Context Switching: The Latent Magic and Hardware Mechanics Dominating Embedded Multitasking

Introduction: Exposing the Multitasking Phantom
Greetings, elite engineers and hardcore developers aggressively defending the www.123microcontroller.com grid! The dark-eyed engineer has securely logged back into the terminal. Today, we are violently excavating the absolute bedrock of Operating Systems (OS) and the hardcore mechanics of Multitasking!
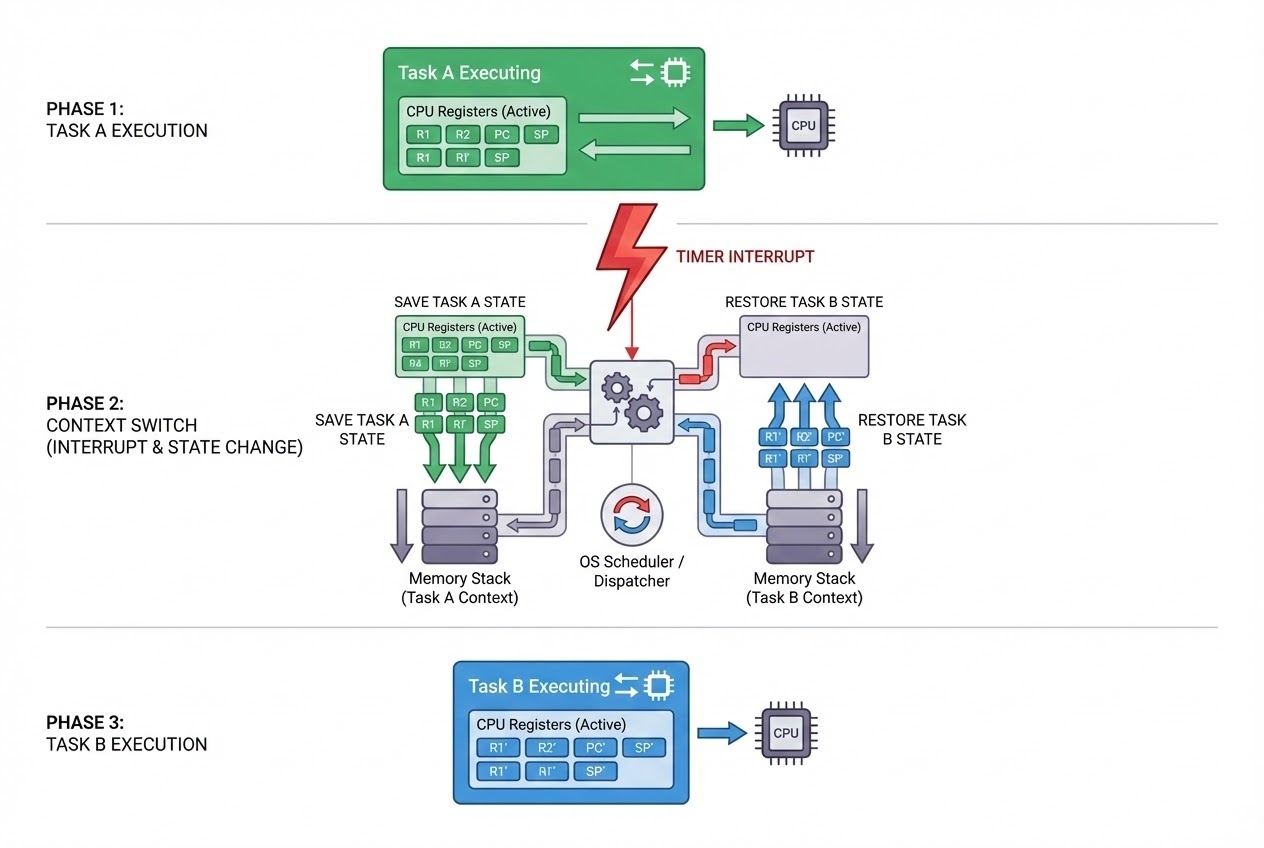
In our previous tactical deep-dives, we brutally dissected how launching multiple heavy Operations (Multitasking) on a severely restricted single-core microcontroller projects a massive “Illusion” of simultaneous parallel execution. However, actively powering this seamless optical illusion is an absolute unseen titan: The “Context Switch”! This ultra-violent, hyper-fast procedure represents the actual beating heart authorizing true Multitasking matrices! Today, we rip open the global architectural schematics, exposing exactly what Context Switching executes, how it brutally manipulates physical hardware, and precisely how much processing power it violently bleeds from your CPU! Initiate the breach!
