Compilation Phase: Breaking the Black Box of the Translation Process, Morphing C Code into Embedded Machine Language

Introduction: Breaching the Core Translation Engine
Greetings, elite engineers and hardcore developers aggressively defending the www.123microcontroller.com grid! The dark-eyed engineer has securely logged back into the terminal. Today, we are violently tearing into the absolute “core engine” orchestrating software creation: The Compilation phase.
Down in the brutal trenches of bare-metal microcontroller combat, our target CPU silicon possesses zero comprehension regarding what an if, while, or printf statement actually is. It exclusively processes pure, raw electrical voltage states: 0s and 1s (Machine Language). In everyday jargon, we frequently weaponize the term “Compiling” or “Building” to describe the entire chaotic journey from source to silicon. However, strictly adhering to the global C language treaty, the overarching Translation Process forces code through a staggering 8 distinct analytical phases. In our previous briefing, we survived the Preprocessing gauntlet (Phases 1-4). Today, we aggressively deploy the Master Engineering Grimoires to expose exactly how the heavy Compilation machinery operates within the massive overarching architecture of the Translation Process, and the brutal mechanics of its internal engine!
Core Theory Autopsy: Compilation Operating Inside the Translation Array
Operating deep within the Translation Process, surviving the chaotic Preprocessor ambush yields an incredibly pure payload designated as the Translation Unit (e.g., the heavily sterilized .i file, completely stripped of human comments and # directive combat tags). This highly unstable, pure code payload is physically handed over to Phase 7 of the global standard: The absolute, authentic Compilation execution phase.
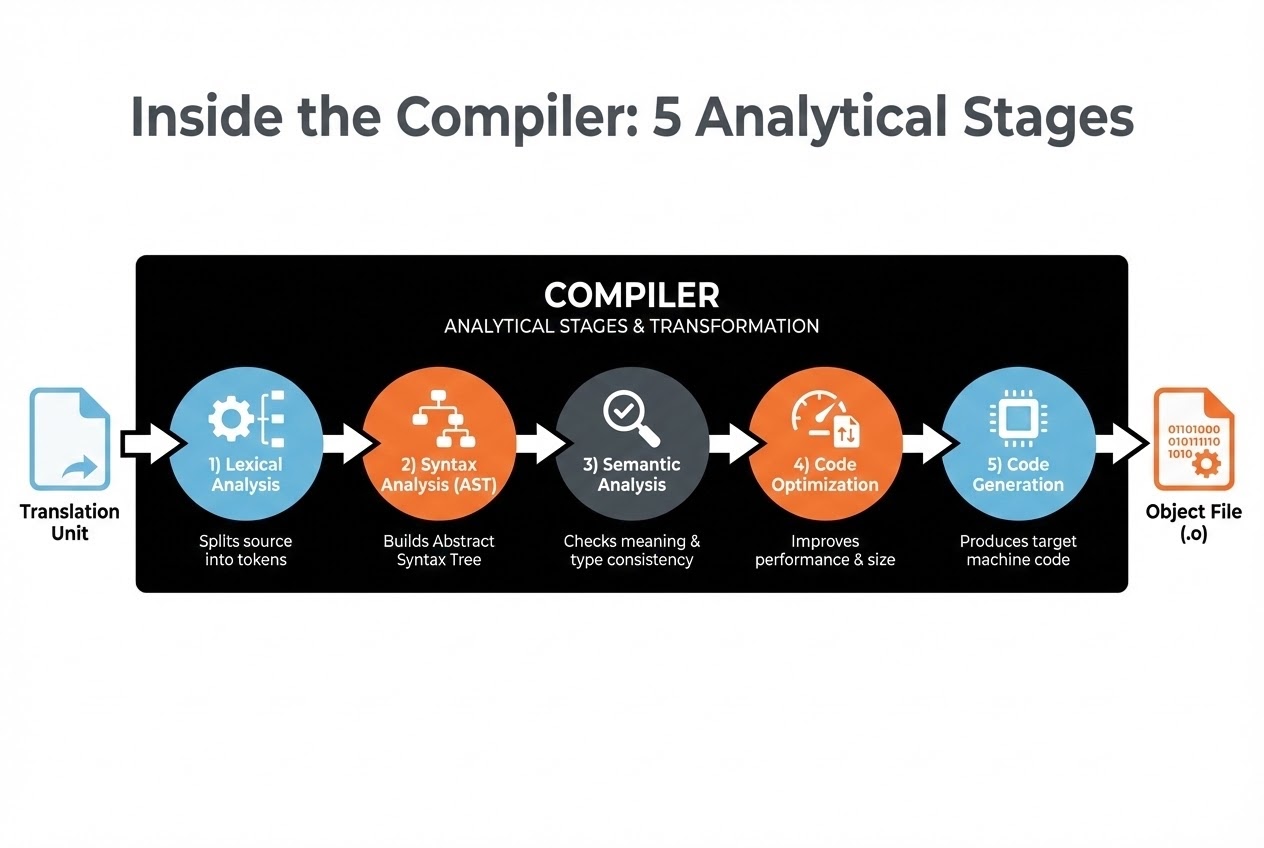
The primary directive of the Compiler engine is incredibly violent: It ingests the pure Translation Unit, forcefully crushing and transmuting high-level architectural constructs (Human-readable C) downward into heavy, low-level execution payloads (Assembly instructions) that the alien architecture of the target processor natively understands. Internally, the Compiler’s brutal anatomy is structurally divided into two massive hemispheres (the Front-end and the Back-end), triggering 5 devastating analytical sub-stages:
- 1. Lexical Analysis (The Tokenizer Shredder): The Compiler sucks in the raw code byte-by-byte, aggressively shredding it mapping the debris into categorized logic groups called “Tokens” (Keywords like
