Jump Tables & Switch Statements: Unlocking Light-Speed Branching via Compiler Shortcut Architectures

Introduction: Bypassing the Conditional Trench
Greetings, elite engineers and hardcore developers aggressively defending the www.123microcontroller.com grid! The dark-eyed engineer has securely logged back into the terminal. Today, we violently tear into an incredible Optimization technique classified deep inside the most fundamental architectural element of C programming: Conditional Branching!
Whenever an operative writes raw code demanding the CPU to selectively execute commands based on a variable’s payload (e.g., executing a State Machine or deserializing raw Serial Port packets), the standard, unoptimized infantry reflexively builds massively long, chaining if-else if structures. But operating deep inside the hardware trenches, did you know that actively commanding a switch statement can violently mutate your entire compiled architecture into a hyper-accelerated “Jump Table”? This is absolute black magic! It aggressively slaughters the latency of interrogating conditions line-by-line, converting the execution into a single, light-speed “Jump” violently teleporting exactly to the target coordinate in a fraction of a microsecond! Today, we rip open the global grandmaster C grimoires dissecting exactly how Jump Tables physically operate and exactly how we weaponize them achieving extreme speed inside our Embedded systems. Initiate the launch sequence!
Core Theory Autopsy: Cracking Switch and Jump Table Mechanics
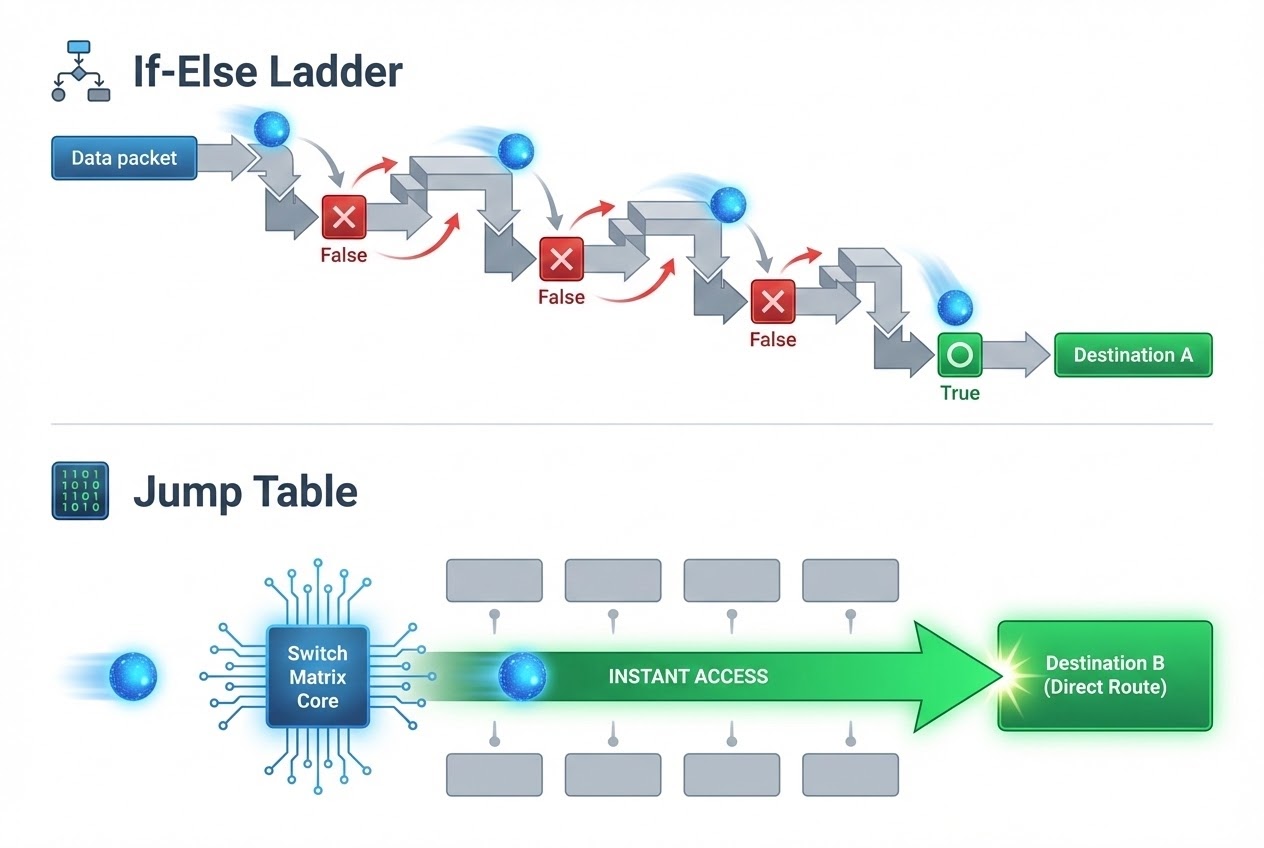
Operating inside the heavily classified Optimization theater, elite sources aggressively distinguish the brutal performance gap separating if-else ladders from switch statements, exposing the underlying hidden “Jump Table” mechanism:
- 1. The Heavy Burden of the
if-else ifLadder: When deploying conditional checks using continuousif-else ifblocks, the CPU is violently forced to physically Calculate conditions (Evaluate expression) and execute massive Conditional Jumps (Conditional branch) strictly “Sequentially, command-by-command” from top to bottom until it strikes a True condition! Imagine an operative frantically searching for a specific room inside a massive hotel, being forced to violently kick open and visually inspect absolutely every single door in order. If the target payload resides identically at the bottom of the ladder, the CPU bleeds catastrophic amounts of execution cycles! - 2. The
