3 Compiler Command Keywords (const, volatile, inline): The Bare-Metal Art of Extreme Optimization
Introduction: Commanding the Compiler Engine
Greetings, elite engineers and hardcore developers aggressively defending the www.123microcontroller.com grid! The dark-eyed engineer has securely logged back into the terminal. Today, we violently dive into the exact battleground that absolutely segregates standard “Desktop Programmers” entirely distinguishing them from God-Tier “Embedded System Engineers”—and that is executing raw Optimization (Extreme Performance Output) directly weaponizing Compiler Keywords!
When we drop raw C code into the terminal, the Compiler engine desperately attempts executing absolutely every trick imaginable aggressively mutating your code forcing it to run “Max Speed” and consuming the “Absolute Minimum Footprint.” It wildly slaughters code it arrogantly deems useless or aggressively hoards critical values hiding them deep inside CPU Registers! But listen closely, rookies: In the brutal, unforgiving realm of bare-metal hardware interfacing, the Compiler’s arrogant “helpfulness” virtually always violently crashes your entire system or mutates hardware logic! Today, we deploy the 3 classified weapon systems—const, volatile, and inline—aggressively communicating directly with the Compiler engine, forcing it into total submission and controlling Optimization absolutely!
Core Theory Autopsy: Dominating the 3 Optimization Directives
Operating inside the heavily fortified Optimization theater, the global Grandmasters specifically deploy these 3 specialized directives executing these distinct tactical maneuvers:
- 1.
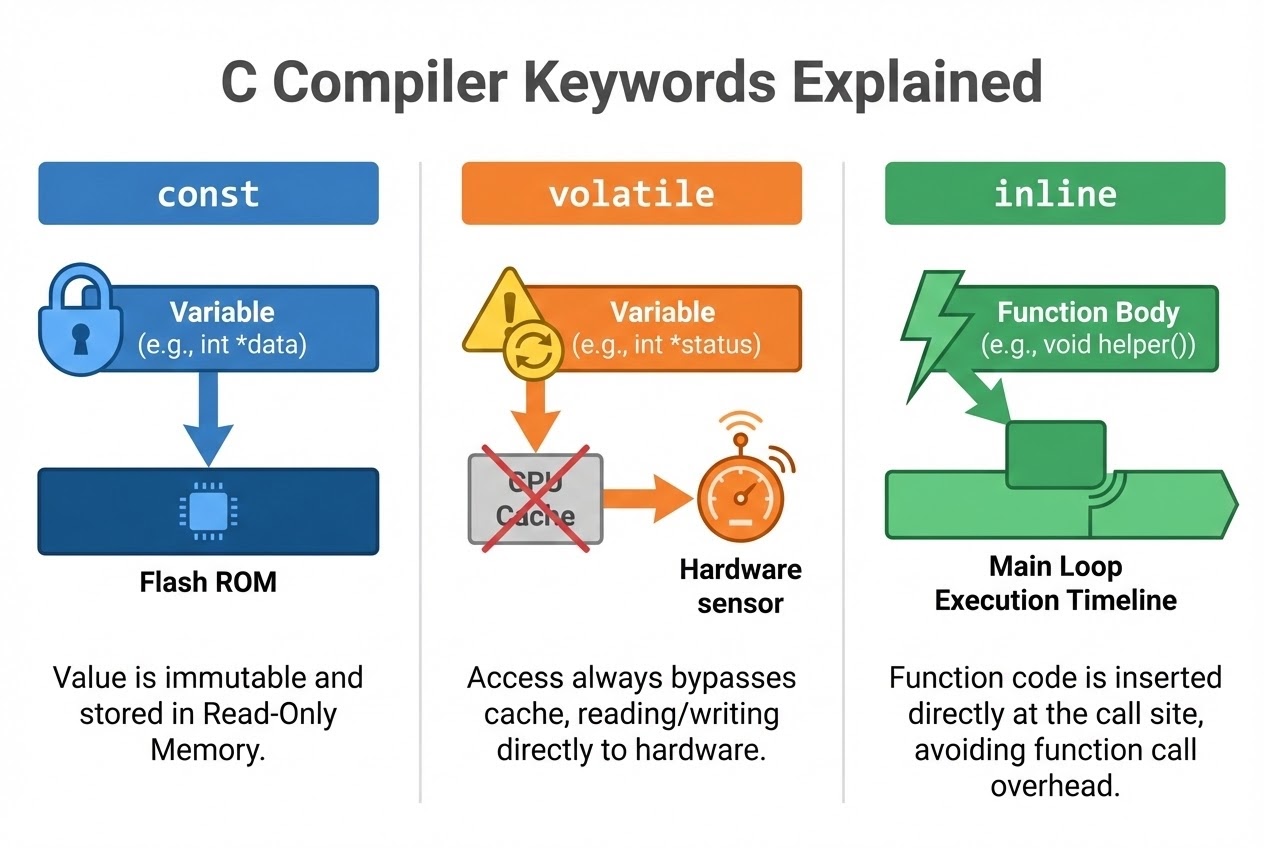
const(The Heavy Data Compressor & Shield):- Translation / Directive: Originates from Constant. This heavy tag screams directly at the Compiler: “This variable payload is permanently locked! Absolute ZERO authorization to overwrite after initialization!”
