Preprocessing: Uncovering the First Frontier of the Translation Process, the Robot Typist Behind C Compilation
Introduction: Breaching the Compiler’s Frontline Defenses
Greetings, elite engineers and hardcore developers aggressively defending the www.123microcontroller.com grid! The dark-eyed engineer has securely logged back into the terminal. Today, we drastically expand our tactical radar to intercept and decode exactly what violently occurs “behind the scenes” the absolute microsecond we smash the Build button or execute the primary compile command.
Many rookies operating in the field operate under the naive assumption that our raw C source code is fired directly, point-blank into the Compiler’s core engine to be instantly translated into pure machine execution logic. However, plunging into the brutal reality of the global C language treaty, the architecture enforces a massive, multi-staged gauntlet officially classified as the Translation Process. This heavily fortified sequence splinters into multiple excruciating sub-phases. The absolute crucial “first frontier”—the vanguard meatgrinder our code must survive—is Preprocessing. Today, we aggressively tear into the Master Engineering Grimoires to expose the hyper-violent role of Preprocessing operating within the massive overarching architecture of the Translation Process. Secure your terminals, let’s breach the frontline!
Core Theory Autopsy: The Translation Process & The Preprocessor’s Ruthless Role
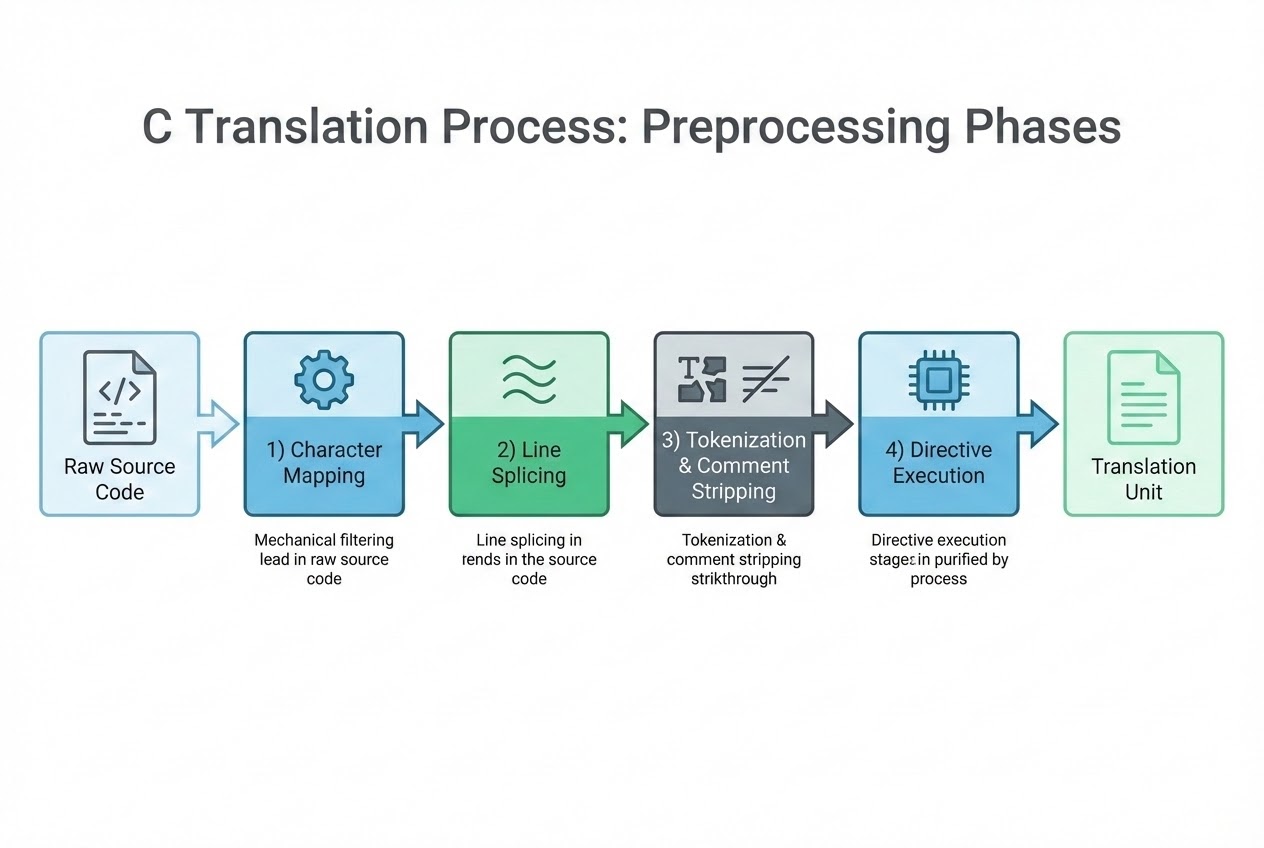
Scanning the structural blueprints defining the translation gauntlet, command documentation explicitly mandates this operation runs heavily staggered across 8 continuous, sequential phases. Preprocessing exclusively dominates and absolutely controls the opening 4 phases of this chaotic theater, operating entirely before any sanitized code is ever handed over to the actual Compiler engine (waiting deep within Phase 7).