Core Theory: What Exactly is a Context Switch in Multitasking?
Operating inside the massive theater of Multitasking, the absolute primary directive of the Queue Commander (Scheduler) is violently rationing CPU cycles across multiple independent payloads (Tasks or Threads). But executing the brutal command forcing the CPU to instantly terminate Task A, violently pivot, and immediately detonate Task B demands a massive architectural maneuver classified as the Context Switch!
Elite global architects dissect this ultra-violent procedure directly comparing it to raw hardware manipulation:
- 1. Defining the “Context” (The Operational State):
Imagine multiple operatives fiercely taking turns reading the exact same highly-classified manual (representing the single-core CPU). To successfully rotate personnel, every single operative absolutely MUST possess a personal “Bookmark,” permanently hardcoding the exact page and sentence they suspended reading!
Inside the brutal CPU architecture, this identical “Bookmark” represents the Context! It dictates the absolute, precise physical state of every single CPU Register captured at that exact microsecond, heavily consisting of:
- The Program Counter (PC) or Instruction Pointer: Violently pointing to the exact memory address containing the absolute next Assembly instruction demanding execution!
- The Stack Pointer: Actively tracking the exact peak coordinate of this specific Task’s local tactical variables!
- General Purpose Registers: The raw, highly volatile data variables the ALU was aggressively calculating mid-strike!
- 2. The Phantom Swap (The Switching Process):
When a catastrophic System Event detonates demanding an immediate Task pivot (e.g., the Time slice violently expires or a massive Hardware Interrupt strikes), the OS brutally “Freezes” the active Task! It then violently rips every single Context variable directly out of the CPU Registers and aggressively “Saves (Pushes)” them deep into external Memory/Stack! Instantaneously, it aggressively yanks the Context of the newly authorized Task out of cold storage, violently “Loads (Pops)” them straight back into the CPU Registers, and violently commands the CPU to detonate execution from the exact suspended Bookmark!
- 3. Absolute Bare-Metal Hardware Command: Because Context Switching demands violently manipulating and physically ripping raw values in and out of silicon CPU Registers, this absolute core logic CANNOT be compiled from C! It MUST be brutally hardcoded deploying raw Assembly Language! The exact syntactic structure of this code will radically mutate depending entirely on the physical silicon architecture (e.g., An ARM Cortex-M Context Switch code structure will violently clash against a PIC or 8051 architecture)!
Firing Live Code Rounds: The Task Control Block
Because a genuine Context Switch demands raw destructive Assembly execution, this briefing will actively deploy C structure simulations visually representing the “Bookmark”, officially classified as the Task Control Block (TCB)! This represents the absolute core data structure every RTOS heavily weaponizes storing the Context of every single Task!
#include <stdint.h>
/*
* Forging the absolute Data Structure serving as the Task's "Bookmark"
* Universally classified across all OS layers as the TCB (Task Control Block)
*/
typedef struct {
uint32_t* stack_pointer; // Aggressively tracking this specific Task's RAM Stack coordinate
uint8_t priority; // The absolute Tactical Execution Rank (Priority)
uint8_t task_state; // The Operational Phase (e.g., READY, RUNNING, BLOCKED)
} TaskControlBlock_t;
TaskControlBlock_t* current_task;
TaskControlBlock_t* next_task;
/*
* This ISR Function is violently detonated by the Hardware Timer Interrupt (e.g., SysTick)
* Actively ordered to brutally swap execution from current_task straight to next_task
*/
void RTOS_Scheduler_ISR(void) {
/* 1. Interrogate the queue: Target the absolute Highest-Priority READY Task! (Heavy Scheduler Logic) */
next_task = find_highest_priority_ready_task();
if (next_task != current_task) {
/*
* 2. DETONATE THE CONTEXT SWITCH!
