Linker Scripts: The Memory Architecture Blueprint, The Final Lethal Shard of the Translation Process
Introduction: Deploying the Final Hardware Blueprint
Greetings, elite engineers and hardcore developers aggressively defending the www.123microcontroller.com grid! The dark-eyed engineer has securely logged back into the terminal. Today, we violently drop into the absolute grand finale officially concluding our massive Translation Process combat series!
In our previous deep-dives, we witnessed the Compiler grinding Source into Object files, and the Linker violently smashing those fragments together (Linkage). But a massive, critical tactical question remains: “How the hell does the program actually know exactly which physical Flash Memory address to inject the execution instructions into? And exactly what physical RAM coordinates must violently hoard the Variables?” The brutal reality is… a standard Linker engine possesses absolutely zero native intelligence regarding your specific silicon! It is completely blind! It absolutely demands a heavy “Navigational Blueprint”—a heavily fortified real-estate zoning document officially classified as the Linker Script—to aggressively execute physical Memory Allocation!
Mastering this highly restricted documentation is considered “Absolute Top-Secret Clearance.” High-level PC programmers completely avoid and entirely ignore this alien artifact. However, for hardcore Embedded Systems operatives, possessing the capability physically writing and dominating Linker Scripts represents the absolute definitive barrier violently separating raw rookies from God-Tier professionals! Today, we tear open the global Grimoires exposing exactly how this core architecture is governed. Secure your terminals, let’s breach the memory banks!
Core Theory Autopsy: The Locator Engine and Linker Script Architecture
Operating deep inside the Translation Process theater, once the Linker successfully fuses all Object shards into a massive unified block, we acquire a highly explosive Relocatable file. This payload is structurally perfect in every aspect, except for one critical fatal flaw: “It possesses absolutely zero mapped physical memory coordinates (Unresolved addresses)!” Entering this final void, a hyper-specialized extraction tool designated as the Locator (which, inside the heavy GNU Toolchain like ld, is physically fused directly inside the main Linker chassis) violently takes total command. It aggressively scans the Linker Script blueprint, physically dragging and dropping the Code and Data payloads directly screaming onto the exact physical Memory Map coordinates defining the targeted microcontroller!
When operatives physically construct a Linker Script, they are aggressively manipulating 2 primary structural monoliths and violently segregating data into 3 massive combat zones (Segments/Sections):
1. The Data Segregation Zones (Sections/Segments): The Linker violently segregates the raw program data into heavily guarded sectors (similar to locking specific ammunition strictly inside designated armory vaults):
- The
.textSegment: The absolute primary vault heavily securing the “Executable Instructions (Code)” and hyper-secure Constant data. This sector is strictly Read-only armor-plated and is universally violently dropped directly into the physical ROM or Flash Memory sectors. - The
.dataSegment: The active combat zone securing “Global or Static variables carrying live, pre-loaded initiation ordnance (Initialized variables)” (e.g.,int count = 10;). This sector absolutely demands live physical space locked inside the RAM array, granting the program authority to actively overwrite and modify the values during live combat. - The
.bssSegment: The phantom zone securing “Variables totally lacking pre-loaded ordnance (Uninitialized variables).” This acronym translates from the ancient Block Started by Symbol registry. This sector operates inside RAM, but the absolute elite tactical advantage is: It physically consumes ZERO footprint mass inside the final Executable file (.bin/.hex)! The Linker merely records the “mathematical dimension size,” commanding the C Startup Code drone to aggressively carpet-bomb and clear that exact physical RAM sector filling it entirely with zeros (0) the microsecond the silicon boots up!
2. The Linker Script Command Directives:
- The
MEMORYDirective: This command screams broadcasting directly to the Linker: “Acknowledge! This specific silicon chip possesses these exact physical hardware memory vaults, initiating at these exact hardcoded hexadecimal coordinates, possessing these exact massive dimensional limits!” - The
SECTIONSDirective: The heavy distribution command dictating exactly mapping mapping dropping specific Sections (like.textor.data) violently dragging them injecting them straight into the targetedMEMORYvaults previously declared.