Visualize the Preprocessor as a heavily armed “Specialized Text Editor Drone”—a rogue automaton whose singular, bloody directive is to ruthlessly format, slash, and modify the raw text within our source files strictly executing our embedded commands. It prepares a completely sanitized, pure manuscript before delivering it to the heavy construction Compiler. This autonomous drone violently executes its programming across 4 distinct tactical phases (Phases 1-4):
- Phase 1: Character Mapping (The Initialization Protocol): The raw source code we key into the terminal is aggressively stripped and converted into an absolute standardized character matrix the internal system natively understands. In ancient, legacy operations, this phase also deployed protocols hunting down and terminating weird, arcane character combinations called Trigraphs, forcefully ripping them into standard operational syntax (e.g., violently transmuting
??=into a clean#). - Phase 2: Line Splicing (The Gravity Crush): If an engineer deploys massive, elongated code structures and strategically drops a Backslash (
\) violently fused with a Newline, the Preprocessor drone engages a gravity crush. It permanently “annihilates” both the\and the hard Newline, screaming crushing the fragmented text, surgically logically welding the code back into a single, massive, continuous attack vector. - Phase 3: Tokenization & Comment Stripping (The Purge): The code structure is brutally hacked and chopped into isolated, micro-atomic logic chunks officially designated as “Tokens” (variables, heavy operators). The absolute critical maneuver here is The Purge: Every single human-readable comment (
/* ... */or//) is violently targeted, completely eradicated, and permanently wiped from existence. The drone brutally overwrites their graves with a single, sterile, microscopic space character. - Phase 4: Directive Execution (The Main Payload): This is the nuclear core of the operation! The drone actively scans the perimeter hunting for any high-priority commands stamped with a leading
#(e.g.,#include,#define,#ifdef). Upon acquiring a lock, it violently executes the payloads: aggressively hijacking and ripping alien files directly into the active matrix, detonating massive text substitutions (Macro expansion), or surgically severing and permanently deleting entire code blocks executing heavy Conditional Compilation strikes. Once the payloads detonate and the commands are fully executed, the physical lines housing these#directives are permanently vaporized!
The Final Tactical Result?
Surviving the absolute chaos of Phase 4, we successfully extract the highly valuable “Translation Unit” (frequently tagged carrying the .i extension). This artifact is pure, absolutely unadulterated, raw C source code—completely sterilized containing zero comments, zero remaining # directives, and harboring fully detonated, fully expanded Macros! This incredibly pure Translation Unit is the exact payload physically handed directly over to the main Compiler engine to commence heavy Syntax analysis and launch the final translation drop into pure, lethal machine instructions.
Firing Live Code Rounds: From Raw Source to Pure Translation Unit
Let us visibly trace the combat path, observing exactly how this robotic Preprocessor drone violently mutates the physical architecture of our code surviving the initial 4 gauntlet phases.