* 🛡️ LETHAL WARNING: The code executing below represents pure simulation comments!
* True execution DEMANDS raw Assembly logic (e.g., using _asm volatile (...))
*/
// [Assembly] PUSH: Violently rip ALL current CPU Registers storing them deep into the active Stack!
// [Assembly] current_task->stack_pointer = CPU_STACK_POINTER;
// [Assembly] CPU_STACK_POINTER = next_task->stack_pointer;
// [Assembly] POP: Violently rip ALL target Registers out of the new Stack jamming them into the CPU!
current_task = next_task;
}
/* 3. TERMINATION: As the ISR concludes, the CPU violently teleports execution directly striking next_task! */
}
Proximity Defcons: Heavy Best Practices & Fatal Pitfalls
Commanding an architecture capable of executing brutal Context Switches operates as a highly volatile double-edged sword inside Embedded combat zones! Elite specialists actively track these catastrophic pitfalls:
- The Context Switch Fatigue Collapse (The Massive Overhead Penalty): Violently ripping and restoring CPU registers is absolutely NEVER free! It aggressively bleeds execution time and raw CPU Cycles (Overhead)! Visualize configuring your Task swap interval (Time slice) identically matching your CPU’s exact Context Switch delay: Your architecture will violently hemorrhage permanently wasting 50% of its total operational capacity doing absolutely NOTHING but swapping tasks! You MUST aggressively tune your Time Slice intervals perfectly balancing raw CPU velocity!
- Catastrophic Shared Payload Annihilation (Race Conditions): Inside a violently Preemptive architecture, a Context Switch can “Assassinate (Interrupt) execution AT ANY MICROSECOND!” Assume Task A is actively breaching a Memory Buffer. Suddenly, it gets violently interrupted authorising Task B (wielding Maximum Priority) to execute! If Task B identically attempts breaching and overwriting that identical Buffer… the entire data payload detonates into absolute garbage! Operatives MUST aggressively defend highly volatile Shared variables deploying heavy Synchronization blast shields like Mutexes, or brutally commanding Temporary Interrupt Suspensions (Locking the Critical Sections)!
- Massive RAM Cannibalism (Stack per Task): Because every single Task absolutely demands a heavily isolated Storage Sector securing its private Context, Multithreading Operating Systems (e.g., RTOS) MUST aggressively allocate Massive, Fully Independent Memory Stacks exclusively for EVERY active Task! If you recklessly deploy extreme volumes of overlapping Tasks, your microcontroller’s RAM will be brutally cannibalized in milliseconds, instantly triggering a catastrophic system-wide Stack Overflow detonation!
Conclusion
The Context Switch serves as the absolute physical mechanism aggressively executing the “Halt, Extract, Save, Load, and Detonate” commands straight into the CPU core! It is the brutal, invisible force actively empowering the Multitasking matrix to physically construct hyper-complex, completely responsive Real-time operational architectures! Although aggressive swapping inevitably generates System Overhead and severely threatens spawning completely untraceable matrix bugs if Shared Resources lack Mutex shielding, it forever remains the absolute bedrock technique every elite Embedded Operative MUST master completely dominating RTOS efficiency!
If any operatives operating on the server are actively interrogating exactly how many raw physical registers their specific MCU (e.g., STM32 or ESP32) violently rips during a Context Switch, or if you’ve suffered severe psychological trauma desperately attempting to tune FreeRTOS Stack Sizes preventing complete system collapse… blast a flare and upload your intel straight onto our active combat grid at www.123microcontroller.com! Maintain heavy shields, Happy Hardcore Coding to absolutely every operative!