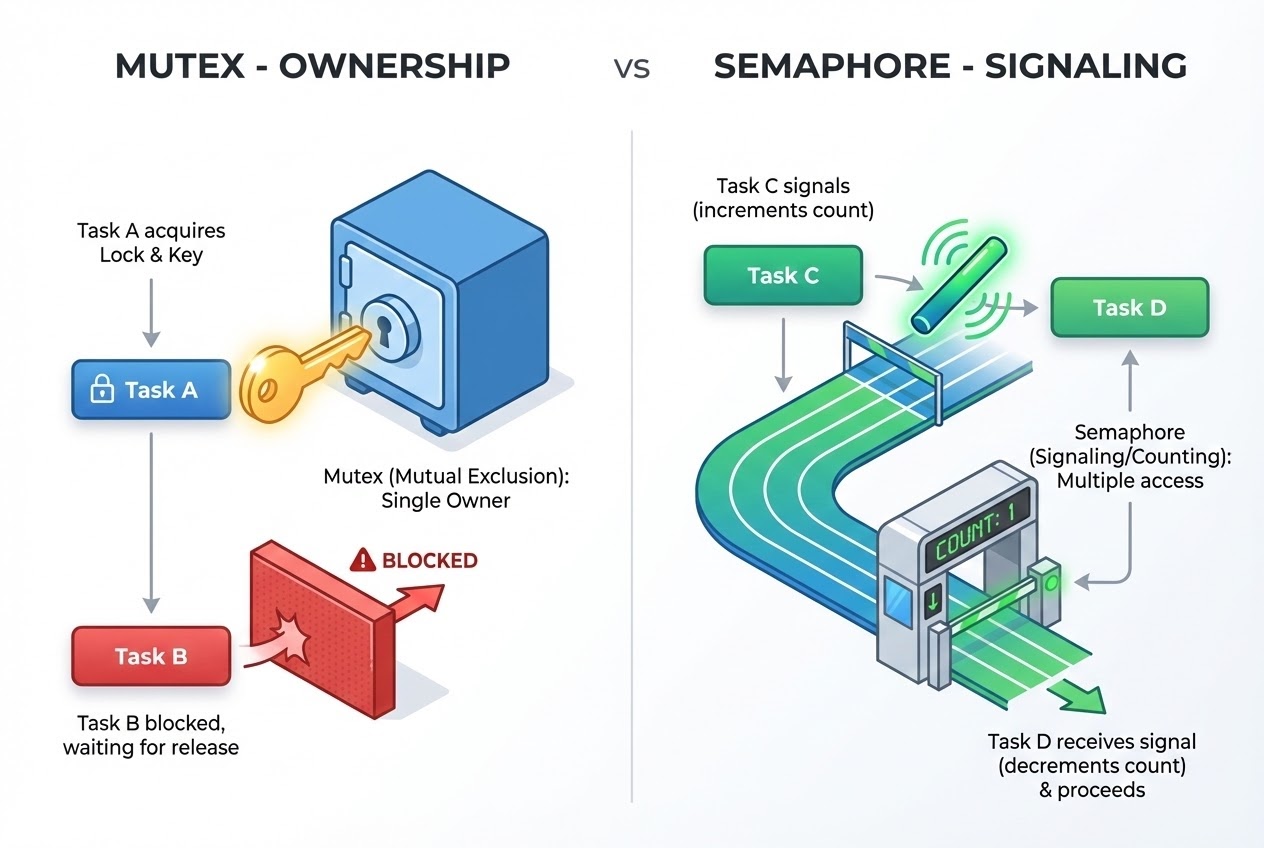
- The Prime Directive: Global experts frequently compare the Mutex to a “Solitary Public Vault Key.” When an active Task violently demands the physical resource (enters the vault), it must aggressively “Lock” this exact key! If any hostile Task concurrently attempts a breach, the OS violently Blocks them! The hostile Task is forced into a frozen suspension state until the primary Task securely terminates its operation and “Unlocks” releasing the key back to the grid!
- Absolute Ownership: The absolute ironclad Law of Mutex: “The Operative who Locked it, MUST meticulously Unlock it!” The specific Thread executing the Lock achieves absolute “Owner” status, hoarding extreme control until it voluntarily triggers the Unlock command!
- Tactical Objective: Exclusively deployed to aggressively shield a single Critical Section, absolutely annihilating the possibility of concurrent hostile interference!
- 2. Semaphore - The Relay Baton & The Payload Counter
- The Prime Directive: A Semaphore is mechanically a raw Integer variable aggressively weaponized entirely to count available hardware resources or fire massive coordination Signals (Signaling) across the entire system matrix!
- Counting Semaphore: Imagine an architecture possessing multiple identical physical vaults and multiple identical keys. The variable aggressively counts exactly how many keys remain! When a Task successfully breaches the vault, it violently decrements the counter (Wait/Decrement). Once the operation terminates, it actively increments releasing the key backing into the grid (Signal/Post/Increment). When the counter hits absolute zero, incoming Tasks are violently blocked!
- Binary Semaphore: Constrained strictly to values of 0 or 1! Mechanically similar to a Mutex, BUT wielding one absolutely massive difference: Semaphores possess ZERO concept of “Ownership”! One specific Thread can aggressively execute the Wait command (locking it), while a totally different, fully independent Thread executes the Signal command (unlocking it)!
