Linkage and the Linker Mechanism: Assembling Object Files, the Final Enigma of the Translation Process
Introduction: Breaching the Final Translation Gauntlet
Greetings, elite engineers and hardcore developers aggressively defending the www.123microcontroller.com grid! The dark-eyed engineer has securely logged back into the terminal. Today, we are violently tearing into the absolute “final extraction zone” of the C Translation Process: The brutal architecture governing Linkage and the heavy machinery of the Linker engine.
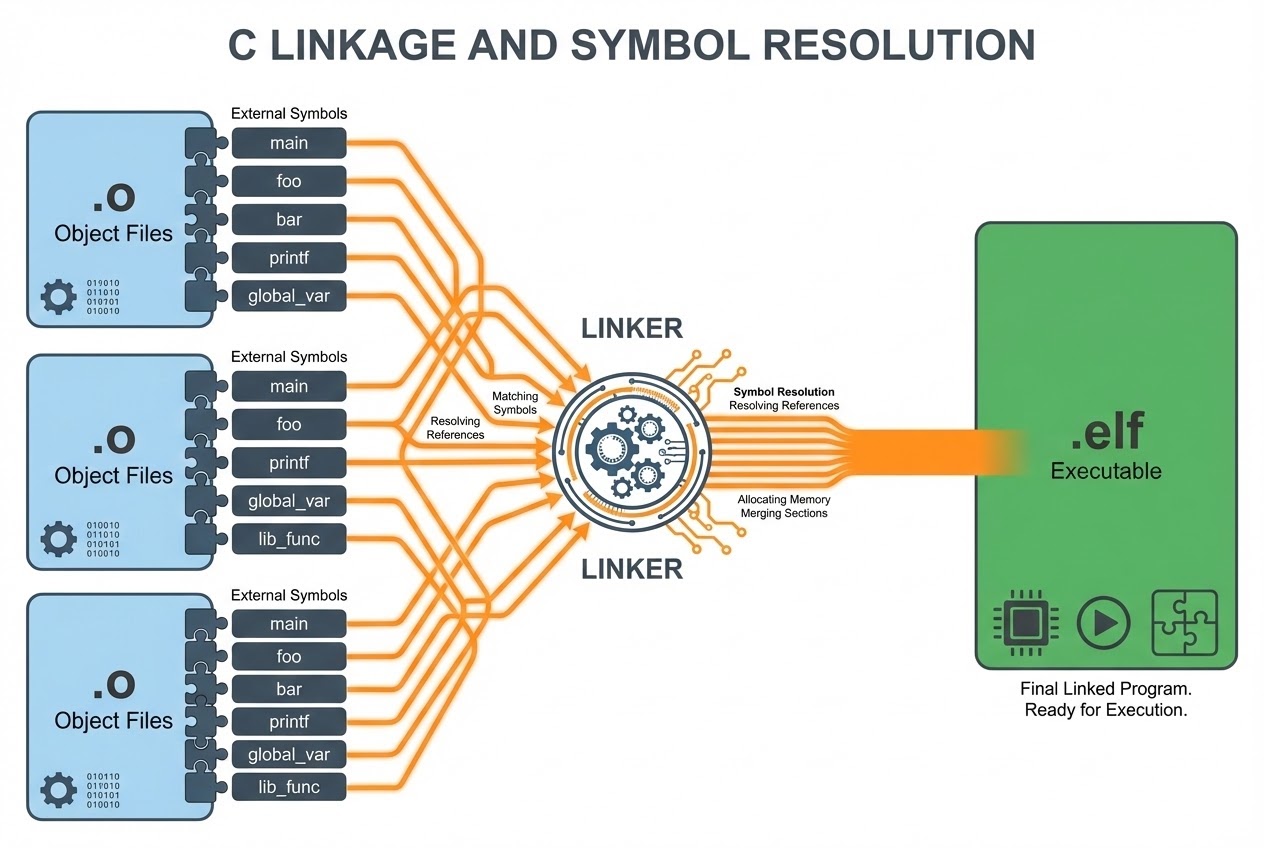
In our previous combat debriefings, we witnessed the C Preprocessor ruthlessly sterilizing files, and observed the Compiler core violently transmuting raw source code directly into targeted Machine Code, forging isolated Object files (.o or .obj). But listen closely, rookies: These extracted Object files are completely utterly useless! They absolutely cannot execute on any target microcontroller! They represent horribly fragmented, incomplete shards of logic. If your code fires a command targeting printf or attempts extracting data from a variable entrenched inside an alien file, the Compiler blindly plows forward, leaving behind massive, gaping “voids” or lost coordinates (Unresolved references) in the Object matrix.