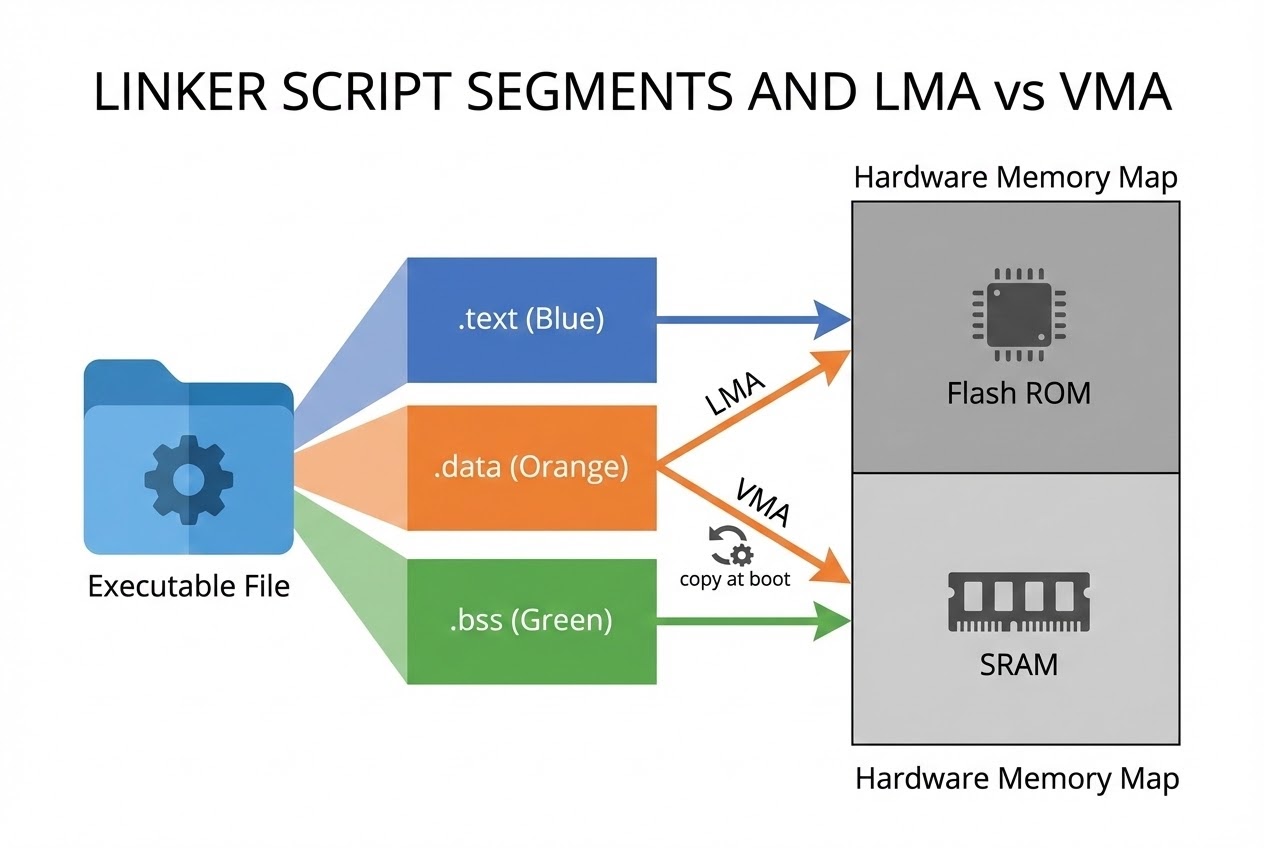
3. The Classified Secrets of LMA and VMA: This is absolute highly classified, critical intelligence for Embedded operations! Addresses legally split into 2 distinct biometric profiles:
- LMA (Load Memory Address): The exact physical static coordinates where the payload is “permanently burned and stored” while the system is dead / powered-down (Virtually always the Flash memory array).
- VMA (Virtual/Runtime Memory Address): The exact physical active coordinates where the payload will be “violently executed and utilized” during live combat operations (Virtually always the SRAM).
For the execution logic (
.text), both LMA and VMA identically occupy the Flash. However, for the.datapayload, the LMA permanently resides locked inside the Flash (securing the initial blast values during total power failure), but the VMA targets the SRAM! The hardcore C Startup protocol violently executes copying the entire.datapayload dragging it from the LMA and dropping it onto the VMA milliseconds before authorizing themain()function execution!
Firing Live Code Rounds: Extracting the Memory Blueprint
Let us visibly inspect the brutal architecture of a hyper-clean bare-metal Linker Script targeting silicon possessing both Flash and SRAM arrays. Aggressively observe the deployment of the AT> command, totally separating the LMA and VMA addressing for the .data payload!