switchand Jump Table Black Magic: The exact millisecond an operative deploys theswitchcommand (which strictly mandates the target expression MUST evaluate strictly to Integer constant expressions), the incredibly advanced Compiler engine virtually always violently Optimizes this exact code block, physically mutating it into a high-speed matrix classified as a Jump Table! - 3. How Jump Tables Physically Execute:
A Jump Table operates identically as an “Array of Target Addresses (Array of
gotovectors)” sequentially indexed directly by the exact Case integers. When the compiled binary fires in live combat, it completely aborts blindly interrogating sequentialiflines! Instead, it violently snatches the raw variable payload, injects it entirely as a mathematical Offset, and brutally “Jumps (Teleports) straight through physical memory directly terminating at the target Case Address!” It executes this using a massive Unconditional Jump (Unconditional branch) exactly 1 or 2 times! Imagine checking the hotel layout matrix once, boarding an express elevator, and teleporting instantly to the exact room! This guarantees absolute Constant-Time performance (O(1) execution latency) regardless of whether you loaded 5 target cases… or 50 target cases! - 4. Macro-Optimization Supremacy (Function Pointers):
If your
switcharchitecture expands into a colossal, massive monolith (e.g., packing hundreds of execution code lines deep inside every single Case), elite embedded security experts aggressively command operatives to entirely abandonswitchand manually forge a custom-built Jump Table! We execute this violently by forging a hardcore “Array of Function Pointers (Dispatch Table)”! Deploying this maneuver brutally disintegrates code complexity, massively reduces the cognitive threat vector (Cyclomatic complexity), and executes with terrifying speed!
Firing Live Code Rounds: Evolving Switch to Vector Function Pointers
To visually dissect this exact Optimization maneuver, let us interrogate the architecture controlling a live Hardware Sensor State Machine. The primary configuration deploys the standard switch, while the hyper-optimized configuration manually deploys the Array of Function Pointers forging a custom Clean Code Jump Table!