while, variable IDs, numerical constants, and physical operators). - 2. Syntax Analysis (The Blueprint Scanner): The engine forcefully aligns the Tokens attempting to validate their legal structural integrity against the strict laws governing C grammar. It violently constructs a massive, branching hierarchical combat map officially designated as the Parse Tree or Abstract Syntax Tree (AST), visualizing the exact structural relationships of the code payload.
- 3. Semantic Analysis (The Logic Interrogator): The system aggressively interrogates the logic: Did the operative actually declare this variable before commanding it? Do the Data Types mathematically align? Does the function return exact legal ordnance? If the system detects any illegal combat maneuvers during stages 1-3, the Compiler screams throwing massive Syntax Errors or Semantic Errors, instantly aborting the entire build protocol!
- 4. Code Optimization (The Performance Accelerator): Validating the code’s legal integrity, the Compiler violently transmutes the AST into an operating Intermediate Representation (IR or RTL). It then brutally optimizes the payload—compressing the logic heavily accelerating execution velocity (Execution speed) and ruthlessly crushing its physical memory footprint.
- 5. Code Generation (The Target Deployment): This is the lethal drop! The optimized IR payload is violently morphed into highly localized, hardware-specific Assembly language targeting exact silicon architecture (e.g., ARM Cortex-M or PIC). This payload is strictly passed onward to the Assembler drone, which physically stamps the logic pressing it into pure Machine Code, legally sealed inside an Object Code file (
.oor.obj).
Cross-Compilation (The Alien Bridge Protocol): Dominating the Embedded Systems combat zone, physically severing the Front-end (C language analysis) from the Back-end (Machine language generation) grants us absolute tactical supremacy: Cross-compiling. We weaponize our heavy desktop PCs (Host) running the massive Compiler engine, commanding it to violently forge Object code specifically targeted for the alien microcontroller architecture (Target), rather than executing generating binaries targeting the host PC’s internal architecture!
Firing Live Code Rounds: Extracting the Register Matrix
Let us visually intercept a hardcore hardware-centric C snippet, aggressively exposing exactly how the Compilation phase (specifically the Code Optimization sector) acts as heavy artillery supporting embedded operatives.
#include <stdint.h>
/* Defining the heavy Base Address and Offset targeting the physical hardware Register */
#define GPIOA_BASE 0x40020000
#define GPIOA_MODER 0x00
/* The physical hardware initialization strike function */
void init_gpio(void) {
/*
* 1. 🛡️ Deploying the 'volatile' heavy combat shield! We explicitly scream at the Compiler
* during the Semantic Analysis interrogation: "ABSOLUTELY DO NOT Optimize or blind-cache
* the memory access pointing to these physical coordinates!"