/* ==========================================
* Standard Tactical Bare-Metal C Linker Script Blueprint
* ========================================== */
/* 1. Designating the Absolute Entry Coordinate (Virtually always the C Startup Boot Protocol) */
ENTRY(Reset_Handler)
/* 2. Broadcasting the Hardware Silicon Perimeter Specifications (MEMORY Map) */
MEMORY
{
/* FLASH memory block initiates striking at 0x08000000, possessing a 256K payload capacity (Read/Execute clearance: rx) */
FLASH (rx) : ORIGIN = 0x08000000, LENGTH = 256K
/* SRAM memory block initiates striking at 0x20000000, possessing a 64K payload capacity (Read/Write/Execute clearance: rwx) */
SRAM (rwx) : ORIGIN = 0x20000000, LENGTH = 64K
}
/* 3. Aggressively dropping specific Sections locking them onto the Memory Grid */
SECTIONS
{
/* Violently securing the execution payload (.text) injecting it directly into FLASH */
.text :
{
*(.isr_vector) /* The absolute critical Interrupt Vector Matrix MUST permanently lock onto the very front lines! */
*(.text) /* The massive compilation of all C execution code ripped from every Object file */
*(.rodata) /* Heavily shielded Read-only assets (e.g., const variables) */
. = ALIGN(4); /* 🛡️ Forcing strict architectural alignment locking exactly onto 4-byte boundaries (Word Alignment)! */
_etext = .; /* Forging a dynamic tracker (Symbol) permanently locking the absolute final Address of the .text block */
} >FLASH
/* Deploying variables carrying live ordnance (.data). The active VMA drops into SRAM, but the dormant LMA is permanently burned AT> FLASH */
.data :
{
. = ALIGN(4);
_sdata = .; /* Forging a dynamic tracker symbol locking onto the absolute starting coordinate of .data residing in RAM */
*(.data)
. = ALIGN(4);
_edata = .; /* Forging a tracker locking the absolute terminal coordinate of .data in RAM */
} >SRAM AT> FLASH /* >SRAM legally identifies the VMA, AT> FLASH legally defines the LMA */
/* Deploying phantom variables lacking ordnance (.bss). This payload drops entirely into SRAM exclusively */
.bss :
{
. = ALIGN(4);
_sbss = .;
*(.bss)
. = ALIGN(4);
_ebss = .;
} >SRAM
}
(Deep inside the C Startup sequence file (e.g., startup.c or startup.s), the system aggressively intercepts utilizing these exact specific symbols like _etext, _sdata, _edata, and _sbss brutally forged by this Linker. It weaponizes them acting as heavy pointers to execute massive Memory Initialization bombardment directly before authorizing entry into main()).
Proximity Defcons: Heavy Best Practices & Fatal Pitfalls
Aggressively hacking and rewriting a Linker Script operates identically to violently demolishing the foundational pillars of a skyscraper! If an operative executes a fatal miscalculation, the entire program will violently detonate and self-destruct milliseconds before ever breaching main()! Global engineering combat standards heavily enforce these absolute survival protocols:
- Absolutely Never Forge from Scratch (The Suicide Run): The absolute primary law of the trench! Silicon manufacturers or Compiler warlords (e.g., GCC, Keil, IAR institutes) identically universally provide heavily fortified, pre-tested standard Linker Script blueprints (
.ldor.icfextensions) bundled directly inside the project perimeter. You must aggressively scavenge and minimally Modify specifically targeting only necessary sectors utilizing their heavily shielded baselines! - Beware the Alignment Trap: Operating inside heavy 32-bit architectural juggernauts like ARM Cortex-M silicon, attempting wildly accessing reading/writing memory dropping onto physical addresses totally failing dividing cleanly by 4 (Unaligned memory access) will instantly violently trip a massive Hardware Fault, permanently locking the entire system dead! Operatives MUST aggressively enforce the
. = ALIGN(4);command perpetually structuring strict boundary perimeters around all Sections! - The Map File is the Ultimate Diagnostic Scanner: Whenever an operative crashes encountering a fatal “Memory Overflow” (e.g., the code payload expands exceeding physical Flash capacity) or demands identifying exactly which rogue function is consuming massive territory… Immediately execute opening targeting the
.mapfile forged by the Linker! This incredible document provides a microscopic autopsy detailing precisely exactly which variable, or which single line of code, dropped onto which exact hexadecimal address, and identically exactly how many physical bytes (Size) it aggressively consumed! - Deploy
KEEPShielding Preventing Optimizer Assassination: If you actively possess absolutely critical code sectors that are virtually never directly called executing within the standard C logic (for example, the absolute critical Interrupt Vector Grid, or segments tagged commanding__attribute__((section("...")))), the hyper-intelligent aggressive Linker optimizer may arrogantly judge: “Zero execution detected! Target acquired, executing deletion!” to aggressively purge space. To completely neutralize this catastrophic error, operatives MUST heavily encapsulate those commands deploying theKEEP(*(.isr_vector))shield directly inside the Linker Script perimeter, violently forcing the Linker to indefinitely retain the payload!
Conclusion
Linker Scripts represent the absolute ultimate, heavy architectural engine executing the absolute final phase translating naked C source code directly forging a heavily weaponized, live Executable firmware locking onto raw silicon hardware! It operates as the ultimate bridge violently fusing the chaotic digital software realm (Object files) directly onto the strict physical constraints mapping spatial real estate (Memory regions like Flash and SRAM). It simultaneously operates functioning as the literal birthplace generating heavy dynamic symbols that the Startup Code aggressively utilizes physically preparing the initial combat environment authorizing the microcontroller to initiate sequence!
Reaching this extraction point, operatives possess a complete tactical visual map exposing the massive overarching Translation Process, aggressively bridging Preprocessing, surviving Compilation, and entirely dominating Linkage! We firmly anticipate moving forward, the next microsecond you smash that Build trigger, you will internally comprehend absolutely every terrifying, violent mechanism screaming behind the terminal glass! For any elite operatives currently deploying bizarre, psychotic hardware memory allocations (e.g., forcing booting executing from External SDRAM arrays) or possessing heavily classified Map File interrogations… Drop a flare actively bleeding sharing the logistics directly onto our active combat grid at www.123microcontroller.com! Maintain heavy shields, Happy Hardcore Coding to absolutely every operative!