#include <stdio.h>
#include <stdint.h>
/* Actively declaring the Sensor Hardware Data Type utilizing an enum (Hardcoded Integer values 0, 1, 2...) */
typedef enum {
SENSOR_TEMP = 0,
SENSOR_HUMID,
SENSOR_LIGHT,
MAX_SENSORS /* Hardcore Hack: Violently inject this to automatically track the absolute array magnitude! */
} SensorType_t;
/* =========================================================
* Tactical Protocol 1: Deploying the standard switch statement
* (The Compiler Engine will covertly mutate this into a raw Jump Table behind the scenes)
* ========================================================= */
void process_sensor_switch(SensorType_t type) {
switch (type) {
case SENSOR_TEMP:
printf("Interrogating Temperature Coordinate...\n");
break;
case SENSOR_HUMID:
printf("Interrogating Humidity Coordinate...\n");
break;
case SENSOR_LIGHT:
printf("Interrogating Photonic Coordinate...\n");
break;
default:
printf("WARNING: Alien Sensor Detected!\n");
break;
}
}
/* =========================================================
* Tactical Protocol 2: Extracting Absolute Maximum Speed via Function Pointers
* (Mandatory deployment replacing colossal switch cases packed with heavy execution logic)
* ========================================================= */
/* 1. Forging the isolated execution function payloads targeting each specific case */
void read_temp(void) { printf("Interrogating Temperature Coordinate...\n"); }
void read_humid(void) { printf("Interrogating Humidity Coordinate...\n"); }
void read_light(void) { printf("Interrogating Photonic Coordinate...\n"); }
/* 2. Forging the Array of Function Pointers (Behold! The physical manual Jump Table!) */
void (*sensor_functions[MAX_SENSORS])(void) = {
read_temp, /* Memory Index 0 */
read_humid, /* Memory Index 1 */
read_light /* Memory Index 2 */
};
/* 3. The Master Function immediately achieves O(1) velocity totally annihilating if-else or switch structures! */
void process_sensor_table(SensorType_t type) {
/* 🛡️ CRITICAL DEFENSE: You MUST absolutely execute strict Bounds Checking prior to jumping to prevent a catastrophic Segmentation Fault crash! */
if (type >= 0 && type < MAX_SENSORS) {
/* Violently jump directly executing the target function matching the exact Memory Index! */
sensor_functions[type]();
} else {
printf("WARNING: Alien Sensor Detected!\n");
}
}
int main(void) {
process_sensor_switch(SENSOR_HUMID);
process_sensor_table(SENSOR_LIGHT);
return 0;
}
Proximity Defcons: Heavy Best Practices & Fatal Pitfalls
Even though deploying switch acts as an absolute gateway massively authorizing Compiler Optimization, the global elite engineering manuals and Secure Coding standards (CERT C) strictly issue heavy, terminal warnings regarding catastrophic pitfalls:
- The Fatal Fall-Through Detonation: Hardcore C syntax laws violently dictate that if an operative critically fails to manually inject the
break;command terminating acase, the CPU execution thread will aggressively bleed (Fall-through) violently crashing downwards executing directly into the subsequentcasecontinuously! This represents the absolute most notorious bug triggering massive logic leaks. Always secure your perimeters deployingbreak;! And operating modern compilers (C23 or C++), if an operative absolutely “intentionally” demands a bleed-through maneuver, you MUST explicitly deploy the[[fallthrough]];attribute communicating your intent to the Compiler, violently suppressing its Warning alarms! - Banned Initialization inside the Switch Dead Zone: The global DCL41-C heavy compliance standard strictly issues extreme warnings: Absolutely NEVER declare and initialize a local variable (e.g.,
int x = 10;) violently dropped inside the open{ ... }block of aswitchresiding physically before the initialcaselabel! The exact microsecond the Compiler commands the massive Jump into a targetcase, it violently “Bypasses the absolute variable Initialization execution completely!” This catastrophic error permanently injects hostile garbage (Indeterminate values) directly into that variable triggering massive system corruption! - Always Deploy the
defaultSafety Net Catch: Even if an operative mathematically guarantees the incoming payload completely matches every designedcase(e.g., heavily restricted viaenum), operating in hostile hardware environments, raw memory can spontaneously fatally corrupt! Operatives MUST always string up a heavydefault:label operating as a fail-safe catch triggering extreme Error notifications (e.g., blasting a Print warning or executing a Hard Assert), actively preventing the architecture from failing silently in the background!
Conclusion
Operating deep inside the Macro-optimization theater, actively electing to weaponize switch targeting massive operations instead of deploying exhausting if-else chains—or aggressively upgrading the architecture deploying a raw Array of Function Pointers—represents elite architectural logic! It violently mutates your physical binary code converting conditions into massive high-speed Jump Tables! This maneuver actively shrinks the compiled binary footprint and massively explodes the exact physical reaction speed executing on your Embedded hardware!
If any operatives operating on the server are obsessively interested in ripping open the raw Assembly logs (.lst) interrogating what an actual Compiler-generated Jump Table physically looks like stripped bare… drop a flare actively sharing the raw Assembly Code snapshots straight onto our active combat grid at www.123microcontroller.com! Maintain heavy shields, Happy Hardcore Coding to absolutely every operative!