*
* 2. Constant Folding Execution: Deep inside the Code Optimization grinder, the Compiler
* acts with extreme intelligence. It physically executes the mathematical addition
* (0x40020000 + 0x00) immediately on the assembly line (Compile-time), utterly destroying
* the necessity deploying real CPU clock-cycles forcing calculations during live combat (Run-time)!
*/
volatile uint32_t * const p_moder = (uint32_t *)(GPIOA_BASE + GPIOA_MODER);
/* Aggressively seizing physical pin control forcing Output mode directly slamming the memory matrix */
*p_moder = 0x00000001;
}
int main(void) {
init_gpio();
while(1) {
/* The infinite operational combat loop */
}
return 0; // Operating in bare-metal, execution vectors must never breach this physical boundary.
}
Proximity Defcons: Heavy Best Practices & Fatal Pitfalls
Evaluating standard combat manuals alongside elite operative battle-scars aggressively illuminates massive, fatal pit-traps hidden within the Compilation architecture:
- Do Not IGNORE Warning Sirens (Warnings are Errors): During heavy Semantic Interrogations, the engine frequently flags suspicious logic evaluating it as “highly anomalous but barely functional”—for instance, violently crunching massive data arrays into microscopic data types (Implicit conversion). The compiler screams throwing Warning alerts. Hardcore operatives MUST command executing
-Walland-Werrorflags (in GCC/Clang arsenals), brutally forcing absolutely every minor Warning converting triggering massive Fatal Errors! This permanently blocks covert bugs infiltrating the deployment. - Beware the Hardware VS Optimizer Blood Feud: Entering Code Optimization, the Compiler operates as a ruthless assassin actively hunting and terminating code it assesses as “useless” (Dead code elimination). If an engineer attempts reading critical sensor data ripping it from a physical Register without securely deploying the
volatilecombat shield, the arrogant Compiler decides, “This value cannot logically alter; I refuse to burn cycles re-reading it!” It caches the data permanently freezing it inside CPU arrays, completely blinding the system leaving you completely incapable of detecting new sensor fluctuations! - The Compiler is Legally Blind (Syntax vs True Logic): Always remember: Surviving the Translation gauntlet extracting the
.oObject file merely legally proves your code possesses perfect, legal grammar (Syntax valid). It absolutely DOES NOT prove “the system operates safely executing correctly without killing the host (Logical correctness).” If you arrogantly command a10 / 0(Divide-by-zero) strike, some weakened compilers may grant authorization, successfully compiling… only for the entire hardware architecture to violently self-destruct during the live drop (Execution-time error). - The Object File (
.o) is a Dud Missile: Reaching the extraction point of the Compilation phase (Phase 7), you acquire the Object file, but it absolutely refuses to execute! The internal target coordinates (Addresses) defining cross-file function calls (such as targetingprintfor heavy external libraries) remain totally unverified and completely detached (Unresolved references). You must survive and heavily rely upon the Linker engine (waiting in Phase 8) to violently smash and fuse all Object files constructing the final lethal payload!
Conclusion
Aggressively summarizing the intel, Compilation is the absolute heaviest, most brutal combat theater operating inside the Translation Process. It represents the massive black-box transmuting human operational logic (Source code) downward into pure, localized silicon execution language (Object code). This requires surviving extreme structural analysis, deep semantic interrogation, and aggressive performance optimization. Executing total dominance over these internal mechanics empowers hardcore operatives heavily manipulating compiler flags forging the fastest, most incredibly lethal C code possible!
In our upcoming deployment, we drop directly into the “final extraction zone” of the Translation Process: Tracking the Linker as it violently smashes entire arrays of Object Code together forging the ultimate Firmware payload locking it directly onto the board! If any operative holds combat records surviving bizarre Compiler warning anomalies operating inside Embedded sectors, drop a flare sharing the logs inside our active grid at www.123microcontroller.com! Maintain heavy shields, Happy Hardcore Coding to all operatives!