The Raw Blueprint (main.c pre-drop):
#include "my_hardware.h" /* 1. Tactical File Hijack (Phase 4) */
/* 2. Forging a Heavy Macro deploying the Gravity Crush (Phase 2 & 4) */
#define SETUP_LED() \
PORTB |= 0x01; \
DDRB |= 0x01;
int main(void) {
// 3. This human intelligence data will be violently purged (Phase 3)
int a = 10;
SETUP_LED(); /* 4. This payload will violently detonate and expand (Phase 4) */
return 0;
}
The Extracted Artifact (The pure Translation Unit pushed to Phase 7 Compiler):
extern void hw_init(void); /* Simulating the violently extracted payload completely ripped from my_hardware.h */
int main(void) {
int a = 10;
PORTB |= 0x01; DDRB |= 0x01;;
return 0;
}
Visual Confirmation: The human intelligence warnings (comments) are annihilated, the # command vectors are vaporized, and SETUP_LED() has violently detonated spreading into standard heavy C payload logic. This incredibly sterilized environment is exactly what the Compiler’s targeting scanner actually locks onto!
Proximity Defcons: Heavy Best Practices & Fatal Pitfalls
Absolutely locking down the understanding that Preprocessing operates strictly as a blind, ignorant “Textual substitution drone” detonating “before” any intelligent Compiler logic engages is the ultimate survival tactic preventing horrific, catastrophic software meltdowns. Elite heavy-tier sources and global Secure Coding Standards (CERT C) scream firing bright red warning lasers projecting these critical hazards:
- Total Lack of Semantic Intelligence (The Blind Destroyer): The Preprocessor drone possesses absolutely zero intellectual comprehension regarding Data Types, variable tracking, functional geometry, or Scopes. It operates purely as a blind, violent text string assassin. If you carelessly forge a syntactically broken, totally illegal Macro, the Preprocessor will blindly approve the drop, passing it directly through the gates! However, the Phase 7 Compiler engine will violently choke on the garbage, screaming throwing massive Fatal Errors! These errors will horribly, identically point straight back at the line invoking the Macro, creating a heavily obfuscated crime scene making Debugging incredibly agonizing!
- Beware the Macro Side-Effect Suicide Bomb (CERT C Rule PRE31-C): When aggressively ramming live variables straight into a Macro payload like
MACRO(x++), you must remember this is a raw, violent copy-paste injection! If the Macro internal logic referencesxacross multiple sectors (e.g., executing a Max/Min combat evaluation), the variablexwill physically detonate incrementing (++) multiple consecutive times (Multiple evaluation chaos)! This triggers completely untraceable, manic, psychotic program behavior destroying the system entirely (Undefined behavior)! Modern C warfare doctrine heavily universally mandates deployinginlinefunctions prioritizing overriding this extreme hazard! - The Token Pasting Catastrophe (
##): Choosing to detonate the##operator deep within Phase 4, attempting to violently smash and weld two independent Tokens permanently together (Token concatenation), carries severe legal restrictions. The resulting welded monstrosity MUST explicitly form a completely valid, legally recognized C Token (e.g., forging a legal, functional new variable tag). If the violent fusion results in creating an illegal, bizarre alien Token, it instantly triggers a catastrophic global Undefined Behavior event (strictly governed by rule PRE32-C).
Conclusion
Stepping back scanning the massive, overarching theater defining the Translation Process, the Preprocessing operation acts aggressively as the absolute frontline vanguard. It serves as the primary brute-force mechanism, violently transmuting raw chaotic source code, hacking open alien files, ruthlessly purging human comments, and detonating heavy macro payloads to forge a terrifyingly pure, sanitized Translation Unit feeding the hungry Compiler! Gaining total absolute mastery dominating this structural hierarchy grants hardcore Embedded engineers the lethal authority effectively wielding #define and #ifdef payloads! This tactical superiority empowers us aggressively controlling heavy multi-hardware build arrays operating securely with absolutely flawless precision!
If you are craving deploying advanced conditional compilation stealth tricks, hacking vendor compilers violently deploying the #pragma backdoor protocol, or simply desire screaming sharing horrific war stories surviving Macro suicide bombs… hit the hyper-link dropping directly into our active combat forum at www.123microcontroller.com to continue the intense debriefing. Keep your shields permanently raised, Happy Hardcore Coding to absolutely every operative!