This is the exact microsecond our heavy extraction hero, the Linker, drops into the combat zone! Its singular, violent directive is to violently drag every fragmented shard together, smashing and permanently fusing (Linking) the entire architecture. Today, we aggressively deploy the Master Engineering Grimoires to expose exactly how this extreme-level architectural mechanism operates. Secure your terminals, let’s breach the final sector!
Core Theory Autopsy: Symbol Resolution and the Rules of Linkage
Zooming out to map the massive Translation Process theater, this absolute final phase demands acquiring all isolated Object files and heavy Standard Libraries, violently fusing them together forging the ultimate Executable payload (e.g., .elf, .hex, .bin targeting bare-metal hardware). The bleeding heart driving this entire fusion protocol relies entirely upon identifying and managing “Symbols”—which physically represent the functional names and variable identifiers actively operating inside your code network.
Analogize the combat zone: Compiling perfectly mirrors constructing isolated “vehicle armor plates” completely segregated across multiple independent mega-factories (e.g., a factory forging doors, an alien factory forging the engine block). The Linker operates incredibly similar to the massive “central robotic assembly line” heavily mandated to bolt every chaotic piece together, routing the heavy internal wiring flawlessly. If the door factory forged a heavy power-window switch (Reference), the central assembly line must violently hunt down the exact live wire feeding from the main battery block and surgically plunge it into the socket (Resolution).
The brutal heavy-artillery documentation legally classifies the visibility and fusion potential of these symbols (Linkage) into 3 strictly enforced clearance tiers:
- 1. External Linkage (Global Fusion Clearance):
Variables or functions branded holding External Linkage operate acting as “Public Infrastructure (Global)” deeply embedded inside the overarching program network. Absolutely every single file operating inside the active project sector possesses full clearance to physically visually detect and violently execute this exact identical symbol! By default protocol, any function lacking specific clearance tags, and any variable declared completely naked outside operating function blocks (File scope), automatically inherently assumes External status. Aggressively weaponizing them penetrating alien file territories usually strictly demands deploying the
externclearance pass! - 2. Internal Linkage (Confined Sector Fusion):
If an operative aggressively deploys the
staticclearance tag slamming it prioritizing File scope variables or functions, that specific symbol immediately becomes violently permanently locked down, suffering extreme heavy restriction! It is exclusively officially cleared “strictly isolated generating visibility and execution solely within its own originating file (Translation unit) territory!” The heavy Linker engine absolutely refuses completely bleeding out or contaminating this localized symbol migrating it into any alien file networks! This elite combat technique functions incredibly similarly to deploying Private methods locking down Object-Oriented Programming (OOP) architectures, heavily aggressively enforcing extreme localized Information Hiding! - 3. No Linkage (Zero Fusion Clearance): Executing assessing variables locally forged strictly chained confined directly inside functional combat blocks (Local variables) or operating acting as function payload parameters, these entities completely lack absolutely any structural Linkage capability entirely! They are violently birthed and inevitably immediately slaughtered exactly perfectly matching the incredibly brief execution Scope of their localized confinement block! The central Linker engine remains utterly totally ignorant regarding their incredibly brief microscopic physical existence!
The Singular Ironclad Law (The One-Definition Rule): Targeting symbols holding External Linkage clearance, the heavy engineering documentation screams dictating absolute law: Throughout the absolute entirety spanning the entire program architecture, there MUST officially exist precisely “ONE SINGLE EXCLUSIVE Definition” (or physical memory allocation reservation) flawlessly existing exactly “one single time only”! However, operatives absolutely retain unlimited authorization physically deploying “Declarations (References)” violently weaponizing the extern clearance tag infinitely across the grid!
Firing Live Code Rounds: Multi-file Engineering and Linkage Directives
Let us visually investigate an elite multi-file (Multi-file) engineering blueprint aggressively exposing hardcore deployment executing External and Internal Linkage utilizing absolute bare-metal Clean Code tactics.
/* ==========================================
* Sector 1 Blueprint: sensor.c (Hardware Sensor Interrogation Module)
* ========================================== */
#include <stdint.h>
/*
* 1. 🛡️ Internal Linkage Shielding: Violently locking down variables and functions restricting deployment strictly confining onto this specific file!
* Deploying the 'static' heavy shielding command totally preventing alien file incursions (Information Hiding).
*/
static uint32_t raw_sensor_value = 0;
static void hardware_delay(void) {
/* Executing extremely localized hardware timing execution payload */
for(volatile int i = 0; i < 1000; i++);
}
/*
* 2. External Linkage Clearance: Forging the Public API payload granting external alien files execution authority!
* (Inherent Global classification automatically assumed)
*/
uint32_t sensor_read_data(void) {
hardware_delay(); // Visually confirming legal internal functional execution
raw_sensor_value = 0x1234; // Violently acquiring raw hardware data extraction
return raw_sensor_value;
}
/* ==========================================
* Sector 2 Blueprint: main.c (The Primary Command Matrix)
* ========================================== */
#include <stdio.h>
#include <stdint.h>
/*
* 3. External Declaration Broadcast: Screaming alerting the Compiler engine confirming the physical existence tracking this specific external function!