- Optimization Impact: The microsecond the Compiler recognizes this value remains eternally frozen, it aggressively executes “Constant folding” instantly ripping the raw value and hardcoding it executing directly, totally obliterating the latency required performing repeated memory read cycles! Furthermore, deep inside Embedded infrastructure, the Compiler almost universally violently drops
constvariable payloads directly locking them into Read-Only Memory (ROM or Flash). Since Flash is significantly cheaper and massively abundant, this aggressive tactical maneuver brilliantly saves incredibly precious RAM real estate!
- 2.
volatile(The Hardware Override / Halting the Optimizer):- Translation / Directive: This incredibly lethal keyword screams warning the Compiler: “Acknowledge! The physical value residing exactly inside this Memory coordinate can aggressively mutate completely randomly, entirely outside the program’s vision or control!” (For example: Hardware forcefully writing to Memory-mapped I/O ports, data mutated inside an explosive Interrupt Service Routine (ISR), or memory hacked by an alien Thread).
- Optimization Impact: This operates as an absolute “Suppression (Override)”! It violently explicitly bans the Compiler from ever executing Optimization on this precise variable! Normally, if a loop continuously interrogates the same variable, a hyper-intelligent Compiler aggressively caches that value locking it inside a CPU Register executing maximum speed. But if that target is a live hardware sensor… you will strictly continuously read the dead, frozen cached value locked in the Register! Slamming down the
volatiletag practically physically grabs the CPU, forcing it to literally violently read the exact physical hardcoded Memory Address coordinate “every single execution cycle” entirely bypassing the Cache! It identically prevents the Compiler from arrogantly assassinating and purging Delay Loops (which normal optimizers violently delete classifying as useless Dead Code)!
- 3.
inline(The Function Overhead Executioner):- Translation / Directive: Forged deep inside the C99 standardization, this is a heavy recommendation directly advising the Compiler to entirely literally rip out the exact “Function Body (The code logic)” and violently splice it directly replacing the “Function Call (The jump command)” everywhere it is deployed across the grid!
- Optimization Impact: Every time the CPU jumps executing a function, a heavy tactical latency penalty (Overhead) strikes! It bleeds cycles forcefully pushing parameters violently down the Stack and jumping registers. Deploying the
inlinetag brutally executing the jump overhead entirely! This massively accelerates the program footprint, heavily optimizing tiny, hyper-repeated functions (e.g., Getters/Setters or extreme mathematical conversions). It is significantly safer than hacking Macros (#define) because the Compiler heavily maintains strict Type-checking security! But Warning: It represents just a “Hint”. The Compiler engine holds total tactical authority absolutely rejecting dropping an Inline execution if the target function is classified too massive!
Firing Live Code Rounds: Bare-Metal Control
Let us visually investigate an elite Clean Code structure aggressively deploying all 3 heavy keywords violently interrogating a raw hardware temperature sensor!
#include <stdint.h>
#include <stdio.h>
/*
* 1. Fusing const with volatile: (Standard Bare-Metal Protocol)
* - volatile: Violently forces the CPU loading the payload directly from the physical Address instantly passing cache (Because Hardware dictates the value).