- Tactical Objective: Massively deployed for cross-thread “Signaling”! Visually identical to a violent relay race passing the baton: Task A might sleep frozen, aggressively awaiting a Signal detonated by Task B or an active Interrupt Service Routine (ISR) screaming that fresh payload data just hit the grid, violently waking Task A to execute!
Firing Live Code Rounds: The Mutex Lockdown
To visually acquire this target, we are deploying a hyper-classic simulation weaponizing a Mutex utilizing the native Pthreads C library! We are aggressively locking down a math operation verifying absolute protection against horrific Race Conditions! (Clean Code, System-Level Architecture).
#include <stdio.h>
#include <stdlib.h>
#include <unistd.h>
#include <pthread.h>
/* Forging the heavy Mutex variable safeguarding the Critical Section! */
pthread_mutex_t my_mutex;
/* Shared Resources (The highly volatile combat zone) */
int shared_a = 5;
int shared_b = 7;
/* Targeted Worker Thread Payload Execution */
void* process_shared_data(void* arg) {
/* 🛡️ BREACHING THE CRITICAL SECTION: Aggressively requesting the Mutex Lock! */
/* If a hostile Thread already holds this lock, THIS Thread violently freezes (Blocks) entirely hitting a solid wall here! */
pthread_mutex_lock(&my_mutex);
/* === INSIDE THE BLAST SHIELD (100% SECURE CRITICAL SECTION) === */
shared_a = shared_a + 3;
shared_b = shared_b - 1;
printf("Access Granted [SECURE]: a = %d, b = %d\n", shared_a, shared_b);
/* Simulating a heavy hardware processing delay payload */
sleep(1);
/* 🛡️ OPERATION SUCCESSFUL: Executing Unlock restoring the physical key back to the system grid! */
pthread_mutex_unlock(&my_mutex);
/* ============================================================== */
return NULL;
}
int main(void) {
pthread_t t1, t2;
/* 1. IGNITE: Initializing the Mutex architecture */
pthread_mutex_init(&my_mutex, NULL);
/* 2. Deploying multiple Thread operatives assaulting the identical function simultaneously! */
pthread_create(&t1, NULL, process_shared_data, NULL);
pthread_create(&t2, NULL, process_shared_data, NULL);
/* 3. Aggressively awaiting the absolute termination of all deployed Threads */
pthread_join(t1, NULL);
pthread_join(t2, NULL);
/* 4. DESTROY: Violently obliterating the Mutex flushing resources back to the OS */
pthread_mutex_destroy(&my_mutex);
return 0;
}
Proximity Defcons: Heavy Best Practices & Fatal Pitfalls
Weaponizing Synchronization mechanics brilliantly preserves data integrity, however, it represents a lethal double-edged sword demanding extreme caution:
- The Phantom Menace - Deadlock (The Infinite Freeze): This absolute catastrophe detonates when Task A violently locks Mutex-1, aggressively demanding Mutex-2. Simultaneously, Task B already successfully locked Mutex-2, and aggressively demands Mutex-1! Both combatants hold the opposing keys hostage, violently refusing to yield! The system completely flatlines permanently! The Countermeasure: You MUST design architectures forcing all Tasks to systematically acquire multiple Mutexes strictly following an absolute “Predefined Sequence” permanently destroying Circular Wait loops!
- The Silent Assassin - Priority Inversion: The most legendary aerospace catastrophic bug in human history (e.g., the Mars Pathfinder anomaly)! This detonates when an absolute garbage Low-Priority Task violently hijacks a Mutex. Suddenly, the absolute Maximum-Priority Task demands that exact Mutex, forcing it to violently freeze! Even worse: an irrelevant Medium-Priority Task spawns, violently hijacking the CPU from the Low Task (bypassing the Mutex entirely)! Result: The Maximum-Priority Task rots waiting forever! The Countermeasure: You MUST deploy heavy OS features like Priority Inheritance!
- Compress the Critical Section (The Violent Bottleneck): Grandmasters aggressively warn that a Mutex is physically a massive system “Bottleneck”! Hoarding a Mutex for agonizing durations (e.g., executing massive
delay()commands while locked) will violently annihilate your Multithreading parallel efficiency! You MUST: Lock, violently grab/modify the data, and instantaneously Unlock! - NEVER Deploy Mutex Locks inside an ISR: If a violent Hardware Interrupt detonates, and the ISR code aggressively attempts calling
mutex_lock()exactly targeting a Mutex actively hoarded by the heavily interrupted Thread… your entire system detonates into an absolute Deadlock instantaneously! Inside an ISR, you are ONLY authorized to deploy Non-blocking commands, specifically firing asemaphore_signal()violently waking secondary Tasks handling the heavy lifting!
Conclusion
In the absolute hardcore realm of Embedded Multitasking, Synchronization mechanics operate as the unquestioned burning core! A Mutex is forged exclusively to shield physical resources enforcing “Temporary Extreme Ownership”, whereas a Semaphore represents the ultimate “Counter and Signaling Device” aggressively coordinating cross-Task execution or violently catching baton-passes direct from Hardware Interrupts! Distinguishing exactly when to deploy these two weapons separates amateur rookies from elite hardcore professionals!
If any operatives operating on the server have ever completely bricked an entire RTOS architecture suffering a catastrophic Deadlock, or successfully engineered highly classified data transfer protocols bridging ISRs and Tasks… blast a flare and upload your intel straight onto our active combat grid at www.123microcontroller.com! Maintain heavy shields, Happy Hardcore Coding to absolutely every operative!