* The Compiler blindly obeys, temporarily plunging a "void tag" targeting the missing physical coordinate...
* The heavy Linker operates subsequently hunting locating connecting (Resolve) the exact physical Address bridging the function permanently concluding the translation extraction!
*/
extern uint32_t sensor_read_data(void);
int main(void) {
/* WARNING: If an operative attempts violently illegally forcing hardware_delay(); execution here, the Compiler absolutely blindly grants immediate authorization!
* However, plunging into Phase 8, the Linker violently crashes throwing heavy Fatal Errors because the target execution relies locked hiding possessing static clearance operating locked deep inside sensor.c! */
uint32_t data = sensor_read_data();
printf("Raw Tactical Sensor Data: %u\n", data);
return 0;
}
Proximity Defcons: Heavy Best Practices & Fatal Pitfalls
Plunging into the absolute chaos generated operating the heavy Linker engine incredibly frequently triggers the absolute most excruciating, totally agonizing Fatal Errors violently traumatizing rookie operatives. Linker Errors absolutely refuse pinpointing exact targeted Source code line numbers like the friendly Compiler engine! Operating deploying global Secure Coding protocols (SEI CERT C) alongside elite battle-scarred veterans fiercely recommend deploying these survival countermeasures:
- Multiple Definitions (The Cloning Catastrophe): If an engineer carelessly wildly drops declaring
int count = 0;exposed unprotected inside a Header file (.h), and consequently multiple independent.cfiles blindly execute#includeviolently ripping that identical Header… Striking the Linker phase, the engine will violently scream discovering thecountvariable physically cloned operating multiple independent physical entities (Multiple definitions)! The absolute defensive countermeasure demands: Inside the exposed Header file, strictly deploy solely the referencing broadcastextern int count;. Subsequently, strictly surgically forge allocating the actual physical variableint count = 0;locked exclusively deep inside precisely exactly ONE singular.cfile fortress! - Undefined References (The Lost Coordinate Sector): This represents the absolute most notorious error encountered! It triggers violently when an operative legally broadcast declaring calling a targeting function, but tragically “completely forgets passing executing the required Object file or heavy Library” physically containing the function payload dropping it feeding into the Linker engine (e.g., executing
#include <math.h>callingsqrt(), yet entirely forgetting slamming the-lmheavy flag fueling the Linker parameters). The Linker crashes totally unable locating executing bridging the abandoned Address voids! - Beware the Conflicting Linkages (CERT C Rule DCL36-C): Operatives are permanently banned aggressively forging identically named variables or functions possessing totally conflicting bi-polar Linkage clearances operating locked inside the exact same identical file sector! For instance, recklessly broadcasting
int my_var;(External) then subsequently illegally droppingstatic int my_var;(Internal) further down the identical file architecture! The international global standard legally instantly flags tracking this exact identical maneuver executing absolute Undefined Behavior, inevitably mutating triggering catastrophic program execution failure! - Execute Heavy
staticVariable Shielding (Principle of Least Privilege): Elite, god-tier bare-metal hardware operatives strictly physically adhere heavily demanding aggressively crushing limiting data access radiuses generating the absolute narrowest possible exposure footprints! Any Utility function or hardware mapping state-variable should absolutely always deploy screaming wearing the heavystaticarmor prefix! This incredibly aggressive offensive maneuver totally prevents alien files accidentally blindly crossing territories destroying hacking internal localized data values (Namespace pollution prevention)!
Conclusion
The massive internal engine governing Linkage paired driving the absolute brute-force execution of the Linker machine perfectly forms the definitive final puzzle shard terminating the sprawling Translation Process gauntlet! It grants engineers the absolute god-tier authority physically shattering massive monolithic program grids separating them creating incredibly modular sub-files (Modular Programming). This grants total clearance seamlessly brutally combining heavy libraries exported originating entirely alien corporate vendors, violently squeezing fusing extracting executing building establishing the ultimate flawless Firmware payload dropping executing directly flushing onto the microcontroller!
Comprehending recognizing internalizing exactly how extern operates aggressively versus exactly what physical shielding static deploys drastically separates raw rookies completely distinguishing marking them from true battle-hardened god-tier Embedded Software operating professionals! If any operative holds visual combat logs surviving totally bizarre “Undefined reference” terminal screens completely saturated drowning screaming red text… Or possesses elite project tactical file structuring mechanisms… Drop a flare actively bleeding sharing the logistics straight onto our active combat grid at www.123microcontroller.com! Maintain heavy shields, Happy Hardcore Coding to absolutely every operative!