* - const: Heavy read-only armor strictly preventing the programmer from accidentally executing a catastrophic overwrite!
*/
uint32_t volatile * const TEMP_DATA_REG = (uint32_t *)0x40021000;
/*
* 2. Deploying const securing static data:
* This critical float payload will violently drop straight into the Flash Memory (ROM), preserving precious RAM capacity!
*/
const float SENSOR_CALIBRATION_FACTOR = 1.045f;
/*
* 3. Executing static inline:
* Brutally executing eliminating the Function Jump Overhead driving absolute maximum performance!
* The Compiler rips the internal mathematical equation splashing it directly replacing the call execution coordinate!
*/
static inline float convert_raw_to_celsius(uint32_t raw_val) {
return ((float)raw_val * 0.01f) * SENSOR_CALIBRATION_FACTOR;
}
int main(void) {
while (1) {
/*
* LETHAL WARNING: If TEMP_DATA_REG completely lacks the volatile tag, the hyper-aggressive Compiler optimizer
* may entirely purge this loop, or simply read the value exactly ONCE storing it permanently executing an infinite dead value!
*/
uint32_t current_raw = *TEMP_DATA_REG;
float current_temp_c = convert_raw_to_celsius(current_raw);
printf("Current Tactical Temp: %.2f C\n", current_temp_c);
// Simulating delay execution (Live combat should deploy a Hardware Timer)
for(volatile int delay = 0; delay < 100000; delay++);
}
return 0;
}
Proximity Defcons: Heavy Best Practices & Fatal Pitfalls
Commanding Optimization engines resembles violently swinging a double-edged plasma sword! The global Secure Coding doctrine (SEI CERT C) and combat veterans aggressively issue these terminal warnings:
- The Lethal
volatileReality Distortion (Thread Safety Illusion): Massive populations of raw programmers possess the tragic, fatal hallucination believing slappingvolatileonto a variable instantly renders it secure against alien Threads attempting hostile execution (Thread-safe) or magically rendering operations Atomic. This is “Catastrophically Incorrect!”volatilestrictly exclusively halts Register Caching! It absolutely FAILS creating massive Memory Barriers and performs exactly ZERO defensive shielding preventing heavy CPU-level Race Conditions! If you are plunging executing deep Multithreading operations, you MUST absolutely deploy heavy Mutexes, Semaphores, or the hardcore<stdatomic.h>library! - Beware the
inlineCode Bloat Mutually Assured Destruction: Whileinlinecommands viciously accelerate speed, violently ripping and cloning copying the exact function logic pasting it repeatedly across 50 independent files violently explodes your physical compiled Binary size (Code Bloat)! Inside an Embedded chip possessing brutally limited Flash Memory, this triggers absolute annihilation. Strictly reserveinlinedeployments exclusively targeting incredibly tiny execution functions! - The Dead-On-Arrival Optimization Bugs (-O2, -O3): Countless code architectures execute flawlessly executing under Debug conditions (Optimization Disabled), but violently detonate the exact millisecond the operative fires the heavy
-O2or-O3Compiler Optimization flags (e.g., Delay loops magically vanish, or button inputs completely freeze). Exactly 99% of these explosive disasters are triggered when an operative completely forgets slapping thevolatiletag shielding variables heavily shared between an Interrupt (ISR) and the Main Loop, or abandoning hardware Registers completely unprotected!
Conclusion
Plunging deep inside the brutal bare-metal C programming trench, const acts as your heaviest, most loyal shield violently defending variables and actively preserving critical RAM arrays. inline operates as your hyper-speed execution tunnel violently accelerating calculations. Finally, volatile acts as the absolute ultimate bridge commanding the Compiler Engine respecting and acknowledging aggressive Hardware mutability entirely without covertly assassinating deleting your code! Mastering this exact triad represents the ultimate core dominating sustainable, flawless Optimization.
If any operatives operating on the server have ever experienced massive system detonation failing to shield variables using volatile (I absolutely guarantee every bare-metal engineer has suffered this trauma!) or possess incredibly hostile inline deployment tactics… drop a flare actively bleeding sharing the logistics straight onto our active combat grid at www.123microcontroller.com! Maintain heavy shields, Happy Hardcore Coding to absolutely every operative!